Abstract
Quantum key distribution protocols constitute an important part of quantum cryptography, where the security of sensitive information arises from the laws of physics. In this paper, we introduce a family of key distribution protocols which generalize the PBC00 protcol. We compare its key with the well-known protocols such as BB84, PBC00 and generation rate to the well-known protocols such as BB84, PBC0 and R04. We also state the security analysis of these protocols based on the entanglement distillation and CSS codes techniques.
Similar content being viewed by others
Avoid common mistakes on your manuscript.
1 Introduction
Quantum cryptography is a blooming field of scientific research, where quantum phenomena are applied to securing sensitive information. Usually, cryptographic systems are based on the key distribution mechanisms and security of the systems depends on computational complexity. The security of quantum cryptography arises from the laws of quantum physics. Scenarios of quantum key distribution (QKD) protocols are based on the assumption that secret key is shared by Alice and Bob. The first QKD protocol, BB84 [1], became a motivation for expanding research in this area. As a consequence, Mayers in [2] proved the unconditional security of this protocol on a noisy channel against a general attack. Quantum entanglement and the violation of Bell’s theorem were introduced to the BB84 protocol by Ekert [3]. Next, Bennett proposed a simple protocol B92 [4] based on two nonorthogonal states. Unconditional security analysis of this protocol was performed by Tamaki et al. in [5, 6] and by Quan et al. in [7]. Subsequently, Phoenix et al. [8] introduced PBC00 protocol and they showed that key bits can be generated more efficiently by the usage of three mutually nonorthogonal states. Renes developed the key creation protocols R04 [9] for two-qubit-based spherical codes, which is a modified version of the PBC00 protocol. The R04 protocol allows one to use all conclusive events for key extraction. In [10], Boileau et al. proved the unconditional security of the trine spherical code QKD protocol, which concerns also to PBC00 and R04 protocols. The experimental realization of PBC00 and R04 protocols was proposed in [11] and [12]. New results referring to asymptotic analysis of three-state protocol can be found in [13].
In this paper, we propose a class of QKD protocols which generalize the PBC00 protocols. We perform the security analysis of this class using of techniques similar as in [5, 10]. It means that the proposed protocol was considered as entanglement distillation protocol (EDP) [14, 15]. Subsequently, similarly as in case of BB84 [16], CSS codes [17, 18] were used to the security proof.
2 Defined state protocol
Our aim is to generalize the PBC00 protocol. We will achieve this in two steps. First generalize the well-known PBC00 protocol to an arbitrary number of states. Next, we will introduce modifications to the measurements used by both parties which allow us to obtain better key rates.
Let us introduce a class of QKD protocols, which generalize the PBC00 protocol [8]. Assume that Alice and Bob would like to share N secret bits \(b_i\). Then, the protocol is as follows.
2.1 Protocol 1 (P1)
-
1.
Alice and Bob share N pairs of maximally entangled two-qubit states \(\rho _{AB}=| \phi ^- \rangle \langle \phi ^- |\), where \(| \phi ^- \rangle = \frac{1}{\sqrt{2}}(| 01 \rangle -| 10 \rangle )\).
-
2.
She chooses K states \(| \psi _k \rangle =\cos (a+\theta _k)| 0 \rangle + \sin (a+\theta _k)| 1 \rangle \), where \(a\in [0,2\pi )\) is a constant and \(\theta _k=\frac{2 k \pi }{K}\) for \(k\in \{0,\ldots ,K-1\}\). The states \(| \psi _k \rangle \) are grouped into pairs \(S_k=\{| \psi _k \rangle ,| \psi _{k+1\mod K} \rangle \}\).
-
3.
Subsequently, Alice measures her parts of the states \(\rho _{AB}\) using the positive operator-valued measure (POVM) \(\{\frac{2}{K}| \psi _k^\perp \rangle \langle \psi _k^\perp |\}_k\), where \(| \psi _k^\perp \rangle \) is orthogonal to \(| \psi _k \rangle \). Detection of the state \(| \psi _{m_i}^\perp \rangle \) after measurement in the ith step is equivalent to sending a state \(| \psi _{m_i} \rangle \) to Bob.
-
4.
Alice chooses each key bit \(b_i\) randomly and calculates \(r_i\in \{0,\ldots ,K-1\}\) as \(r_i = m_i + b_i \mod K\). This \(r_i\) determines the encoding base \(S_{r_i}\).
-
5.
Alice publicly announces when all of her measurements are done.
-
6.
Bob prepares measurements described by the POVM \(\{\frac{2}{K}| \psi _k^\perp \rangle \langle \psi _k^\perp |\}_k\) and measures his parts of the states \(\rho _{AB}\). He announces when the measurements are done.
-
7.
Alice sends sequences of values \(r_i\) to Bob.
-
8.
Bob detects the state \(| \psi _{j_i}^\perp \rangle \). If \(j_i=r_i\), he decodes \(b_i=0\). If \(j_i=r_i-1 \mod K\), he decodes \(b_i=1\). In other cases, the events are regarded as inconclusive. These results are discarded.
-
9.
Half of randomly chosen conclusive events are used in the estimation of a bit error rate. If the bit error rate is to high, then they abort the protocol.
-
10.
In the end, they use a classical error correction and privacy amplification protocols.
Notice that for \(K=3\) and an appropriate choice of constant a, the above scenario is equivalent to the PBC00 protocol [8]. It can also be shown that protocols of this class achieve the highest key rate for \(K=3\). Note that for \(K=4\) the protocol becomes trivial as there are only two unique operators \(| \psi _k \rangle \langle \psi _k |\). Hence, the potential eavesdropper knows exactly which measurements to perform.
3 An enhancement
Now we consider a modification of the above protocol. Steps 1–4 are the same as in the previous protocol.
3.1 Protocol 2 (P2)
- 5\(^\prime \).:
-
Alice publicly announces when all her measurements are done and she sends sequences of values \(r_i\) to Bob.
- 6\(^\prime \).:
-
For each \(r_i\), Bob prepares an unambiguous measurement described by the POVM
$$\begin{aligned} \begin{aligned} \{\varPi _{r_i-1},\varPi _{r_i},\varPi _\mathrm{fill}\}&= \left\{ \frac{1}{\lambda }| {\psi }^\perp _{r_i} \rangle \langle {\psi }^\perp _{r_i} |, \frac{1}{\lambda }| {\psi }^\perp _{r_i+1\!\!\!\!\mod K} \rangle \langle {\psi }^\perp _{r_i+1\!\!\!\!\mod K} | \right. \\&\quad \left. \mathbb {1}_2 - \frac{1}{\lambda } \left( | {\psi }^\perp _{{r_i}} \rangle \langle {\psi }^\perp _{{r_i}} |+ | {\psi }^\perp _{{r_i}+1\!\!\!\!\mod K} \rangle \langle {\psi }^\perp _{{r_i}+1\!\!\!\!\mod K} |\right) \right\} \end{aligned} \end{aligned}$$(1)where \(\lambda = \frac{\sqrt{2}}{2} \sqrt{\cos \frac{4\pi }{K}+1} + 1 = 1 +|\cos (\frac{2\pi }{K})|\). The value \(\lambda \) is determined as a maximal eigenvalue of
$$\begin{aligned} | {\tilde{\psi }}_{r_i} \rangle \langle {\tilde{\psi }}_{r_i} | + | {\tilde{\psi }}_{r_i+1\!\!\!\!\mod K} \rangle \langle {\tilde{\psi }}_{r_i+1\!\!\!\!\mod K} |. \end{aligned}$$(2) - \(7^\prime \).:
-
This point is now redundant and can be omitted.
Steps 8, 9 and 10 are again the same as in the previous protocol. For \(K=3\), the characteristics of the protocols P1 and P2 are the same and are equivalent to the characteristics of the PBC00 protocol. In next section, we will show that we get higher key rate in the case of protocol P2 with \(K=5\) than the case of PBC00 protocol.
4 Security analysis
Similarly to [5, 10, 16], we consider an entanglement distillation protocol (EDP) [15] related to quantum error-correcting codes [16], which can be reduced to a QKD protocol equivalent to the above scheme. Lo and Chau shown similarities between QKD and EDP [15]. Notice that Alice and Bob share Bell state, which provides security from an eavesdropper. Lo and Chau proved that existence of eavesdropping or noise does not spoil of security of QKD protocol based on EDP [15]. Shor and Preskill used approach proposed by Lo and Chau for analysis of security proof based on CSS codes [16]. In contrast to classical linear error-correcting codes, quantum codes refer not only with bit errors, but also with phase errors. It can be supposed that in Lo-Chau protocol, Alice and Bob can use CSS codes able to correcting bit and phase errors. One of the advantage of CSS codes is fact that bit errors and phase errors are correctable separately. Similarly to [10], we prepare phase error estimation utilizing the Azuma’s inequality [19].
Firstly, we transform the vectors \(| \psi _i \rangle \) by the rotation operator \(R(-\eta )\), where \(R_y(\theta )=\left( \begin{matrix} \cos \theta &{} -\sin \theta \\ \sin \theta &{} \cos \theta \end{matrix}\right) \) and \(\eta =\arccos (\langle \psi _1 |{\psi _0}\rangle )/2 + \arctan \left( \frac{\langle \psi _0 |{1}\rangle }{\langle \psi _0 |{0}\rangle }\right) \). After this transformation, we get states \(| \tilde{\psi _i} \rangle =R(-\eta )| {\psi _i} \rangle \), where \(| \tilde{\psi _0} \rangle =\cos (\frac{\pi }{K})| 0 \rangle + \sin (\frac{\pi }{K})| 1 \rangle \) and \(| \tilde{\psi _1} \rangle =\cos (-\frac{\pi }{K})| 0 \rangle + \sin (-\frac{\pi }{K})| 1 \rangle \). This transformation has no impact on the protocol, but is important in the security analysis. Assume that Alice prepares many pairs of qubits in the entangled state \(| \psi \rangle =\frac{1}{\sqrt{2}}(| + \rangle | {\tilde{\psi }}_0 \rangle +| - \rangle | {\tilde{\psi }}_1 \rangle )\), where \(| \pm \rangle =\frac{1}{\sqrt{2}}(| 0 \rangle \pm | 1 \rangle )\) and the basis \(\{| + \rangle ,| - \rangle \}\) will be denoted by ±-basis. Next, she randomly chooses a string \(r_i\), \(r_i\in \{0,\ldots , K-1\}\) of length N and applies \(R_y(\theta _{r_i})\) on the second qubit of every pair. After that, she sends qubits to Bob through a quantum channel. Alice announces the values of \(r_i\). Next, Bob performs local filtering operations [20,21,22] \(F=\frac{1}{\sqrt{2\lambda }}\Big ((| {\tilde{\psi }}^\perp _0 \rangle + | {\tilde{\psi }}^\perp _1 \rangle )\langle 0 | + (| {\tilde{\psi }}^\perp _0 \rangle - | {\tilde{\psi }}^\perp _1 \rangle )\langle 1 | \Big )\) and operation \(R_y(-\theta _{r_i})\) on the received qubits. Next, half of the states are used to determine the number of bit errors after application of ±-basis measurements by Alice and Bob. If the number of errors is too high, then the protocol is aborted. Remaining qubits are used to distill Bell states by an EDP based on CSS codes. Alice and Bob perform ±-basis measurements on Bell states to obtain a secret key.
Notice that \(R_y(\theta _{r_i})| {\tilde{\psi }}_j \rangle =| {\tilde{\psi }}_{r_i+j \mod K} \rangle \) and Alice’s operation related to measurement \(\{\frac{1}{\lambda }| {\tilde{\psi }}_i^\perp \rangle \langle {\tilde{\psi }}_i^\perp |\}_i\) on her state are equivalent to ±-basis measurement on the state \(\big (\mathbb {1}_2\otimes R_y(\theta _{r_i})\big )| \psi \rangle \). The filtering operations F, rotation operation \(R_y(-\theta _{r_i})\) and ±-basis measurement performed by Bob can by described by the following POVM
This measurement is equivalent to the POVM
In [16], Shor and Preskill have shown that if the bound of estimations of bit and phase error decreases exponentially as N increases, then Eve’s information on secret key is exponentially small. This approach was used to prove the unconditional security of the Bennet 1992 protocol, by Tamaki et al. [5], and the PBC00 and R04 protocols, by Boileau et al. [10]. These proofs were based on the usage of reduction to an entanglement distillation protocol initiated by a local filtering process. Subsequently, we will prove the security of the above entanglement distillation protocol in the same manner as in [5, 10, 16].
Assume that \(\{p_{b}^{(i)}\}_{i=1}^N\) and \(\{p_{p}^{(i)}\}_{i=1}^N\) are sets of probabilities of a bit error and a phase error, respectively, on the ith pair after Alice and Bob have done the same measurements on \(i-1\) previous pairs. Thus, \(p_{b}^{(i)}\) and \(p_{p}^{(i)}\) depend on previous results. Moreover, we introduce \(e_{b}\) and \(e_{p}\) as rates of bit error and phase error in all conclusive results, respectively.
Estimations of bit and phase error rates will be performed by the use of Azuma’s inequality [19] as in [10].
Theorem 1
([19]) Let \(\{X_i:i=0,1,\dots \}\) be a martingale sequence and for each k it holds that \(|X_k-X_{k-1}|\le c_k\). Then for all integers \(N\ge 0\) and real numbers \(\gamma \ge 0\)
Notice that for \(c_k=1\) we get
As a result of the Azuma’s inequality, \(Ce_{b}\) is exponentially close to \(e_{p}\) (\(Ce_{b}=e_{p}\)) for particular constant C, if \(Cp^{(i)}_{b}=p_{p}^{(i)}\) is satisfied for all i. Assume that Eve can perform any coherent attack \(E^{(i)}\) on qubits sent by Alice such that \(\sum _i E^{(i)\dagger } E^{(i)}\le \mathbb {1}\). The general equation for the ith state can be described by a mixed state
where
Let us introduce the notation \(| \varPhi ^\pm \rangle =\frac{1}{\sqrt{2}}(| + \rangle | + \rangle \pm | - \rangle | - \rangle )\) and \(| \varPsi ^\pm \rangle =\frac{1}{\sqrt{2}}(| + \rangle | - \rangle \pm | - \rangle | + \rangle )\). Since the probability of sharing by Alice and Bob a Bell state \(| \varPhi ^+ \rangle \) is equal to the probabilities of a bit error \(p_{b}^{(i)}\) and phase error \(p_{p}^{(i)}\) on the ith, respectively, thus
where
It can be checked that
Similarly as in [10], we calculate the key rate S from the following formula
where \(h(x)=-x\log _2 x -(1-x)\log _2(1-x)\) and \(p_c(e_{b})\) is the probability of a conclusive result. Since \(Ce_{b}=e_{p}\), we get
Notice that for a bit value \(b=0\) we get outcome probabilities
\(\{0,\frac{1}{\lambda }|\langle {\tilde{\psi }}^\perp _{r_i+1\!\!\!\! \mod K} |{{\tilde{\psi }}_{r_i}}\rangle |^2, 1-\frac{1}{\lambda }|\langle {\tilde{\psi }}^\perp _{r_i+1\!\!\!\! \mod K} |{{\tilde{\psi }}_{r_i}}\rangle |^2\}\), and for \(b=1\), we get
\(\{\frac{1}{\lambda }|\langle {\tilde{\psi }}^\perp _{r_i} |{{\tilde{\psi }}_{r_i+1\!\!\!\! \mod K}}\rangle |^2, 0, 1-\frac{1}{\lambda }|\langle {\tilde{\psi }}^\perp _{r_i} |{{\tilde{\psi }}_{r_i+1\!\!\!\! \mod K}}\rangle |^2\}\). Hence, it can be checked that \(|\langle {\tilde{\psi }}^\perp _{r_i+1\!\!\!\! \mod K} |{{\tilde{\psi }}_{r_i}}\rangle |^2=|\langle {\tilde{\psi }}^\perp _{r_i} |{{\tilde{\psi }}_{r_i+1\!\!\!\! \mod K}}\rangle |^2=\sin ^2\left( \frac{2\pi }{K}\right) \). Thus, the probability of a conclusive result, with the assumption that \(e_{b}=0\), is equal to
which can be simplified to \(p_c(0)=2\sin ^2(\frac{\pi }{K})\) for \(K>3\). Note that \(K=4\) we have \(p_c(0)=1\). This is to be expected for a trivial protocol as this corresponds to sending the key over a public channel.
Generally, \(p_c\) can be expressed as
which was derived in “Appendix A.” Notice that for \(K=3\) Eq. (15) is reduced to \(p_c(e_{b})=\frac{1}{2-e_{b}}\), which corresponds to probability of conclusive results in PBC00 protocol.
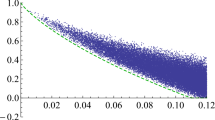
In the case of BB84 protocol, bit error rate is equal to phase error rate. Thus, \(C=1\) and \(p_c(e_{b})=\frac{1}{2}\). In the case of PBC00, \(C=\frac{5}{4}\) and \(p_c(e_{b})=\frac{1}{2-e_{b}}\). From Eq. (13), we get that \(e_{b}\approx 11.0\%\) for BB84 protocol and \(e_{b}\approx 9.81\%\) for PBC00 protocol. It can be checked that an interesting case is for \(K=5\), where \(C=\frac{1}{8}(11-\sqrt{5})\) and \(e_{b}\approx 10.5\%\). Comparison of proposed protocol with BB84 and PBC00 protocols is shown in Fig. 1. As we can see, the best key rate is for \(K=5\). We plot the key rates for K up to 7. For higher K, the key rates decrease with K and are bounded from above by \(2\sin ^2\left( \frac{\pi }{K}\right) \).
The fact that the highest key rate is obtained for \(K=5\) can be explained as follows. The POVM elements are projection operators corresponding to vectors evenly distributed on a circle. For \(K=3\), we get that the angle between the vectors is \(\frac{2}{3} \pi \), and for \(K=5\), we get angle of \(\frac{2}{5} \pi \). The latter is closer to \(\frac{\pi }{2}\); hence, the probability of distinguishing the vectors is higher which yields a higher key rate. As discussed earlier, the case \(K=4\) reduces to a trivial protocol.
5 Conclusion
In this paper, we have introduced a new class of quantum key distribution protocols. We have also provided unconditional security analysis of this protocol. We have shown that there exists 5-state protocol with reasonably high key rate for small bit-flip error rates.
References
Bennett, C.H., Brassard, G.: An update on quantum cryptography. In: Crypto, vol. 84, pp. 475–480 Springer (1984)
Mayers, D.: Quantum key distribution and string oblivious transfer in noisy channels. In: Advances in Cryptology—Proceedings of Crypto96, pp. 343–357. Springer (1996)
Ekert, A.K.: Quantum cryptography based on bell’s theorem. Phys. Rev. Lett. 67(6), 661 (1991)
Bennett, C.H.: Quantum cryptography using any two nonorthogonal states. Phys. Rev. Lett. 68(21), 3121 (1992)
Tamaki, K., Koashi, M., Imoto, N.: Unconditionally secure key distribution based on two nonorthogonal states. Phys. Rev. Lett. 90(16), 167904 (2003)
Tamaki, K., Lütkenhaus, N.: Unconditional security of the bennett 1992 quantum key-distribution protocol over a lossy and noisy channel. Phys. Rev. A 69(3), 032316 (2004)
Quan, Z., Chaojing, T.: Simple proof of the unconditional security of the bennett 1992 quantum key distribution protocol. Phys. Rev. A 65(6), 062301 (2002)
Phoenix, S.J.D., Barnett, S.M., Chefles, A.: Three-state quantum cryptography. J. Mod. Opt. 47(2–3), 507–516 (2000)
Renes, J.M.: Spherical-code key-distribution protocols for qubits. Phys. Rev. A 70(5), 052314 (2004)
Boileau, J.-C., Tamaki, K., Batuwantudawe, J., Laflamme, R., Renes, J.M.: Unconditional security of a three state quantum key distribution protocol. Phys. Rev. Lett. 94(4), 040503 (2005)
Senekane, M., Mafu, M., Petruccione, F.: Six-state symmetric quantum key distribution protocol. J. Quantum Inf. Sci. 5(02), 33 (2015)
Schiavon, M., Vallone, G., Villoresi, P.: Experimental realization of equiangular three-state quantum key distribution. Sci. Rep. 6, 30089 (2016)
Krawec, W.O.: Asymptotic analysis of a three state quantum cryptographic protocol. In: 2016 IEEE International Symposium on Information Theory (ISIT), pp. 2489–2493. IEEE (2016)
Bennett, C.H., DiVincenzo, D.P., Smolin, J.A., Wootters, W.K.: Mixed-state entanglement and quantum error correction. Phys. Rev. A 54(5), 3824 (1996)
Lo, H.-K., Chau, H.F.: Unconditional security of quantum key distribution over arbitrarily long distances. Science 283(5410), 2050–2056 (1999)
Shor, P.W., Preskill, J.: Simple proof of security of the BB84 quantum key distribution protocol. Phys. Rev. Lett. 85(2), 441 (2000)
Calderbank, A.R., Shor, P.W.: Good quantum error-correcting codes exist. Phys. Rev. A 54(2), 1098 (1996)
Steane, A.: Multiple-particle interference and quantum error correction. Proc. R. Soc. Lond. Math. Phys. Eng. Sci. 452, 2551–2577 (1996)
Azuma, K.: Weighted sums of certain dependent random variables. Tohoku Math. J. Second Ser. 19(3), 357–367 (1967)
Gisin, N.: Hidden quantum nonlocality revealed by local filters. Phys. Lett. A 210(3), 151–156 (1996)
Bennett, C.H., Bernstein, H.J., Popescu, S., Schumacher, B.: Concentrating partial entanglement by local operations. Phys. Rev. A 53(4), 2046 (1996)
Horodecki, M., Horodecki, P., Horodecki, R.: Inseparable two spin-\(\frac{1}{2}\) density matrices can be distilled to a singlet form. Phys. Rev. Lett. 78(4), 574 (1997)
Acknowledgements
The authors acknowledge the support by the Polish National Science Center under the Project Number 2015/17/B/ST6/01872.
Author information
Authors and Affiliations
Corresponding author
Appendix A: Probability of conclusive events
Appendix A: Probability of conclusive events
Notice that if Alice performs \(| \psi ^\perp _i \rangle \), where \(| \psi _i \rangle \in S_r\), \(i=r\) or \(i=r+b\mod K\) and Bob chooses \(| \psi _i^\perp \rangle \), then it corresponds to an error. In the case when Bob chooses a state which corresponds to \(S_r\) but is not orthogonal to Alice’s state, then Bob can correctly conclude the state \(| \psi _i \rangle \).
Let \(n_g, n_e, n_i\) denote the numbers of good conclusive, error conclusive and inconclusive events, respectively. Besides that, let \(n_t = n_g+n_e+n_i\) and thus \(1=\frac{n_g}{n_t}+\frac{n_e}{n_t}+\frac{n_i}{n_t}\). Assume that after Alice sent r to Bob, Bob performs measurement described by POVM
Now, we suppose that \(b=0\) and Eve simulates a noisy channel, where state \(| {\psi }_r \rangle \langle {\psi }_r |\) evolves as \(\rho _B=(1-p)| {\psi }_r \rangle \langle {\psi }_r |+\frac{p}{2}\mathbb {1}_2\). Next, Bob performs measurement and receives measurement outcomes with probabilities \(\{\mathrm {Tr}\varPi _r \rho _B = \frac{p}{2\lambda }, \mathrm {Tr}\varPi _{r+1} \rho _B = \frac{p}{2\lambda } + \frac{1-p}{\lambda }\sin ^2(\frac{2\pi }{K}), \mathrm {Tr}\varPi _\mathrm{fill} \rho _{b} = 1- \frac{p}{\lambda }-\frac{1-p}{\lambda }\sin ^2(\frac{2\pi }{K}\}\).
A bit error rate \(e_{b}\) is defined as the rate of error in conclusive results. Hence
Notice that error \(e_{b}\) can be estimated as
Now, let us determine a ratio
From the central limit theorem and the above calculation we get
Continuing we obtain
and
Rights and permissions
Open Access This article is distributed under the terms of the Creative Commons Attribution 4.0 International License (http://creativecommons.org/licenses/by/4.0/), which permits unrestricted use, distribution, and reproduction in any medium, provided you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons license, and indicate if changes were made.
About this article
Cite this article
Kurzyk, D., Pawela, Ł. & Puchała, Z. Unconditional security of a K-state quantum key distribution protocol. Quantum Inf Process 17, 228 (2018). https://doi.org/10.1007/s11128-018-1998-3
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11128-018-1998-3