Abstract
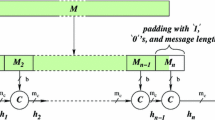
BLAKE is a hash function selected by NIST as one of the 14 second round candidates for the SHA-3 Competition. In this paper, we follow a bottom-up approach to exhibit properties of BLAKE and of its building blocks: based on differential properties of the internal function G, we show that a round of BLAKE is a permutation on the message space, and present an efficient inversion algorithm. For 1.5 rounds we present an algorithm that finds preimages faster than in previous attacks. Discovered properties lead us to describe large classes of impossible differentials for two rounds of BLAKE’s internal permutation, and particular impossible differentials for five and six rounds, respectively for BLAKE-32 and BLAKE-64. Then, using a linear and rotation-free model, we describe near-collisions for four rounds of the compression function.
Supported in part by European Commission through the ICT programme under contract ICT-2007-216676 ECRYPT II. A full version of this article appears in [1].
Chapter PDF
Similar content being viewed by others
Keywords
References
Aumasson, J.P., Guo, J., Knellwolf, S., Meier, W., Matusiewicz, K.: Differential and invertibility properties of BLAKE (full version). Cryptology ePrint Archive, Report 2010/043 (2010)
Aumasson, J.P., Henzen, L., Meier, W., Phan, R.C.W.: SHA-3 proposal BLAKE. Submission to the SHA-3 Competition (2008)
Biham, E., Dunkelman, O.: A framework for iterative hash functions - HAIFA. Cryptology ePrint Archive, Report 2007/278 (2007)
Bernstein, D.J.: ChaCha, a variant of Salsa20, http://cr.yp.to/chacha.html
Ji, L., Liangyu, X.: Attacks on round-reduced BLAKE. Cryptology ePrint Archive, Report 2009/238 (2009)
Biham, E., Biryukov, A., Shamir, A.: Miss in the middle attacks on IDEA and Khufu. In: Knudsen, L.R. (ed.) FSE 1999. LNCS, vol. 1636, pp. 124–138. Springer, Heidelberg (1999)
Knudsen, L.R.: DEAL - a 128-bit block cipher. Technical Report 151, University of Bergen (1998); Submitted as an AES candidate
Jakimoski, G., Desmedt, Y.: Related-key differential cryptanalysis of 192-bit key AES variants. In: Matsui, M., Zuccherato, R.J. (eds.) SAC 2003. LNCS, vol. 3006, pp. 208–221. Springer, Heidelberg (2004)
Biham, E., Dunkelman, O., Keller, N.: Related-key impossible differential attacks on 8-round aes-192. In: Pointcheval, D. (ed.) CT-RSA 2006. LNCS, vol. 3860, pp. 21–33. Springer, Heidelberg (2006)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2010 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Aumasson, JP., Guo, J., Knellwolf, S., Matusiewicz, K., Meier, W. (2010). Differential and Invertibility Properties of BLAKE. In: Hong, S., Iwata, T. (eds) Fast Software Encryption. FSE 2010. Lecture Notes in Computer Science, vol 6147. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-13858-4_18
Download citation
DOI: https://doi.org/10.1007/978-3-642-13858-4_18
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-13857-7
Online ISBN: 978-3-642-13858-4
eBook Packages: Computer ScienceComputer Science (R0)