Abstract
The application of Internet of Things promotes the cooperation among firms, and it also introduces some information security issues. Due to the vulnerability of the communication network, firms need to invest in information security technologies to protect their confidential information. In this paper, considering the multiple-step propagation of a security breach in a fully connected network, an information security investment game among n firms is investigated. We make meticulous theoretic and experimental analyses on both the Nash equilibrium solution and the optimal solution. The results show that a larger network size (n) or a larger one-step propagation probability (q) has a negative effect on the Nash equilibrium investment. The optimal investment does not necessarily increase in n or q, and its variation trend depends on the concrete conditions. A compensation mechanism is proposed to encourage firms to coordinate their strategies and invest a higher amount equal to the optimal investment when they make decisions individually. At last, our model is extended by considering another direct breach probability function and another network structure, respectively. We find that a higher connection density of the network will result in a greater expected cost for each firm.
Similar content being viewed by others
Avoid common mistakes on your manuscript.
1 Introduction
In recent years, the rapid development of sensor technology, RFID technology, wireless transmission technology, and data processing technology drives the applications of Internet of Things (IoT). With the wide application of IoT in all walks of life and ensuing emergence of new services, all related firms are required to coordinate as well as share confidential information with each other. The extent of collaboration relies on information technology (IT) and communication networks. However, the communication networks also introduce significant information security issues. Hackers and malicious entities attack the network firms with various motivations such as financial goals, peer recognition, or curiosity. These attacks include attacks on the network as a whole, attacks on selected end points, undesirable forms of interactions such as spam e-mail, and annoyances such as Web pages that are unavailable or defaced (Grossklags et al, 2008). It is well known that communication networks increase the likelihood of information security breaches. For better cooperation, a firm often allows other partnering firms to access information in their sites directly using trusted interconnections, which also facilitates the propagation of security breaches (Bandyopadhyay et al, 2010). A hacker that has penetrated one firm may be able to hack other connected firms relatively easily via the trusted connections (Zhao et al, 2013). As reported by Grance et al (2002), “If one of the connected systems is compromised, the interconnection could be used as a conduit to compromise the other system and its data.” For instance, Walmart and Proctor & Gamble (P&G) adopt industry standards Electronic data interchange (EDI) to communicate key business documents with each other (Grean and Shaw, 2002). Since the EDI link is a trusted connection, a hacker having breached Walmart’s information system will break into the information system of P&G more easily, and vice versa. Therefore, the attacks launched by hackers may not only cause the attacked firms, but also the partnering firms in the network a great loss. As a result, firms in the network will not trust or rely on each other, and the collaboration among firms will disintegrate at last.
As the economic benefits brought by IoT-related services are enormous, maintaining good cooperation relationships with partnering firms is necessary. Therefore, preventing attacks and mitigating the damages from computer and information security breaches are of great significance, not only to protect the attacked firm itself, but also the cooperated firms from a great loss. A high level of information security contributes to the collaboration of firms in the network. Hence, firms need to invest in information and network security technologies to reduce the likelihood of probable damages caused by information security incidents. However, the cost of information security is very high, and a completely secure information system does not exist. Thus, the critical task for a firm is to determine the right amount of information security investment, based on the potential loss associated with a security breach if it does occur, and the information security environment the firm faces (Huang et al, 2008).
The rest of this paper is organized as follows: Section 2 mainly describes some related works about the information security investment. A description of our information security game is given in Section 3. In Section 4, we make Nash equilibrium analyses on our game. Section 5 analyzes the optimal investment in our game model. To better illustrate our theoretical analyses, a simulation experiment is conducted in Section 6. Finally, the conclusion is presented in Section 7.
2 Literature review
To address information security investment issues, a number of rigorous analyses have been proposed. Bodin et al (2005) used the analytic hierarchy process (AHP) to address the allocation of the fixed information security budget. Based on given data center network topology, Wang et al (2011) recommended a probability-based model for calculating the probability of insecurity of each protected resource and the optimal investment on each security protection device. Shirtz and Elovici (2011) put forward a new framework to optimize the information security investment strategies when facing with various security measures and found that a higher investment level did not assure a higher security level. Eisenga et al (2012) made an analysis on different practices and techniques which were used to calculate the investments in IT security. Then, they presented some advisable methods for investing in IT security. Within the changing corporate business environment, Kong et al (2012) analyzed the information security investment strategies and performance from a balanced score card perspective by considering the characteristics of information security investment. Bojanc et al (2012) proposed a mathematical model to optimize the information security investment evaluation and decision-making processes. The model was on the basis of a quantitative analysis on the security risks and a digital-assets assessment. Yasasin et al (2014) improved an existing research about a fuzzy decision support model for investing in highly distributed systems. Their proposed model contained uncertainty in regard to the impact of investments on the achieved security levels of components of the distributed system. In addition, a heuristic was developed to solve the problem. Nazareth and Choi (2015) used a system dynamics model to assess various information security management strategies, which can provide managers guidance for security decisions. They found that investing in security detection tools leads to a better payoff than in deterrence activities. Apart from these decision-theory-based analyses, economics-based analyses and game-theory-based analyses were also presented in some literatures.
Based on economics, some studies involving information security investment have appeared since 2002. Gordon et al (2002) first proposed an economic model to optimize the information security investment. They found that for a given potential loss, a firm did not always need to focus its investments on the information sets with the highest vulnerability. To protect an information set, Hausken (2006) considered four kinds of marginal returns to security investment, and proposed classes of all four kinds. However, the optimal investment level in his model was no longer capped at 1/e, which was different from that of Gordon et al (2002). Huang et al (2008) analyzed the information security investment of a firm whose decision maker was risk-averse and followed common economic principles. It was found that the maximum security investment increased with the potential loss a security breach brought, but never exceeded it. The results showed that the announcement of a corporate security breach had an adverse impact of about 1% of the market value of the firm. Based on stock market investors’ behavior toward a firm’s IT security investment announcements, Chai et al (2011) utilized event methodology to verify the value of information security investment. Their study supported the hypothesis that information security investment had a positive and abnormal effect on the returns for firms. Huang and Behara (2013) proposed a model to analyze the information security investment allocation of a fixed budget. Considering concurrent heterogeneous attacks with distinct characteristics and deriving the breach probability functions based on the theory of scale-free networks, they made analytical and numerical analyses subject to various boundary conditions to investigate the relationships among the major variables. Based on economic decision analysis techniques, Huang et al (2014) modeled the Healthcare Information Exchanges (HIEs) to determine the optimal information security investment. They found that it was necessary to prevent the security breach when the potential loss of a security breach reached the threshold level.
Game theory (Pardalos et al, 2008) was also adopted in some literatures concerning information security investment. Lye and Wing (2005) made an analysis on the security of computer networks. They introduced a two-player stochastic game between an attacker and the administrator and constructed a model for the game. Through using a nonlinear program, Nash equilibrium strategies for both players were obtained. Grossklags et al (2008) introduced five game-theoretic models that contain expenditures in information security investment and self-insurance technologies to examine how incentives shifted between investment in a public good and a private good. Sun et al (2008) made a game-theoretic analysis on the information security investment and proposed some constructive suggestions for the defensive organization to invest in information security. The relationship between the strategies chosen by two similar firms in terms to knowledge sharing, and investment in information security was analyzed by Liu et al (2011). Their analyses revealed that the nature of information assets, either complementary or substitutable, had a significant influence on the two firms’ information security investment strategies. Gao et al (2013) considered firms’ information security investment under Cournot and Bertrand competition and constructed a differential game in which over time hackers became knowledgeable by propagating security knowledge and firms could inhibit it by investing in information security. Their findings showed that higher effectiveness of inhibiting knowledge dissemination did not mean a higher investment. Gao et al (2014) analyzed the information sharing strategies and information security investing strategies of two firms by assuming that their information assets were complementary. They acquired the optimal strategies for the two firms and the attacker. The effect of a social planner on the social total costs was also analyzed.
However, all the aforementioned studies do not consider that communication networks propagate security breaches from one firm to another. In 2005, considering the propagation of security breaches, Bandyopadhyay et al investigated the security investment strategies of N supply chain firms in a star network. Their analysis concentrated on the difference between the retailer’s strategy and the vendors’ strategies when all firms made decisions individually. As to the optimal investment, they used implicit equation to present the optimal solution and did not make an analysis on the optimal investment. In the dissertation of Bandyopadhyay (2006), the author analyzed the security investment strategies of N supply chain firms in a concatenated network in Chapter 3.7 and in a star network in Chapter 3.8, respectively. He made an experimental analysis on firms’ strategies and did not make related theoretical analysis. For the concatenated network, the author gave an expression to represent the optimal solution and did not analyze the optimal investment. In 2010, Bandyopadhyay et al took into account the propagation of security breaches and carefully analyzed firms’ information security strategies in a two-firm model. Some valuable insights on firms’ security investments were offered in their work. Since just considering the two-firm case, they did not assess the impacts of the network size and network connection density on firms’ investments. In addition, all the aforementioned three papers did not consider the multiple-step propagation of security breaches. The multiple-step propagation does exist in the communication network. For instance, in Figure 1, firm A is breached first by a hacker, firm B is then breached again through the inner link between A and B, and firm C is breached through the inner link between B and C. Apparently, firm B is breached through a one-step propagation, and firm C is breached through a two-step propagation. Therefore, three-step propagation, four-step propagation, and other multiple-step propagations can be deduced by analogy. In consideration of the multiple-step propagation among firms, this paper conducts a research on the information security investments for multiple firms in a fully connected network. Meticulous theoretic and experimental analyses are made on both the Nash equilibrium solution and the optimal solution.
3 Description of information security investment game
The emergence of various IoT technologies promotes the development of intelligent logistics, intelligent healthcare, and so on. These smart services need multiple firms to exchange and share their information with each other through a communication network. In this paper, we consider a network consisting of n (n ≥ 3) firms. The network structure is a complete graph and is shown in Figure 2, where the ellipsis represents that some firms have been omitted between the two nodes. The information systems of n firms are physically connected through the communication network. In this network, each firm is vulnerable to direct and indirect security breaches. A direct breach means a hacker breaches the firm directly because of the firm’s own security lapse. An indirect breach on a firm occurs when the security of any other partnering firm is breached first and the breach spreads to the first firm because of the vulnerability of the communication network, which propagates the breach (Bandyopadhyay et al, 2010). The one-step propagation and the multiple-step propagation are both considered in this paper. If a breach on a firm occurs, then it will cause the firm a great loss, including a direct financial loss, reputation, and maybe an opportunity to share the benefits brought by the smart service.
For simplicity, we formalize our information security game with the following assumptions:
-
1.
All the n firms are homogeneous, and the potential loss for each firm is identical when a breach occurs. L is denoted as the fixed potential loss of each firm.
-
2.
The probability of a direct breach of firm i (i = 1, 2, …, n) only depends on the monetary investment x i of firm i on information security. We refer to the function p(x i , v) of Gordon and Loeb (2002) as the direct breach probability function, where \( p\left( {x_{i} ,v} \right) = v^{{\alpha x_{i} + 1}} \). The parameter v represents the probability of a direct breach without any investment, and it belongs to the interval (0, 1). The parameter α (α > 0) mainly measures the effect of monetary investment on the direct breach. Thus, if firm i’s security investment is zero, the probability of its information system being breached directly by hackers is v. For a firm with a security investment x, the reduction in the probability of being breached directly due to the security investment is denoted as v − p(x, v).
-
3.
If a firm has suffered a security breach, then the probability that an indirect breach of any other firm occurs through a one-step propagation of the security breach is a constant value q. We call q as “one-step propagation probability.”
-
4.
All the firms in the network are risk neutral.
-
5.
The initial investment of each firm is 0.
According to the description of our information security investment game, we first analyze the probability of a security breach of each firm in the network. Then, we get the following proposition, which will be used in Sections 4 and 5.
Proposition 1
The probability of a breach of firm \( i\,\left( {i = 1,2, \ldots ,n} \right) \) is \( 1 - \left( {1 - p_{i} } \right)A(n,i) \) , where \( A(n,i) = \prod\nolimits_{j = 1,j \ne i}^{n} {\prod\nolimits_{k = 1}^{n - 1} {\left( {1 - p_{j} q^{k} } \right)^{{\prod\nolimits_{s = 1}^{k - 1} {(n - 1 - s)} }} } } \), \( p_{i} = p\left( {x_{i} ,v} \right) \) , and \( p_{j} = p\left( {x_{j} ,v} \right) \).
Proof
Firstly, we analyze the probability of an indirect breach of firm i because of the propagation of firm j. The probability of an indirect breach of firm i because of a k-step propagation of firm j is denoted by \( P\left( {k,j} \right)\left( {k = 1,2, \ldots ,n - 1} \right) \). Then, we have P(1, j) = p j q, and there is just 1 one-step propagation pathway between i and j. P(2, j) = p j q 2 can also be obtained, and the number of two-step propagation pathways between i and j is n − 2. By analogy, it can be obtained that P(k, j) = p j q k, and there exist \( \prod\nolimits_{s = 1}^{k - 1} {(n - 1 - s)} \) k-step propagation pathways between i and j. Therefore, the probability firm i will not suffer an indirect breach because the propagation of firm j is \( \prod\nolimits_{k = 1}^{n - 1} {\left( {1 - p_{j} q^{k} } \right)^{{\prod\nolimits_{s = 1}^{k - 1} {(n - 1 - s)} }} } \). Thus, the probability that firm i will not suffer an indirect breach is \( A\left( {n,i} \right) = \prod\nolimits_{j = 1,j \ne i}^{n} {\prod\nolimits_{k = 1}^{n - 1} {\left( {1 - p_{j} q^{k} } \right)^{{\prod\nolimits_{s = 1}^{k - 1} {(n - 1 - s)} }} } } \). As the probability of a direct breach of firm i is p i , we can easily get that the probability of a breach of firm i (i = 1, 2, …, n) is \( 1 - \left( {1 - p_{i} } \right)A(n,i) \).\(\quad{\square}\)
Proposition 1 presents the probability of a security breach of each firm in the network. It indicates that the probability of a firm suffering a security breach is determined not only by the firm’s own security investment, but also by other firms’ investments. In the one firm case investigated by Gordon and Loeb (2002), as they did not consider the indirect breach, the expected benefit of an investment in information security for a firm is equal to the reduction in the firm’s expected loss attributable to the extra security, i.e., \( (v - p(x,v))L \). Thus, the expected net benefit of the investment is \( (v - p(x,v))L - x \). While in our model, firms will suffer the indirect breaches, it can be derived that the expected net benefit of an investment in information security for firm i is \( \left( {v - p\left( {x_{i} ,v} \right)} \right)A(n,i)L - x_{i} \).
Next, we turn to explore the impact of the network size n and one-step propagation probability q on the probability of a security breach of each firm. Since \( A\left( {n,i} \right) = \prod\nolimits_{j = 1,j \ne i}^{n} {\prod\nolimits_{k = 1}^{n - 1} {\left( {1 - p_{j} q^{k} } \right)^{{\prod\nolimits_{s = 1}^{k - 1} {(n - 1 - s)} }} } } \), it is easy to conclude that A(n, i) decreases with the increase of q. As the probability of a breach of firm i is \( 1 - \left( {1 - p_{i} } \right)A(n,i) \), we obtain that the probability of a security breach of each firm increases with the increase of q. As to the impact of network size, we have the following proposition.
Proposition 2
At the same investment level, an increase in the number of firms in the network increases the probability of a breach of any firm.
Proof
Since \( A(n,i) = \prod\nolimits_{j = 1,j \ne i}^{n} {\prod\nolimits_{k = 1}^{n - 1} {\left( {1 - p_{j} q^{k} } \right)^{{\prod\nolimits_{s = 1}^{k - 1} {(n - 1 - s)} }} } } \), we have \( A\left( {n + 1,i} \right) = \prod\nolimits_{j = 1,j \ne i}^{n + 1} {\prod\nolimits_{k = 1}^{n} {\left( {1 - p_{j} q^{k} } \right)^{{\prod\nolimits_{s = 1}^{k - 1} {(n - s)} }} } } \). Then, it can be derived that
Since \( 0 < p_{i} < 1 \left( {i = 1,2, \ldots ,n} \right), \) \( 0 < q < 1 \), it can be obtained that \( \frac{{A\left( {n + 1,i} \right)}}{{A\left( {n,i} \right)}} < 1 \), which means A(n + 1, i) < A(n, i). The probability of a breach of firm i is 1 − (1 − p i )A(n, i); thus, we can get that an increase in the number of firms (i.e., n) increases the probability of a breach for any firm.\(\quad{\square}\)
Although a newcomer introduces greater information sharing for an existing network and thus brings more benefits, Proposition 2 shows that a new member’s accession will increase the probability of being breached of any other firm in the network. The reason is that a security breach of the newcomer will spread to other firms. Therefore, firms in the existing network should balance the advantages and disadvantages of the newcomer’s accession.
4 Nash equilibrium analyses
In this section, we will study the Nash equilibrium strategies where each firm chooses its information security investment unilaterally, in an effort to minimize its own cost. As the probability of a breach of firm i (i = 1, 2, …, n) is 1 − (1 − p i )A(n, i), the objective function of firm i is:
The strategy variable for each firm is its investment that will optimize its respective objective. Each firm will dynamically change its decision variable according to other firms’ strategies until reaching the equilibrium point. In the equilibrium point, each firm does not want to change its strategy, and any one changing its strategy will increase its own cost. Each firm determines its investment in advance as the game evolves, and eventually each player reaches the equilibrium point. We use A 0 to represent the value of A(n, i) in the initial state (i.e., all firms have none investment). In regard to the Nash equilibrium investment, our analysis results are shown in the following three propositions.
Proposition 3
If \( \alpha A_{0} Lv\ln v\ge- 1 \) , then the Nash equilibrium solution is \( \left( {0,0,0, \ldots ,0} \right) \) . Otherwise, the Nash equilibrium solution is \( \left( {x^{*} ,x^{*} ,x^{*} , \ldots ,x^{*} } \right) \) , where \( x^{*} \) satisfies the following conditions: \( v^{{\alpha x^{*} + 1}} \prod\nolimits_{k = 1}^{n - 1} {\left( {1 - v^{{\alpha x^{*} + 1}} q^{k} } \right)}^{{\prod\nolimits_{s = 1}^{k} {(n - s)} }} = \frac{ - 1}{\alpha L\ln v} \) , and \( \frac{{{\text{d}}^{2} F_{i} }}{{{\text{d}}x_{i}^{2} }}|_{{x_{i} = x^{*} }} > 0 \).
Proof
In the initial state, all firms have none investment. Firm i will not invest unless the amount of investment is less than the expected reduced loss the investment brings. We need to consider the first-order condition \( {\text{d}}F_{i} /{\text{d}}x_{i} = 0 \) and the second-order condition \( {\text{d}}^{2} F_{i} /{\text{d}}x_{i}^{2} > 0 \). Since \( p_{i} = v^{{\alpha x_{i} + 1}} \), we have \( {\text{d}}F_{i} /{\text{d}}x_{i} = 1 + \alpha A_{0} Lv^{{\alpha x_{i} + 1}} \ln v \). We can easily get that \( {\text{d}}^{2} F_{i} /{\text{d}}x_{i}^{2} = \alpha^{2} A_{0} Lv^{{\alpha x_{i} + 1}} \ln^{2} v > 0 \). If \( {\text{d}}F_{i} /{\text{d}}x_{i} |_{{x_{i} = 0}} \ge 0 \), i.e., \( \alpha A_{0} Lv\ln v \ge - 1 \), then firm i will not invest. Therefore, when we have \( A_{0} Lv\ln v \ge - 1 \), every firm will pick the strategy x i = 0 in the Nash equilibrium point.
If \( {\text{d}}F_{i} /{\text{d}}x_{i} |_{{x_{i} = 0}} < 0 \), i.e.,\( \alpha A_{0} Lv\ln v < - 1 \), then firm i will choose \( {\text{d}}F_{i} /{\text{d}}x_{i} = 1 + \alpha A_{0} Lv^{{\alpha x_{i} + 1}} \ln v = 0 \). Then, it can be derived that \( x_{i} = \frac{{\frac{{\ln \left( { - 1/\left( {\alpha A_{0} L\ln v} \right)} \right)}}{\ln v} - 1}}{\alpha } \). However, this is not a stable strategy because other firms will also choose the same strategy. Thus, each firm will change its strategy endlessly until all firms reach the equilibrium point. In the Nash equilibrium point, for firm i, the first-order condition \( {\text{d}}F_{i} /{\text{d}}x_{i} = 0 \) should hold, so that
Similarly, for any firm \( i^{\prime } \,\left( {i^{\prime } = 1,2, \ldots ,n;i^{\prime } \ne i} \right) \), we have
Based on Eqs. (2) and (3), it can be obtained that \( \frac{A(n,i)}{{A\left( {n,i^{\prime } } \right)}} = \frac{{v^{{\alpha x_{{i^{\prime } }} + 1}} }}{{v^{{\alpha x_{i} + 1}} }} = \frac{{p_{{i^{\prime } }} }}{{p_{i} }} \). Since we have \( A(n,i) = \prod\nolimits_{j = 1,j \ne i}^{n} {\prod\nolimits_{k = 1}^{n - 1} {\left( {1 - p_{j} q^{k} } \right)^{{\prod\nolimits_{s = 1}^{k - 1} {(n - 1 - s)} }} } } \) and \( A\left( {n,i^{{\prime }} } \right) = \prod\nolimits_{{j = 1,j \ne i^{{\prime }} }}^{n} {\prod\nolimits_{k = 1}^{n - 1} {\left( {1 - p_{j} q^{k} } \right)^{{\prod\nolimits_{s = 1}^{k - 1} {(n - 1 - s)} }} } } \), it can be easily derived that \( \frac{A(n,i)}{{A\left( {n,i^{{\prime }} } \right)}} = \frac{{\mathop \prod \nolimits_{k = 1}^{n - 1} \left( {1 - p_{i'} q^{k} } \right)^{{\mathop \prod \nolimits_{s = 1}^{k - 1} \left( {n - 1 - s} \right)}} }}{{\mathop \prod \nolimits_{k = 1}^{n - 1} \left( {1 - p_{i} q^{k} } \right)^{{\mathop \prod \nolimits_{s = 1}^{k - 1} \left( {n - 1 - s} \right)}} }} \). Then, we get that \( \ln \frac{A(n,i)}{{A\left( {n,i^{\prime } } \right)}} = \sum\nolimits_{k = 1}^{n - 1} {\prod\nolimits_{s = 1}^{k - 1} {\left( {n - 1 - s} \right)\ln \frac{{1 - p_{{i^{\prime } }} q^{k} }}{{1 - p_{i} q^{k} }}} } \). Combining with \( \frac{A(n,i)}{{A\left( {n,i^{\prime } } \right)}} = \frac{{p_{{i^{\prime } }} }}{{p_{i} }} \), we can obtain
Apparently, Eq. (4) holds if \( p_{i'} = p_{i} \). Assuming that Eq. (4) also holds if \( p_{i'} \ne p_{i} \). For the case of \( p_{i'} > p_{i} \), we have \( 1 - p_{{i^{\prime}}} q^{k} < 1 - p_{i} q^{k} \). It can be easily derived that the left-hand side of Eq. (4) is a negative value and the right-hand side of Eq. (4) is a positive value, which is contradictive. For the case of \( p_{i'} < p_{i} \), we will also obtain a contradiction. Thus, Eq. (4) holds if and only if \( p_{i'} = p_{i} \). As \( p_{i'} = \) \( v^{{\alpha x_{i'} + 1}} \) and \( p_{i} = v^{{\alpha x_{i} + 1}} \), it can be easily derived that \( x_{i'} = x_{i} \) in the equilibrium point. Therefore, we can obtain that the strategies all firms chose are the same in the Nash equilibrium. Based on Eq. (2) and \( p_{j} = v^{{\alpha x_{j} + 1}} \), we can get that if \( \alpha A_{0} Lv{ \ln }v < - 1 \), then the Nash equilibrium solution is \( \left( {x^{*} ,x^{*} ,x^{*} , \ldots ,x^{*} } \right) \), where \( x^{*} \) satisfies the following conditions: \( v^{{\alpha x^{*} + 1}} \prod\nolimits_{k = 1}^{n - 1} {\left( {1 - v^{{\alpha x^{*} + 1}} q^{k} } \right)^{{\prod\nolimits_{s = 1}^{k} {(n - s)} }} } = \frac{ - 1}{\alpha L\ln v} \), and \( \frac{{d^{2} F_{i} }}{{dx_{i}^{2} }}|_{{x_{i} = x^{*} }} > 0 \).\(\quad{\square}\)
Proposition 4
If the Nash equilibrium solution is nonzero (i.e., \( \alpha A_{0} Lv\ln v < - 1 \) ), then the Nash equilibrium solution \( x^{*} \) decreases with the number of firms in the network.
Proof
In the Nash equilibrium, all firm’s strategies are the same, and the direct breach probability of each firm is identical, which is denoted by p, where \( p = v^{{\alpha x^{*} + 1}} \). Therefore, we have \( A(n,i) = A(n,j) = \prod\nolimits_{k = 1}^{n - 1} {(1 - pq^{k} )^{{\prod\nolimits_{s = 1}^{k} {(n - s)} }} \,(\forall i,j \in \left\{ {\left. {1,2, \ldots ,n} \right\}} \right.,i \ne j)} \). Then, we denote \( \prod\nolimits_{k = 1}^{n - 1} {\left( {1 - pq^{k} } \right)^{{\prod\nolimits_{s = 1}^{k} {(n - s)} }} } \) by A(n). From Proposition 3, we get that \( x^{*} \) satisfies Eq. (2). Thus, it can be obtained that \( 1 + \alpha A(n)Lp\ln v = 0 \). Proposition 2 indicates that A(n) decreases with the increase of the number of firms. Therefore, as for firm i, to satisfy the equation \( 1 + \alpha A(n)Lp_{i} \ln v = 0 \), the value of p i should become larger. However, this is not a stable strategy because other firms will also make the same decision. As all firms choose to increase the value of p, which makes A(n) decreased, firm i will increase p i again to satisfy the equation \( 1 + \alpha A(n)Lp_{i} \ln v = 0 \). Apparently, this is also an unstable strategy, and each firm will increase p continually until reaching the new equilibrium point. Therefore, with the increase of the number of firms, the new Nash equilibrium solution will decrease as \( p = v^{{\alpha x^{*} + 1}} \) increases.\(\quad{\square}\)
Proposition 5
If the Nash equilibrium solution is nonzero (i.e., \( \alpha A_{0} Lv\ln v < - 1 \) ), then the Nash equilibrium solution \( x^{*} \) decreases with one-step propagation probability q.
Proof
We have \( A(n) = \prod\nolimits_{k = 1}^{n - 1} {\left( {1 - pq^{k} } \right)^{{\prod\nolimits_{s = 1}^{k} {(n - s)} }} } \). Apparently, A(n) decreases with the increase of one-step propagation probability q. Similar to the proof of Proposition 4, to satisfy the equation \( 1 + \alpha A(n)Lp\ln v = 0 \), the Nash equilibrium solution \( x^{*} \) should decrease.\(\quad{\square}\)
Proposition 3 presents the zero Nash equilibrium solution and the nonzero Nash equilibrium solution in corresponding conditions, respectively. Propositions 4 and 5 expose the negative impact of the communication network. It should be noted that Proposition 4 is similar to Proposition 1 proposed by Bandyopadhyay et al (2010) in the two-firm model, which demonstrate that the propagation probability decreases firms’ incentive to invest more in security in both the two-firm case and the multi-firm case. We have shown that the increase of the numbers of firms or one-step propagation probability can increase the probability of being breached. However, aforementioned Nash equilibrium analyses show that firms will decrease their security investment instead of increasing investment to mitigate the higher security risk, which deteriorates the security environment further. The reason leading to such result is that there exist free-rider behaviors among firms. The investment of a firm contributes not only to the security of its own system, but also the other firms’ systems. With the increase of investment, each firm’s marginal utility of investment decreases. When the number of firms or one-step propagation probability increases (i.e., each firm is easier to suffer an indirect breach), the marginal utility of investment will be smaller, which leads each firm to decrease its investment.
5 The optimal investment
To eliminate the negative impact of the network and minimize the costs of all firms, a social planner is needed to make decisions for all the firms in the network. The objective function is:
Because of the homogeneity and symmetry, the optimal investment of each firm will be the same. We use x to denote the investment of each firm. Thus, the direct breach probability of each firm is \( p = v^{\alpha x + 1} \). Since \( A(n) = \prod\nolimits_{k = 1}^{n - 1} {\left( {1 - pq^{k} } \right)^{{\prod\nolimits_{s = 1}^{k} {(n - s)} }} } \), the objective function can be transformed into the following form:
By analyzing the relationship between the optimal investment of each firm and the investment in Nash equilibrium point, the following proposition is obtained.
Proposition 6
If the Nash equilibrium solution is nonzero (i.e., \( \alpha A_{0} Lv\ln v < - 1 \) ), then the optimal investment of each firm is greater than the investment in the Nash equilibrium point.
Proof
As for the optimal investment, the first-order condition should satisfy \( {\text{d}}F/{\text{d}}x = n + nL\left( {\alpha A(n)v^{\alpha x + 1} \ln v - \left( {1 - v^{\alpha x + 1} } \right)\frac{\partial A(n)}{\partial x}} \right) = 0 \). We use Q to denote \( \sum\nolimits_{k = 1}^{n - 1} {\frac{{q^{k} \mathop \prod \nolimits_{s = 1}^{k} (n - s)}}{{1 - v^{\alpha x + 1} q^{k} }}} \), then we have \( \frac{{{\text{d}}A(n)}}{{{\text{d}}x}} = - Q\alpha A(n)v^{\alpha x + 1} \ln v \). Based on \( \frac{{{\text{d}}A(n)}}{{{\text{d}}x}} = - Q\alpha A(n)v^{\alpha x + 1} \ln v \), it can be derived that \( {\text{d}}F/{\text{d}}x = n + nL\alpha A(n)v^{\alpha x + 1} \ln v\left( {1 + \left( {1 - v^{\alpha x + 1} } \right)Q} \right) = 0 \). The optimal investment of each firm is denoted by \( x_{o} \). The value of A(n) and the value of Q when \( x = x_{o} \) are denoted by \( A\left( n \right)_{o} \) and \( Q_{o} \), respectively. Then, \( x_{o} \) should satisfy \( \frac{{{\text{d}}^{2} F}}{{{\text{d}}x^{2} }}|_{{x = x_{o} }} > 0 \) and \( {\text{d}}F/{\text{d}}x|_{{x = x_{o} }} = n + nL\alpha A(n)_{o} v^{{\alpha x_{o} + 1}} \ln v\left( {1 + \left( {1 - v^{{\alpha x_{o} + 1}} } \right)Q_{o} } \right) = 0 \), i.e.,
We use x N to denote the investment of each firm in the Nash equilibrium point, the value of A(n), and the value of Q when x = x N is denoted by A(n) N and Q N , respectively. From Proposition 3, we get that x N satisfies \( v^{{\alpha x_{N} + 1}} A(n)_{N} = \frac{ - 1}{\alpha L\ln v} \). Therefore, it can be obtained that \( \left( {1 + \left( {1 - v^{{\alpha x_{o} + 1}} } \right)Q_{o} } \right)v^{{\alpha x_{o} + 1}} A(n)_{o} = v^{{\alpha x_{N} + 1}} A(n)_{N} \). Since \( \left( {1 + \left( {1 - v^{{\alpha x_{o} + 1}} } \right)Q_{o} } \right) > 1 \), then we have \( v^{{\alpha x_{o} + 1}} A(n)_{o} < v^{{\alpha x_{N} + 1}} A(n)_{N} \). As \( \alpha A_{0} Lv\ln v < - 1 \), based on Eq. (7), it can be obtained that \( \left( {1 + \left( {1 - v^{{\alpha x_{o} + 1}} } \right)Q_{o} } \right)v^{{\alpha x_{o} + 1}} = \frac{ - 1}{{\alpha L\ln vA\left( n \right)_{o} }} < \frac{ - 1}{{\alpha L\ln vA_{0} }} < \frac{{\alpha Lv\ln vA_{0} }}{{\alpha L\ln vA_{0} }} = v < 1 \). Then, we get that \( (v^{{\alpha x_{o} + 1}} Q_{o} - 1)\left( {1 - v^{{\alpha x_{o} + 1}} } \right) < 0 \). Since \( 1 - v^{{\alpha x_{o} + 1}} > 0 \), we have \( v^{{\alpha x_{o} + 1}} Q_{o} < 1 \). Define \( f(x) = v^{\alpha x + 1} A(n) \). Then it can be easily obtained that \( \frac{\partial f(x)}{\partial x} = \alpha v^{\alpha x + 1} \!\ln vA(n) + v^{\alpha x + 1} \frac{\partial A(n)}{\partial x} = \alpha v^{\alpha x + 1} \ln vA(n)\left( {1 - v^{\alpha x + 1} Q} \right) \), which means that f(x) is a decreasing function of x when x satisfies \( v^{\alpha x + 1} Q < 1 \). Assume that \( x_{N} \ge x_{o} \). It is easy to prove that \( v^{\alpha x + 1} Q \) is a decreasing function of x. Hence, we have \( v^{{\alpha x_{N} + 1}} Q_{N} \le v^{{\alpha x_{o} + 1}} Q_{o} \). Since we have proved that \( v^{{\alpha x_{o} + 1}} Q_{o} < 1 \), it can be derived that \( v^{{\alpha x_{N} + 1}} Q_{N} \le v^{{\alpha x_{o} + 1}} Q_{o} < 1 \), which means that both x N and x o satisfy \( v^{\alpha x + 1} Q < 1 \). As f(x) is a decreasing function, we can get that \( v^{{\alpha x_{N} + 1}} A(n)_{N} \le v^{{\alpha x_{o} + 1}} A(n)_{o} \), which is contradictive to previous conclusion \( v^{{\alpha x_{o} + 1}} A(n)_{o} < v^{{\alpha x_{N} + 1}} A(n)_{N} \). Therefore, the assumption \( x_{N} \ge x_{o} \) is untenable, and we can obtain that x o > x N , i.e., the optimal investment of each firm is greater than the investment in the Nash equilibrium point.\(\quad{\square}\)
Proposition 6 indicates that each firm invests more when they make decisions jointly compared to the situation when they make decisions individually, which is similar to Proposition 2 proposed by Bandyopadhyay et al (2010). Bandyopadhyay et al (2010) assumed that the breach of being breached when making decisions jointly is less than 0.5. We release this assumption and prove that Proposition 6 still holds. The reason causing the outcome in Proposition 6 is that when decisions are determined individually, each firm is selfish and just considers its own benefit. Any firm in the network does not care about whether its direct breach will propagate to other firms and cause loss to the others. Thus, the firm does not have the incentive to invest more to decrease other firms’ loss. If all firms coordinate their strategies, their objective is to minimize the total cost. Each firm is responsible for other firms’ loss, which encourages firms to invest more to decrease the total cost. Therefore, to eliminate the negative impact of the communication network and minimize the total costs of all firms, we need a social planner to determine the optimal investments for all firms.
The variation trends of the optimal investment with the increase of q in different conditions are investigated, and the results are shown in the following two propositions.
Proposition 7
If the Nash equilibrium solution is nonzero (i.e., \( \alpha A_{0} Lv\ln v < - 1 \) ) for any \( q \in \left[ {0,1} \right] \) , then the optimal security investment of each firm increases with q.
Proof
We define \( f(x,q) = \left( {1 + \left( {1 - v^{\alpha x + 1} } \right)Q} \right)v^{\alpha x + 1} A(n) \). From the proof of Proposition 6, we get that the optimal investment x satisfies \( f(x,q) = \frac{ - 1}{\alpha L\ln v} \), and \( \frac{\partial f(x,q)}{\partial x} = \frac{{{\text{d}}^{2} F/{\text{d}}x^{2} }}{n\alpha L\ln v} <\,0 \). Then, we have \( v^{\alpha x + 1} (1 + (1 - v^{\alpha x + 1} )Q) = \frac{ - 1}{\alpha LA(n)\ln v} \), and it can be derived that \( 1 - v^{\alpha x + 1} Q = \left( {1 + \frac{1}{\alpha LA\left( n \right)\ln v}} \right)/\left( {1 - v^{\alpha x + 1} } \right) \).
The first partial derivative of f(x, q) with respects to q is:
Since \( 1 - v^{\alpha x + 1} Q = \left( {1 + \frac{1}{\alpha LA(n)\ln v}} \right)/\left( {1 - v^{\alpha x + 1} } \right) \), we can obtain that
Define \( g(q,k) = 1 - v^{\alpha x + 1} + \frac{1}{\alpha LA(n)\ln v} - \frac{{v^{\alpha x + 1} q^{k} }}{\alpha LA(n)\ln v} \). Then, we have
As \( \frac{1}{\alpha L\ln v} < 0 \), apparently, we can get that g(q, k) is a decreasing function of q. Thus, we have \( g(q,k) = 1 - v^{\alpha x + 1} + \frac{{1 - v^{\alpha x + 1} q^{k} }}{\alpha LA(n)\ln v} \ge g\left( {1,k} \right) = \left( {1 - v^{\alpha x + 1} } \right)\left( {1 + \frac{1}{{\alpha LA(n)|_{q = 1} \ln v}}} \right) \). Since \( \alpha A_{0} Lv\ln v < - 1 \) is valid for any \( \in \left[ {0,1} \right] \), we can get that \( 1 + \frac{1}{{\alpha LA(n)|_{q = 1} \ln v}} > 1 + \frac{1}{{\alpha LA_{0} \ln v}} > 1 + \frac{1}{{\alpha A_{0} Lv\ln v}} > 0 \). As \( 1 - v^{\alpha x + 1} > 0 \), we obtain that \( g\left( {1,k} \right) > 0 \). Then. we have \( g(q,k) = 1 - v^{\alpha x + 1} + \frac{1}{\alpha LA(n)\ln v} - \frac{{v^{\alpha x + 1} q^{k} }}{\alpha LA(n)\ln v} \ge g(1,k) > 0 \). Since \( kq^{k - 1} \prod\nolimits_{s = 1}^{k} {\left( {n - s} \right) > 0} \), it can be derived that \( \frac{{\partial f\left( {x,q} \right)}}{\partial q} = v^{\alpha x + 1} A(n)\mathop \sum \limits_{k = 1}^{n - 1} \frac{{\left[ {1 - v^{\alpha x + 1} + \frac{1}{\alpha LA(n)\ln v} - \frac{{v^{\alpha x + 1} q^{k} }}{\alpha LA(n)\ln v}} \right]kq^{k - 1} \mathop \prod \nolimits_{s = 1}^{k} \left( {n - s} \right)}}{{\left( {1 - v^{\alpha x + 1} q^{k} } \right)^{2} }} > 0 \).
As \( \frac{{\partial f\left( {x,q} \right)}}{\partial q} > 0 \) and \( \frac{{\partial f\left( {x,q} \right)}}{\partial x} < 0 \), x should increase with the increase of q to satisfy the condition \( f(x,q) = \frac{ - 1}{\alpha L\ln v} \). Therefore, the optimal security investment of each firm increases with the one-step propagation probability q.\(\quad{\square}\)
Proposition 8
If the optimal security investment of each firm is nonzero for any \( q \in \left( {0,q_{0} } \right) \) , where \( q_{0} \in \left( {0,1} \right] \) and the optimal investment is precisely zero when \( q = q_{0} \) , then different properties can be obtained according to the value of v:
-
(i)
When v takes a very small value, the optimal investment increases with q.
-
(ii)
When v takes a very large value, the optimal investment decreases with q.
-
(iii)
When v takes a moderate value, there exists a \( q_{\tau } \in \left( {0,q_{0} } \right) \) satisfying \( \frac{{\partial f\left( {x,q} \right)}}{\partial q}|_{{q = q_{\tau } }} = 0 \) . The optimal investment increases with q when \( q \in \left[ {0,q_{\tau } } \right] \) , and decreases with q when \( q \in \left[ {q_{\tau } ,q_{0} } \right] \) , where x represents the optimal security investment of each firm, \( f(x,q) = \left( {1 + \left( {1 - v^{\alpha x + 1} } \right)Q} \right)v^{\alpha x + 1} A(n) \).
Proof
As the proof of Proposition 7, we have \( \frac{\partial f(x,q)}{\partial x} = \frac{{{\text{d}}^{2} F/{\text{d}}x^{2} }}{n\alpha L\ln v} < 0 \) and \( \frac{\partial f(x,q)}{\partial q} = v^{\alpha x + 1} A(n)\sum\nolimits_{k = 1}^{n - 1} {\frac{{\left[ {1 - v^{\alpha x + 1} + \frac{1}{\alpha LA(n)\ln v} - \frac{{v^{\alpha x + 1} q^{k} }}{\alpha LA(n)\ln v}} \right]kq^{k - 1} \mathop \prod \nolimits_{s = 1}^{k} \left( {n - s} \right)}}{{\left( {1 - v^{\alpha x + 1} q^{k} } \right)^{2} }}} \). Define \( g(q,k,v) = 1 - v^{\alpha x + 1} + \frac{1}{\alpha LA(n)\ln v} - \frac{{v^{\alpha x + 1} q^{k} }}{\alpha LA(n)\ln v} \). In the proof of Proposition 7, we get that g(q, k, v) is a decreasing function of q, and it is easy to prove that g(q, k, v) is also a decreasing function of k and v. If \( v \to 0 \), then \( g(q,k,v) \to 1 - v^{\alpha x + 1} > 0 \). And if \( v \to 1 \), then \( g\left( {q,k,v} \right) \to - \infty \). Therefore, we have the following conclusions:
-
(1)
When v takes a smaller value, for any q, we have \( g\left( {q,1,v} \right) > g\left( {q,n - 1,v} \right) > 0 \), then \( \frac{{\partial f\left( {x,q} \right)}}{\partial q} > 0 \), \( \frac{\partial x}{\partial q} = - \frac{{\frac{{\partial f\left( {x,q} \right)}}{\partial q}}}{{\frac{{\partial f\left( {x,q} \right)}}{\partial x}}} > 0 \). Thus, the optimal investment increases with q.
-
(2)
When v takes a larger value, for any q, we have \( g\left( {q,n - 1,v} \right) < g\left( {q,1,v} \right) < 0 \), then \( \frac{{\partial f\left( {x,q} \right)}}{\partial q} < 0 \), \( \frac{\partial x}{\partial q} = - \frac{{\frac{{\partial f\left( {x,q} \right)}}{\partial q}}}{{\frac{{\partial f\left( {x,q} \right)}}{\partial x}}} < 0 \). Hence, the optimal investment decreases with q.
-
(3)
When v takes a moderate value, there must exist a \( q_{\tau } \in \left( {0,q_{0} } \right) \) satisfying \( g\left( {q_{\tau } ,1,v} \right) > 0 > g\left( {q_{\tau } ,n - 1,v} \right) \) and \( \frac{{\partial f\left( {x,q} \right)}}{\partial q}|_{{q = q_{\tau } }} = 0 \). Based on \( g\left( {q_{\tau } ,1,v} \right) = 1 - v^{\alpha x + 1} + \frac{{1 - v^{\alpha x + 1} q_{\tau } }}{{\alpha LA\left( n \right)|_{{q = q_{\tau } }} { \ln }v}} > 0 \), and \( g\left( {q_{\tau } ,n - 1,v} \right) = 1 - v^{\alpha x + 1} + \frac{{1 - v^{\alpha x + 1} q_{\tau }^{n - 1} }}{{\alpha LA(n)|_{{q = q_{\tau } }} \ln v}} < 0 \), we can obtain that \( - \frac{{1 - v^{\alpha x + 1} }}{{1 - v^{\alpha x + 1} q_{\tau } }} < \frac{1}{{\alpha LA(n)|_{{q = q_{\tau } }} \ln v}} < - \frac{{1 - v^{\alpha x + 1} }}{{1 - v^{\alpha x + 1} q_{\tau }^{n - 1} }} < - \left( {1 - v^{\alpha x + 1} } \right) \). It can be derived that
\( \begin{aligned} \frac{{\partial^{2} f(x,q)}}{{\partial q^{2} }} & = v^{\alpha x + 1} \mathop \sum \limits_{k = 1}^{n - 1} \frac{{kq^{k - 1} A(n)\mathop \prod \nolimits_{s = 1}^{k} \left( {n - s} \right)}}{{\left( {1 - v^{\alpha x + 1} q^{k} } \right)^{2} }}\left[ {\left( {1 - v^{\alpha x + 1} } \right)\left[ {\left( {k - 1} \right)q^{ - 1} + \left( {k + 1} \right)v^{\alpha x + 1} q^{k - 1} } \right.} \right. \\ & \quad \left. {\left. { - \left( {1 - v^{\alpha x + 1} q^{k} } \right)\mathop \sum \limits_{{k^{\prime} = 1}}^{n - 1} \frac{{k^{\prime } v^{\alpha x + 1} q^{{k^{\prime } - 1\mathop \prod \nolimits_{s = 1}^{{k^{\prime } }} \left( {n - s} \right)}} }}{{1 - v^{\alpha x + 1} q^{{k^{\prime}}} }}} \right] + \frac{{1 - v^{\alpha x + 1} q^{k} }}{\alpha LA(n)\ln v}\left[ {\left( {k - 1} \right)q^{ - 1} + v^{\alpha x + 1} q^{k - 1} } \right]} \right] \\ \end{aligned} \)
Define
As we have proved that \( \frac{1}{{\alpha LA(n)|_{{q = q_{\tau } }} \ln v}} < - \left( {1 - v^{\alpha x + 1} } \right) \), it can be obtained that
Since \( n \ge 3 \), we have \( 2kv^{\alpha x + 1} q_{\tau }^{k - 1} < \left( {1 - v^{\alpha x + 1} q_{\tau }^{k} } \right)\sum\nolimits_{{k^{\prime} = 1}}^{n - 1} {\frac{{k^{\prime } v^{\alpha x + 1} q_{\tau }^{{k^{\prime } - 1\mathop \prod \nolimits_{s = 1}^{{k^{\prime } }} \left( {n - s} \right)}} }}{{1 - v^{\alpha x + 1} q_{\tau }^{{k^{\prime } }} }}} \). Then, it can be obtained that \( h\left( {q_{\tau } ,k} \right) < 0 \). Hence, we can get that \( \frac{{\partial^{2} f(x,q)}}{{\partial q^{2} }} < 0 \). As \( \frac{\partial f(x,q)}{\partial q}|_{{q = q_{\tau } }} = 0 \) and \( \frac{{\partial^{2} f(x,q)}}{{\partial q^{2} }} < 0 \), it is easy to conclude that \( \frac{\partial f(x,q)}{\partial q} \le 0\left( {q \ge q_{\tau } } \right) \) and \( \frac{\partial f(x,q)}{\partial q} > 0(q < q_{\tau } ) \). Thus, we have that \( \frac{\partial x}{\partial q} = - \frac{{\frac{{\partial f\left( {x,q} \right)}}{\partial q}}}{{\frac{{\partial f\left( {x,q} \right)}}{\partial x}}} > 0 \) when \( \in \left[ {0,q_{\tau } } \right) \) and \( \frac{\partial x}{\partial q} = - \frac{{\frac{{\partial f\left( {x,q} \right)}}{\partial q}}}{{\frac{{\partial f\left( {x,q} \right)}}{\partial x}}} < 0 \) when \( q \in \left( {q_{\tau } ,q_{0} } \right] \). Therefore, the optimal investment increases with q when \( q \in \left[ {0,q_{\tau } } \right] \) and decreases with q when \( q \in \left[ {q_{\tau } ,q_{0} } \right] \).\(\quad{\square}\)
Proposition 7 demonstrates that for all \( q \in \left[ {0,1} \right] \), if the Nash equilibrium solution is nonzero, then the level of optimal investment will be higher if q increases, which is contrary to the variation trend of the Nash equilibrium solution. Proposition 8 reveals that the variation trend of optimal investment with q depends on the value v takes. When v is small, the optimal investment increases with the increase of q, and when v takes a large value, the optimal investment decreases with the increase of q. When v takes a moderate value, the optimal investment of each firm increases with the increase of q until q reaches the threshold, and decreases when q exceeds the threshold. This is an interesting and explainable phenomenon. Apparently, an increase of q leads firms to suffer indirect breaches more easily. When q does not reach the threshold, with the increase of q, an augment in security investment can lead to the reduction of the total security costs. However, when q exceeds the threshold, with the increase of q, it is not economical to increase security investment level because any increase in security investment will be greater than the expected reduced loss it brings.
6 Compensation mechanism
As firms will invest less than the optimal amount when they make decisions individually, we need a social planner to coordinate the strategies for all firms in the network. However, if each firm is selfish and just wants to minimize its own cost, then the optimal investment will be an unstable strategy. Thus, we need to design a compensation mechanism to encourage firms to increase their security investments to the optimal level. A compensation mechanism which coordinates all firms’ investments is proposed in the following proposition.
Proposition 9
If firm i suffers a direct breach and is responsible for an indirect breach of firm j \( (j \ne i) \) , then i needs to pay \( \frac{{\sqrt {1 - p_{i} } }}{{\sqrt {1 - p_{j} } }}L \) to j; similarly, if firm i suffers an indirect breach due to the propagation of firm j’s direct breach, then firm i will acquire a compensation of \( \frac{{\sqrt {1 - p_{j} } }}{{\sqrt {1 - p_{i} } }}L \) from firm j \( (j \ne i) \) . Under this mechanism, firms will invest the optimal amount when they make decisions individually.
Proof
It should be noted that firm i will pay the compensation for firm j if and only if: (1) firm j does not suffer a direct breach and just suffers an indirect breach; (2) firm j’s indirect breach is just caused by the propagation of firm i’s direct breach, and any other firm l (\( l = 1,2, \ldots ,n;l \ne i,j \)) is not responsible for j’s indirect breach. Thus, under the proposed mechanism, firm i’s objective function is
The first term in the right-hand side of Eq. (8) is firm i’s investment. The second term refers to the expected loss. The third term is the total compensations firm that i needs to pay, and the forth term represents the total compensation firm that i will acquire. Denote \( \prod\nolimits_{k = 1}^{n - 1} {\left( {1 - p_{i} q^{k} } \right)^{{\mathop \prod \limits_{s = 1}^{k - 1} \left( {n - 1 - s} \right)}} } \) by B(i); then, we have \( A(n,i) = \prod\nolimits_{j = 1,j \ne i}^{n} {B(j)} \). Simplify Eq. (8), we yield
When making decisions individually, to satisfy the first-order condition, it should be
Due to the symmetry, we have \( x_{i} = x_{j} \left( {j = 1,2, \ldots ,n;j \ne i} \right) \) in the equilibrium point. Then, it can be obtained that p i = p j and B(i) = B(j). As all firms’ investments are the same, we omit the subscript. Based on Eq. (10), it can be derived that
In the proof of Proposition 6, we have \( Q = \sum\nolimits_{k = 1}^{n - 1} {\frac{{q^{k} \mathop \prod \nolimits_{s = 1}^{k - 1} \left( {n - s} \right)}}{{1 - pq^{k} }}} \). As \( \frac{{{\text{d}}p}}{{{\text{d}}x}} = \alpha v^{\alpha x + 1} \ln v \), combining with Eq. (11), we can obtain
Equation (12) and Eq. (7) have the identical form, thus, the new Nash equilibrium investment under the mechanism equals to the optimal investment.\(\quad{\square}\)
The mechanism presented in Proposition 9 shows that the firm responsible for the indirect breach of another firm should compensate for the other firm’s loss, which is rational and encourages firms to invest more in information security. \( \frac{{\sqrt {1 - p_{i} } }}{{\sqrt {1 - p_{j} } }}L \) decreases, and \( \frac{{\sqrt {1 - p_{j} } }}{{\sqrt {1 - p_{i} } }}L \) increases in p i , respectively; it means that firm i pays less to other firms and acquires more compensation from others if firm i cuts down its investment. Thus, at first sight, the mechanism seems to reduce each firm’s investing incentive. However, one should note that if firm i reduces its investment, then the probability firm i suffers a direct breach will increase, which increases the probability firm i pays compensation to other firms and decreases the probability firm i acquires compensation from others. Moreover, the impact of the change in the probabilities of paying and acquiring compensation on the total cost is larger than that of the change in the compensation amounts. Therefore, under the mechanism, firms will increase their investments when making decisions individually.
7 Simulation experiment
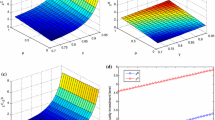
A simulation experiment is conducted to illustrate the above-mentioned theoretical analyses. The purpose of this simulation experiment is to assess the impact of one-step propagation probability and network size on the information security investment level of each firm in both Nash equilibrium point and optimal solution. As the number of firms varies from 3 to infinite, it is impossible to enumerate all cases. We just consider three simple cases: n = 3, n = 4, and n = 5. For the similar reason, the value of v is chosen in the following five cases: v = 0.1, v = 0.3, v = 0.5, v = 0.7, and v = 0.9. L and α should not be too small in case that \( \alpha A_{0} Lv{\ln}v \ge - 1 \) for any \( q \in \left[ {0,1} \right] \). Here, we set L = 200, and α = 0.1.
When v varies from 0.1 to 0.9, the relationships between each firm’s investment x and one-step propagation probability q in both Nash equilibrium solution and optimal solution are shown in Figures 3, 4, 5, 6 and 7, respectively.
In Figures 3, 4, 5, 6 and 7, we get that in the condition of Nash equilibrium, each firm will reduce its investment level with the increase of q until q reaches a specific value, suppose q 0, and when q exceeds q 0, each firm will not invest. This is because for any \( q \in \left[ {q_{0} ,1} \right] \), \( \alpha A_{0} Lv{ \ln }v \ge - 1 \), which means that each firm will not invest according to Proposition 3. Taking the case of n = 5, and v = 0.1 as an example, we have \( \alpha A_{0} Lv{ \ln }v \ge - 1 \) when \( q \ge 0.6004 \), which means each firm will not invest when q exceeds 0.6004. Apparently, this conclusion accords with Figure 3. In Figures 3, 4, 5, 6 and 7, it is easy to find that when other parameters are the same, the Nash equilibrium solution decreases with the increase of n from 3 to 5, which meet with Proposition 4. Obviously, Figures 3, 4, 5, 6 and 7 show that if the Nash equilibrium solution is nonzero, then the optimal investment of each firm is greater than the investment in the Nash equilibrium point, which accords with Proposition 6. In the case of n = 3, and v = 0.1, any q from 0 to 1 satisfies \( \alpha A_{0} Lv{ \ln }v < - 1 \), and Figure 3 shows that in this case, the optimal solution increases with the increase of q from 0 to 1, which meets with Proposition 7. In Figure 7, we find that in any case of n = 3, n = 4, and n = 5, the optimal investment increases with the increase of q from 0 to a specific value and then decreases when q exceeds the specific value, which accords with Proposition 8.
The simulation experiment has verified our aforementioned theoretical analyses. Besides, it also inspires us to find some properties which have not been analyzed in above sections. Figures 3, 4, 5 and 6 show that the optimal investment increases with the increase of n from 3 to 5 for any \( q \in \left[ {0,1} \right] \), whereas in Figure 7, the variation trend of optimal investment with the increase of n depends on q. If q takes a small value, then the optimal investment increases with the increase of n from 3 to 5. And if q takes a large value, then the contrary result will be obtained. Hence, the variation trend of optimal investment with the increase of n depends on multiple influence factors, and it is very difficult using theoretical analysis to find out the exact variation trend of optimal investment with the increase of n. Nevertheless, based on the simulation result, we can still find some properties in regard to the variation trend of optimal investment with the increase of n. Firstly, when both v and q take small values, the optimal investment will increase with the increase of n until n reaches the threshold and will decrease with the increase of n if n exceeds the threshold. An increase of n will lead each firm to be more vulnerable to a security breach. When n does not reach the threshold, the probability of each firm being breached is small. It is cost-efficient to increase security investment because the increased security investment will be less than the expected reduced loss it brings. Whereas, when n is larger than the threshold, any increased investment in information security will be greater than the expected reduced loss, in some extreme cases, when n takes a very large value, the probability of a breach of each firm is close to 1, and it will be unnecessary to invest in information security. Secondly, when v and q take sufficiently large values, the probability of each firm being breached is very large. The increase of n will lead each firm to reduce its investment because it will be not cost-efficient to increase security investment. Due to the limited values of n in this experiment, Figures 3, 4, 5 and 6 have not completely presented aforementioned properties, while in Figure 7, these properties have been demonstrated.
In addition, we examine the Price of Anarchy (PoA) by using numerical examples to assess the impact of one-step propagation probability and network size on the social costs of the Nash equilibrium solution and the optimal solution. The PoA is defined as the ratio between the social value of the Nash equilibrium and the optimal social value. In this paper, we have \( {\text{PoA}} = \frac{{\mathop \sum \nolimits_{i = 1}^{n} F_{i} |_{{x_{i} = x_{N} }} }}{{\mathop \sum \nolimits_{i = 1}^{n} F_{i} |_{{x_{i} = x_{o} }} }} \). The network size is selected as: n = 3, n = 4, and n = 5. In Figures 4, 5, 6 and 7, we can get that when v and q take larger values, the Nash equilibrium investment will be zero. To ensure that the Nash equilibrium investment is nonzero, we set the values of v and q as: v = 0.1, q = 0.1, q = 0.2, q = 0.3, q = 0.4, and q = 0.5. The values of other parameters are chosen as follows: L = 200, and α = 0.1. Table 1 presents the values of PoA in different cases. From Table 1, we find that the PoA value increases with the increase of q from 0.1 to 0.5 and the increase of n from 3 to 5. Thus, we can conjecture that when v takes relatively small value, the PoA value will increase with q and n provided that the values of q and n are not too large, which means that the free-rider behaviors are more serious when the one-step propagation probability and the network size are relatively larger.
8 Extension of the model
In this section, we extend our model in regard to the direct breach probability function and the network structure, respectively. Due to the limited space of this paper, the theoretical analyses are omitted and we just conduct some simulation experiments.
8.1 Direct breach probability function
Ceteris paribus, we extend the model from the previous direct breach probability function \( p\left( {x,v} \right) = v^{\alpha x + 1} \) to the other function \( p(x,v) = \frac{v}{{\left( {\gamma x + 1} \right)^{\beta } }} \) of Gordon and Loeb (2002), where γ > 0 and β ≥ 1 are used to measure the effect of monetary investment on the direct breach. A simulation experiment is conducted to verify the robustness of some main results obtained in above sections. As to the network size, we also consider 3 simple cases: n = 3, n = 4, and n = 5. The value of v is chosen as follows: v = 0.1, v = 0.3, v = 0.5, v = 0.7, and v = 0.9. We set L = 200, β = 1, and γ = 0.1. The simulation results which present the relationships between each firm’s investment x and one-step propagation probability q in different cases are shown in Figures 8, 9, 10, 11 and 12, respectively.
Figures 8, 9, 10, 11 and 12 show that the Nash equilibrium investment decreases in q and n, which consists with Propositions 4 and 5. We find that the Nash equilibrium investment is smaller than the optimal investment for all cases in Figures 8, 9, 10, 11 and 12, which corresponds to Proposition 6. In Figures 8, 9, 10, 11 and 12, when the Nash equilibrium investment is nonzero, the optimal investment increases with q, which conforms with Proposition 7. In accordance with Proposition 8, Figures 9, 10, 11 and 12 present that when n = 5, the optimal investment first increases and then decreases with q. Hence, the simulation figures demonstrate that our previous theoretical analyses results are robust and not just applicable for the specific direct breach probability function \( p\left( {x,v} \right) = v^{\alpha x + 1} \).
8.2 Network structure
The breach probability of a firm varies with different network structures. In a fully connected network, the connection density is very high since any two firms are connected with each other. In order to examine the effect of connection density on firms’ strategies, this section makes an analysis on firms’ investments in the ring network, the connection density of which is relatively low. The ring network structure of n firms is shown in Figure 13. There exist two firms whose direct breaches need k (k = 1, 2, …, n − 1) steps to propagate to firm i, and the two firms are denoted by k1 and k2. Similar to the case of fully connected network, it can be easily obtained that the breach probability of firm i in the ring network is \( 1 - \left( {1 - p_{i} } \right)B\left( {n,i} \right) \), where \( B(n,i) = \prod\nolimits_{k = 1}^{n - 1} {\left( {1 - p_{k1} q^{k} } \right)\left( {1 - p_{k2} q^{k} } \right)} \). The objective function of firm i is
We assume \( \alpha Lv\ln v\prod\nolimits_{k = 1}^{n - 1} {\left( {1 - vq^{k} } \right)^{2} < - 1} \) to ensure that each firm’s investment will be nonzero when making decisions individually. It can be easily derived that the Nash equilibrium investment x Nr and the optimal investment x or satisfy the following two equations, respectively (the derivation process is omitted).
Some numerical examples are employed to give an insight into how a firms’ investment changes when n and q increase in the ring network, as well as to explore the effect of connection density on a firm’s investment and expected cost. In the case of n = 3, the ring network is also the fully connected network. Hence, we just consider two simple cases: n = 4 and n = 5. To guarantee that each firm will invest a nonzero amount when making decisions individually in both network structures, we set the values of v and q as: v = 0.1, v = 0.3, v = 0.5, q = 0.1, q = 0.2 and q = 0.3. The other parameters are selected as follows: L = 200 and α = 0.1. Tables 2 and 3 present the experiment results. We find that similar to the case of fully connected network, when v and q take relatively small values, firms in the ring network will also invest less when making decisions individually and invest more when making decisions jointly with the increase of n and q. Thus, based on the results of Tables 2 and 3, we can conjecture that the properties we get in the fully connected network will also apply to the circumstance of ring network. Apart from the similarity, in Tables 2 and 3, we find that when firms make decisions individually, a firm will invest more in the ring network than in the fully connected network. This is because the connection density is lower in the ring network, which means that a firm is less vulnerable to the propagation of other firms’ breaches and thus the firm’s security investment will be more favorable to itself. Consequently, when making its own decision, a firm’s investment will be larger in the ring network than in the fully connected network. However, Tables 2 and 3 show that if firms make decisions jointly, then each firm will invest less in the ring network compared to in the fully connected network. The reason for this less investment is that in the ring network, the breach probability of each firm is smaller due to the lower connection density and firms do not need to invest the same level as in the fully connected network. Hence, we can infer that a higher connection density decreases firms’ incentives to invest in security when they make their own decisions and encourages firms to invest more if they make decisions jointly. Furthermore, we find that whether the decisions are made individually or jointly, each firm’s expected cost is smaller in the ring network, which consists with intuition and implies that a higher connection density has a negative effect on a firm’s expected cost. Therefore, under the premise of satisfying the need for business, firms should try their best to reduce the network connection density in the network structure designing practice.
9 Conclusion
Internet of Things is conducive to improving efficiency and can bring a great amount of convenience to firms, which drives the emergence of some IoT-related services and the collaboration of relevant enterprises. Besides enabling the communication among cooperative firms, communication network also introduces some information security issues.
In consideration of the multiple-step propagation of a security breach in the network, this paper studies the information security investment strategies in both Nash equilibrium point and optimal solution for all firms. We find that firms will invest less when determining strategies individually compared to when making decisions jointly. The increase of n and q will make each firm more liable to suffer a security breach, whereas firms will cut down their investment instead of increasing if they make decisions individually, which will further increase the information security risk. If all firms in the network coordinate their strategies, and the Nash equilibrium solution is nonzero for any \( q \in \left[ {0,1} \right] \), then each firm’s investment level will be higher with the increase of q. Our analyses and simulation experiment results demonstrate that: (1) When v takes a small value, the optimal investment increases with the increase of q. (2) When v takes a moderate value, the optimal investment increases with the increase of q from 0 to a specific value, and decreases when q exceeds the specific value. (3) When v takes a large value, the optimal investment even decreases with the increase of q. The simulation experiment also shows that the number of firms (i.e., n) is another factor which affects the optimal investment. In order to verify the robustness of our research results, an extension study is conducted by considering another direct breach probability function and another network structure.
Based on the theoretic and experimental results, we attain the following policy implications into firms’ information security management. First, the optimal investment does not always increase in q and n. Instead of blindly increasing or decreasing their information security investments with the increase of some parameters, firms should determine their optimal investments according to the concrete conditions. Second, though a newcomer brings greater knowledge sharing and more benefits for an existing network, the increase of the network size increases each firm’s breach probability. Firms in the existing network should make a trade-off between the advantages and disadvantages of enabling the newcomer’s entry. Third, our findings inspire all firms to coordinate their strategies. A compensation mechanism should be designed to encourage firms to increase their investments to the optimal level when they make decisions individually. Fourth, the network should be configured properly to reduce the one-step propagation probability q to cut down the total expected cost. An appropriate connection density of the network should be determined to satisfy the business need among firms with the minimal connections.
Some extended studies can be conducted in the future. First, this model just considers the disadvantage of increasing the network size. Whereas a larger network size can bring more business benefits, one can extend our model by taking into account the benefit of increasing the network size. Second, the cooperation among firms needs the information sharing of all firms. Information sharing mechanism can be incorporated with this model. In addition, some other direct breach probability functions and other network topologies can be considered to verify the conclusions in this paper.
References
Bandyopadhyay T (2006). Mitigation and transfer of information security risk: Investment in financial instruments and technology. http://dllibrary.spu.ac.th:8080/dspace/handle/123456789/2482.
Bandyopadhyay T, Jacob V and Raghunathan S (2005). Information security investment strategies in supply chain firms: Interplay between breach propagation, shared information assets and chain topology. In: Proceedings of 11th AMCIS, 11–14 August, Omaha.
Bandyopadhyay T, Jacob V and Raghunathan S (2010). Information security in networked supply chains: Impact of network vulnerability and supply chain integration on incentives to invest. Information Technology and Management 11(1):7–23.
Bodin LD, Gordon LA and Loeb MP (2005). Evaluating information security investments using the analytic hierarchy process. Communications of the ACM 48(2):78–83.
Bojanc R, Jerman-Blažič B and Tekavčič M (2012). Managing the investment in information security technology by use of a quantitative modeling. Information Processing and Management 48(6):1031–1052.
Chai S, Kim M and Rao HR (2011). Firms’ information security investment decisions: Stock market evidence of investors’ behavior. Decision Support Systems 50(4):651–661.
Eisenga A, Jones TL and Rodriguez W (2012). Investing in IT security: How to determine the maximum threshold. International Journal of Information Security and Privacy 6(3):75–87.
Gao X, Zhong W and Mei S (2013). A differential game approach to information security investment under hackers’ knowledge dissemination. Operations Research Letters 41(5):421–425.
Gao X, Zhong W and Mei S (2014). A game-theoretic analysis of information sharing and security investment for complementary firms. Journal of the Operational Research Society 65(11):1682–1691.
Gordon LA and Loeb MP (2002). The economics of information security investment. ACM Transactions on Information and System Security 5(4):438–457.
Grance T, Hash J, Peck S, Smith J and Korow-Diks K (2002). Security guide for interconnecting information technology systems. NIST Special Publication 800-47.
Grean M and Shaw MJ (2002). Supply-chain partnership between P&G and Wal-Mart. In: Shaw MJ (ed.) E-business management: Integration of Web technologies with business models. Kluwer Academic Publishers, New York, pp. 155–171.
Grossklags J, Christin N and Chuang J (2008). Secure or insure? A game-theoretic analysis of information security games. In: Proceedings of the 17th International Conference on World Wide Web, 21–25 April, Beijing.
Hausken K (2006). Returns to information security investment: The effect of alternative information security breach functions on optimal investment and sensitivity to vulnerability. Information Systems Frontiers 8(5):338–349.
Huang CD and Behara RS (2013). Economics of information security investment in the case of concurrent heterogeneous attacks with budget constraints. International Journal of Production Economics 141(1):255–268.
Huang CD, Hu Q and Behara RS (2008). An economic analysis of the optimal information security investment in the case of a risk-averse firm. International Journal of Production Economics 114(2):793–804.
Huang CD, Behara RS and Goo J (2014). Optimal information security investment in a Healthcare Information Exchange: An economic analysis. Decision Support Systems 61(1):1–11.
Kong HK, Kim TS and Kim J (2012). An analysis on effects of information security investments: A BSC perspective. Journal of Intelligent Manufacturing 23(4):941–953.
Liu D, Ji Y and Mookerjee V (2011). Knowledge sharing and investment decisions in information security. Decision Support Systems 52(1):95–107.
Lye K and Wing JM (2005). Game strategies in network security. International Journal of Information Security 4(1–2):71–86.
Nazareth DL and Choi J (2015). A system dynamics model for information security management. Information and Management 52(1):123–134.
Pardalos PM, Migdalas A and Pitsoulis L (2008). Pareto Optimality, Game Theory and Equilibria. Springer, Berlin.
Shirtz D and Elovici Y (2011). Optimizing investment decisions in selecting information security remedies. Information Management and Computer Security 19(2):95–112.
Sun W, Kong X, He D and You X (2008). Information security investment game with penalty parameter. In: The 3rd International Conference on Innovative Computing Information and Control (ICICIC’08), 18–20 June, Dalian.
Wang SL, Chen JD, Stirpe PA and Hong TP (2011). Risk-neutral evaluation of information security investment on data centers. Journal of Intelligent Information Systems 36(3):329–345.
Yasasin E, Rauchecker G, Prester J and Schryen G (2014). A fuzzy security investment decision support model for highly distributed systems. In: Proceedings—International Workshop on Database and Expert Systems Applications, 1–4 September, Munich.
Zhao X, Xue L and Whinston AB (2013). Managing interdependent information security risks: Cyberinsurance, managed security services, and risk pooling arrangements. Journal of Management Information Systems 30(1):123–152.
Acknowledgements
This work is supported by the National Nature Science Foundation of China (71231004, 71521001, 71601065, 71501058, 71131002), the Humanities and Social Sciences Foundation of the Chinese Ministry of Education (No. 15YJC630097), Nature Science Foundation of Anhui Province (1508085QG148, 1608085QG167), and the Fundamental Research Funds for the Central Universities of China (JZ2014HGQC0143). Panos M. Pardalos is partially supported by the project of “Distinguished International Professor by the Chinese Ministry of Education” (MS2014HFGY026).
Author information
Authors and Affiliations
Corresponding authors
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made.
The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder.
To view a copy of this licence, visit https://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Qian, X., Liu, X., Pei, J. et al. A game-theoretic analysis of information security investment for multiple firms in a network. J Oper Res Soc 68, 1290–1305 (2017). https://doi.org/10.1057/s41274-016-0134-y
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1057/s41274-016-0134-y