Abstract
In a dynamic world of technological advances, the Internet of Things (IoT) is a transformational and widespread force that has revolutionized the way we communicate with our surroundings and regulate our environments. It offers several advantages but also introduces inherent risks. In this study, we provide a comprehensive analysis of the risks associated with IoT and employ the effectiveness of a Linear Diophantine Fuzzy Set to rank the risk factors. Because of the significant uncertainties frequently present in IoT contexts, the use of a fuzzy framework is invaluable in discerning and addressing these risks. The primary contribution is to employ the Measurement of Alternatives and Ranking according to the Compromise Solution (MARCOS) method and linear diophantine fuzzy sets to propose a multi-criteria group decision-making method (MCGDM) for ranking attributes to facilitate risk prioritization, enabling consumers to determine the crucial hazards in their IoT systems. Furthermore, we implement a comparative study and a sensitivity analysis to demonstrate the robustness of our proposed methodology. The insights obtained from our research not only improve the awareness of IoT hazards but also enable organizations and individuals to make informed decisions when navigating IoT fields. By proactively addressing these risks, we endorse the development and secure deployment of IoT technology.
Similar content being viewed by others
Avoid common mistakes on your manuscript.
1 Introduction
The Internet of Things (IoT) is a pervasive and transformational force in the dynamic terrain of modern technology that has changed how we connect with our surroundings and manage our environments. IoT, a term that has become increasingly popular in recent years, refers to the networking of a wide range of physical objects, devices, and systems that are all equipped with the ability to gather, share, and process data to form an intelligent, interconnected system 1.
IoT is fundamentally an expression of the interconnected society envisioned by the digital age, in which commonplace items and industrial gear are active players in the digital ecosystem rather than being passive objects. The possibilities are endless because of this interconnection, which can optimize supply chains, healthcare systems, and agriculture in addition to enabling smart homes and cities. It gives organizations, authorities, and people the ability to fully utilize the promise of data-driven decision-making, increased productivity, and cutting-edge services that were previously only seen in science fiction. The ubiquitous nature of IoT, which crosses industry borders and permeates a wide range of sectors, is one of its distinguishing features. IoT devices are used in healthcare to track vital signs of patients and provide medical personnel with real-time data. Automation and smart sensors can improve crop management and reduce agricultural waste. IoT helps create intelligent transportation networks in urban planning, which reduces traffic and environmental effects. These are only a few instances of the enormous possibilities that the IoT offers.
Enabling these items to interact, communicate, and make intelligent decisions without direct human interaction is the main premise underlying the IoT. Important IoT components include:
-
1.
Devices or Things: These actual physical items or entities with communication interfaces, actuators, and sensors installed in them. These sensors can collect information regarding location, temperature, humidity, and other factors.
-
2.
Connectivity: To connect to the Internet and other devices, Internet of Things (IoT) devices use a variety of communication protocols, including Wi-Fi, Bluetooth, cellular networks, and Low power wide area network.
-
3.
Analytics and Data Processing: For processing and analysis, the gathered data are transferred to edge computing systems or the cloud. Advanced analytics, machine learning, and artificial intelligence algorithms are frequently used to obtain valuable insights from data.
-
4.
User Interface: IoT systems generally feature user interfaces that allows users to view and manage linked devices from a distance. These interfaces can be online or mobile.
-
5.
Automobile gadgets: IoT devices frequently can act or control other devices in addition to gathering data, depending on the algorithms in place and the data they receive. A smart thermostat, for instance, can change the temperature in response to sensor data and user preferences.
IoT has the potential to provide several advantages, including increased safety, cost savings, efficiency gains, and improved decision-making. It also introduces up issues with data management, security, privacy, and the possibility of IoT data misuse. As a result, solving these issues is crucial as IoT develops and grows. There are numerous uses of IoT in many different industries, such as:
-
1.
Smart home: Remotely controlled appliances, lights, security cameras, and thermostats for energy efficiency and convenience.
-
2.
Industrial IoT (IIoT): supply chain management in production, predictive maintenance of equipment, and monitoring and optimization of industrial processes.
-
3.
Healthcare: Connectivity between medical devices, wearable fitness trackers, and remote patient monitoring to enhance healthcare delivery.
-
4.
Smart cities: Putting IoT technologies into practice for trash management, traffic control, environmental monitoring, and energy saving in metropolitan regions.
-
5.
Transportation: Smart traffic management systems, driverless cars, and connected vehicles for safer and more effective transportation.
-
6.
Agriculture: Precision farming methods that maximize crop management, irrigation, and animal monitoring using IoT.
-
7.
Retail: IoT-based inventory control, customer tracking, and customized shopping experience.
Functions of IoT devices: IoT devices are essential for many applications, ranging from increasing productivity and safety in transportation and industry to boosting convenience in smart homes. Depending on the technology they use and their intended use, their functionality and capabilities can differ greatly 2. Typically, IoT devices operate by performing the following:
-
1.
Collection of data: The gadgets gather information pertinent to their functions through sensors. For instance, a smart thermostat gathers information on humidity and temperature.
-
2.
Data processing: Depending on the capabilities of the device, some processing of the gathered data may occur. More sophisticated processing may occur at the edge or in the cloud,.
-
3.
Data transmission: To communicate the gathered data to a central server, cloud platform, or user’ device, IoT devices use a variety of communication protocols, such as Wi-Fi, Bluetooth, cellular networks, or LPWAN.
-
4.
Data analysis and Storage: Users can access the data through apps or dashboards, or it can be analyzed for insights using a central database or cloud platform.
-
5.
Supervision and supply: IoT devices may occasionally be able to receive updates or orders from user devices or the cloud, thereby enabling remote control or configuration modifications.
A large and growing body of literature has investigated IoT. Some of the markable research on the IoT is presented in table 1.
1.1 Comprehensive review
In this section, we explore the foundations for the development and conceptualization of our innovative approach.
1.1.1 Linear Diophantine Fuzzy Set
The concept of fuzzy sets (FS) was initially articulated by Zadeh (1965). FS has a wide range of applications in various fields( Chen and Lee (2010); Chen and Jian (2017); Chen et al. (2019); Al-Zibaree and Konur (2023)). Consequently, citeifs introduced the Intuitionistic Fuzzy Set (IFS), a non-membership grade that was added to the fuzzy set. Following various limitations of the two IFS memberships( Rajareega and Vimala (2021); Chen and Randyanto (2013); Zou et al. (2020); Chen et al. (2016)), Yager (2014) created a Pythagorean fuzzy set (PFS). Given the complexity of the problems and progress made in PFS theory, Yager (2017) provided another extensive description of the q-Rung Orthopair Fuzzy Set (q-ROFS). By adding neutral membership, spherical fuzzy set was introduced by and Mahmood et al. (2018). The arbitrary property of the reference parameters was also employed to show that the space of this set is larger than that of FS, IFS, PFS, and q-ROFS(Pethaperumal et al. 2023).
Riaz and Hashmi (2019) suggested using linear diophantine fuzzy control parameters to remove the limits because they stated that these set ideas have limitations about membership and non-membership grades. In LDFS, Riaz and Hashmi employed the reference parameter approach, which is gaining popularity as a precise and thorough method for evaluating choices. This prompted us to contemplate the necessity of demanding and comprehensive LDFS observations. In soft computing, optimization, and uncertain decision-making analysis, the LDFS is a modern approach for tackling real-world problems. A different utilization of the reference parameters is used as a weight vector whose cumulative is less than 1. These characteristics help handle unclear information about the objects under examination by classifying the physical properties of an object.
Due to the practicality of LDFS, they have attracted the attention of several academics from other systematic fields, leading to the writing of several important works. Iampan et al. (2021) covered the LDFS for MCDM issues using a variety of Einstein aggregation approaches. Subsequently, by making decisions, Ayub et al. (2021) created LDF relationship and related algebraic properties. Kamacı (2021) built algebraic structures using an LDF. The LDFS was expanded by Riaz et al. (2020), who included the concept of soft rough sets for material handling equipment. The application of modeling uncertainty in spherical linear Diophantine fuzzy sets to MCDM was discussed in Hashmi et al. (2021). Riaz et al. (2021) developed prioritized AOs for linear Diophantine fuzzy numbers (LDFNs), which were then used to choose third-party logistics suppliers. The applications of Einstein’s prioritized linear Diophantine fuzzy AOs were proposed by Farid et al. (2022). Furthermore, Frank AOs for interval-valued linear Diophantine fuzzy numbers were recently constructed by Riaz et al. (2022). The goal of Petchimuthu et al. (2022) was to identify methods for selecting suppliers using IVLDF data and its AOs. Similarity metrics for LDFS have been introduced and applied to pattern recognition to overcome the COVID-19 issue Mohammad et al. (2022). Subsequently, some LDFS extensions have been presented and used in the fields of medical diagnosis (Vimala et al. 2023), agri-drones(Jayakumar et al. 2023), tender selection(KANNAN and JAYAKUMAR 2023), climate crisis(Kannan et al. 2024) and digital transformations(Jeevitha et al. 2023). Also, the correlation coefficient for LDFS was introduced by Kannan et al. (2024).
1.1.2 MARCOS technique
The theoretical basis for a new approach to problem-solving called MARCOS (Measurement of Alternative and Ranking According to the Compromise Solution), was laid by Popescu et al. (2021) MARCOS solves a variety of issues, that expedites the decision-making process in the literature. The utility functions of the alternatives are determined, and an adaptive ranking of the options is obtained by defining the relationship between the options and the ideal and counter-ideal degrees as reference points. When comparing the MARCOS method to another multicriteria decision making(MCDM) methods such as WASPAS(Radomska-Zalas 2023), DEMATEL(?), SWARA-MOORA (Ghoushchi and Sarvi 2023), VIKOR ( Daǧıstanlı 2024), SAW(Aliyeva et al. 2023), and TOPSIS(Vimala et al. 2023), some of its advantages include higher efficiency, ease of structuring and optimization of the decision process, more accurate determination of the degree of desirability concerning the reference point, better stability and robustness of the results in terms of changing measurement scales, and no problem of ranking inversion(Stević et al. 2020).
The MARCOS method has been applied in several fields. ? employed a technique to sort drivers based on five criteria to assess the transportation system of an international transportation company. Subsequently, a sensitivity analysis was conducted between the MARCOS methods and other methods, demonstrating the superiority of the MARCOS method and the dependability of the ranking. To select a suitable provider, Chattopadhyay et al. (2020) used a modified version of the Marcos technique with the application of D numbers. Ecer and Pamucar (2021) ranked insurance companies in healthcare services by using the MARCOS technique in an intuitionistic fuzzy environment.
Supplier selection using the hybrid grey theory Marcos technique, as proposed by Badi and Pamucar (2020). Moreover, the picture fuzzy MARCOS approach was developed by Simić et al. (2020) to score railway infrastructures. Geographic information systems (GIS), the best-worst method (BWM), and MAROCS techniques are integrated by Torkayesh et al. (2021) to address sustainable landfill placement selection issues for medical waste. The authors employed this terminology when selecting a sustainable provider Subsequently, Stanković et al. (2020) presented an implementation of the MARCOS approach in a fuzzy version. Puška et al. (2020) used the MARCOS approach to address the problem of evaluating project management software. By offering its applications in many disciplines, researchers further expanded the MARCOS approach Using the MARCOS technique in an IF setting, Kang et al. (2022) evaluated the performance of insurance firms during the COVID-19 pandemic. Ali (2021) created a score function and improved the MARCOS approach in the q-ROF scenario.
1.2 Contribution of this research
The contribution of this study comprises of:
-
1.
Demonstrating the MARCOS in LDF framework, a revolutionary approach to IoT risk assessments.
-
2.
Offering a thorough method for ranking risks in an environment of uncertainty.
-
3.
Providing knowledgeable decision-making instruments to stakeholders to manage risks.
-
4.
Raising awareness and encouraging the safe application of IoT technology.
-
5.
Verifying via sensitivity analysis and comparative studies the robustness of the suggested methodology.
1.3 Motivation and objective of this research
The Internet of Things (IoT) has a widespread influence on how we interact with our surroundings in a rapidly changing world of technological breakthroughs. Despite its many advantages, there are risks associated with the Internet of Things. The urgent necessity to thoroughly examine these hazards in light of the ever-changing nature of IoT technology is what has spurred this study. Through the application of the Linear Diophantine Fuzzy Set to handle uncertainties and the MARCOS approach to prioritize risks, our research aims to increase awareness so that people and organizations can make educated decisions when navigating the complex IoT environment. The ultimate objective is to contribute to the safe development and application of IoT technology.
-
1.
Dynamic nature of IoT:
-
(i)
Discuss the ever-changing field of technological innovation.
-
(ii)
Recognize and assess the revolutionary effects of IoT on environmental regulation and communication.
-
(iii)
Comprehensive investigation focusing on vulnerabilities inherent in IoT technologies.
-
(iv)
Explain the uncertainty of IoT, highlighting the necessity of flexible analytical models.
-
(i)
-
2.
LDF-MARCOS technique:
-
(i)
To prioritize and comprehend IoT risk variables in the face of ambiguity, we use the Linear Diophantine Fuzzy Set.
-
(ii)
Benefits of using a fuzzy framework to identify and manage risks in an ever-changing IoT environment.
-
(iii)
Make use of the MARCOS technique to prioritize risks efficiently and help users identify critical risks in their IoT systems.
-
(iv)
Conduct sensitivity analysis and comparative research to demonstrate the strength of the proposed methodology.
-
(i)
-
3.
Proactive risk addressing:
-
(i)
Boost knowledge and awareness of the dangers posed by IoT technologies.
-
(ii)
Give people and organizations the tools they need to navigate the complex IoT environment and make wise decisions.
-
(iii)
Encourage the creation and safe application of IoT technology by taking proactive measures to mitigate the hazards discovered.
-
(i)
In summary, our research is motivated by the need to fully comprehend and manage the dangers related to the ever-changing and revolutionary nature of IoT technology. The objective is to support safe development and well-informed decision-making in the IoT space.
1.4 Flow of the research
The background definitions for this study are provided in Section 2. In Section 3, the multicriteria group decision (MCGDM) method based on the LDF-MARCOS methodology is described. In Section 4, an IoT risk factors case study is presented. The section labeled "Result and Discussion" comprises a sensitivity analysis and comparative evaluation of the suggested methodology. The research discussed throughout the study and forthcoming initiatives are included in the concluding section.
2 Preliminaries
Definition 1
Zadeh (1965) The fuzzy set \(\mathbb {F}\) defined on the set \(\aleph\) is characterized by a mapping \(\mu\): \(\aleph \rightarrow [0, 1]\), where \(\mu (\mathfrak {g})\) indicates the extent to which elements in \(\aleph\) exhibit membership in the set, and the set is represented as
Definition 2
Riaz and Hashmi (2019) The object of the form:
Here, \(\mu _{\mathbb {L}}(\mathfrak {g}), \nu _{\mathbb {L}}(\mathfrak {g}), \tau _{\mathbb {L}}(\mathfrak {g}), \eta _{\mathbb {L}}(\mathfrak {g}) \in [0, 1]\) are the membership, non-membership and reference parameters respectively. These are restricted by the constraints
and
for all \(\mathfrak {g} \in \aleph\)
Definition 3
Riaz and Hashmi (2019) Consider two LDFS \(\mathfrak {C}_{1} = {(\mathfrak {g}, \langle \mu _{\mathfrak {C}_{1}}, \nu _{\mathfrak {C}_{1}}\rangle , \langle \alpha _{\mathfrak {C}_{1}}, \beta _{\mathfrak {C}_{1}}\rangle ): \mathfrak {g} \in \aleph }\) and \(\mathfrak {C}_{2} = {(\mathfrak {g},\langle \mu _{\mathfrak {C}_{2}}, \nu _{\mathfrak {C}_{2}}\rangle , \langle \tau _{\mathfrak {C}_{2}}, \eta _{\mathfrak {C}_{2}}\rangle ): \mathfrak {g} \in \aleph }\). The arithmetic operations between \(\mathfrak {C}_{1}\) and \(\mathfrak {C}_{2}\) are summarized as follows:
-
1.
\(\mathfrak {C}_{1} \cup \mathfrak {C}_{2} = \left( \langle max\{\mu _{\mathfrak {C}_{1}},\mu _{\mathfrak {C}_{2}}\}, min\{\nu _{\mathfrak {C}_{1}},\nu _{\mathfrak {C}_{2}}\}\rangle ,\langle max\{\tau _{\mathfrak {C}_{1}},\tau _{\mathfrak {C}_{2}}\}, min\{\eta _{\mathfrak {C}_{1}},\eta _{\mathfrak {C}_{2}}\rangle \right)\)
-
2.
\(\mathfrak {C}_{1} \cap \mathfrak {C}_{2} = (\langle min\{\mu _{\mathfrak {C}_{1}},\mu _{\mathfrak {C}_{2}}\}, max\{\nu _{\mathfrak {C}_{1}},\nu _{\mathfrak {C}_{2}}\}\rangle ,\langle min\{\tau _{\mathfrak {C}_{1}},\tau _{\mathfrak {C}_{2}}\}, max\{\eta _{\mathfrak {C}_{1}},\eta _{\mathfrak {C}_{2}}\rangle ).\)
-
3.
\(\mathfrak {C}_{1}^{c} = \left( \langle \nu _{\mathfrak {C}_{1}},\mu _{\mathfrak {C}_{1}}\rangle , \langle \eta _{\mathfrak {C}_{1}},\tau _{\mathfrak {C}_{1}}\rangle \right)\)
-
4.
\(\mathfrak {C}_{1} \oplus \mathfrak {C}_{2} = (\langle \mu _{\mathfrak {C}_{1}}+\mu _{\mathfrak {C}_{2}}-\mu _{\mathfrak {C}_{1}}\mu _{\mathfrak {H}}, \nu _{\mathfrak {C}_{1}}\nu _{\mathfrak {C}_{2}}\rangle ,\langle \tau _{\mathfrak {C}_{1}}+\tau _{\mathfrak {C}_{2}}-\tau _{\mathfrak {C}_{1}}\tau _{\mathfrak {H}}, \eta _{\mathfrak {C}_{1}}\eta _{\mathfrak {C}_{2}}\rangle )\)
-
5.
\(\mathfrak {C}_{1} \otimes \mathfrak {C}_{2} = ( \langle \mu _{\mathfrak {C}_{1}}\mu _{\mathfrak {C}_{2}}\rangle ,\nu _{\mathfrak {C}_{1}}+ \nu _{\mathfrak {C}_{2}}-\nu _{\mathfrak {C}_{1}}\nu _{\mathfrak {C}_{2}},\langle \tau _{\mathfrak {C}_{1}}\tau _{\mathfrak {C}_{2}},\eta _{\mathfrak {C}_{1}}+\eta _{\mathfrak {C}_{2}}-\eta _{\mathfrak {C}_{1}}\eta _{\mathfrak {C}_{2}} \rangle )\)
-
6.
\(\sigma {\mathfrak {C}_{1}} = (\langle 1-(1-\mu _{\mathfrak {C}_{1}}^{\sigma }),(\nu _{\mathfrak {C}_{1}})^{\sigma }\rangle , \langle 1-(1-\tau _{\mathfrak {C}_{1}})^{\sigma },(\eta _{\mathfrak {C}_{1}})^{\sigma }\rangle ),\) where \(\sigma\) is non-zero positive real number.
-
7.
\(\mathfrak {C}_{1}^{\sigma }= (\langle (\mu _{\mathfrak {C}_{1}})^{\sigma }, 1-(1-\nu _{\mathfrak {C}_{1}})^{\sigma } \rangle , \langle (\tau _{\mathfrak {C}_{1}})^{\sigma }, 1-(1-\eta _{\mathfrak {C}_{1}})^{\sigma }\rangle )\)
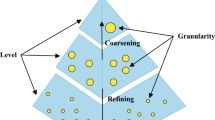
3 The proposed MCGDM method based on linear diophantine fuzzy sets and the MARCOS method
Step 1: Organize the LDF decision matrices given by m experts for r alternatives based on n criteria.
where \(\xi _{ij}^{(p)} = \langle \mu ^{(p)}_{\xi _{ij}}, \nu ^{(p)}_{\xi _{ij}} \rangle , \langle \alpha ^{(p)}_{\xi _{ij}}, \beta ^{(p)}_{\xi _{ij}} \rangle\) are the LDF value given by expert p (p= 1,2,...,m) for alternative i (i=1,2...r) based on criteria j (j=1,2,...n) Step 2: Aggregate the m LDF decision matrix \(\mathfrak {A} = [\xi _{ij}]\) by utilizing the formula
where \(^\mathfrak {u}_p\) be the weight of decision makers. Step 3: Utilizing the two equations below, compute the positive and negative distance measures \(\psi ^{+}_{ij}\) and \(\psi ^{-}_{ij}\) respectively.
Step 4: Use the positive and negative distance measures to determine the closeness coefficient as follows:
Step 5: Construct the extended LDF matrix as:
where \(\mathfrak {E}_{aij}\) = min \(\mathfrak {E}_{ij}\) if j \(\in\) Benefit type or max \(\mathfrak {E}_{ij}\) if j \(\in\) Cost type
\(\mathfrak {E}_{dij}\) = max \(\mathfrak {E}_{ij}\) if j \(\in\) Benefit type or min \(\mathfrak {E}_{ij}\) if j \(\in\) Cost type Step 6: Determine the weight \(\mathfrak {w}_j(j=1,2,...,n)\) of each criteria.
-
6.1 Construct a LDF matrix(n\(\times\)m) for n criteria provided by m decision makers.
-
6.2 Making use of steps 2, 3, and 4, find the closeness coefficient.
-
6.3 After the normalization, determine the weight of each criterion.
Step 7: Normalize the extended LDF matrix.
Step 8: Build the weighted LDF matrix \(\mathfrak {P} = [\mathfrak {W}_{ij}]\)
Step 9: Create the matrix \(S_{i}\) such that
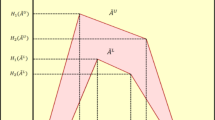
Step 10: Determine the Utility degrees for each alternative by using the formula
Step 11: Compute the utility function of alternatives as follows:
where \(\mathfrak {f}(\mathfrak {y}_i^{-})\) and \(\mathfrak {f}(\mathfrak {y}_i^{+})\) are anti-ideal and ideal computed by the formula:
Step 12: Sort the alternatives based on utility function values. An alternative with a higher value is more desirable. A Schematic of the LDF-MARCOS methodology is shown in Fig. 3
4 Prioritizing IoT risk factors: an analysis with LDF-MARCOS
This section examined the risk factors related to IoT and assessed the LDF-MARCOS technique to identify the level of risk in risk factors.
4.1 Case study: IoT risk factors
The IoT is the cornerstone of a smarter and, more connected future in this age of rapid technological innovation. It is a driving force behind innovation, productivity, and advancement that highlights the indisputable reality that the world is growing increasingly intelligent, connected, and dependent on the Internet of Things every day. To create a more connected, data-driven, and efficient world in the future, this article examines many facets of the IoT, including its applications, difficulties, and potential.
4.1.1 Risk factors of IoT
The internet of things (IoT) has brought about numerous benefits: however, it also introduces several risk factors and challenges. Some of the key risk factors associated with IoT are as follows:
-
1.
Interoperability challenges: Seamless integration may be hampered by IoT devices from various manufacturers being unable to readily connect with one another owing to disparate communication protocols and standards.
-
2.
Reliability and availability: IoT devices depend on network connectivity, and any outages in that connectivity may cause interruptions in services. The actual IoT devices may malfunction or break down, which can cause problems in vital applications.
-
3.
Scalability and management: Managing and servicing IoT devices becomes more difficult as their quantity increases. It can be difficult to guarantee that IoT devices receive security upgrades on time, and if updates are not applied regularly, devices may become vulnerable.
-
4.
Regulatory and compliance issues: IoT installations are more complicated to implement because they must abide by data protection rules, which differ depending on the location.
-
5.
Physical security: Physical tampering with IoT devices can lead to security or functionality breaches. Sensitive data may be exposed if the theft involves expensive IoT equipment.
-
6.
Environmental factors: Extreme environments (such as industrial settings or isolated places) may cause wear and tear on IoT devices more quickly.
-
7.
Privacy issues:IoT devices frequently gather information about their usage and surroundings, which gives rise to concerns regarding data ownership and privacy. IoT devices can gather and use user data without their knowledge, which could result in privacy violations.
-
8.
Security concerns: Owing to their weak security protocols, many IoT devices are open to hacking and illegal access. Sensitive information, such as private company or personal information, may become public knowledge if an IoT device is compromised. IoT devices may be enlisted in botnets for various activities, such as distributing denial-of-service (DDoS) assaults.
4.1.2 Criteria for risk analysis
Impact: Taking into account the possible outcomes of the risk, such as monetary losses, business interruptions, harm to one’s reputation, or safety risks. Risks with large potential consequences were frequently chosen.
Likelihood: Determines the likelihood that risk will materialize. In general, risks that have a higher chance of occurrence are considered more serious.
Relevance: Assess the applicability of risk to a particular project, procedure, or circumstance. Risks should be aligned with the goals and circumstances of the assessment.
Severity: Consider the risk of possible injury or damage when determining the severity of injury. Hazards that may have disastrous effects require additional caution.
Risk tolerance: This takes into account the risk appetite and tolerance of the project or organization. The risk culture of an organization may make some hazards more tolerable than others.
Legal and regulatory compliance: Recognize the dangers associated with non-compliance with rules, as breaking the law may have legal repercussions. Let us consider the risk factors \(\{\mathfrak {R}_1, \mathfrak {R}_2, \mathfrak {R}_3, \mathfrak {R}_4, \mathfrak {R}_5, \mathfrak {R}_6, \mathfrak {R}_7, \mathfrak {R}_8\}\) as a collection of alternatives. The criteria for the risk analysis were taken as parameter sets \(\{\mathfrak {S}_1, \mathfrak {S}_2, \mathfrak {S}_3, \mathfrak {S}_4, \mathfrak {S}_5, \mathfrak {S}_6\}\). Let \(\{\mathfrak {A}^1, \mathfrak {A}^2, \mathfrak {A}^3, \mathfrak {A}^4\}\) be the four experts taken in consideration. The weight of decision makers are \(\mathfrak {u}_1\) = 0.25, \(\mathfrak {u}_2\) = 0.15, \(\mathfrak {u}_3\) = 0.40, \(\mathfrak {u}_4\) = 0.20.
4.2 LDF-MARCOS approach
Determination of weights for criteria: The LDF-matrix \(\mathfrak {M}\) for criteria given by the four experts is considered as follows:
Using formulas 1, 2, 3, 4 the closeness coefficient of each criterion was determined. After normalization, we determined the weight of each criterion, and the values are listed in Table 2.
-
*
Step 1: The LDF decision matrices given by four experts are computed in the matrix \(\mathfrak {A}^{1}_{ij}, \mathfrak {A}^{2}_{ij}, \mathfrak {A}^{3}_{ij}, \mathfrak {A}^{4}_{ij}\).
$$\begin{aligned} \tiny{} & {} \mathfrak {A}^{1}_{ij}=\begin{bmatrix} &{} \mathfrak {S}_1 &{} \mathfrak {S}_2 &{} \mathfrak {S}_3 &{} \mathfrak {S}_4&{} \mathfrak {S}_5&{} \mathfrak {S}_6\\ {\mathfrak {R}_1} &{} \langle 0.81,0.23 \rangle , \langle 0.85, 0.11 \rangle &{} \langle 0.74,0.31 \rangle , \langle 0.80, 0.15 \rangle &{} \langle 0.73,0.40 \rangle , \langle 0.82, 0.16 \rangle &{} \langle 0.59,0.31 \rangle , \langle 0.78, 0.16 \rangle &{} \langle 0.74,0.18 \rangle , \langle 0.79, 0.14 \rangle &{} \langle 0.69,0.36 \rangle , \langle 0.88, 0.10 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_2} &{} \langle 0.47,0.64 \rangle , \langle 0.53, 0.41 \rangle &{} \langle 0.55,0.44 \rangle , \langle 0.68, 0.32 \rangle &{} \langle 0.83,0.41 \rangle , \langle 0.85, 0.09 \rangle &{} \langle 0.65,0.42 \rangle , \langle 0.74, 0.19 \rangle &{} \langle 0.43,0.51 \rangle , \langle 0.74, 0.14 \rangle &{} \langle 0.46,0.62 \rangle , \langle 0.76, 0.74 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_3} &{} \langle 0.42,0.61 \rangle , \langle 0.54, 0.40 \rangle &{} \langle 0.54,0.45 \rangle , \langle 0.65, 0.32 \rangle &{} \langle 0.48,0.61 \rangle , \langle 0.56, 0.42 \rangle &{} \langle 0.63,0.34 \rangle , \langle 0.74, 0.13 \rangle &{} \langle 0.55,0.45 \rangle , \langle 0.60, 0.32 \rangle &{} \langle 0.56,0.49 \rangle , \langle 0.81, 0.17 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_4} &{} \langle 0.71,0.34 \rangle , \langle 0.82, 0.17 \rangle &{} \langle 0.65,0.42 \rangle , \langle 0.72, 0.18 \rangle &{} \langle 0.74,0.31 \rangle , \langle 0.80, 0.18 \rangle &{} \langle 0.46,0.48 \rangle , \langle 0.56, 0.41 \rangle &{} \langle 0.62,0.42 \rangle , \langle 0.74, 0.22 \rangle &{} \langle 0.68,0.31 \rangle , \langle 0.72, 0.26 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_5} &{} \langle 0.64,0.50 \rangle , \langle 0.71, 0.24 \rangle &{} \langle 0.72,0.35 \rangle , \langle 0.84, 0.10 \rangle &{} \langle 0.52,0.49 \rangle , \langle 0.67, 0.30 \rangle &{} \langle 0.42,0.60 \rangle , \langle 0.69, 0.28 \rangle &{} \langle 0.64,0.36 \rangle , \langle 0.71, 0.26 \rangle &{} \langle 0.47,0.53 \rangle , \langle 0.56, 0.38 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_6} &{} \langle 0.23,0.64 \rangle , \langle 0.80, 0.18 \rangle &{} \langle 0.36,0.70 \rangle , \langle 0.82, 0.16 \rangle &{} \langle 0.41,0.60 \rangle , \langle 0.75, 0.22 \rangle &{} \langle 0.48,0.55 \rangle , \langle 0.68, 0.31 \rangle &{} \langle 0.39,0.65 \rangle , \langle 0.72, 0.26 \rangle &{} \langle 0.26,0.73 \rangle , \langle 0.70, 0.26 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_7} &{} \langle 0.82,0.20 \rangle , \langle 0.90, 0.09 \rangle &{} \langle 0.81,0.16 \rangle , \langle 0.85, 0.12 \rangle &{} \langle 0.79,0.29 \rangle , \langle 0.89, 0.10 \rangle &{} \langle 0.72,0.39 \rangle , \langle 0.80, 0.19 \rangle &{} \langle 0.63,0.40 \rangle , \langle 0.81, 0.14 \rangle &{} \langle 0.69,0.42 \rangle , \langle 0.79, 0.20 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_8} &{} \langle 0.76,0.29 \rangle , \langle 0.82, 0.16 \rangle &{} \langle 0.86,0.24 \rangle , \langle 0.91, 0.07 \rangle &{} \langle 0.81,0.25 \rangle , \langle 0.94, 0.05 \rangle &{} \langle 0.76,0.39 \rangle , \langle 0.91, 0.08 \rangle &{} \langle 0.82,0.26 \rangle , \langle 0.91, 0.06 \rangle &{} \langle 0.81,0.27 \rangle , \langle 0.89, 0.09 \rangle \\ \end{bmatrix}\\ \tiny{} & {} \mathfrak {A}^{2}_{ij}= \begin{bmatrix} &{} {\mathfrak {S}_1} &{} {\mathfrak {S}_2} &{} {\mathfrak {S}_3} &{} {\mathfrak {S}_4}&{} {\mathfrak {S}_5}&{} {\mathfrak {S}_6}\\ {\mathfrak {R}_1} &{} \langle 0.74,0.14 \rangle , \langle 0.82, 0.09 \rangle &{} \langle 0.86,0.17 \rangle , \langle 0.82, 0.15 \rangle &{} \langle 0.71,0.42 \rangle , \langle 0.85, 0.12 \rangle &{} \langle 0.58,0.48 \rangle , \langle 0.71, 0.23 \rangle &{} \langle 0.75,0.23 \rangle , \langle 0.80, 0.14 \rangle &{} \langle 0.70,0.32 \rangle , \langle 0.86, 0.15 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_2} &{} \langle 0.36,0.73 \rangle , \langle 0.74, 0.15 \rangle &{} \langle 0.44,0.47 \rangle , \langle 0.70, 0.28 \rangle &{} \langle 0.52,0.65 \rangle , \langle 0.76, 0.12 \rangle &{} \langle 0.43,0.54 \rangle , \langle 0.82, 0.15 \rangle &{} \langle 0.62,0.38 \rangle , \langle 0.80, 0.13 \rangle &{} \langle 0.51,0.56 \rangle , \langle 0.79, 0.20 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_3} &{} \langle 0.56,0.39 \rangle , \langle 0.62, 0.28 \rangle &{} \langle 0.42,0.58 \rangle , \langle 0.53, 0.41 \rangle &{} \langle 0.53,0.44 \rangle , \langle 0.62, 0.34 \rangle &{} \langle 0.66,0.39 \rangle , \langle 0.72, 0.13 \rangle &{} \langle 0.73,0.32 \rangle , \langle 0.78, 0.12 \rangle &{} \langle 0.52,0.60 \rangle , \langle 0.73, 0.21 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_4} &{} \langle 0.75,0.39 \rangle , \langle 0.81, 0.15 \rangle &{} \langle 0.60,0.45 \rangle , \langle 0.75, 0.19 \rangle &{} \langle 0.76,0.30 \rangle , \langle 0.82, 0.17 \rangle &{} \langle 0.47,0.51 \rangle , \langle 0.52, 0.40 \rangle &{} \langle 0.70,0.34 \rangle , \langle 0.76, 0.14 \rangle &{} \langle 0.65,0.46 \rangle , \langle 0.70, 0.26 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_5} &{} \langle 0.61,0.46 \rangle , \langle 0.80, 0.16 \rangle &{} \langle 0.76,0.40 \rangle , \langle 0.86, 0.11 \rangle &{} \langle 0.56,0.51 \rangle , \langle 0.62, 0.31 \rangle &{} \langle 0.46,0.50 \rangle , \langle 0.78, 0.12 \rangle &{} \langle 0.67,0.46 \rangle , \langle 0.70, 0.24 \rangle &{} \langle 0.59,0.62 \rangle , \langle 0.64, 0.23 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_6} &{} \langle 0.42,0.70 \rangle , \langle 0.76, 0.21 \rangle &{} \langle 0.40,0.69 \rangle , \langle 0.76, 0.21 \rangle &{} \langle 0.37,0.70 \rangle , \langle 0.70, 0.29 \rangle &{} \langle 0.32,0.70 \rangle , \langle 0.70, 0.29 \rangle &{} \langle 0.40,0.59 \rangle , \langle 0.70, 0.28 \rangle &{} \langle 0.31,0.63 \rangle , \langle 0.73, 0.22 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_7} &{} \langle 0.76,0.30 \rangle , \langle 0.92, 0.06 \rangle &{} \langle 0.80,0.19 \rangle , \langle 0.82, 0.09 \rangle &{} \langle 0.76,0.26 \rangle , \langle 0.85, 0.13 \rangle &{} \langle 0.79,0.30 \rangle , \langle 0.82, 0.12 \rangle &{} \langle 0.65,0.50 \rangle , \langle 0.82, 0.12 \rangle &{} \langle 0.64,0.39 \rangle , \langle 0.86, 0.10 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_8} &{} \langle 0.82,0.24 \rangle , \langle 0.90, 0.06 \rangle &{} \langle 0.87,0.32 \rangle , \langle 0.92, 0.06 \rangle &{} \langle 0.86,0.19 \rangle , \langle 0.92, 0.06 \rangle &{} \langle 0.75,0.40 \rangle , \langle 0.91, 0.07 \rangle &{} \langle 0.86,0.24 \rangle , \langle 0.93, 0.03 \rangle &{} \langle 0.79,0.33 \rangle , \langle 0.91, 0.06 \rangle \\ \end{bmatrix} \\ \tiny{} & {} \mathfrak {A}^{3}_{ij}=\begin{bmatrix} &{} {\mathfrak {S}_1} &{} {\mathfrak {S}_2} &{} {\mathfrak {S}_3} &{} {\mathfrak {S}_4}&{} {\mathfrak {S}_5}&{} {\mathfrak {S}_6}\\ {\mathfrak {R}_1} &{} \langle 0.68,0.40 \rangle , \langle 0.70, 0.24 \rangle &{} \langle 0.74,0.26 \rangle , \langle 0.82, 0.17 \rangle &{} \langle 0.57,0.48 \rangle , \langle 0.78, 0.21 \rangle &{} \langle 0.64,0.38 \rangle , \langle 0.81, 0.16 \rangle &{} \langle 0.76,0.15 \rangle , \langle 0.80, 0.18 \rangle &{} \langle 0.72,0.36 \rangle , \langle 0.85, 0.17 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_2} &{} \langle 0.73, 0.35 \rangle , \langle 0.82, 0.17 \rangle &{} \langle 0.57,0.45 \rangle , \langle 0.72, 0.18 \rangle &{} \langle 0.65,0.41 \rangle , \langle 0.74, 0.17 \rangle &{} \langle 0.51,0.46 \rangle , \langle 0.75, 0.19 \rangle &{} \langle 0.74,0.23 \rangle , \langle 0.80, 0.15 \rangle &{} \langle 0.50,0.47 \rangle , \langle 0.80, 0.17 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_3} &{} \langle 0.45,0.53 \rangle , \langle 0.62, 0.24 \rangle &{} \langle 0.49,0.54 \rangle , \langle 0.55, 0.41 \rangle &{} \langle 0.52,0.47 \rangle , \langle 0.64, 0.31 \rangle &{} \langle 0.47,0.38 \rangle , \langle 0.54, 0.36 \rangle &{} \langle 0.52,0.63 \rangle , \langle 0.65, 0.31 \rangle &{} \langle 0.49,0.56 \rangle , \langle 0.76, 0.22 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_4} &{} \langle 0.74,0.32 \rangle , \langle 0.80, 0.17 \rangle &{} \langle 0.54,0.51 \rangle , \langle 0.68, 0.30 \rangle &{} \langle 0.74,0.24 \rangle , \langle 0.85, 0.10 \rangle &{} \langle 0.50,0.47 \rangle , \langle 0.58, 0.32 \rangle &{} \langle 0.65,0.39 \rangle , \langle 0.70, 0.26 \rangle &{} \langle 0.71,0.24 \rangle , \langle 0.75, 0.19 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_5} &{} \langle 0.64,0.32 \rangle , \langle 0.75, 0.21 \rangle &{} \langle 0.69,0.43 \rangle , \langle 0.80, 0.19 \rangle &{} \langle 0.61,0.46 \rangle , \langle 0.70, 0.26 \rangle &{} \langle 0.50,0.62 \rangle , \langle 0.65, 0.34 \rangle &{} \langle 0.60,0.41 \rangle , \langle 0.73, 0.26 \rangle &{} \langle 0.62,0.36 \rangle , \langle 0.46, 0.51 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_6} &{} \langle 0.40,0.67 \rangle , \langle 0.75, 0.19 \rangle &{} \langle 0.37,0.65 \rangle , \langle 0.72, 0.26 \rangle &{} \langle 0.33,0.65 \rangle , \langle 0.77, 0.19 \rangle &{} \langle 0.38,0.69 \rangle , \langle 0.72, 0.26 \rangle &{} \langle 0.32,0.71 \rangle , \langle 0.76, 0.12 \rangle &{} \langle 0.24,0.74 \rangle , \langle 0.80, 0.16 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_7} &{} \langle 0.79,0.24 \rangle , \langle 0.89, 0.10 \rangle &{} \langle 0.75,0.31 \rangle , \langle 0.80, 0.16 \rangle &{} \langle 0.74,0.30 \rangle , \langle 0.87, 0.10 \rangle &{} \langle 0.82,0.24 \rangle , \langle 0.82, 0.16 \rangle &{} \langle 0.61,0.49 \rangle , \langle 0.84, 0.13 \rangle &{} \langle 0.68,0.36 \rangle , \langle 0.83, 0.12 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_8} &{} \langle 0.79,0.30 \rangle , \langle 0.84, 0.11 \rangle &{} \langle 0.89,0.23 \rangle , \langle 0.90, 0.06 \rangle &{} \langle 0.79,0.22 \rangle , \langle 0.90, 0.09 \rangle &{} \langle 0.81,0.26 \rangle , \langle 0.92, 0.06 \rangle &{} \langle 0.79,0.32 \rangle , \langle 0.92, 0.06 \rangle &{} \langle 0.86,0.30 \rangle , \langle 0.88, 0.09 \rangle \\ \end{bmatrix}\\ \tiny{} & {} \mathfrak {A}^{4}_{ij}=\begin{bmatrix} &{} {\mathfrak {S}_1} &{} {\mathfrak {S}_2} &{} {\mathfrak {S}_3} &{} {\mathfrak {S}_4}&{} {\mathfrak {S}_5}&{} {\mathfrak {S}_6}\\ {\mathfrak {R}_1} &{} \langle 0.72,0.34 \rangle , \langle 0.77, 0.14 \rangle &{} \langle 0.82,0.14 \rangle , \langle 0.91, 0.06 \rangle &{} \langle 0.57,0.31 \rangle , \langle 0.68, 0.31 \rangle &{} \langle 0.42,0.73 \rangle , \langle 0.63, 0.24 \rangle &{} \langle 0.81,0.14 \rangle , \langle 0.89, 0.10 \rangle &{} \langle 0.75,0.31 \rangle , \langle 0.81, 0.14 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_2} &{} \langle 0.86, 0.17 \rangle , \langle 0.90, 0.02 \rangle &{} \langle 0.84,0.34 \rangle , \langle 0.90, 0.12 \rangle &{} \langle 0.75,0.31 \rangle , \langle 0.85, 0.12 \rangle &{} \langle 0.72,0.23 \rangle , \langle 0.80, 0.13 \rangle &{} \langle 0.70,0.34 \rangle , \langle 0.79, 0.20 \rangle &{} \langle 0.47,0.61 \rangle , \langle 0.82, 0.12 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_3} &{} \langle 0.53,0.48 \rangle , \langle 0.61, 0.32 \rangle &{} \langle 0.63,0.34 \rangle , \langle 0.65, 0.32 \rangle &{} \langle 0.56,0.45 \rangle , \langle 0.60, 0.35 \rangle &{} \langle 0.61,0.34 \rangle , \langle 0.69, 0.26 \rangle &{} \langle 0.63,0.45 \rangle , \langle 0.65, 0.32 \rangle &{} \langle 0.62,0.40 \rangle , \langle 0.82, 0.12 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_4} &{} \langle 0.78,0.36 \rangle , \langle 0.82, 0.16 \rangle &{} \langle 0.65,0.40 \rangle , \langle 0.75, 0.18 \rangle &{} \langle 0.79,0.26 \rangle , \langle 0.80, 0.12 \rangle &{} \langle 0.54,0.46 \rangle , \langle 0.61, 0.39 \rangle &{} \langle 0.61,0.42 \rangle , \langle 0.69, 0.24 \rangle &{} \langle 0.69,0.34 \rangle , \langle 0.71, 0.26 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_5} &{} \langle 0.66,0.41 \rangle , \langle 0.82, 0.16 \rangle &{} \langle 0.80,0.24 \rangle , \langle 0.82, 0.15 \rangle &{} \langle 0.48,0.60 \rangle , \langle 0.59, 0.40 \rangle &{} \langle 0.54,0.56 \rangle , \langle 0.70, 0.26 \rangle &{} \langle 0.65,0.39 \rangle , \langle 0.75, 0.14 \rangle &{} \langle 0.45,0.59 \rangle , \langle 0.53, 0.42 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_6} &{} \langle 0.45,0.62 \rangle , \langle 0.69, 0.28 \rangle &{} \langle 0.31,0.72 \rangle , \langle 0.79, 0.16 \rangle &{} \langle 0.46,0.60 \rangle , \langle 0.69, 0.36 \rangle &{} \langle 0.42,0.56 \rangle , \langle 0.64, 0.31 \rangle &{} \langle 0.38,0.69 \rangle , \langle 0.82, 0.12 \rangle &{} \langle 0.35,0.70 \rangle , \langle 0.75, 0.21 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_7} &{} \langle 0.81,0.16 \rangle , \langle 0.85, 0.13 \rangle &{} \langle 0.71,0.36 \rangle , \langle 0.82, 0.16 \rangle &{} \langle 0.75,0.31 \rangle , \langle 0.85, 0.12 \rangle &{} \langle 0.75,0.30 \rangle , \langle 0.79, 0.20 \rangle &{} \langle 0.60,0.39 \rangle , \langle 0.81, 0.10 \rangle &{} \langle 0.70,0.31 \rangle , \langle 0.81, 0.18 \rangle \\ &{}&{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_8} &{} \langle 0.75,0.35 \rangle , \langle 0.87, 0.10 \rangle &{} \langle 0.82,0.24 \rangle , \langle 0.91, 0.07 \rangle &{} \langle 0.84,0.26 \rangle , \langle 0.91, 0.05 \rangle &{} \langle 0.79,0.32 \rangle , \langle 0.94, 0.07 \rangle &{} \langle 0.83,0.19 \rangle , \langle 0.96, 0.03 \rangle &{} \langle 0.73,0.36 \rangle , \langle 0.92, 0.04 \rangle \\ \end{bmatrix}\end{aligned}$$ -
*
Step 2: The Aggregated matrix is computed by ultilizing the formula 1.
$$\begin{aligned} {\mathfrak {A}_{i}{j}}=\begin{bmatrix} &{} {\mathfrak {S}_{1}} &{} {\mathfrak {S}_{2}} &{} {\mathfrak {S}_{3}} &{} {\mathfrak {S}_{4}}&{} {\mathfrak {S}_{5}}&{} {\mathfrak {S}_{6}}\\ {\mathfrak {R}_{1}} &{} \langle 0.7349,0.2881 \rangle &{} \langle 0.7799,0.2252 \rangle &{} \langle 0.6392,0.4119 \rangle &{} \langle 0.5813,0.4262 \rangle &{} \langle 0.7649,0.1963 \rangle &{} \langle 0.7163,0.3433 \rangle \\ &{} \langle 0.7844,0.1530 \rangle &{} \langle 0.8391,0.1313 \rangle &{} \langle 0.7871,0.1950 \rangle &{} \langle 0.7601,0.1832 \rangle &{} \langle 0.8204,0.1331 \rangle &{} \langle 0.8528,0.1405 \rangle \\ &{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_{2}} &{} \langle 0.6810,0.3933 \rangle &{} \langle 0.6287,0.4259 \rangle &{} \langle 0.7136,0.4155 \rangle &{} \langle 0.5880,0.4010 \rangle &{} \langle 0.6554,0.3272 \rangle &{} \langle 0.4859,0.5448 \rangle \\ &{} \langle 0.7850,0.1355 \rangle &{} \langle 0.7619,0.2048 \rangle &{} \langle 0.7994,0.1284 \rangle &{} \langle 0.7702,0.1700 \rangle &{} \langle 0.7843,0.1529 \rangle &{} \langle 0.7935,0.1548 \rangle \\ &{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_{3}} &{} \langle 0.4776,0.5140 \rangle &{} \langle 0.5248,0.4754 \rangle &{} \langle 0.5543,0.4924 \rangle &{} \langle 0.5737,0.3639 \rangle &{} \langle 0.5887,0.4892 \rangle &{} \langle 0.5408,0.5116 \rangle \\ &{} \langle 0.5993,0.2956 \rangle &{} \langle 0.5955,0.3667 \rangle &{} \langle 0.6103,0.3475 \rangle &{} \langle 0.6579,0.2244 \rangle &{} \langle 0.6625,0.2727 \rangle &{} \langle 0.7825,0.1814 \rangle \\ &{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_{4}} &{} \langle 0.7431,0.3426 \rangle &{} \langle 0.6017,0.4542 \rangle &{} \langle 0.7538,0.2688 \rangle &{} \langle 0.4943,0.4763 \rangle &{} \langle 0.6433,0.3950 \rangle &{} \langle 0.6902,0.3024 \rangle \\ &{} \langle 0.8107,0.1648 \rangle &{} \langle 0.7161,0.2226 \rangle &{} \langle 0.8245,0.1301 \rangle &{} \langle 0.5729,0.3785 \rangle &{} \langle 0.7182,0.2236 \rangle &{} \langle 0.7277,0.2293 \rangle \\ &{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_{5}} &{} \langle 0.6398,0.3970 \rangle &{} \langle 0.7336,0.3595 \rangle &{} \langle 0.5569,0.5005 \rangle &{} \langle 0.4838,0.5834 \rangle &{} \langle 0.6315,0.3998 \rangle &{} \langle 0.5502,0.4749 \rangle \\ &{} \langle 0.7650,0.1974 \rangle &{} \langle 0.8244,0.1422 \rangle &{} \langle 0.6612,0.3016 \rangle &{} \langle 0.6929,0.2626 \rangle &{} \langle 0.7250,0.2270 \rangle &{} \langle 0.5304,0.4045 \rangle \\ &{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_{6}}&{} \langle 0.3756,0.6565 \rangle &{} \langle 0.3606,0.6819 \rangle &{} \langle 0.3814,0.6340 \rangle &{} \langle 0.4064,0.6267 \rangle &{} \langle 0.3624,0.6716 \rangle &{} \langle 0.2788,0.7119 \rangle \\ &{} \langle 0.7547,0.2056 \rangle &{} \langle 0.7687,0.2024 \rangle &{} \langle 0.7406,0.2386 \rangle &{} \langle 0.6924,0.2861 \rangle &{} \langle 0.7565,0.1653 \rangle &{} \langle 0.7579,0.2001 \rangle \\ &{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_{7}}&{} \langle 0.7979,0.2186 \rangle &{} \langle 0.7675,0.2516 \rangle &{} \langle 0.7584,0.2931 \rangle &{} \langle 0.7803,0.2930 \rangle &{} \langle 0.6194,0.4463 \rangle &{} \langle 0.6810,0.3675 \rangle \\ &{} \langle 0.8910,0.0950 \rangle &{} \langle 0.8206,0.1366 \rangle &{} \langle 0.8689,0.1079 \rangle &{} \langle 0.8094,0.1673 \rangle &{} \langle 0.8241,0.1242 \rangle &{} \langle 0.8220,0.1439 \rangle \\ &{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_{8}} &{} \langle 0.7803,0.2967 \rangle &{} \langle 0.8678,0.2464 \rangle &{} \langle 0.8175,0.2298 \rangle &{} \langle 0.7859,0.3200 \rangle &{} \langle 0.8177,0.2622 \rangle &{} \langle 0.8169,0.3074 \rangle \\ &{} \langle 0.8527,0.1082 \rangle &{} \langle 0.9078,0.0643 \rangle &{} \langle 0.9167,0.0650 \rangle &{} \langle 0.9208,0.0680 \rangle &{} \langle 0.9297,0.0471 \rangle &{} \langle 0.8963,0.0720 \rangle \\ &{}&{}&{}&{}&{}&{}\\ \end{bmatrix} \\ \mathfrak {A}_{ij}=\begin{bmatrix} {lllllll} &{} {\mathfrak {S}_{1}} &{} {\mathfrak {S}_{2}} &{} {\mathfrak {S}_{3}} &{} {\mathfrak {S}_{4}}&{} {\mathfrak {S}_{5}}&{} {\mathfrak {S}_{6}}\\ { \mathfrak {R}_{1 }} &{} \langle 0.7349,0.2881 \rangle &{} \langle 0.7799,0.2252 \rangle &{} \langle 0.6392,0.4119 \rangle &{} \langle 0.5813,0.4262 \rangle &{} \langle 0.7649,0.1963 \rangle &{} \langle 0.7163,0.3433 \rangle \\ &{} \langle 0.7844,0.1530 \rangle &{} \langle 0.8391,0.1313 \rangle &{} \langle 0.7871,0.1950 \rangle &{} \langle 0.7601,0.1832 \rangle &{} \langle 0.8204,0.1331 \rangle &{} \langle 0.8528,0.1405 \rangle \\ &{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_{2}} &{} \langle 0.6810,0.3933 \rangle &{} \langle 0.6287,0.4259 \rangle &{} \langle 0.7136,0.4155 \rangle &{} \langle 0.5880,0.4010 \rangle &{} \langle 0.6554,0.3272 \rangle &{} \langle 0.4859,0.5448 \rangle \\ &{} \langle 0.7850,0.1355 \rangle &{} \langle 0.7619,0.2048 \rangle &{} \langle 0.7994,0.1284 \rangle &{} \langle 0.7702,0.1700 \rangle &{} \langle 0.7843,0.1529 \rangle &{} \langle 0.7935,0.1548 \rangle \\ &{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_{3}} &{} \langle 0.4776,0.5140 \rangle &{} \langle 0.5248,0.4754 \rangle &{} \langle 0.5543,0.4924 \rangle &{} \langle 0.5737,0.3639 \rangle &{} \langle 0.5887,0.4892 \rangle &{} \langle 0.5408,0.5116 \rangle \\ &{} \langle 0.5993,0.2956 \rangle &{} \langle 0.5955,0.3667 \rangle &{} \langle 0.6103,0.3475 \rangle &{} \langle 0.6579,0.2244 \rangle &{} \langle 0.6625,0.2727 \rangle &{} \langle 0.7825,0.1814 \rangle \\ &{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_{4}} &{} \langle 0.7431,0.3426 \rangle &{} \langle 0.6017,0.4542 \rangle &{} \langle 0.7538,0.2688 \rangle &{} \langle 0.4943,0.4763 \rangle &{} \langle 0.6433,0.3950 \rangle &{} \langle 0.6902,0.3024 \rangle \\ &{} \langle 0.8107,0.1648 \rangle &{} \langle 0.7161,0.2226 \rangle &{} \langle 0.8245,0.1301 \rangle &{} \langle 0.5729,0.3785 \rangle &{} \langle 0.7182,0.2236 \rangle &{} \langle 0.7277,0.2293 \rangle \\ &{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_{5}} &{} \langle 0.6398,0.3970 \rangle &{} \langle 0.7336,0.3595 \rangle &{} \langle 0.5569,0.5005 \rangle &{} \langle 0.4838,0.5834 \rangle &{} \langle 0.6315,0.3998 \rangle &{} \langle 0.5502,0.4749 \rangle \\ &{} \langle 0.7650,0.1974 \rangle &{} \langle 0.8244,0.1422 \rangle &{} \langle 0.6612,0.3016 \rangle &{} \langle 0.6929,0.2626 \rangle &{} \langle 0.7250,0.2270 \rangle &{} \langle 0.5304,0.4045 \rangle \\ &{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_{6}}&{} \langle 0.3756,0.6565 \rangle &{} \langle 0.3606,0.6819 \rangle &{} \langle 0.3814,0.6340 \rangle &{} \langle 0.4064,0.6267 \rangle &{} \langle 0.3624,0.6716 \rangle &{} \langle 0.2788,0.7119 \rangle \\ &{} \langle 0.7547,0.2056 \rangle &{} \langle 0.7687,0.2024 \rangle &{} \langle 0.7406,0.2386 \rangle &{} \langle 0.6924,0.2861 \rangle &{} \langle 0.7565,0.1653 \rangle &{} \langle 0.7579,0.2001 \rangle \\ &{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_{7}}&{} \langle 0.7979,0.2186 \rangle &{} \langle 0.7675,0.2516 \rangle &{} \langle 0.7584,0.2931 \rangle &{} \langle 0.7803,0.2930 \rangle &{} \langle 0.6194,0.4463 \rangle &{} \langle 0.6810,0.3675 \rangle \\ &{} \langle 0.8910,0.0950 \rangle &{} \langle 0.8206,0.1366 \rangle &{} \langle 0.8689,0.1079 \rangle &{} \langle 0.8094,0.1673 \rangle &{} \langle 0.8241,0.1242 \rangle &{} \langle 0.8220,0.1439 \rangle \\ &{}&{}&{}&{}&{}&{}\\ {\mathfrak {R}_{8}} &{} \langle 0.7803,0.2967 \rangle &{} \langle 0.8678,0.2464 \rangle &{} \langle 0.8175,0.2298 \rangle &{} \langle 0.7859,0.3200 \rangle &{} \langle 0.8177,0.2622 \rangle &{} \langle 0.8169,0.3074 \rangle \\ &{} \langle 0.8527,0.1082 \rangle &{} \langle 0.9078,0.0643 \rangle &{} \langle 0.9167,0.0650 \rangle &{} \langle 0.9208,0.0680 \rangle &{} \langle 0.9297,0.0471 \rangle &{} \langle 0.8963,0.0720 \rangle \\ &{}&{}&{}&{}&{}&{}\\ \end{bmatrix} \end{aligned}$$ -
*
Step 3: Using the formula 2, 3, 4 the closeness coefficient of each alternative is calculated, as given in Table 3.
-
*
Step 4: Utilizing the values in Table 3 and the formula in Step 5, the extended LDF-matrix \(\mathfrak {G}\) is constructed.
$$\begin{aligned} \mathfrak {G} = \begin{bmatrix} 0.7656 &{} 0.8124 &{} 0.6967 &{} 0.6738 &{} 0.8091 &{} 0.7603\\ 0.7234 &{} 0.6829 &{} 0.7288 &{} 0.6870 &{} 0.7324 &{} 0.6279\\ 0.5646 &{} 0.5689 &{} 0.5802 &{} 0.6573 &{} 0.6191 &{} 0.6442\\ 0.7550 &{} 0.6545 &{} 0.7895 &{} 0.5526 &{} 0.6820 &{} 0.7205\\ 0.6962 &{} 0.7541 &{} 0.6013 &{} 0.5769 &{} 0.6784 &{} 0.5501\\ 0.5570 &{} 0.5510 &{} 0.5551 &{} 0.5423 &{} 0.5583 &{} 0.5249\\ 0.8363 &{} 0.7962 &{} 0.7951 &{} 0.7787 &{} 0.7005 &{} 0.7370\\ 0.7973 &{} 0.8521 &{} 0.8469 &{} 0.8074 &{} 0.8396 &{} 0.8155\\ 0.8363 &{} 0.8521 &{} 0.8469 &{} 0.8074 &{} 0.5583 &{} 0.8155\\ 0.5570 &{} 0.5510 &{} 0.5551 &{} 0.5423 &{} 0.5396 &{} 0.5249\\ \end{bmatrix} \end{aligned}$$ -
*
Step 5: Normalized LDF-matrix is computed as \(\check{\mathfrak {G}}\).
$$\begin{aligned} \check{\mathfrak {G}} =\begin{bmatrix} 0.9155 &{} 0.9534 &{} 0.8226 &{} 0.8345 &{} 0.6900 &{} 0.9323\\ 0.8650 &{} 0.8014 &{} 0.8606 &{} 0.8509 &{} 0.7623 &{} 0.7700\\ 0.6751 &{} 0.6676 &{} 0.6851 &{} 0.8141 &{} 0.9018 &{} 0.7899\\ 0.9028 &{} 0.7681 &{} 0.9322 &{} 0.6844 &{} 0.8186 &{} 0.8835\\ 0.8325 &{} 0.8850 &{} 0.7100 &{} 0.7145 &{} 0.8230 &{} 0.6746\\ 0.6660 &{} 0.6466 &{} 0.6554 &{} 0.6717 &{} 1 &{} 0.6437\\ 1 &{} 0.9344 &{} 0.9388 &{} 0.9645 &{} 0.7246 &{} 0.9037\\ 0.9534 &{} 1 &{} 1 &{} 1 &{} 0.6650 &{} 1\\ 0.8363 &{} 0.8521 &{} 0.8469 &{} 0.8074 &{} 0.5583 &{} 0.8155\\ 0.5570 &{} 0.5510 &{} 0.5551 &{} 0.5423 &{} 0.5396 &{} 0.5249\\ \end{bmatrix} \end{aligned}$$ -
*
Step 6: The weighted LDF-matrix is computed as \(\mathfrak {P}\) with the weights \(\mathfrak {w}_j (j = 1,2,3,4,5,6)\) estimated in the earlier steps.
$$\begin{aligned} \mathfrak {P} = \begin{bmatrix} 0.1419 &{} 0.1401 &{} 0.1431 &{} 0.1636 &{} 0.1076 &{} 0.1604 \\ 0.1341 &{} 0.1178 &{} 0.1497 &{} 0.1668 &{} 0.1189 &{} 0.1324 \\ 0.1046 &{} 0.0981 &{} 0.1192 &{} 0.1596 &{} 0.1407 &{} 0.1359\\ 0.1399 &{} 0.1129 &{} 0.1622 &{} 0.1341 &{} 0.1277 &{} 0.1520\\ 0.1290 &{} 0.1301 &{} 0.1235 &{} 0.1400 &{} 0.1284 &{} 0.1160\\ 0.1032 &{} 0.0951 &{} 0.1140 &{} 0.1317 &{} 0.1560 &{} 0.1107\\ 0.155 &{} 0.1374 &{} 0.1634 &{} 1890 &{} 0.1130 &{} 0.1154\\ 0.1478 &{} 0.147 &{} 0.174 &{} 0.196 &{} 0.1037 &{} 0.172\\ 0.1296 &{} 0.1253 &{} 0.1474 &{} 0.1583 &{} 0.0871 &{} 0.1403\\ 0.0863 &{} 0.0810 &{} 0.0966 &{} 0.1063 &{} 0.1310 &{} 0.0903\\ \end{bmatrix} \end{aligned}$$ -
*
Step 7: The utility function of each alternative is computed in Table 4 using the formula 6, 7, 8, 9, 10.
-
*
Step 8: From the table, the ranking of alternatives is \(\mathfrak {R}_8> \mathfrak {R}_7> \mathfrak {R}_1> \mathfrak {R}_4> \mathfrak {R}_2> \mathfrak {R}_3> \mathfrak {R}_5 > \mathfrak {R}_6\).
5 Results and discussion
In this section, the comparative and sensitivity analyses of our proposed methodology are addressed. Also, the limitations and practical implications of our proposed method are discussed.
5.1 Comparative study
Table 5 provides a comparison of the suggested technique with a few other techniques.
The capacity of the Fuzzy MARCOS approach to more skillfully manage the ambiguity and uncertainties present in decision-making processes is a significant benefit over the classic MARCOS method. LDF MARCOS provides a more accurate and subtle way to determine the degree of utility, enabling a more accurate depiction of decision-maker preferences in complex and unpredictable contexts. It does this by combining fuzzy reference points and utility functions. Due to this improvement, LDF MARCOS outperforms traditional MARCOS when optimizing several goals under uncertain situations, producing more reasonable and consistent outcomes, especially when processing big datasets and dynamic contexts.
5.2 Sensitivity analysis
In this study, a sensitivity analysis was carried out on the weight given to the four decision-makers. In the proposed approach, the weights of the experts were given in the order of \(\mathfrak {A}_3> \mathfrak {A}_1> \mathfrak {A}_4 > \mathfrak {A}_2\). Here, we consider two cases with a change in the order.
Case 1: \(\mathfrak {u}_1\) = 0.40, \(\mathfrak {u}_2\) = 0.25, \(\mathfrak {u}_3\) = 0.20, \(\mathfrak {u}_4\) = 0.15.
-
1.
The weights for the criteria are determined in the table 6.
$$\begin{aligned} \mathfrak {G}= & {} \begin{bmatrix} 0.7814 &{} 0.8365 &{} 0.7047 &{} 0.6321 &{} 0.8277 &{} 0.7654\\ 0.7539 &{} 0.7168 &{} 0.7425 &{} 0.7173 &{} 0.7159 &{} 0.6198\\ 0.5696 &{} 0.5949 &{} 0.5677 &{} 0.6817 &{} 0.6440 &{} 0.6659\\ 0.7423 &{} 0.6764 &{} 0.7862 &{} 0.5542 &{} 0.6822 &{} 0.7031\\ 0.6949 &{} 0.7765 &{} 0.5732 &{} 0.5919 &{} 0.6885 &{} 0.5380\\ 0.5564 &{} 0.5516 &{} 0.5517 &{} 0.5434 &{} 0.5492 &{} 0.5277\\ 0.8402 &{} 0.7964 &{} 0.7947 &{} 0.7672 &{} 0.7060 &{} 0.7381\\ 0.7935 &{} 0.8468 &{} 0.8498 &{} 0.7984 &{}0.8548 &{} 0.8064\\ 0.8402 &{} 0.8468 &{} 0.8498 &{} 0.7984 &{} 0.5492 &{} 0.8064\\ 0.5564 &{} 0.5516 &{} 0.5517 &{} 0.5542 &{} 0.8548 &{} 0.5277\\ \end{bmatrix}\\{} & {} \check{\mathfrak {G}} = \begin{bmatrix} 0.9300 &{} 0.9878 &{} 0.8293 &{} 0.7917 &{} 0.6635 &{} 0.9492\\ 0.8973 &{} 0.8465 &{} 0.8737 &{} 0.8984 &{} 0.7671 &{} 0.7686\\ 0.6779 &{} 0.7025 &{} 0.6680 &{} 0.8538 &{} 0.8528 &{} 0.8258\\ 0.8835 &{} 0.7988 &{} 0.9252 &{} 0.6941 &{} 0.8050 &{} 0.8719\\ 0.8271 &{} 0.9170 &{} 0.6745 &{} 0.7414 &{} 0.7977 &{} 0.6672\\ 0.6622 &{} 0.6514 &{} 0.6492 &{} 0.6806 &{} 1 &{} 0.6544\\ 1 &{} 0.9405 &{} 0.9352 &{} 0.9609 &{} 0.7779 &{} 0.9153\\ 0.9444 &{} 1 &{} 1 &{} 1 &{} 0.6425 &{} 1\\ \end{bmatrix}\\{} & {} \mathfrak {P} = \begin{bmatrix} 0.1572 &{} 0.1413 &{} 0.1410 &{} 0.1536 &{} 0.1022 &{} 0.1614\\ 0.1516 &{} 0.1210 &{} 0.1485 &{} 0.1743 &{} 0.1181 &{} 0.1307\\ 0.1146 &{} 0.1005 &{} 0.1136 &{} 0.1656 &{} 0.1313 &{} 0.1404\\ 0.1493 &{} 0.1142 &{} 0.1573 &{} 0.1347 &{} 0.1240 &{} 0.1482\\ 0.1398 &{} 0.1311 &{} 0.1147 &{} 0.1438 &{} 0.1228 &{} 0.1134\\ 0.1119 &{} 0.0932 &{} 0.1104 &{} 0.1320 &{} 0.1540 &{} 0.1112\\ 0.1690 &{} 0.1345 &{} 0.1590 &{} 0.1864 &{} 0.1198 &{} 0.1556\\ 0.1596 &{} 0.1430 &{} 0.1700 &{} 0.1940 &{} 0.0990 &{} 0.1700\\ 0.1420 &{} 0.1211 &{} 0.1445 &{} 0.1549 &{} 0.0846 &{} 0.1371\\ 0.0940 &{} 0.0789 &{} 0.0938 &{} 0.1075 &{} 0.1316 &{} 0.0897\\ \end{bmatrix} \end{aligned}$$ -
2.
The utility function of each alternative is computed in Table 7 using the formula.
Case:2 \(\mathfrak {u}_1\) = 0.40, \(\mathfrak {u}_2\) = 0.25, \(\mathfrak {u}_3\) = 0.20, \(\mathfrak {u}_4\) = 0.15.
-
1.
The weights for the criteria are determined in the table 8.
-
2.
The extended LDF-matrix \(\mathfrak {G}\), normalized LDF-matrix \(\check{\mathfrak {G}}\) and weighted LDF-matrix \(\mathfrak {P}\) were computed.
$$\begin{aligned} \mathfrak {G}= & {} \begin{bmatrix} 0.7814 &{} 0.8365 &{} 0.7047 &{} 0.6321 &{} 0.8277 &{} 0.7654\\ 0.7539 &{} 0.7168 &{} 0.7425 &{} 0.7173 &{} 0.7159 &{} 0.6198\\ 0.5696 &{} 0.5949 &{} 0.5677 &{} 0.6817 &{} 0.6440 &{} 0.6659\\ 0.7423 &{} 0.6764 &{} 0.7862 &{} 0.5542 &{} 0.6822 &{} 0.7031\\ 0.6949 &{} 0.7765 &{} 0.5732 &{} 0.5919 &{} 0.6885 &{} 0.5380\\ 0.5564 &{} 0.5516 &{} 0.5517 &{} 0.5434 &{} 0.5492 &{} 0.5277\\ 0.8402 &{} 0.7964 &{} 0.7947 &{} 0.7672 &{} 0.7060 &{} 0.7381\\ 0.7935 &{} 0.8468 &{} 0.8498 &{} 0.7984 &{} 0.8548 &{} 0.8064\\ 0.8402 &{} 0.8468 &{} 0.8498 &{} 0.7984 &{} 0.5492 &{} 0.8064\\ 0.5564 &{} 0.5516 &{} 0.5517 &{} 0.5434 &{} 0.8548 &{} 0.5277\\ \end{bmatrix}\\ \check{\mathfrak {G}}= & {} \begin{bmatrix} 0.9300 &{} 0.9878 &{} 0.8293 &{} 0.7917 &{} 0.6635 &{} 0.9492\\ 0.8973 &{} 0.8465 &{} 0.8737 &{} 0.8984 &{} 0.7671 &{} 0.7686\\ 0.6779 &{} 0.7025 &{} 0.6680 &{} 0.8538 &{} 0.8528 &{} 0.8258\\ 0.8835 &{} 0.7988 &{} 0.9252 &{} 0.6941 &{} 0.8050 &{} 0.8719\\ 0.8271 &{} 0.9170 &{} 0.6745 &{} 0.7414 &{} 0.7977 &{} 0.6672\\ 0.6622 &{} 0.6514 &{} 0.6492 &{} 0.6806 &{} 1 &{} 0.6544\\ 1 &{} 0.9405 &{} 0.9352 &{} 0.9609 &{} 0.7779 &{} 0.9153\\ 0.9444 &{} 1 &{} 1 &{} 1 &{} 0.6425 &{} 1\\ \end{bmatrix}\\ \mathfrak {P}= & {} \begin{bmatrix} 0.1693 &{} 0.1413 &{} 0.1360 &{} 0.1480 &{} 0.1009 &{} 0.1633\\ 0.1633 &{} 0.1210 &{} 0.1433 &{} 0.1680 &{} 0.1166 &{} 0.1322\\ 0.1234 &{} 0.1005 &{} 0.1096 &{} 0.1597 &{} 0.1296 &{} 0.1420\\ 0.1608 &{} 0.1142 &{} 0.1517 &{} 0.1298 &{} 0.1224 &{} 0.1500\\ 0.1505 &{} 0.1311 &{} 0.1106 &{} 0.1386 &{} 0.1213 &{} 0.1148\\ 0.1205 &{} 0.0932 &{} 0.1065 &{} 0.1273 &{} 0.1520 &{} 0.1126\\ 0.182 &{} 0.1345 &{} 0.1534 &{} 0.1797 &{} 0.1182 &{} 0.1574\\ 0.1719 &{} 0.143 &{} 0.164 &{} 0.1870 &{} 0.0977 &{} 0.172\\ 0.1529 &{} 0.1211 &{} 0.1394 &{} 0.1493 &{} 0.0835 &{} 0.1387\\ 0.1013 &{} 0.0789 &{} 0.0905 &{} 0.1016 &{} 0.1299 &{} 0.0908\\ \end{bmatrix} \end{aligned}$$ -
3.
The utility function of each alternative is computed in Table 9 using the formula.
Based on these studies and the comparative analysis, we conclude that the results calculated using the suggested technique are conservative because they are compatible with the current research. The main advantage of the proposed technique over the current methods for decision-making is that it uses a large amount of data to interpret ambiguities in the data. Because it communicates object information more accurately and objectively under an LDFS, it is a useful tool for dealing with ambiguous and imprecise information throughout the decision-making process. The primary advantage of this suggested approach is the inclusion of the MARCOS method, which provides a more precise weighting of qualities.
The uniqueness of the results obtained from the comparative and sensitivity analyses demonstrates the robustness of the proposed method. From the results, the risk factor " Security concerns" is considered a high risk in IoT devices.
5.3 Limitations of this study
-
1.
There is a chance that some new threats or vulnerabilities pertinent to particular IoT applications or contexts will be left out of the study, which may not cover all possible IoT dangers.
-
2.
Our suggested approach has a computational cost that makes manual calculation impracticable, especially when working with huge datasets. Although it can produce precise results, the large number of algorithmic stages makes manual computing difficult, emphasizing the need for software tools in implementation.
5.4 Practical implications
We will improve the discussion portion of our study to emphasize the following topics in order to make clear the practical consequences of our suggested methodology:
-
1.
Decision Support for Stakeholders: By offering a systematic framework for ranking IoT hazards, our technique helps stakeholders decide on risk management tactics and resource allocation. Organizations may improve the security and resilience of their IoT systems by detecting and mitigating significant hazards.
-
2.
Integration into Risk Management Processes: We will focus on the doable steps involved in incorporating our methodology into the processes that organizations now use for risk management. This entails developing procedures for gathering, analyzing, and making decisions based on data and instructing staff members on how to apply the suggested methodology.
-
3.
We will emphasize the iterative nature of risk management in the context of the Internet of Things, emphasizing the necessity for continual improvement and adaption of risk assessment approaches. Through the adoption of a proactive risk mitigation strategy and the utilization of input from industry experts and stakeholders, organizations can augment their capacity to successfully tackle dynamic risks.
6 Conclusion
This study delves into the complex world of Internet of Things (IoT) technologies, acknowledging how they revolutionize environmental control and communication. We have focused on the dynamic character of these technologies and the requirement for flexible analytical frameworks through a thorough examination of the inherent risks connected to the Internet of Things.
We have been able to rank and comprehend the multitude of dangers in IoT scenarios by applying the Linear Diophantine Fuzzy Set, which has helped us address the enormous uncertainties that frequently characterize this rapidly developing field. Our methodology is made more practical by applying the MARCOS method for risk prioritization. This gives users a useful tool for recognizing and managing critical dangers in IoT systems.
Our results now include a practical component in addition to the validation of the robustness of our suggested technique with the addition of a comparison study and sensitivity analysis. Our goal is to demonstrate the efficacy of our method and offer stakeholders a solid framework for decision-making in a dynamic IoT space. The primary contribution is that the inclusion of MARCOS in the LDF framework improves IoT risk assessments by giving users a way to prioritize hazards in the face of uncertainty and support well-informed decision-making. Through thorough risk assessment and strong technique validation, this strategy promotes awareness and the safe use of IoT technologies.
This study advances the overarching objective of safeguarding the advancement and implementation of IoT technology by raising awareness of IoT hazards and offering useful tools for risk mitigation. The knowledge gathered from this study enables people and organizations to proactively manage risks by traversing the unknowns of the technological future, promoting safer and more sustainable development of IoT technology.
Data availability
All data generated are analysed during this study are included in this article.
Code availability
NA.
References
Abdullah A, Hamad R, Abdulrahman M, Moala H, Elkhediri S (2019) Cybersecurity: a review of internet of things (iot) security issues, challenges and techniques. In: 2019 2nd International Conference on Computer Applications & Information Security (ICCAIS). p 1–6 . https://doi.org/10.1109/CAIS.2019.8769560
Abomhara M, Kien GM (2015) Cyber security and the internet of things: Vulnerabilities, threats, intruders and attacks. J Cyber Sec Mobility. 4(1): 65–88 https://doi.org/10.13052/jcsm2245-1439.414
Ali J (2021) A q-rung orthopair fuzzy marcos method using novel score function and its application to solid waste management. Appl Intell 52(8):8770–8792. https://doi.org/10.1007/s10489-021-02921-2
Aliyeva K, Aliyeva A, Aliyev R, Özdeşer M (2023) Application of fuzzy simple additive weighting method in group decision-making for capital investment. Axioms 12(8):797
Al-Zibaree HKY, Konur M (2023) Fuzzy analytic hierarchal process for sustainable public transport system. J Operat Intell. 1(1): 1–10 https://doi.org/10.31181/jopi1120234
Andrade RO, Yoo SG, Tello-Oquendo L, Ortiz-Garces I (2020) A comprehensive study of the iot cybersecurity in smart cities. IEEE Access 8:228922–228941. https://doi.org/10.1109/access.2020.3046442
Aydos M, Vural Y, Tekerek A (2019) Assessing risks and threats with layered approach to internet of things security. Measure Control 52(5–6):338–353. https://doi.org/10.1177/0020294019837991
Ayub S, Shabir M, Riaz M, Aslam M, Chinram R (2021) Linear diophantine fuzzy relations and their algebraic properties with decision making. Symmetry 13(6):945. https://doi.org/10.3390/sym13060945
Badi I, Pamucar D (2020) Supplier selection for steelmaking company by using combined grey-marcos methods. Decision Making Appl Manag Eng. 3(2): 37–48 https://doi.org/10.31181/dmame2003037b
Boudko S, Abie H (2019) Adaptive cybersecurity framework for healthcare internet of things. In: 2019 13th International Symposium on Medical Information and Communication Technology (ISMICT). p 1–6. https://doi.org/10.1109/ISMICT.2019.8743905
Chattopadhyay R, Chakraborty S, Chakraborty S (2020) An integrated d-marcos method for supplier selection in an iron and steel industry. Decision Making Appl Manag Eng. 3(2), 49–69 https://doi.org/10.31181/dmame2003049c
Chen S-M, Jian W-S (2017) Fuzzy forecasting based on two-factors second-order fuzzy-trend logical relationship groups, similarity measures and pso techniques. Inf Sci 391–392:65–79. https://doi.org/10.1016/j.ins.2016.11.004
Chen S-M, Lee L-W (2010) Fuzzy decision-making based on likelihood-based comparison relations. IEEE Trans Fuzzy Syst 18(3):613–628. https://doi.org/10.1109/TFUZZ.2010.2045385
Chen S-M, Randyanto Y (2013) A novel similarity measure between intuitionistic fuzzy sets and its applications. Int J Pattern Recognit Artif Intell 27(07):1350021. https://doi.org/10.1142/s0218001413500213
Chen S-M, Cheng S-H, Tsai W-H (2016) Multiple attribute group decision making based on interval-valued intuitionistic fuzzy aggregation operators and transformation techniques of interval-valued intuitionistic fuzzy values. Inf Sci 367–368:418–442. https://doi.org/10.1016/j.ins.2016.05.041
Chen S-M, Zou X-Y, Gunawan GC (2019) Fuzzy time series forecasting based on proportions of intervals and particle swarm optimization techniques. Inf Sci 500:127–139. https://doi.org/10.1016/j.ins.2019.05.047
Daǧıstanlı HA (2024) An interval-valued intuitionistic fuzzy vikor approach for r &d project selection in defense industry investment decisions. J Soft Comput Decision Anal. 2(1), 1–13 https://doi.org/10.31181/jscda21202428
Ecer F, Pamucar D (2021) Marcos technique under intuitionistic fuzzy environment for determining the covid-19 pandemic performance of insurance companies in terms of healthcare services. Appl Soft Comput 104:107199. https://doi.org/10.1016/j.asoc.2021.107199
Farid HMA, Riaz M, Khan MJ, Kumam P, Sitthithakerngkiet K (2022) Sustainable thermal power equipment supplier selection by einstein prioritized linear diophantine fuzzy aggregation operators. AIMS Math 7(6):11201–11242. https://doi.org/10.3934/math.2022627
Ghoushchi S, Sarvi S (2023) Prioritizing and evaluating risks of ordering and prescribing in the chemotherapy process using an extended swara and moora under fuzzy z-numbers. J Operations Intell. 1: 44–66 https://doi.org/10.31181/jopi1120238
Hashmi MR, Tehrim ST, Riaz M, Pamucar D, Cirovic G (2021) Spherical linear diophantine fuzzy soft rough sets with multi-criteria decision making. Axioms 10(3):185. https://doi.org/10.3390/axioms10030185
Iampan A, Santos-García G, Riaz M, Farid HM, Chinram R (2021) Linear diophantine fuzzy Einstein aggregation operators for multi-criteria decision-making problems. J Math. 2021:1–31. https://doi.org/10.1155/2021/5548033
Islam MR, Aktheruzzaman KM (2020) An analysis of cybersecurity attacks against internet of things and security solutions. J Comput Commun 08(04):11–25. https://doi.org/10.4236/jcc.2020.84002
Jayakumar V, Mohideen ABK, Saeed MH, Alsulami H, Hussain A, Saeed M (2023) Development of complex linear diophantine fuzzy soft set in determining a suitable agri-drone for spraying fertilizers and pesticides. IEEE Access 11:9031–9041. https://doi.org/10.1109/access.2023.3239675
Jeevitha K, Garg H, Vimala J, Aljuaid H, Abdel-Aty A-H (2023) Linear diophantine multi-fuzzy aggregation operators and its application in digital transformation. J Intell Fuzzy Syst 45(2):3097–3107. https://doi.org/10.3233/jifs-223844
Kamacı H (2021) Linear diophantine fuzzy algebraic structures. J Ambient Intell Humaniz Comput 12(11):10353–10373. https://doi.org/10.1007/s12652-020-02826-x
Kang D, Anuja A, Narayanamoorthy S, Gangemi M, Ahmadian A (2022) A dual hesitant q-rung orthopair enhanced marcos methodology under uncertainty to determine a used ppe kit disposal. Environ Sci Pollut Res 29(59):89625–89642. https://doi.org/10.1007/s11356-022-21601-3
Kannan J, Jayakumar V, Pethaperumal M, Kather Mohideen AB (2024) An intensified linear diophantine fuzzy combined dematel framework for the assessment of climate crisis. Stoch Env Res Risk Assess. https://doi.org/10.1007/s00477-023-02618-7
Kannan J, Jayakumar V, Saeed M, Alballa T, Khalifa HAE-W, Gomaa HG (2024) Linear diophantine fuzzy clustering algorithm based on correlation coefficient and analysis on logistic efficiency of food products. IEEE Access. 12:34889–34902. https://doi.org/10.1109/access.2024.3371986
KANNAN J, JAYAKUMAR V (2023) Sustainable method for tender selection using linear diophantine multi-fuzzy soft set. Communications Faculty Of Science University of Ankara Series A1Mathematics and Statistics. 72(4), 976–991 https://doi.org/10.31801/cfsuasmas.1255830
Kulik T, Tran-Jørgensen PWV, Boudjadar J, Schultz C (2018) A framework for threat-driven cyber security verification of iot systems. In: 2018 IEEE International Conference on Software Testing, Verification and Validation Workshops (ICSTW). p 89–97 . https://doi.org/10.1109/ICSTW.2018.00033
Kuzlu M, Fair C, Guler O (2021) Role of artificial intelligence in the internet of things (iot) cybersecurity. Discov Internet Things. https://doi.org/10.1007/s43926-020-00001-4
Lopez-Vargas A, Fuentes M, Vivar M (2020) Challenges and opportunities of the internet of things for global development to achieve the united nations sustainable development goals. IEEE Access 8:37202–37213. https://doi.org/10.1109/access.2020.2975472
Machine learning techniques for iot security: Current research and future vision with generative ai and large language models. Internet of Things and Cyber-Physical Systems. 4: 167–185 (2024) https://doi.org/10.1016/j.iotcps.2023.12.003
Mahmood T, Ullah K, Khan Q, Jan N (2018) An approach toward decision-making and medical diagnosis problems using the concept of spherical fuzzy sets. Neural Comput Appl 31(11):7041–7053. https://doi.org/10.1007/s00521-018-3521-2
Mahmoud R, Yousuf T, Aloul F, Zualkernan I (2015) Internet of things (iot) security: Current status, challenges and prospective measures. In: 2015 10th International Conference for Internet Technology and Secured Transactions (ICITST). p 336–341. https://doi.org/10.1109/ICITST.2015.7412116
Mohammad MMS, Abdullah S, Al-Shomrani MM (2022) Some linear diophantine fuzzy similarity measures and their application in decision making problem. IEEE Access. 10:29859–29877. https://doi.org/10.1109/access.2022.3151684
Mu X, Antwi-Afari MF (2024) The applications of internet of things (iot) in industrial management: a science mapping review. Int J Prod Res 62(5):1928–1952. https://doi.org/10.1080/00207543.2023.2290229
Nurse JRC, Creese S, De Roure D (2017) Security risk assessment in internet of things systems. IT Prof 19(5):20–26. https://doi.org/10.1109/mitp.2017.3680959
Petchimuthu S, Riaz M, Kamacı H (2022) Correlation coefficient measures and aggregation operators on interval-valued linear diophantine fuzzy sets and their applications. Comput Appl Math. https://doi.org/10.1007/s40314-022-02077-w
Pethaperumal M, Jeyakumar V, Kannan J, Banu A (2023) An algebraic analysis on exploring q-rung orthopair multi-fuzzy sets. J Fuzzy Ext Appl. 4(3): 235–245 https://doi.org/10.22105/jfea.2023.408513.1302
Popescu T, Popescu A, Prostean G (2021) Iot security risk management strategy reference model (iotsrm2). Future Internet 13(6):148. https://doi.org/10.3390/fi13060148
Puška A, Stojanović I, Maksimović A, Osmanović N (2020) Project management software evaluation by using the measurement of alternatives and ranking according to compromise solution (marcos) method. Operat Res Eng Sci Theory Appl. 3(1): 89–101 https://doi.org/10.31181/oresta2001089p
Radomska-Zalas A (2023) Application of the waspas method in a selected technological process. Procedia Computer Science 225, 177–187 https://doi.org/10.1016/j.procs.2023.10.002 . 27th International Conference on Knowledge Based and Intelligent Information and Engineering Sytems (KES 2023)
Rajareega S, Vimala J (2021) Operations on complex intuitionistic fuzzy soft lattice ordered group and cifs-copras method for equipment selection process. J Intell Fuzzy Syst 41(5):5709–5718. https://doi.org/10.3233/jifs-189890
Riaz M, Hashmi MR (2019) Linear diophantine fuzzy set and its applications towards multi-attribute decision-making problems. J Intell Fuzzy Syst 37(4):5417–5439. https://doi.org/10.3233/jifs-190550
Riaz M, Hashmi MR, Kalsoom H, Pamucar D, Chu Y-M (2020) Linear diophantine fuzzy soft rough sets for the selection of sustainable material handling equipment. Symmetry 12(8):1215. https://doi.org/10.3390/sym12081215
Riaz M, Farid HMA, Aslam M, Pamucar D, Bozanić D (2021) Novel approach for third-party reverse logistic provider selection process under linear diophantine fuzzy prioritized aggregation operators. Symmetry 13(7):1152. https://doi.org/10.3390/sym13071152
Riaz M, Farid HMA, Wang W, Pamucar D (2022) Interval-valued linear diophantine fuzzy frank aggregation operators with multi-criteria decision-making. Mathematics 10(11):1811. https://doi.org/10.3390/math10111811
Rizvi S, Kurtz A, Pfeffer J, Rizvi M (2018) Securing the internet of things (iot): a security taxonomy for iot. In: 2018 17th IEEE International Conference On Trust, Security And Privacy In Computing And Communications/ 12th IEEE International Conference On Big Data Science And Engineering (TrustCom/BigDataSE). p 163–168 . https://doi.org/10.1109/TrustCom/BigDataSE.2018.00034
Sarker IH, Khan AI, Abushark YB, Alsolami F (2022) Internet of things (iot) security intelligence: a comprehensive overview, machine learning solutions and research directions. Mobile Netw Appl 28(1):296–312. https://doi.org/10.1007/s11036-022-01937-3
Simić V, Soušek R, Jovčić S (2020) Picture fuzzy mcdm approach for risk assessment of railway infrastructure. Mathematics 8(12):2259. https://doi.org/10.3390/math8122259
Stanković M, Stević Das DK, Subotić M, Pamučar D (2020) A new fuzzy marcos method for road traffic risk analysis. Mathematics 8(3):457. https://doi.org/10.3390/math8030457
Stević č, Pamučar D, Puška A, Chatterjee P, (2020) Sustainable supplier selection in healthcare industries using a new mcdm method: measurement of alternatives and ranking according to compromise solution (marcos). Comput Ind Eng 140:106231. https://doi.org/10.1016/j.cie.2019.106231
Tawalbeh L, Muheidat F, Tawalbeh M, Quwaider M (2020) Iot privacy and security: challenges and solutions. Appl Sci 10(12):4102. https://doi.org/10.3390/app10124102
Toapanta SMT, Pesantes RPR, Gallegos LEM (2020) Impact of cybersecurity applied to iot in public organizations in latin america. In: 2020 Fourth World Conference on Smart Trends in Systems, Security and Sustainability (WorldS4). p 154–161. https://doi.org/10.1109/WorldS450073.2020.9210416
Torkayesh AE, Hashemkhani Zolfani S, Kahvand M, Khazaelpour P (2021) Landfill location selection for healthcare waste of urban areas using hybrid bwm-grey marcos model based on gis. Sustain Cities Soc 67:102712. https://doi.org/10.1016/j.scs.2021.102712
Tweneboah-Koduah S, Skouby KE, Tadayoni R (2017) Cyber security threats to iot applications and service domains. Wireless Pers Commun 95(1):169–185. https://doi.org/10.1007/s11277-017-4434-6
Ullah F, Naeem H, Jabbar S, Khalid S, Latif MA, Al-turjman F, Mostarda L (2019) Cyber security threats detection in internet of things using deep learning approach. IEEE Access 7:124379–124389. https://doi.org/10.1109/access.2019.2937347
Vimala J, Garg H, Jeevitha K (2023) Prognostication of myocardial infarction using lattice ordered linear diophantine multi-fuzzy soft set. Int J Fuzzy Syst 26(1):44–59. https://doi.org/10.1007/s40815-023-01574-2
Vimala J, Mahalakshmi P, Rahman AU, Saeed M (2023) A customized topsis method to rank the best airlines to fly during covid-19 pandemic with q-rung orthopair multi-fuzzy soft information. Soft Comput 27(20):14571–14584. https://doi.org/10.1007/s00500-023-08976-2
Xiaojian Z, Liandong C, Jie F, Xiangqun W, Qi W (2021) Power iot security protection architecture based on zero trust framework. p 166–170 . https://doi.org/10.1109/CSP51677.2021.9357607
Yager RR (2014) Pythagorean membership grades in multicriteria decision making. IEEE Trans Fuzzy Syst 22(4):958–965. https://doi.org/10.1109/tfuzz.2013.2278989
Yager RR (2017) Generalized orthopair fuzzy sets. IEEE Trans Fuzzy Syst 25(5):1222–1230. https://doi.org/10.1109/tfuzz.2016.2604005
Zadeh LA (1965) Fuzzy sets. Inf Control 8(3):338–353. https://doi.org/10.1016/S0019-9958(65)90241-X
Zhao S, Li S, Qi L, Xu LD (2020) Computational intelligence enabled cybersecurity for the internet of things. IEEE Trans Emerg Topics Comput Intell 4(5):666–674. https://doi.org/10.1109/TETCI.2019.2941757
Zou X-Y, Chen S-M, Fan K-Y (2020) Multiple attribute decision making using improved intuitionistic fuzzy weighted geometric operators of intuitionistic fuzzy values. Inf Sci 535:242–253. https://doi.org/10.1016/j.ins.2020.05.011
Acknowledgements
The article has been written with the joint financial support of RUSA-Phase 2.0 grant sanctioned vide letter No.F 24-51/2014-U, Policy (TN Multi-Gen), Dept. of Edn. Govt. of India, Dt. 09.10.2018, DST-PURSE 2nd Phase Programme vide letter no. SR/PURSE Phase 2/38 (G) Dt. 21.02.2017 and DST (FIST - level I) 657876570 vide letter No.SR/FIST/MS-I/2018/17 Dt. 20.12.2018.
Funding
No funds, grants, or other support was received.
Author information
Authors and Affiliations
Contributions
Conceptualization, methodology, writing - JK; review, editing, and investigation - VJ, NK, MD, XW.
Corresponding authors
Ethics declarations
Conflict of interest
The authors declare no conflict of interest regarding this paper.
Ethical approval
NA.
Consent to participate
NA.
Consent for publication
NA.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made. The images or other third party material in this article are included in the article's Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article's Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Jayakumar, V., Kannan, J., Kausar, N. et al. Multicriteria group decision making for prioritizing IoT risk factors with linear diophantine fuzzy sets and MARCOS method. Granul. Comput. 9, 56 (2024). https://doi.org/10.1007/s41066-024-00480-8
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s41066-024-00480-8