Abstract
We propose an efficient four-intensity decoy-state BB84 protocol and derive concise security bounds for this protocol with the universally composable finite-key analysis method. Comparing with the efficient three-intensity protocol, we find that our efficient four-intensity protocol can increase the secret key rate by at least 30%. Particularly, this increasing rate of secret key rate will be raised as the transmission distance increases. At a large transmission distance, our efficient four-intensity protocol can improve the performance of quantum key distribution profoundly.
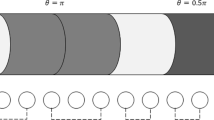
Graphical abstract

Similar content being viewed by others
References
C.E. Shannon, Bell System Technical Journal 28, 656 (1949)
C.H. Bennett, G. Brassard, Quantum cryptography: Public key distribution and coin tossing, in Proceedings of IEEE International Conference on Computers, Systems and Signal Processing (New York, 1984), pp. 175–179
A.K. Ekert, Phys. Rev. Lett. 67, 661 (1991)
H.K. Lo, H.F. Chau, Science 283, 2050 (1999)
P.W. Shor, J. Preskill, Phys. Rev. Lett. 85, 441 (2000)
D. Mayers, J. ACM (JACM) 48, 351 (2001)
R. Renner, N. Gisin, B. Kraus, Phys. Rev. A 72, 012332 (2005)
G. Brassard, N. Lütkenhaus, T. Mor, B.C. Sanders, Phys. Rev. Lett. 85, 1330 (2000)
N. Lütkenhaus, M. Jahma, New J. Phys. 4, 44 (2002)
W.Y. Hwang, Phys. Rev. Lett. 91, 057901 (2003)
X.B. Wang, Phys. Rev. Lett. 94, 230503 (2005)
H.K. Lo, X.F. Ma, K. Chen, Phys. Rev. Lett. 94, 230504 (2005)
M. Hayashi, R. Nakayama, New J. Phys. 16, 063009 (2014)
C.C.W. Lim, M. Curty, N. Walenta, F. Xu, H. Zbinden, Phys. Rev. A 89, 022307 (2014)
M. Tomamichel, R. Renner, Phys. Rev. Lett. 106, 110506 (2011)
M. Tomamichel, C.C.W. Lim, N. Gisin, R. Renner, Nat. Commun. 3, 634 (2012)
X.B. Wang, Phys. Rev. A 72, 012322 (2005)
M. Hayashi, New J. Phys. 9, 284 (2007)
Y.H. Zhou, Z.W. Yu, X.B. Wang, Phys. Rev. A 89, 052325 (2014)
Z.W. Yu, Y.H. Zhou, X.B. Wang, arXiv:1509.04011 (2015)
R.Y.Q. Cai, V. Scarani, New J. Phys. 11, 045024 (2009)
X.F. Ma, B. Qi, Y. Zhao, H.K. Lo, Phys. Rev. A 72, 012326 (2005)
Z. Wei, W. Wang, Z. Zhang, M. Gao, Z. Ma, X.F. Ma, Sci. Rep. 3, 2453 (2013)
M. Lucamarini, K.A. Patel, J.F. Dynes, B. Fröhlich, A.W. Sharpe, A.R. Dixon, Z.L. Yuan, R.V. Penty, A.J. Shields, Opt. Express 21, 24550 (2013)
H.K. Lo, H.F. Chau, M. Ardehali, J. Cryptol. 18, 133 (2005)
B. Korzh, C.C.W. Lim, R. Houlmann, N. Gisin, M.J. Li, D. Nolan, B. Sanguinetti, R. Thew, H. Zbinden, Nat. Phot. 9, 163 (2015)
B. Fröhlich, J.F. Dynes, M. Lucamarini, A.W. Sharpe, Z.L. Yuan, A.J. Shields, Nature 501, 69 (2013)
N. Walenta, T. Lunghi, O. Guinnard, R. Houlmann, H. Zbinden, N. Gisin, J. Appl. Phys. 112, 063106 (2012)
X.F. Ma, C.H.F. Fung, M. Razavi, Phys. Rev. A 86, 052305 (2012)
M. Curty, F. Xu, W. Cui, C.C.W. Lim, K. Tamaki, H.K. Lo, Nat. Commun. 5, 3732 (2014)
H.L. Yin, W.F. Cao, Y. Fu, Y.L. Tang, Y. Liu, T.Y. Chen, Z.B. Chen, Opt. Lett. 39, 5451 (2014)
D. Rosenberg, J.W. Harrington, P.R. Rice, P.A. Hiskett, C.G. Peterson, R.J. Hughes, A.E. Lita, S.W. Nam, J.E. Nordholt, Phys. Rev. Lett. 98, 010503 (2007)
A.R. Dixon, Z.L. Yuan, J.F. Dynes, A.W. Sharpe, A.J. Shields, Opt. Express 16, 18790 (2008)
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Jiang, H., Gao, M., Yan, B. et al. Universally-composable finite-key analysis for efficient four-intensity decoy-state quantum key distribution. Eur. Phys. J. D 70, 78 (2016). https://doi.org/10.1140/epjd/e2016-60655-2
Received:
Revised:
Published:
DOI: https://doi.org/10.1140/epjd/e2016-60655-2