Abstract
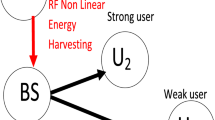
This paper considers an underlay relaying network where a cognitive relay performs decode-and-forward operation to aid communication between a cognitive source-destination pair. Transmit powers of cognitive users are subject to both interference and peak transmit power constraints. To stimulate support, the relay merely spends power scavenged from source signals with realistic non-linear energy harvester for its operation. Additionally, to secure secret transmission of both the source and the relay, this paper proposes to merge jamming signals with secret ones before their transmission. Relied on practical observations that jamming signals and channel state information at legitimate receivers may not be suppressed and estimated perfectly, respectively, this paper analyzes system performance under inaccuracies of jamming suppression and channel estimation. Purposively, this paper analyzes security-reliability trade-off of underlay relaying networks under joint practical influences of erroneous channel information, Nakagami-m fading severity, jamming suppression error, energy harvesting non-linearity, and power constraints of cognitive users. Towards this end, explicit expressions of intercept and outage probabilities are first derived. Then, they are used to quickly generate numerous results so as to withdraw interesting findings. More specifically, the proposed jamming strategy experienced the trade-off between security and reliability as well as reliability/security saturation at high peak transmit power. Additionally, channel estimation error, fading severity, jamming suppression error, and energy harvesting non-linearity significantly impact system performance. Nonetheless, system parameters can be set properly to achieve different security levels and prevent absolute outage.









Similar content being viewed by others
Notes
CRs have two other (overlay and interweave) operation mechanisms, which are outside our interest.
This paper assumes that the cognitive relay is willing to support the communication between the cognitive source and the cognitive destination. Therefore, it is certain that the relay is trusted, not malicious. Also, there must be an initial process to select the trusted relay before any transmission, which was a widely accepted assumption in the open literature (please see references in this paper). As such, the initial process is assumed to be well-known and the focus now is shifted to the performance analysis and evaluation.
In the case that the relay does not help the communication between the cognitive source and the cognitive destination, it can use the harvested energy for its own purpose, which may be considered as a reward for the relay.
In the underlay mechanism, licensed users also interfere with cognitive users. Nevertheless, such interference is negligible in cases where the distance between cognitive and licensed users is sufficiently large or the interference is Gaussian-distributed. Neglecting such interference is complied widely in the publications of underlay networks (e.g., [61,62,63]).
\(c\sim \text {Nak}\!\left( m,\nu \right) \) notates a random variable c following Nakagami-m distribution with a parameter set \((m, \nu )\).
\(\xi \sim {{\mathcal {C}}}{{\mathcal {N}}}\left( {0,{\tau }} \right) \) means a zero-mean \(\tau -\)variance complex Gaussian random variable.
Other signal combining methods such as equal gain combining and maximum ratio combining can be employed by \(\textsf {E}\) for improved performance at expense of higher complexity [68].
These two inequalities constrain \(\delta \) as \(\delta \ge 1 - 2{{{\bar{\Psi }}}_e}\min \left( {\frac{1}{{{{\log }_2}\left( {{G^{ - 1}} + 1} \right) }},\frac{1}{{{{\log }_2}\left( {{V^{ - 1}} + 1} \right) }}} \right) \).
References
Shinohara, N.: Trends in wireless power transfer: WPT technology for energy harvesting, mllimeter-wave/THz rectennas, MIMO-WPT, and advances in near-field WPT applications. IEEE Micro. Mag. 22(1), 46–59 (2021)
Alaukally, M.N.N.; et al.: Miniaturized flexible metamaterial antenna of circularly polarized high gain-bandwidth product for radio frequency energy harvesting. Int. J. Commun. Syst. (2021). https://doi.org/10.1002/dac.5024
Abdulmjeed, A.; et al.: Metamaterial vivaldi printed circuit antenna based solar panel for self-powered wireless systems. Prog. Electromagn. Res. M 102, 181–192 (2021)
Imran, A.I.; et al.: On the distortionless of UWB wearable Hilbert-Shaped metamaterial antenna for low energy applications. Prog. Electromagn. Res. M 101, 219–239 (2021)
Elwi, T.A.; et al.: Further realization of a flexible metamaterial based antenna on indium nickel oxide polymerized palm fiber substrates for RF energy harvesting. Int. J. Microw. Wirel. Technol. 5(4), 1–9 (2020)
Elwi, T.A.; et al.: Novel miniaturized folded UWB microstrip antenna-based metamaterial for RF energy harvesting. J. Commun. Syst.1(2) (2020)
Elwi, T.A.; et al.: Hilbert metamaterial printed antenna based on organic substrates for energy harvesting. IET Microw. Antennas Propag. 12(4), 1–8 (2019)
Elwi, T.A.: Novel UWB printed metamaterial microstrip antenna based organic substrates for RF-energy harvesting applications. J. Electron. Commun. 101, 1–10 (2019)
Ge, L.; et al.: Performance analysis for multihop cognitive radio networks with energy harvesting by using stochastic geometry. IEEE IoT J. 7(2), 1154–1163 (2020)
Solanki, S.; et al.: Performance analysis of piece-wise linear model of energy harvesting-based multiuser overlay spectrum sharing networks. IEEE OJ CS 1, 1820–1836 (2020)
Ho-Van, K.; et al.: Security enhancement for energy harvesting cognitive networks with relay selection. Wire. Commun. Mobile Comput. 1–13 (2020)
Ali, Z.; et al.: A joint optimization framework for energy harvesting based cooperative CR networks. IEEE Trans. Cogn. Commun. Netw. 5(2), 452–462 (2019)
Miridakis, N.I.; et al.: Simultaneous spectrum sensing and data reception for cognitive spatial multiplexing distributed systems. IEEE Trans. Wire. Commun. 16(5), 3313–3327 (2017)
Lei, H.; et al.: On secure underlay MIMO cognitive radio networks with energy harvesting and transmit antenna selection. IEEE Trans. Green Commun. Netw. 1(2), 192–203 (2017)
Shi, H.; et al.: Physical layer security in an untrusted energy harvesting relay network. IEEE Access 7, 24819–24828 (2019)
Miridakis, N.I.; et al.: MIMO underlay cognitive radio: optimized power allocation, effective number of transmit antennas and harvest-transmit tradeoff. IEEE Trans. Green Commun. Netw. 2(4), 1101–1114 (2018)
Mishra, D.; et al.: Transmit precoding and receive power splitting for harvested power maximization in MIMO SWIPT systems. IEEE Trans. Green Commun. Netw. 2(3), 774–786 (2018)
Wang, F.; et al.: Secure resource allocation for polarization-based non-linear energy harvesting over 5G cooperative CRNs. IEEE Wire. Commun. Lett.. Accepted
Dang-Ngoc, H.; et al.: Key secrecy performance metrics of overlay networks with energy scavenging and artificial noise. In: Proc. IEEE SigTelCom, Vietnam, 28–29, pp. 77–81 (2020)
Su, R.; et al.: Destination-Assisted Jamming for Physical-Layer Security in SWIPT Cognitive Radio Systems. In: 2018 IEEE Wireless Communications and Networking Conference (WCNC), pp. 1–6. IEEE WCNC, Spain (2018)
Xu, M.; et al.: Secure transmission solutions in energy harvesting enabled cooperative cognitive radio networks. In:2018 IEEE Wireless Communications and Networking Conference (WCNC, pp. 1–6. IEEE WCNC, Spain (2018)
Pham-Thi-Dan, N.; et al.: Secrecy throughput analysis of energy scavenging overlay networks with artificial noise. In: 2020 International Conference on Advanced Technologies for Communications (ATC), Vietnam, pp. 90–94, 8–10 Aug (2020)
Wang, D.; et al.: Primary privacy preserving with joint wireless power and information transfer for cognitive radio networks. IEEE Trans. Cogn. Commun. Netw. 6(2), 683–693 (2020)
Ho-Van, K.; et al.: Overlay networks with jamming and energy harvesting: security analysis. Arab. J. Sci. Eng. 46, 9713–9724 (2021)
Su, R.; et al.: Secure cooperative transmission in cognitive AF relay systems with destination-aided jamming and energy harvesting. In: 2019 IEEE 30th Annual International Symposium on Personal, Indoor and Mobile Radio Communications (PIMRC), pp. 1–5. Turkey, IEEE PIMRC (2019)
Dang-Ngoc, H.; et al.: Secrecy analysis of overlay mechanism in radio frequency energy harvesting networks with jamming underNakagami-m fading. Wire. Pers. Commun. 120, 447–479 (2021)
Ho-Van, K.; et al.: Impact of channel estimation-and-artificial noise cancellation imperfection on artificial noise-aided energy harvesting overlay networks. Telecom. Syst. 78, 273–292 (2021)
Wang, D.; et al.: Performance analysis of energy beamforming WPCN links with channel estimation errors. IEEE OJ CS 1, 1153–1170 (2020)
Wang, D.; et al.: Performance analysis and resource allocations for a WPCN with a new nonlinear energy harvester model. IEEE OJ CS 1, 1403–1424 (2020)
Ma, G.; et al.: Time-division energy beamforming for multiuser wireless power transfer with non-linear energy harvesting. IEEE Wire. Commun. Lett. 10(1), 53–57 (2021)
Zhu, Z.; et al.: Robust beamforming designs in secure MIMO SWIPT IoT networks with a non-linear channel model. IEEE IoT J. 8(3), 1702–1715 (2021)
Vu, T.X.; et al.: Joint optimization for PS-based SWIPT multiuser systems with non-linear energy harvesting. In: 2020 IEEE Wireless Communications and Networking Conference (WCNC, pp. 1-6, Seoul, Korea, 25–28 May (2020)
Liu, X.; et al.: Secrecy throughput optimization for the WPCNs with non-linear EH model. IEEE Access 7, 59477–59490 (2019)
Lu, Y.; et al.: Global energy efficiency in secure MISO SWIPT systems with non-linear power-splitting EH model. IEEE JSAC 37(1), 216–232 (2019)
Gao, S.; et al.: Outage performance of wireless-powered SWIPT networks with non-linear EH model in Nakagami-m fading. 2018 14th IEEE International Conference on Signal Processing (ICSP), pp. 668–671, China, 12–16 Aug (2018)
Ni, L.; et al.: Outage constrained robust secrecy energy efficiency maximization for EH cognitive radio networks. IEEE Wire. Commun. Lett. 9(3), 363–366 (2020)
Zhou, F.; et al.: Enhancing PHY security of MISO NOMA SWIPT systems with a practical non-linear EH model. In: 2018 IEEE International Conference on Communications Workshops (ICC Workshops), pp. 1–6, USA, 20–24 May (2018)
Boshkovska, E.; et al.: Power-efficient and secure WPCNs with hardware impairments and non-linear EH circuit. IEEE Trans. Commun. 66(6), 2642–2657 (2018)
Che, Y.; et al.: UAV-aided information and energy transmissions for cognitive and sustainable 5G networks. IEEE Trans. Wire. Commun. 20(3), 1668–1683 (2021)
Wang, D.; et al.: Secure energy efficiency for NOMA based cognitive radio networks with nonlinear energy harvesting. IEEE Access 6, 62707–62716 (2018)
Shanin, N.; et al.: Markov decision process based design of SWIPT systems: non-linear EH circuits, memory, and impedance mismatch. IEEE Trans. Commun. 69(2), 1259–1274 (2021)
Bayat, S.; et al.: Resource allocation for MC MISO-NOMA SWIPT-enabled HetNets with non-linear energy harvesting. IEEE Access 8, 192270–192281 (2020)
Kazmi, S.A.A.; et al.: Optimization of full-duplex relaying system with non-linear energy harvester. IEEE Access 8, 201566–201576 (2020)
Anwar, A.: SWIPT-based three-step multiplicative amplify-and-forward two-way relay networks with non-linear energy conversion model. 2018 IEEE 4th International Conference on Computer and Communications (ICCC), pp. 152–157 China, 7–10 Dec (2018)
Raut, P.; et al.: Power-time splitting-based non-linear energy harvesting in FD short-packet communications. IEEE Trans. Veh. Tech. 69(8), 9146–9151 (2020)
Liu, Y.; et al.: Outage performance analysis for SWIPT-based incremental cooperative NOMA networks with non-linear harvester. IEEE Commun. Lett. 24(2), 287–291 (2020)
Shi, L.; et al.: Heterogeneous power-splitting based two-way DF relaying with non-linear energy harvesting. 2018 IEEE Global Communications Conference (GLOBECOM), pp. 1–7, United Arab Emirates, 9–13 Dec (2018)
Xie, X.; et al.: Outage performance and QoS optimization in full-duplex system with non-linear energy harvesting model. IEEE Access 6, 44281–44290 (2018)
Liu, Y.; et al.: Performance analysis for incremental DF relaying networks with non-linear energy harvesting. 2020 IEEE 20th International Conference on Communication Technology (ICCT), pp. 354–360 China, 28–31 Oct (2020)
Zhang, Y.; et al.: Generalized non-linear energy harvesting protocol for enhancing security of AF multi-antenna relaying systems. 2019 IEEE 2nd International Conference on Electronics and Communication Engineering (ICECE), pp. 195–201, China, 9–11 Dec (2019)
Hakimil, A.; et al.: Full-duplex non-orthogonal multiple access cooperative spectrum-sharing networks with non-linear energy harvesting. IEEE Trans. Veh. Tech. 69(10), 10925–10936 (2020)
Babaei, M.; et al.: BER performance of full-duplex cognitive radio network with nonlinear energy harvesting. IEEE Trans. Green Commun. Netw. 4(2), 448–460 (2020)
Agrawal, K.; et al.: NOMA with battery-assisted energy harvesting full-duplex relay. IEEE Trans. Veh. Tech. 69(11), 13952–13957 (2020)
Prathima, A.; et al.: Two-way cooperative cognitive radio networks with nonlinear RF-energy harvester. In: 2020 IEEE Latin-American Conference on Communications (LATINCOM), pp. 1–6, 18–20 Nov (2020)
Ho-Van, K.; et al.: Security improvement for energy harvesting based overlay cognitive networks with jamming-assisted full-duplex destinations. IEEE Trans. Veh. Tech. 70(11), 12232–12237 (2021)
Maji, P.; et al.: Physical layer security with non-linear energy harvesting relay. In: 2019 10th International Conference on Computing, Communication and Networking Technologies (ICCCNT), India, pp. 1–6, 6–8 July (2019)
Li, H.; et al.: Throughput maximization with energy harvesting in UAV-assisted cognitive mobile relay networks. IEEE Trans. Cogn. Commun. Netw. 7(1), 197–209 (2021)
Shome, A.; et al.: BER performance analysis of energy harvesting underlay cooperative cognitive radio network with randomly located primary users and secondary relays. IEEE Trans. Veh. Tech. 70(5), 4740–4752 (2021)
Nguyen, T.V.; et al.: A deep-neural-network-based relay selection scheme in wireless-powered cognitive IoT networks. IEEE IoT J. 8(9), 7423–7436 (2021)
Pham-Minh, T.; et al.: Simultaneous jamming-and-transmitting scheme for spectrum-sharing relaying networks with non-linear energy scavenging. Wire. Commun. Mobile Comput. 2021, 1–15 (2021)
Zhang, X.; et al.: Outage performance study of cognitive relay networks with imperfect channel knowledge. IEEE Commun. Lett. 17(1), 27–30 (2013)
Seyfi, M.; et al.: Relay selection in cognitive radio networks with interference constraints. IET Commun. 7(10), 922–930 (2013)
Nguyen, M.; et al.: Secure cooperative half-duplex cognitive radio networks with \(K\)-th best relay selection. IEEE Access 5, 6678–6687 (2017)
Simon, M.K.; et al.: Digital communication over fading channels. John Wiley & Sons, USA (2005)
Wang, L.; et al.: On the fnite-SNR DMT of two-way AF relaying with imperfect CSI. IEEE Wire. Commun. Lett. 1, 161–164 (2012)
Ho-Van, K.; et al.: Underlay cooperative cognitive networks with imperfect Nakagami-m fading channel information and strict transmit power constraint: interference statistics and outage probability analysis. J. Commun. Netw. 16(1), 10–17 (2014)
Zhao, R.; et al.: Secrecy performance analysis of cognitive decode-and-forward relay networks in Nakagami-\(m\) fading channels. IEEE Trans. Commun. 65(2), 549–563 (2017)
Vucetic, B.; et al.: Space-time coding. John Wiley & Sons, USA (2003)
Gradshteyn, I.S.; et al.: Table of integrals, series and products, 6th edn Academic Press, San Diego, CA (2000)
Sofotasios, P.C.; et al.: Novel expressions for the Marcum and one dimensional Q-functions. In: 2010 7th International Symposium on Wireless Communication Systems, IEEE ISWCS, UK (2010)
Acknowledgements
We would like to thank Ho Chi Minh City University of Technology (HCMUT), VNU-HCM for the support of time and facilities for this study.
Author information
Authors and Affiliations
Corresponding author
Appendices
Appendix A: Formulas for \({{{\hat{\Lambda }}}_1}\), \({{{\hat{\Lambda }}}_2}\), \({{{\hat{\Lambda }}}_3}\)
This appendix derives formulas for \({{{\hat{\Lambda }}}_1}\), \({{{\hat{\Lambda }}}_2}\), and \({{{\hat{\Lambda }}}_3}\) in (22), (23), and (24), respectively, to complete numerical evaluation for the intercept probability.
Invoking \(P_r\) in (9) to further simplify (20) as

where  and
and

Applying [69, eq. (8.352.1)] to expand \(\gamma (\cdot ,\cdot )\) into series yields

where \({{\bar{H}}} = \frac{{\beta _{rp}^{{m_{rp}}}{e^{ - {{\bar{U}}}}}}}{{\Gamma \left( {{m_{rp}}} \right) }}\),  , and
, and  . It is reminded that \({\left( \star \right) }\) is obtained by using binomial expansion while \({\left( \circ \right) }\) is achieved by using the pdf of \({{{{\tilde{g}}}_{rp}}}\) and the definition of the upper incomplete Gamma function \(\Gamma (\cdot ,\cdot )\) in [69].
. It is reminded that \({\left( \star \right) }\) is obtained by using binomial expansion while \({\left( \circ \right) }\) is achieved by using the pdf of \({{{{\tilde{g}}}_{rp}}}\) and the definition of the upper incomplete Gamma function \(\Gamma (\cdot ,\cdot )\) in [69].
Since  in (2) takes two distinct values corresponding to two different conditions, (36) is solved by firstly considering the following two scenarios and then applying total probability law to obtain its explicit form.
in (2) takes two distinct values corresponding to two different conditions, (36) is solved by firstly considering the following two scenarios and then applying total probability law to obtain its explicit form.
Scenario 1: 
This scenario happens as \({g_{sr}} \le \frac{{{\phi }}}{{{P_s}}}\). By taking the expectation over \({g_{sr}} \le \frac{{{\phi }}}{{{P_s}}}\), one deduces and denotes  in (36) for this scenario as
in (36) for this scenario as

where



Now,  ,
,  , and
, and  are derived to solve
are derived to solve  . First of all, expanding \(\gamma (\cdot ,\cdot )\) into series yields
. First of all, expanding \(\gamma (\cdot ,\cdot )\) into series yields

Then, using binomial expansion and performing some manipulations yield

where
Using the pdf of \(g_{sr}\) and applying series expansion for \({{e^{ - {\nu _{sr}}x}}}\), one obtains an explicit form of \({{\mathcal {A}}}\left( {a,b,k} \right) \) as
In \({\left( \bullet \right) }\), variable change \(y=1/x\) is applied to reduce the last integral to the form of the function \(\Theta (\cdot ,\cdot ,\cdot )\) as
where \({\mathrm{Ei}}(\cdot )\) is the exponential integral [69].
Secondly, using the pdf of \(g_{sr}\) and applying [69, eq. (8.352.2)] to expand \(\Gamma (\cdot ,\cdot )\) into series yield

Finally,  is solved by recalling that
is solved by recalling that  and
and  are in a similar form:
are in a similar form:

Scenario 2: 
This scenario occurs as \({g_{sr}} > \frac{{{\phi }}}{{{P_s}}}\). By taking the expectation over this region, one deduces and denotes  in (36) for this scenario as
in (36) for this scenario as

where

Conditioned on these two scenarios, total probability law reduces (36) to

To continue the proof, plugging (18) into (17) and (52) into (19), one deduces \(\Lambda _1\) and \(\Lambda _2\) as
and

Now, inserting (53) and (54) into (16), one obtains (21) where
with








Before deriving (56) and (58)-(65) to obtain explicit forms of \({{{\hat{\Lambda }}}_1}\), \({{{\hat{\Lambda }}}_2}\), and \({{{\hat{\Lambda }}}_3}\) in (22), (23), and (24), respectively, one needs to find the pdf of \(P_s\). Toward this end, one derives firstly the cdf of \(P_s\) as

The first derivative of \({F_{{P_s}}}\left( x \right) \) yields the pdf of \(P_s\) as

Now, we are back to deriving (56) and (58)-(65). Firstly, using  in (44) yields the explicit form of \({{{\tilde{\Lambda }}}_{21}}\) as
in (44) yields the explicit form of \({{{\tilde{\Lambda }}}_{21}}\) as

where
and

Before deriving \({{{\tilde{\Lambda }}}_{21a}}\) and \({\mathcal {B}}(\cdot ,\cdot )\) in an explicit form, the following integral must be solved first:
Using (67) and appropriate variable change, \({{\mathcal {D}}}\left( {{{\bar{J}}},q} \right) \) is represented in an explicit form as

Therefore, using explicit form of \({\mathcal {A}}(\cdot ,\cdot ,\cdot )\) in (46) and performing some simplifications, one expresses \({\mathcal {B}}(\cdot ,\cdot )\) as

where  .
.
Then, using series expansion for \(\gamma (\cdot ,\cdot )\) and binomial expansion to solve \({{{\tilde{\Lambda }}}_{21a}}\) as
Secondly, using  in (48) and
in (48) and  in (49), one deduces
in (49), one deduces

and
Thirdly, \({{{\hat{\Lambda }}}_{1b}}\) is solved as
where \({{{\hat{\Lambda }}}_2}\), which is defined in (56), is solved in an explicit form by using series expansion for \(\gamma (\cdot ,\cdot )\) and binomial expansion as
Fourthly, using  in (44) yields
in (44) yields

where
and

By using series expansion for \(\gamma (\cdot ,\cdot )\) and performing some simplifications, \({{{{\bar{\Lambda }}}}_{21a}}\) is computed as
Also, using the explicit form of \(\mathcal {A}(\cdot ,\cdot ,\cdot )\) in (46) and executing basic manipulations yield

Fifthly, using  in (48) and
in (48) and  in (49), one obtains
in (49), one obtains

and

Finally, \({{{\tilde{\Lambda }}}_{2b}}\) is solved as
Appendix B: Explicit Expression for 
This appendix derives the explicit expression for  in (35) to complete numerical evaluation for the outage probability.
in (35) to complete numerical evaluation for the outage probability.
Since  in (2) accepts two different values corresponding to two conditions,
in (2) accepts two different values corresponding to two conditions,  in (34) is derived by firstly considering the following two scenarios and then applying total probability law to reach its explicit form.
in (34) is derived by firstly considering the following two scenarios and then applying total probability law to reach its explicit form.
Scenario 1: 
This scenario happens as \({g_{sr}} \le \frac{{{\phi }}}{{{P_s}}}\). Incorporating this condition with  in (34) yields a feasible region of
in (34) yields a feasible region of  . By taking the expectation of
. By taking the expectation of  in (30) over
in (30) over  , one deduces and denotes
, one deduces and denotes  for this scenario as
for this scenario as

where

and

Using series expansions for \(\Gamma (\cdot ,\cdot )\) and \(\gamma (\cdot ,\cdot )\) as well as binomial expansion, one achieves

where

At first, we solve \({\bar{{\mathcal {K}}}}\). By variable changes \(t = \sqrt{y}\) and then \(y = t\sqrt{2{\beta _{sr}}/\left( {1 - \psi } \right) }\), one obtains

where \({{{\mathcal {Q}}}_{{m}}}\left( { \cdot , \cdot } \right) \) is the Marcum-Q function in [64, eq. (4.60)].
Inserting (92) into (91) and then applying a simple representation for \(\mathcal {Q}_m(\cdot , \cdot )\) in [70, eq. (6)], it follows that \({{\mathcal {K}}}\left( {a,l} \right) \) is expressed in an explicit form after some basic simplifications:
where the parameter \(\omega \) represents the accuracy-complexity trade-off when simplifying \(\mathcal {Q}_m(\cdot , \cdot )\),  and \({\tilde{V}} = \frac{{\nu _{sr}^{{m_{sr}} + q + j}{{\left( { - 1} \right) }^j}{\psi ^q}{{\left( {1 - \psi } \right) }^{ - q - j}}{\omega ^{1 - 2q}}\Gamma \left( {\omega + q} \right) }}{{j!\Gamma \left( {{m_{sr}}} \right) \Gamma \left( {q + 1} \right) \Gamma \left( {\omega - q + 1} \right) \Gamma \left( {{m_{sr}} + q} \right) }}\).
and \({\tilde{V}} = \frac{{\nu _{sr}^{{m_{sr}} + q + j}{{\left( { - 1} \right) }^j}{\psi ^q}{{\left( {1 - \psi } \right) }^{ - q - j}}{\omega ^{1 - 2q}}\Gamma \left( {\omega + q} \right) }}{{j!\Gamma \left( {{m_{sr}}} \right) \Gamma \left( {q + 1} \right) \Gamma \left( {\omega - q + 1} \right) \Gamma \left( {{m_{sr}} + q} \right) }}\).
Again, using series expansion for \(\Gamma (\cdot ,\cdot )\) yields

Scenario 2: 
This scenario occurs as \({g_{sr}} > \frac{{{\phi }}}{{{P_s}}}\). Incorporating this condition with  in (34) yields a feasible region of \(\left( g_{sr}, \tilde{g}_{sr}\right) \) as
in (34) yields a feasible region of \(\left( g_{sr}, \tilde{g}_{sr}\right) \) as  . By taking the expectation of
. By taking the expectation of  in (30) over
in (30) over  , one deduces and denotes
, one deduces and denotes  for this scenario as
for this scenario as

where  denotes
denotes  computed at
computed at  .
.
Following the same steps as deriving \(\mathcal {K}(\cdot ,\cdot )\), one obtains
where \({{\bar{B}}} = \frac{{{\nu _{sr}}\phi }}{{1 - \psi }}\) and \({{\bar{V}}} = \frac{{\Gamma \left( {\omega + q} \right) {\omega ^{1 - 2q}}{{\left( {1 - \psi } \right) }^{{m_{sr}}}}{\psi ^q}}}{{\Gamma \left( {{m_{sr}}} \right) \Gamma \left( {q + 1} \right) \Gamma \left( {\omega - q + 1} \right) \Gamma \left( {{m_{sr}} + q} \right) }}\).
Conditioned on these two scenarios, total probability law yields  . Therefore,
. Therefore,  in (35) reduces to
in (35) reduces to

where
Now, we proceed to derive \({{{\hat{\Upsilon }}}_1}\), \({{{\hat{\Upsilon }}}_2}\), and \(\hat{{\mathcal {L}}}\) to complete  in (97), eventually completing \(\Upsilon \) in (35). Firstly, inserting (90) into (98) yields
in (97), eventually completing \(\Upsilon \) in (35). Firstly, inserting (90) into (98) yields

where
Plugging (93) into (102), it follows that
where
Using series expansion for \(\Gamma (\cdot ,\cdot )\) and the explicit form of \(\Theta (\cdot ,\cdot ,\cdot )\) in (47), one achieves an explicit form of \({{\mathcal {W}}}\left( c \right) \) as

where

Likewise, inserting (94) into (99) yields
Finally, using series expansion for \(\Gamma (\cdot ,\cdot )\) and binomial expansion, one obtains the following after some basic manipulations:
Rights and permissions
About this article
Cite this article
Le-Thanh, T., Ho-Van, K. Joint Influences of Erroneous Channel Information, Fading Severity, Jamming Suppression Error, Energy Harvesting Non-Linearity on Underlay Relaying Networks. Arab J Sci Eng 47, 14471–14489 (2022). https://doi.org/10.1007/s13369-022-06789-3
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s13369-022-06789-3