Abstract
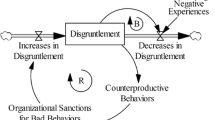
This paper describes the modeling of the potential of an organization to develop an insider threat given certain attributes of its culture. The model represents all employees of the organization and their likelihood of becoming an insider threat. Each employee is instantiated in an agent-zero construct, which accounts for affective, rational, and social behavioral influences. The main driver of behavior is the employee’s level of disgruntlement against the organization. The simulation is run over a period of 10 years and the total number of employees that exceed a certain threshold of becoming an insider threat are computed. This number is compared with survey data on work force ethics as a measure of validity of the simulation results.

Similar content being viewed by others
Notes
Linear regression in which data are modeled using linear predictor functions and unknown model parameters are estimated from the data; non-linear regression in which observational data are modeled by a function which is a nonlinear combination of the model parameters dependent on one or more independent variables; and multiple regression focusing on the relationship between several independent or predictor variables and a dependent or criterion variable.
The authors acknowledge that studies have been limited to specialized areas resulting in isolated findings where factors such as gender, background, and psychological have been omitted (Munshi 2012). Thus, it is for writing simplicity that the male pronoun will be used to identify the insider threat individual throughout this paper.
References
Cappelli DM, Desai AG, Moore AP, Shimeall TJ, Weaver EA, Willke BJ (2008) Management and education of the risk of insider threat (MERIT): system dynamics modeling of computer system sabotage. Software Engineering Institute, Pittsburgh
Cappelli DM, Moore AP, Trzeciak RF (2012) The CERT guide to insider threats: how to prevent, detect, and respond to information technology crimes (Theft, Sabotage, Fraud). Addison-Wesley, Boston
Chinchani R et al (2005) Towards a theory of insider threat assessment. In: IEEE proceedings of the international conference on dependable systems and networks, Yokohama. Institute of Electrical and Electronics Engineers, Inc., pp 108–117
Deloitte (2012) Mitigating the insider threat: building a secure workforce. http://csrc.nist.gov/organizations/fissea/2012-conference/presentations/fissea-conference-2012_mahoutchian-and-gelles.pdf
Dover TJ (2010) The Offender Interaction Process Model. Forensic Exam 19:28–40
Eldardiry H, Evgeniy BL, Juan L, Hanley J, Price B, Brdiczka O (2013) Multi-domain information fusion for insider threat detection. In: IEEE CS security and privacy workshop, San Francisco, CA, May 23–24. Institute of Electrical and Electronics Engineers, Inc., pp 45–51
Epstein JM (2013) Agent zero: toward neurocognitive foundations for generative social science. Princeton University Press, Princeton
Ethics Resource Center (2013) National Business Ethics Survey of the U. S. Workforce. Ethics Resource Center, Arlington
Farahmand F, Spafford EH (2013) Understanding insiders: an analysis of risk-taking behavior. Inform Syst Front 15:5–15
Greitzer FL, Paulson PR, Kangas LJ, Franklin LR, Edgar TW, Frincke DA (2009) Predictive modeling for insider threat mitigation. Pacific Northwest Laboratory, Richland
Greitzer FL, Kangas LJ, Noonan CF, Dalton AC, Hohimer RE (2012) Identifying at-risk employees: modeling psychosocial precursors of potential insider threats. In: Sprague R (ed) 45th Hawaii International Conference on System Science, Maui. Institute of Electrical and Electronics Engineers, Inc., pp 2392–2401
Keeney MD et al (2005) Insider threat study: computer sabotage in critical infrastructure sectors. CERT Program and Software Engineering Institute, Pittsburgh
Kowalski ET et al (2008) Insider threat study: illicit cyber activity in the government sector. U. S. Secret Service and CERT/SEI, Washington, DC
Legg P et al (2012) Towards a conceptual model and reasoning structure for insider threat detection. J Wirel Mobile Netw, Ubiquitous Computing, Dependable Appl 4:20–37
Munshi AP, Dell P, Armstrong H (2012) Insider threat behavior factors: a comparison of theory and reported incidents. In: 45th Hawaii international conference on system science, Maui, January 4–7. Institute of Electrical and Electronics Engineers, Inc., pp 2402–2411
Nguyen N, Reiher P, Kuenning GH (2003) Detecting insider threats by monitoring system call activity. In: 2003 IEEE workshop on information assurance, United States Military Academy, West Point, June 18–20. IEEE Systems, Man and Cybernetics Society. IEEE, pp 45–52
Petty MD (2010) Verification, Validation, and Accreditation. In: Sokolowski JA, Banks CM (eds) Modeling and simulation fundamentals: theoretical underpinnings and practical domains. John Wiley and Sons Inc, Hoboken, pp 325–372
Phyo AH, Furnell SM (2004) A detection-oriented classification of insider IT misuse. Paper presented at the Third Security Conference, Las Vegas, NV
Spooner D et al (2013) spotlight on insider theft of intellectual property inside the U. S. involving Foreign Governments Or Organizations. CERT, Pittsburgh
United States Secret Service National Threat Assessment Center (2004) Insider threat study: illicit cyber-activity in the banking and finance sector. http://www.secretservice.gov/ntac/its_report_040820.pdf
Welinsky U (1999) NetLogo. Center for connected learning and computer-based modeling. Northwestern University, Evanston
Wood BJ (2000) An insider threat model for adversary simulation. In: Anderson RH, Bozek T, Longstaff T, Meitzler W, Skroch M, Van Wyk K (eds) Research on mitigating the insider threat to information systems, vol 2., RAND PublicationsSanta Monica, CA, pp 41–48
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of Interest
The authors declare that they have no conflict of interest.
Rights and permissions
About this article
Cite this article
Sokolowski, J.A., Banks, C.M. & Dover, T.J. An agent-based approach to modeling insider threat. Comput Math Organ Theory 22, 273–287 (2016). https://doi.org/10.1007/s10588-016-9220-6
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10588-016-9220-6