Abstract
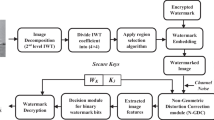
Digital watermarking has been widely used in digital rights management and copyright protection. In this paper, new cryptographic watermark schemes are proposed. Compare to the existing watermarking techniques, our proposed watermark schemes combine both security and efficiency that none of the existing schemes can do. We first develop an algorithm to randomly generate the watermark indices based on the discrete logarithm problem (DLP) and the Fermat’s little theorem. Then we embed watermark signal into the host image in both time domain and frequency domain at the indices. Our security analysis and simulation demonstrate that our proposed schemes can achieve excellent transparency and robustness under the major security attacks and common signal degradations. The novel approaches provided in this paper are ideal for general purpose commercial digital media copyright protection.
Similar content being viewed by others
References
Swanson, M., Kobayashi, M., Tewfik, A.: Multimedia data embedding and watermarking technologies. Proc. IEEE 86(6), 1064–1087 (June 1998)
Hwang, M.-S., Chang, C.-C., Hwang, K.-F.: A watermarking technique based on one-way hash functions. IEEE Trans. Consumer Electron. 45(2), 286–294 (May 1999)
Chen, B., Gornell, G.W.: Quantization index modulation: a class of probably good methods for digital watermarking and information embedding. IEEE Trans. Inf. Theory 47(4), 1423–1443 (May 2001)
Malvar, H.S., Florêncio, D.A.F.: Improved spread spectrum: a new modulation technique for robust watermarking. IEEE Trans. Signal Proc. 51(4), 898–905 (April 2003)
Xie, L., Arce, G.R.: A class of authentication digital watermarks for secure multimedia communication. IEEE Trans. Image Proc. 10(11), 1754–1764 (November 2001)
Tang, C.-W., Hang, H.-M.: A feature-based robust digital image watermarking scheme. IEEE Trans. Signal Proc. 51(4), 950–959 (April 2003)
Cox, I., Kilian, J., Leighton, F., Shamoon, T.: Secure spread spectrum watermarking for multimedia. IEEE Trans. Image Process 6(12), 1673–1687 (December 1997)
Wang, S.-H., Lin, Y.-P.: Wavelet tree quantization for copyright protection watermarking. IEEE Trans. Image Process 13(2), 154–165 (February 2004)
Moulin, P., O’Sullivan, J.: Information-theoretic analysis of information hiding. IEEE Trans. Inf. Theory 49(3), 563–593 (March 2003)
Moulin, P., Mihçak, M.: The parallel-Gaussian watermarking game. IEEE Trans. Inf. Theory 50(2), 272–289 (September 2004)
Craver, S., Memon, N., Yeo, B., Yeung, M.: Can invisible watermarks resolve rightful ownerships? IBM Tech. Rep. RC 20509 (July 1996)
Rivest, R., Shamir, A., Adleman, L.: A method for obtaining digital signatures and public-key cryptosystems. Commun. Assoc. Comp. Mach. 21(2), 120–126 (1978)
Lidl, R., Niederreiter, H.: Finite Fields. Cambridge University Press (2000)
Pérez-González, P., Balado, F., Martin, J.R.H.: Performance analysis of existing and new methods for data hiding with known-host information in additive channels. IEEE Trans. Signal Proc. 51(4), 960–980 (April 2003)
Moulin, P., Mihçak, M.: A framework of evaluating the data-hiding capacity of image sources. IEEE Trans. Image Process 11(9), 1029–1042 (September 2002)
Chandramouli, R., Memon, N.D.: On sequential watermark detection. IEEE Trans. Signal Proc. 51(4), 1034–1044 (2003)
Kirovski, D., Petitcolas, F.A.: Blind pattern matching attack on watermarking systems. IEEE Trans. Signal Proc. 51(4), 1045–1053 (April 2003)
Author information
Authors and Affiliations
Corresponding author
Additional information
Communicated by Lixin Shen and Yuesheng Xu.
Rights and permissions
About this article
Cite this article
Ren, J. A cryptographic watermarking technique for multimedia signals. Adv Comput Math 31, 267–281 (2009). https://doi.org/10.1007/s10444-008-9096-1
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10444-008-9096-1