Abstract
Twin-field quantum key distribution (TF-QKD) and its variant protocols are highly attractive due to the advantage of overcoming the rate-loss limit for secret key rates of point-to-point QKD protocols. For variations of TF-QKD, the key point to ensure security is switching randomly between a code mode and a test mode. Among all TF-QKD protocols, their code modes are very different, e.g. modulating continuous phases, modulating only two opposite phases, and sending or not sending signal pulses. Here we show that, by discretizing the number of global phases in the code mode, we can give a unified view on the first two types of TF-QKD protocols, and demonstrate that increasing the number of discrete phases extends the achievable distance, and as a trade-off, lowers the secret key rate at short distances due to the phase post-selection.
Similar content being viewed by others
Explore related subjects
Find the latest articles, discoveries, and news in related topics.Introduction
Quantum key distribution (QKD)1,2 provides two distant parties (Alice and Bob) with a secure random bit string against any eavesdropper (Eve) guaranteed by the law of quantum mechanics. During the past three decades, QKD has rapidly developed both in theory and experiment3,4,5,6,7, and it is on the way to a wide range of implementation. Among all QKD experiments before, without quantum repeaters, the maximum key rates are bounded with respect to the channel transmittance η, defined as the probability for an effective detector click caused by a transmitted photon. So, one of the crucial tasks for the theorists is to find the maximum key rate achievable under ideal implementation (based on perfect single-photon sources, pure-loss channels, perfect detectors, perfect post-processing, and so on). With the aim of finding an upper bound of secret key rate, the theorists have provided several answers8,9,10. The recent work has provided the fundamental limit called Pirandola–Laurenza–Ottaviani–Banchi (PLOB) bound10, which establishes that the secret key rate without quantum repeaters must satisfy R ≤ −log(1 − η).
Remarkably, the twin-field (TF)-QKD protocol, proposed by Lucamarini et al.11, is capable of overcoming this PLOB bound with some restrictions on Eve’s strategies, which is mainly attributed to the single-photon interferometric measurement at the third untrusted party Eve. In other words, a single photon that came from either Alice or Bob interferes at Eve’s beam splitter and clicks the detector, which means that generating a secret key bears a unilateral transmission loss. Because of this dramatic breakthrough, a variant of TF-QKD protocols have been proposed consequentially12,13,14,15,16,17 and some protocols have been demonstrated experimentally18,19,20,21,22. For variant TF-QKD protocols, the key idea to ensure the security is switching probabilistically between a code mode and a test mode, where the former is for key generation, and the latter is for parameter estimation17. Among all TF-QKD protocols, their code modes are very different, e.g., modulating continuous phases11,12, modulating only two opposite phases14,15,16, and sending or not sending signal pulses13. The code modes of the first two kinds are similar in some sense. Intuitively, they may be explained by a unified view.
Interestingly, by discretizing the global phases of Alice and Bob’s emitted pulses in the code mode, we can give a unified view on two kinds of TF-QKD protocols11,12,14,15,16. Specifically, Alice and Bob encode classical bit 0, 1 into phases 0, π of a coherent state, respectively, then randomize them by adding a phase chosen randomly 0, π/M, 2π/M, …, (M − 1)π/M. According to whether or not to perform phase post-selection in the test mode, we introduce two protocols. To prove their security, we establish a universal framework against collective attacks, which can be extended to robust against coherent attacks23 with the technique in ref. 24. The security analysis indicates that increasing the number of discrete phases can extend the achievable distance but lower the secret key rate at short distances due to the phase post-selection. Furthermore, simulation results show that a small number of random phases (say M = 2) may be the best choice for practical implementations.
Results
We first describe details of our proposed TF-QKD protocols that have discrete phase randomization in the code mode, and the schematic set-up is shown in Fig. 1.
In each trial, Alice and Bob randomly choose code mode and test mode and send their quantum states to the untrusted receiver Eve. If a code mode is selected, Alice (Bob) prepares coherent state chosen from \(\{|\alpha {e}^{i{k}_{a(b)}\pi }\rangle ,|\alpha {e}^{i({k}_{a(b)}+\frac{1}{M})\pi }\rangle ,\ldots ,|\alpha {e}^{i({k}_{a(b)}+\frac{M-1}{M})\pi }\rangle \}\). If a test mode is selected, Alice (Bob) prepares coherent state chosen from \(\{\left|{\beta }_{0}{e}^{i{\phi }_{0}}\right\rangle ,\left|{\beta }_{1}{e}^{i{\phi }_{1}}\right\rangle ,\ldots ,\left|{\beta }_{k}{e}^{i{\phi }_{k}}\right\rangle \}\). After interference at beam splitter (BS) and detector click on Eve’s side, she announces the outcome. More detailed explanation can be found in protocol descriptions.
Protocol I
Step 1. Alice and Bob randomly choose code mode or test mode in each trial.
Step 2. If a code mode is selected, Alice (Bob) randomly generates a key bit ka (kb) and a random number x (y) and then prepares the coherent state \(\left|\alpha {e}^{i({k}_{a}+\frac{x}{M})\pi }\right\rangle\) (\(|\alpha {e}^{i({k}_{b}+\frac{y}{M})\pi }\rangle\)), where x, y ∈ {0, 1, 2, …, M − 1}. If a test mode is selected, Alice (Bob) generates a random phase ϕa ∈ [0, 2π) (ϕb ∈ [0, 2π)) and emits coherent state \(\left|{\beta }_{a}{e}^{i{\phi }_{a}}\right\rangle\) (\(\left|{\beta }_{b}{e}^{i{\phi }_{b}}\right\rangle\)), where βa (βb) is randomly chosen from a pre-decided set.
Step 3. Alice and Bob send their quantum states to the untrusted receiver Eve. For each trial, only three outcomes are acceptable, which are “Only detector L clicks”, “Only detector R clicks”, and “No detectors click”, and Eve announces one of these outcomes. Note that the outcome “Both detectors L and R click” is considered as “No detectors click”.
Step 4. Alice and Bob repeat the above steps many times. For the successful detection outcomes (only detector L or R clicks), Alice and Bob publicly announce which trials are the code modes and which trials are the test modes. For each successful trial in the code mode, Alice and Bob announce their x and y, and keep ka, kb as their raw key if x = y. Moreover, Bob should flip his key kb if Eve announces “Only detector R clicks”.
Step 5. For each trial that both Alice and Bob select test mode, Alice and Bob announce βa with random phase ϕa and βb with random phase ϕb, and only keep the trial that βa = βb and ∣ϕa − ϕb∣ = 0 or π.
Step 6. Alice and Bob perform information reconciliation and privacy amplification to extract the final secure keys.
For the simplicity in experiments, we can remove post-selection in the test mode, and the simplified protocol runs as follows.
Protocol II
Step 1. Same as Protocol I.
Step 2. Same as Protocol I.
Step 3. Alice and Bob send their quantum states to the untrusted receiver Eve. For each trial, only three outcomes are acceptable, which are “Only detector L clicks”, “Only detector R clicks”, and “No detectors click”. Note that, the outcome “Both detectors L and R click” is considered as “No detectors click” in the code mode and is considered as only detector L or R clicks with equal probability in the test mode. Consequentially, Eve announces one of these outcomes.
Step 4. Alice and Bob repeat the above steps many times. For the successful detection outcomes (only detector L or R clicks), Alice and Bob publicly announce which trials are the code modes and which trials are the test modes. For each successful trial in the code mode, Alice and Bob announce their x and y, and keep ka, kb as their raw key if x = y. Moreover, Bob should flip his key kb if Eve announces “Only detector R clicks”.
Step 5. For each trial that both Alice and Bob select the test mode, the yield Yl,k, probability of Eve announcing the successful outcome provided Alice emits l-photon state and Bob emits k-photon state, can be estimated.
Step 6. Same as Protocol I.
Our security proof is based on Devetak–Winter’s bound25, concretely, bounding the information leakage IAE. Thus the secret key rate is given by
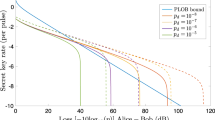
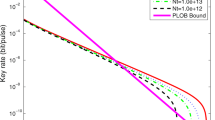
where Q is the counting rate, 1/M is the shifting factor, e is the error rate, and f is the error correction efficiency. By applying infinite decoy states26,27,28,29 in the test mode, we can simulate the performance of our two protocols with different M. The simulation parameters are given in Table 1. For Protocol I, we present the numerical simulations of secret key rate in Fig. 2 and the maximal channel loss in Table 2. If we remove the sifting efficiency, the limitary channel loss with M → ∞ is 81.5 dB as shown in Table 2. According to Fig. 2 and Table 2, it is sufficient to apply TF-QKD with M = 2, which almost reaches the theoretical limit channel loss. Analogously, for Protocol II, we get simulation results comparable to those of Protocol I, and we show the secret key rate in Fig. 3 and the theoretical limit channel loss in Table 3. When removing the sifting factor, the maximal channel loss of Protocol II with M → ∞ is 75.8 dB. In addition, one may refer to “Methods” section and Fig. 4 for the cases with finite decoy states.
When we compare Protocol I with Protocol II, the latter one does not require post-selection in the test mode; as a trade-off, the maximal channel loss will be lower. Here we consider the relationship with several varietal TF-QKD protocols12,14,15,16. When M → ∞, Protocol I is exactly the phase matching QKD12 if we relax the post-selection condition ∣ϕa − ϕb∣ = 0 or π and add a corresponding sifting factor. When M = 1, Protocol II is the same as14,15,16 in the code mode, the difference is the way to estimate the information leakage or the “phase error”. To some extent, our proposed TF-QKD protocols with discrete phase randomization in code mode cover the four varietal TF-QKD protocols above.
Discussion
In summary, we have introduced a variant TF-QKD with discrete phase randomization in the code mode and proven its security in asymptotic scenarios. Our protocol can be viewed as a generalization of the four varietal TF-QKD protocols12,14,15,16 to some extent. The security proof discloses that the transmission distance becomes longer with M exponentially increasing; as a trade-off, the secret key rate is lower at short distances. As a result, the transmission distance reaches a limitation when M tends to infinity. Numerical simulations show that it is sufficient to apply TF-QKD with M = 2, for it almost reaches the limitary transmission distance at the cost of about half of secret key rate, compared with the case of M = 1, at short distance. Furthermore, post-selection in the test mode is not convenient in experiment, thus we remove it to make experiments simpler in a modified protocol. We find that the removal of post-selection in the test mode has very limited influence on the secret key rate and achievable distance. Our findings expect that TF-QKD can be run with optimal phase randomization actively, i.e., at short distance one can simply bypass phase randomization, while a phase randomization of 0 or π/2 is sufficient at the long distance case.
During the preparation of this paper, we found that Primaatmaja et al.30 proposed an open question that if coding phases in TF-QKD under different bases, which is quite similar to our idea of phase discrete randomization, can improve secret key rate significantly. Their open question is answered by our finding that M = 2 is almost optimal in some sense.
Methods
Security proof
Here we present security proof Protocol I. First, we analyze the composite states shared by Alice and Bob when they both select the test mode. In the case of βa = βb = β and ϕa = ϕb = ϕ, the composite state of Alice and Bob can be written as
where the fock state is defined as
and the probability is given by
where μ = ∣β∣2 is the light intensity. In the case of βa = βb = β and ϕa = ϕb + π(mod 2π) = ϕ, the composite state of Alice and Bob can be written as
where the fock state is defined as
with probability Pn.
In what follows, we concentrate on bounding Eve’s Holevo information. Eve’s general collective attack can be given by
where state \({\left|e\right\rangle }_{{\rm{E}}}\) is Eve’s ancilla. Then Eve is supposed to announce one of legal outcomes “Only detector L clicks”, “Only detector R clicks”, and “No detectors click” determined by her measurement results “\(\left|L\right\rangle\)”, “\(\left|R\right\rangle\)”, and “\(\left|N\right\rangle\)”, respectively. In the case of βa = βb and ϕa = ϕb, \(|{\gamma }_{n,+}^{L}\rangle\), \(|{\gamma }_{n,+}^{R}\rangle\), and \(|{\gamma }_{n,+}^{N}\rangle\) are some arbitrary quantum states referring to Eve’s measurement results “\(\left|L\right\rangle\)”, “\(\left|R\right\rangle\)”, and “\(\left|N\right\rangle\)”, respectively. \({Y}_{n,+}^{L}\), \({Y}_{n,+}^{R}\), and \({Y}_{n,+}^{N}\) satisfying \({Y}_{n,+}^{L}+{Y}_{n,+}^{R}+{Y}_{n,+}^{N}=1\) are the yields referring to Eve’s measurement results “\(\left|L\right\rangle\)”, “\(\left|R\right\rangle\)”, and “\(\left|N\right\rangle\)”, respectively. Similarly, in the case of βa = βb and ∣ϕa − ϕb∣ = π, \(|{\gamma }_{n,-}^{L}\rangle\), \(|{\gamma }_{n,-}^{R}\rangle\), and \(\|{\gamma }_{n,-}^{N}\rangle\) are some arbitrary quantum states referring to Eve’s measurement results “\(\left|L\right\rangle\)”, “\(\left|R\right\rangle\)”, and “\(\left|N\right\rangle\)”, respectively. \({Y}_{n,-}^{L}\), \({Y}_{n,-}^{R}\), and \({Y}_{n,-}^{N}\) satisfying \({Y}_{n,-}^{L}+{Y}_{n,-}^{R}+{Y}_{n,-}^{N}=1\) are the yields referring to Eve’s measurement results “\(\left|L\right\rangle\)”, “\(\left|R\right\rangle\)”, and “\(\left|N\right\rangle\)”, respectively.
Without loss of generality, we first consider the secret key rate when her measurement result is “\(\left|L\right\rangle\)”. When Alice and Bob both select the code mode, the initial prepared state \(\left|\alpha {e}^{i({k}_{a}+\frac{x}{M})\pi }\right\rangle\) and \(|\alpha {e}^{i({k}_{b}+\frac{y}{M})\pi }\rangle\), with matched-basis trials x = y, can be given by
For the sake of simplicity, we define unnormalized states
where j ∈ {0, 1, 2, …, 2M − 1}. We also define other unnormalized states
After Eve’s attack according to Eq. (7) and her announcing “\(\left|L\right\rangle\),” Alice and Bob keep trials only if x = y. Thus the unnormalized state of Eve conditioned on Alice’s classical bit can be given by
where \(P\{\left|x\right\rangle \}=\left|x\right\rangle \left\langle x\right|\). The probability of Alice obtaining a shifted key (x = y) in a code mode when Eve announces “\(\left|L\right\rangle\)” is
and correspondingly an error click occurs if ka ⊕ kb = 1, thus the error rate of shifted key (x = y) is given by
Thanks to the strong subadditivity of von Neumann entropy (the detailed derivation of how we apply the strong subadditivity is in the Appendix A of ref. 31), Eve’s Holevo information with her announcing “\(\left|L\right\rangle\)” is given by
where \(H(x)=-x\ {\mathrm{log}\,}_{2}x-(1-x){\mathrm{log}\,}_{2}(1-x)\) is binary Shannon entropy and the second inequality holds due to Jensen’s inequality. For each trial that x = y and Eve announces “\(\left|L\right\rangle\)”, the secret key rate is given by
where f is error correction efficiency. What we need to do next is to calculate the average secret key rate for different x when Eve announces “\(\left|L\right\rangle\).” Without considering the sifting factor, the average secret key rate when Eve announces “\(\left|L\right\rangle\)” is given by
We use QL to denote the average gain and eL to denote the average error rate of shifted key, which are written as
Thanks to the concavity of binary Shannon entropy, we utilize Jensen’s inequality to minimize RL. For the second term of Eq. (16) on the right, we have
The condition for equality of Eq. (18) is that \({e}_{0}^{L}={e}_{1}^{L}=\ldots ={e}_{M-1}^{L}\). Similarly, for the third term of Eq. (16) on the right, we have
Here we define \({I}_{{\rm{AE}}}^{L}=H\left(\frac{\mathop{\sum }\nolimits_{j = 0}^{M-1}| \left|{\psi }_{2M+2j,+}^{L}\right\rangle {| }^{2}\,+\,| \left|{\psi }_{2M+2j,-}^{L}\right\rangle {| }^{2}}{2{Q}^{L}}\right)\). Consequently, we have
Similarly, when Eve’s measurement result is “\(\left|R\right\rangle\)”, the analysis of secret key rate is almost the same with the ones when she announces “\(\left|L\right\rangle\)”. Thus the secret key rate when Eve announces “\(\left|R\right\rangle\)” is given by
where \({I}_{{\rm{AE}}}^{R}\) is given by
The trials when Eve’s measurement result is “\(\left|N\right\rangle\)” will not contribute to the secret key. Thus the total secret key rate is R = RL + RR. The total gain and the total error rate of shifted key are given by
In order to find the lower bound of the total secret key rate R, we apply the Jensen’s inequality to the estimation items in Eqs. (15) and (21), and we can get
where the equality holds when eL = eR = e and
where we define
Consequently, the total secret key rate formula can be expressed by
where 1/M is the shifting factor. And the problem of finding the lower bound of the total secret key rate can be converted into finding the upper bound of IAE,
Simulation
In this section, we simulate the performance of our TF-QKD protocols, and the simulation method is very similar to Ma et al.12. Ideally, for Protocol I, Alice and Bob can estimate \({Y}_{n,\pm }^{L/R}\) precisely by infinite decoy-state method.
We assume that the total efficiency of channels and detectors is η, dark counting rate of single photon detectors is d per trial, the optical misalignment is emis, and the mean photon number of each pulse emitted by Alice and Bob is μ. The counting rate is given by
and the error rate is
Applying infinite decoy states, \({Y}_{n,\pm }^{L/R}\) can be given by
We define
Thanks to Cauchy inequality, we have
Thus we can get an equivalent upper bound of IAE given by
The security proof of Protocol II is almost the same as Protocol I. In Protocol II, Eve’s general collective attack is given by
where \({\left|l,k\right\rangle }_{{\rm{AB}}}\) represents the photon-number base prepared by Alice and Bob, \(|{\gamma }_{l,k}^{L}\rangle\), \(|{\gamma }_{l,k}^{R}\rangle\), and \(|{\gamma }_{l,k}^{N}\rangle\) are some arbitrary quantum states referring to Eve’s measurement results “\(\left|L\right\rangle\)”, “\(\left|R\right\rangle\)”, and “\(\left|N\right\rangle\)”, respectively. Besides, \({Y}_{l,k}^{L}\), \({Y}_{l,k}^{R}\), and \({Y}_{l,k}^{N}\) satisfying \({Y}_{l,k}^{L}+{Y}_{l,k}^{R}+{Y}_{l,k}^{N}=1\) are the yields referring to Eve’s measurement results “\(\left|L\right\rangle\)”, “\(\left|R\right\rangle\)”, and “\(\left|N\right\rangle\)”, respectively. Compared to the expression of Eve’s general collective attack in Protocol I, it can be argued that the general collective attack is actually the same as Protocol I if we set
Consequently, applying the security proof method to Protocol II, we find that the expression of the upper bound of IAE is same as the one of Protocol I. In Protocol II, for removing phase post-selection, we estimate the yield Yl,k rather than Yn to bound X2M + 2j. Combining Eqs. (9) and (36), we obtain
where even and odd are the assembles referring to even number set and odd number set, respectively. Similar to Eq. (33), by utilizing Cauchy inequality, we have
where \({Y}_{l,k}={Y}_{l,k}^{L}+{Y}_{l,k}^{R}\). Due to the decoy-state method implemented, Yl,k satisfies the constraints
Thus we have obtained the upper bound of X2M+2j given as follows
Briefly, the upper bound of IAE in Protocol II is given by,
For the sake of analyzing the upper bound of IAE with the increase of M, we define the upper bound of \(\mathop{\sum }\nolimits_{j = 0}^{M-1}{X}_{2M+2j}\) as a function of positive integer M, which is given by
As binary Shannon entropy H(x) increases when 0 ≤ x ≤ 1/2 and decreases when 1/2 ≤ x ≤ 1, it is sufficient to consider the case of F(M) ≤ Q/2. It can be proven that
where N is a positive integer. In order to prove Eq. (43), we rewrite Eq. (42) as follows
where we denote F(M) and \(\sqrt{{P}_{2Mn+2j}{Y}_{2Mn+2j}}\) as G(M) and A2Mn+2j, respectively. For A2Mn+2j is absolutely a nonnegative term, we have
where the inequality holds because of the nonnegative cross term \(\mathop{\sum }\nolimits_{j\ne {j}^{\prime}}^{M-1}(\mathop{\sum }\nolimits_{n = 0}^{\infty }{A}_{2Mn+2j})(\mathop{\sum }\nolimits_{n = 0}^{\infty }{A}_{2Mn+2{j}^{\prime}})\). Similarly,
where we use subscript k instead of \(Nj+{j}^{\prime}\). The nonnegative cross term vanishes when M → ∞, then we have
Thus we have proven Eq. (43). Then we obtain that the upper bound of IAE decreases with M exponentially increasing. In other words, the achievable distance becomes longer as M exponentially increases. As a result, the achievable distance comes to a limitation when M tends to infinity.
Finite-decoy method for Protocol II with M = 2
As Protocol II does not require phase post-selection in the test mode, it is more practical than Protocol I. For Protocol II, it almost reaches the limitary transmission distance with M = 2 shown in Table 3, thus it is interesting and necessary to consider applying finite-decoy states in the test mode.
When finite-decoy states are implemented, finding the upper bound of IAE is equivalent to the following optimized problem
where μa, μb ∈ {μ1, μ2, μ3}. As Fig. 4 shows, the performance is maintained using only three intensity settings. That is, we only need three decoy intensities {μ1, μ2, μ3}, and the signal intensity is chosen from one of them.
Data availability
The data that support the findings of this study are available from the corresponding author upon reasonable request.
References
Bennett, C. H. & Brassard, G. Quantum cryptography: public key distribution and coin tossing. In Proc. IEEE International Conference on Computers, Systems & Signal Processing 175–179 (IEEE, 1984).
Ekert, A. K. Quantum cryptography based on Bell’s theorem. Phys. Rev. Lett. 67, 661 (1991).
Inoue, K., Brunner, N. & Yamamoto, Y. Differential phase shift quantum key distribution. Phys. Rev. Lett. 89, 037902 (2002).
Lo, H.-K. et al. Measurement-device-independent quantum key distribution. Phys. Rev. Lett. 108, 130503 (2005).
Gobby, C., Yuan, Z. L. & Shields, A. J. Quantum key distribution over 122 km of standard telecom fiber. Appl. Phys. Lett. 84, 3726 (2004).
Jouguet, P. et al. Experimental demonstration of long-distance continuous-variable quantum key distribution. Nat. Photonics 115, 160502 (2013).
Wang, C. et al. Phase-reference-free experiment of measurement-device-independent quantum key distribution. Phys. Rev. Lett. 115, 160502 (2015).
Pirandola, S. et al. Direct and reverse secret-key capacities of a quantum channel. Phys. Rev. Lett. 102, 050503 (2009).
Takeoka, M., Guha, S. & Wilde, M. M. Fundamental rate-loss tradeoff for optical quantum key distribution. Nat. Commun. 5, 1 (2014).
Pirandola, S. et al. Fundamental limits of repeaterless quantum communications. Nat. Commun. 8, 15043 (2014).
Lucamarini, M. et al. Overcoming the rate-distance limit of quantum key distribution without quantum repeaters. Nature 557, 400 (2018).
Ma, X., Zeng, P. & Zhou, H. Phase-matching quantum key distribution. Phys. Rev. X 8, 031043 (2018).
Wang, X. B., Yu, Z. W. & Hu, X. L. Twin-field quantum key distribution with large misalignment error. Phys. Rev. A. 6, 062323 (2018).
Cui, C. et al. Twin-field quantum key distribution without phase postselection. Phys. Rev. Appl. 11, 034053 (2019).
Curty, M., Azuma, K. & Lo, H. K. Simple security proof of twin-field type quantum key distribution protocol. npj Quantum Inf. 5, 1 (2019).
Lin, J. & Lütkenhaus, N. Simple security analysis of phase-matching measurement-device-independent quantum key distribution. Phys. Rev. A. 98, 042332 (2018).
Tamaki, K. et al. Information theoretic security of quantum key distribution overcoming the repeaterless secret key capacity bound. Preprint at http://arxiv.org/abs/1805.05511 (2018).
Minder, M. et al. Experimental quantum key distribution beyond the repeaterless secret key capacity. Nat. Photonics 13, 334 (2019).
Wang, S. et al. Beating the fundamental rate-distance limit in a proof-of-principle quantum key distribution system. Phys. Rev. X 9, 021046 (2019).
Liu, Y. et al. Experimental twin-field quantum key distribution through sending or not sending. Phys. Rev. Lett. 123, 100505 (2019).
Zhong, X. et al. Proof-of-principle experimental demonstration of twin-field type quantum key distribution. Phys. Rev. Lett. 123, 100506 (2019).
Chen, J. P. et al. Sending-or-Not-Sending with Independent Lasers: Secure Twin-Field Quantum Key Distribution over 509 km. Phys. Rev. Lett. 124, 070501 (2020).
Lu, F. Y. et al. Practical issues of twin-field quantum key distribution. N. J. Phys. 21, 123030 (2019).
Christandl, M., König, R. & Renner, R. Postselection technique for quantum channels with applications to quantum cryptography. Phys. Rev. Lett. 102, 020504 (2009).
Devetak, I. & Winter, A. Distillation of secret key and entanglement from quantum states. Proc. R. Soc. Lond. A: Math., Phys. Eng. Sci. 461, 207 (2005).
Hwang, W.-Y. Quantum Key Distribution with High Loss: Toward Global Secure Communication. Phys. Rev. Lett. 91, 057901 (2003).
Lo, H.-K., Ma, X. & Chen, K. Decoy State Quantum Key Distribution. Phys. Rev. Lett. 94, 230504 (2005).
Wang, X.-B. Beating the photon-number-splitting attack in practical quantum cryptography. Phys. Rev. Lett. 94, 230503 (2005).
Ma, X. et al. Practical Decoy State for Quantum Key Distribution. Phys. Rev. A. 72, 012326 (2005).
Primaatmaja, I. W. et al. Versatile security analysis of measurement-device-independent quantum key distribution. Phys. Rev. A. 99, 062332 (2019).
Wang, R. et al. Security proof for single-photon round-robin differential-quadrature-phase-shift quantum key distribution. Phys. Rev. A. 98, 062331 (2018).
Acknowledgements
This work has been supported by the National Key Research and Development Program of China (Grant No. 2018YFA0306400); National Natural Science Foundation of China (Grant Nos. 61822115, 61961136004, 61775207, 61702469, 61771439, 61627820, 61675189, 61675189); National Cryptography Development Fund (Grant No. MMJJ20170120); and Anhui Initiative in Quantum Information Technologies.
Author information
Authors and Affiliations
Contributions
Z.-Q.Y., S.W., W.C., G.-C.G., Z.-F.H., and R.W. conceived the basic idea of the security proof. R.W. finished the details of the security proof. Z.-Q.Y., R.W., F.-Y.L., C.-M.Z., W.H., and B.-J.X. designed the simulations. Z.-Q.Y. and R.W. wrote the paper.
Corresponding author
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Supplementary information
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons license, and indicate if changes were made. The images or other third party material in this article are included in the article’s Creative Commons license, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons license and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this license, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Wang, R., Yin, ZQ., Lu, FY. et al. Optimized protocol for twin-field quantum key distribution. Commun Phys 3, 149 (2020). https://doi.org/10.1038/s42005-020-00415-0
Received:
Accepted:
Published:
DOI: https://doi.org/10.1038/s42005-020-00415-0
- Springer Nature Limited
This article is cited by
-
Improving the performance of practical phase-matching quantum key distribution with advantage distillation
Quantum Information Processing (2024)
-
Twin-field quantum key distribution over 830-km fibre
Nature Photonics (2022)
-
Practical long-distance twin-field quantum digital signatures
Quantum Information Processing (2022)
-
Satellite-based phase-matching quantum key distribution
Quantum Information Processing (2022)
-
Discrete-phase-randomized twin-field quantum key distribution without phase postselection in the test mode
Quantum Information Processing (2021)