Abstract
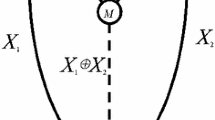
This paper proposes a coding-aware reliable route design scheme to tackle any single link failure for the traffic demands of all possible source destination pairs in a network. Instantaneous recovery is ensured in the proposed scheme by employing network coding (NC) based \(1+1\) protection technique. The proposed scheme considers all possible source destination pairs by creating N scenarios with k sources and a common destination (kSD) according to a given traffic matrix with unequal demands. Each of the N nodes in the network is chosen as the common destination and k nodes, where \(2\le k\le N-1\), among the remaining ones are the sources. We prove that optimum coding-aware \(1+1\) protection route design in kSD scenarios is an NP-hard problem. The proposed scheme tackles this intractable problem by choosing either two or three sources out of k sources at a time according to the largest effective gain first policy, and then routing is assigned to the selected 2SD or 3SD scenario by using our developed mathematical models. We compare the total path costs of NC based \(1+1\) protection for all possible source destination pairs, obtained by our proposed scheme, with that of the conventional \(1+1\) protection technique (without NC). Numerical results observes that 7–16 % of resource saving is achieved in our examined networks. Computation time, example scenarios, and other solution approaches for the proposed scheme are also discussed.






Similar content being viewed by others
Notes
An example that \(\xi _{NO\_NC} > \xi _{NC}\) is included in [21].
When k is even, \(W_2(k)\) is derived from, \(W_2(k)=k \atopwithdelims ()2\). When k is odd, \(W_2(k)\) is derived from \(W_2(k)=k \times W_2(k-1) = k \times k-1 \atopwithdelims ()2\). A similar computation is applicable to \(W_3(k)\).
Equal traffic demands are assumed for computing optimum results, since the mathematical models for 3SD scenarios presented in this paper also assumes equal traffic demands.
References
Menth, M., Duelli, M., & Milbrandt, J. (2009). Resilience analysis of packet-switched communication networks. IEEE/ACM Transactions on Networking, 17(6), 1950–1963.
Zhou, D., & Subramaniam, S. (2000). Survivability in optical neteworks. IEEE Network, 14(6), 16–23.
Kodialam, M., & Lakshman, T. V. (2003). Dynamic routing of bandwidth-guaranteed tunnels using aggregated network resource usage information. IEEE/ACM Transactions on Networking, 11(3), 399–410.
Clouqueur, M., & Grover, W. D. (2002). Availability analysis of span-restorable mesh networks. IEEE JSAC, 20(4), 810–821.
Ahlswede, R., Cai, N., Li, S. Y. R., & Yeung, R. W. (2000). Network information flow. IEEE Transactions on Information Theory, 46(4), 1204–1216.
Kamal, A. E., & Al-Kofahi, O. (2011). Efficient and agile 1+N protection. IEEE Transaction on Communications, 59(1), 169–180.
Kamal, A. E. (2010). 1+N network protection for mesh networks: Network coding-based protection using p-cycles. IEEE/ACM Transactions on Networking, 18(1), 67–80.
Kamal, A. E., Ramamoorthy, A., Long, L., & Li, S. (2011). Overlay protection against link failures using network coding. IEEE/ACM Transactions on Networking, 19(4), 1071–1084.
Aly, S. A., Kamal, A. E., & Al-Kohfahi, O. M. (2012). Network protection codes: Providing self-healing in autonomic networks using network coding. Computer Networks, 56, 99–111.
Barla, I. B., Rambach, F., Schupke, D. A., & Thakur, M. (2010). Network coding for protection against multiple link failures in multi-domain networks. In Proceedings IEEE ICC’10 (pp. 1–6).
Barla, I. B., Rambach, F., Schupke, D. A., & Carle, G. (2010). Efficient protection in single-domain networks using network coding. In IEEE GLOBECOM’10 (pp. 1–5).
Jose, A. A., Muktadir, A. H. A., & Oki, E. (2012). Network coding aware instantaneous recovery scheme based on optimal traffic splitting. IEICE Communications Express, 1(1), 28–32.
Rouayheb, S. E., Sprintson, A., & Georghiades, C. (2011). Robust network codes for unicast connections: A case study. IEEE/ACM Transactions on Networking, 19(3), 644–656.
Avci, S. N., & Ayanoglu, E. (2014). Link failure recovery in large arbitrary networks via network coding. In Proceedings information theory and applications workshop (ITA 2014) (pp. 1–10).
Manley, E. D., Deogun, J. S., Xu, L., & Alexander, D. R. (2010). All-optical network coding. IEEE/OSA JOCN, 2(4), 175–191.
Lun, D. S., Rantakar, N., Medard, M., Koetter, R., Karger, D. R., Ho, T., et al. (2006). Minimum-cost multicast over coded packet networks. IEEE Transactions on Information Theory, 52(6), 2608–2623.
Katti, S., Rahul, H., Hu, W., Katabi, D., Medard, M., & Crowcroft, J. (2008). XORs in the air: Practical wireless network coding. IEEE/ACM Transactions on Networking, 16(3), 497–510.
Al-Kofahi, O., & Kamal, A. E. (2009). Network coding-based protection of many-to-one wireless flows. IEEE JSAC, 27(5), 797–813.
Sengupta, S., Rayanchu, S., & Banerjee, S. (2010). Network coding-aware routing in wireless networks. IEEE/ACM Transactions on Networking, 18(4), 1158–1170.
Xiong, C., & Li, X. (2010). Minimum cost optimization of multicast wireless networks with network coding. In Proceedings 44th CISS’10 (pp. 1–5).
Muktadir, A. H. A., & Oki, E. (2014). Optimum route design in 1+1 protection with network coding for instantaneous recovery. IEICE Transactions on Communications, E97–B(1), 87–104.
Belzner, M., Alexander, F., & Haunstein, H. (2009). Performance of network coding in transport networks with traffic protection. In Proceedings 2009 ITG symposium on photonic networks (pp. 1–7).
Muktadir, A. H. A., & Oki, E. (2012). A mathematical model for routing in 1+1 protection with network coding for instantaneous recovery. IEICE Communications Express, 1(6), 228–233.
Muktadir, A. H. A., & Oki, E. (2014). A heuristic routing algorithm for network coding aware 1+1 protection route design for instantaneous recovery. In Proceedings of the IEEE 15th international conference on high performance switching and routing (HPSR 2014) (pp. 84–89).
Phong, P. V., Muktadir, A. H. A., & Oki, E. (2015). A hybrid instantaneous recovery route design scheme with two different coding aware scenarios. IEICE Communications Express, 4(1), 8–13.
Oki, E. (2012). Linear programming and algorithms for communication networks. Boca Raton: CRC Press.
Bhandari, R. (1999). Survivable networks: Algorithms for diverse routing. New York: Springer.
Garey, M. R., & Johnson, D. S. (1979). Computers and in- tractability: A guide to the theory of NP-completeness. New York: W.H. Freeman.
Kimelfeld, B., & Sagiv, Y. New algorithms for computing Steiner trees for a fixed number of terminals. unpublished manuscript. http://researcher.ibm.com/researcher/files/us-kimelfeld/papers-steiner06.
BRITE (Boston University Representative Internet Topology Generator). http://www.cs.bu.edu/brite/.
CPLEX. (2015). http://www-01.ibm.com/software/integration/optimization/cplex-optimizer/.
Harai, H., Furukawa, H., Fujikawa, K., Miyazawa, T., & Wada, N. (2014). Optical packet and circuit integrated networks and software defined networking extension. Journal of Lightwave Technology, 32(16), 2751–2759.
Hisano, D., Maruta, A., & Kitayama, K. (2013). Demonstration of all-optical network coding by using SOA-MZI based XOR gates. In Proceedings of the OFC/NFOEC conference.
An, Y., Ros, F. D., & Peucheret, C. (2013). All-optical network coding for DPSK signals. In Proceedings of the OFC/NFOEC conference.
Kim, J. H., Jhon, Y. M., Byun, Y. T., Lee, S., Woo, D. H., & Kim, S. H. (2002). All-optical XOR gate using semiconductor optical amplifiers without additional input beam. IEEE Photonics Technology Letters, 12(10), 1436–1438.
Wang, Q., Zhu, G., Chen, H., Jaques, J., Leuthold, J., Piccirilli, A. B., et al. (2004). Study of all-optical XOR using Mach–Zehnder interferometer and differential scheme. IEEE Journal of Quantum Electronics, 40(6), 703–710.
Wang, Y., Cheng, T. H., & Lim, M. H. (2005). A Tabu search algorithm for static routing and wavelength assignment problem. IEEE Communications Letters, 9(9), 841–843.
Armaghan, M., Haghighat, A. T., & Armaghan, M. (2009) QoS multicast routing algorithms based on Tabu search with Elite candidate list. In International conference on application of information and communication technologies (AICT 2009) (pp. 1–5).
Wu, Y., & Liu, W. (2013). Routing protocol based on genetic algorithm for energy harvesting-wireless sensor networks. IET Wireless Sensor Systems, 3(2), 112–118.
Miguel, D., Vallejos, I., Beghelli, R. A., & Ramanj, D. (2009). Genetic algorithm for joint routing and dimensioning of dynamic WDM networks. IEEE/OSA Journal of Optical Communications and Networking, 1(7), 608–621.
Zhao, Y., Sun, R., & Xu, L. (2010) An ant simulated annealing routing algorithm for wireless mesh network. In International conferences on internet technologies and applications (pp. 1–4).
Lopez, A. M., & Heisterkamp, D. R. (2011). Simulated annealing based hierarchical Q-routing: A dynamic routing protocol. In 2011 Eighth international conference on information technology: New generations (ITNG) (pp. 791–796).
Acknowledgments
This work was supported in part by the Ministry of Education, Science, Sports and Culture, Grant-in-Aid for Scientific Research (C) 15K00116 and the National Institute of Information and Communications Technology, Japan. The authors would like to thank Prof. Hiro Ito for his suggestion regarding the complexity discussion of the considered network coding based \(1+1\) protection route design problem.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Al Muktadir, A.H., Oki, E. A coding-aware reliable route design scheme for instantaneous recovery. Telecommun Syst 62, 495–509 (2016). https://doi.org/10.1007/s11235-015-0089-3
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11235-015-0089-3