Abstract
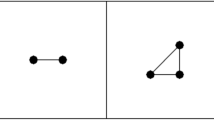
This paper introduces a topological approach to detection of image tampering for forensics purposes. This is based on the emerging Topological Data Analysis (TDA) concept of persistent homological invariants associated with certain image features. Image features of interest are pixels that have a uniform Local Binary pattern (LBP) code representing texture feature descriptors. We construct the sequence of simplicial complexes for increasing sequence of distance thresholds whose vertices are the selected set of pixels, and calculate the corresponding non-increasing sequence of homology invariants (number of connected components). The persistent homology of this construction describes the speed with which the sequence terminates, and our tamper detection scheme exploit its sensitivity to image tampering/degradation. We test the performance of this approach on a sufficiently large image dataset from a benchmark dataset of passport photos, and show that the persistent homology sequence defines a discriminating criterion for the morphing attacks (i.e. distinguishing morphed images from genuine ones).
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Ferrara, M., Franco, A., Maltoni, D.: The magic passport. In: IEEE Joint International Conference on Biometrics, Florida (2014)
GIMP, GNU Image Manipulation Program. https://www.gimp.org/. Accessed 8 May 2017
GIMP, GIMP Animation Package. https://www.gimp.org/tutorials/Using_GAP/. Accessed 8 May 2017
Ferrara, M., Franco, A., Maltoni, D.: On the effects of image alterations on face recognition accuracy. In: Bourlai, T. (ed.) Face Recognition Across the Imaging Spectrum, pp. 195–222. Springer, Cham (2016). doi:10.1007/978-3-319-28501-6_9
Makrushin, A., Neubert, T., Dittmann, J.: Automatic generation and detection of visually faultless facial morphs. In: Proceedings of the 12th International Joint Conference on Computer Vision, Imaging and Computer Graphics Theory and Applications, Porto (2017)
Wang, J., Cha, B., Cho, S., Jay Kuo, C.-C.: Understanding Benford’s Law and its vulnerability in image forensics. In: IEEE International Conference on Multimedia and Expo, New York, USA (2009)
Gunnar, C.: Topology and data. Bull. Am. Math. Soc. 46(2), 255–308 (2009)
Lum, P., Singh, G., Lehman, A., Ishkanov, T., Vejdemo-Johansson, M., Alagappan, M., Carlsson, J., Carlsson, G.: Extracting insights from the shape of complex data using topology. Nature scientific reports, no. 1236 (2013)
Lamar-León, J., García-Reyes, E.B., Gonzalez-Diaz, R.: Human gait identification using persistent homology. In: Alvarez, L., Mejail, M., Gomez, L., Jacobo, J. (eds.) CIARP 2012. LNCS, vol. 7441, pp. 244–251. Springer, Heidelberg (2012). doi:10.1007/978-3-642-33275-3_30
Leon, J.L., Alonso, R., Reyes, E.G., Diaz, R.G.: Topological features for monitoring human activities at distance. In: Mazzeo, P.L., Spagnolo, P., Moeslund, T.B. (eds.) AMMDS 2014. LNCS, vol. 8703, pp. 40–51. Springer, Cham (2014). doi:10.1007/978-3-319-13323-2_4
Sreeparna, B.: Size functions in galaxy morphology classification. Int. J. Comput. Appl. 100(3), 1–4 (2014)
Rieck, B., Leitte, H.: Persistent homology for the evaluation of dimensionality reduction schemes. In: Eurographics Conference on Visualization (EuroVis) (2015)
Janusch, I., Kropatsch, W.: Shape classification using LBP and persistent of critical points. In: International Conference on Discrete Geometry for Computer Imagery, Heidelberg (2016)
Edelsbrunner, H., Morozov, D.: Persistent homology: theory and practice. In: European Congress of Mathematics, Kraków, 2–7 July 2012
Ojala, T., Pietikainen, M., Harwood, D.: A comparative study of texture measures with classification based on featured distributions. Pattern Recogn. 29(1), 51–59 (1996)
Ahonen, T., Hadid, A., Peitikainen, M.: Face description with local binary patterns: application to face recognition. IEEE Trans. Pattern Anal. Mach. Intell. 28(12), 2037–2041 (2006)
Shan, C., Gong, S., McOwan, P.: Facial expression recognition based on local binary patterns: a comprehensive study. Image Vis. Comput. 27, 803–816 (2009)
Meng, J., Gao, Y., Wang, X., Lin, T., Zhang, J.: Face recognition based on local binary patterns with threshold. In: IEEE International Conference on Granular Computing, pp. 352–356 (2010)
Ghrist, R.: Barcodes: the persistent topology of data. Bull. Am. Math. Soc. (New Ser.) 45(1), 61–75 (2008)
Bendich, P., Marron, J., Miller, E., Pieloch, A., Skwerer, S.: Persistent homology analysis of brain artery trees. Ann. Appl. Stat. 10(1), 198–218 (2016)
Rubin, A., Carlsson, G.: Classification of hepatic lesions using the matching metric. Comput. Vis. Image Underst. 121, 36–42 (2014)
Leon, J.L., Cerri, A., Reyes, E.G., Diaz, R.G.: Gait-based gender classification using persistent homology. In: Ruiz-Shulcloper, J., Sanniti di Baja, G. (eds.) CIARP 2013, Part II. LNCS, vol. 8259, pp. 366–373. Springer, Heidelberg (2013). doi:10.1007/978-3-642-41827-3_46
Acknowledgement
Authors would like to thank Dr. Andrey Makrushin for providing morph images and discussions about morph techniques.
Author information
Authors and Affiliations
Corresponding authors
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2017 Springer International Publishing AG
About this paper
Cite this paper
Asaad, A., Jassim, S. (2017). Topological Data Analysis for Image Tampering Detection. In: Kraetzer, C., Shi, YQ., Dittmann, J., Kim, H. (eds) Digital Forensics and Watermarking. IWDW 2017. Lecture Notes in Computer Science(), vol 10431. Springer, Cham. https://doi.org/10.1007/978-3-319-64185-0_11
Download citation
DOI: https://doi.org/10.1007/978-3-319-64185-0_11
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-64184-3
Online ISBN: 978-3-319-64185-0
eBook Packages: Computer ScienceComputer Science (R0)