Abstract
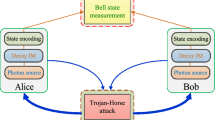
Measurement-device-independent quantum key distribution (MDI-QKD) is proposed to close all possible side channel detector attacks. The security of the original proposal relies on the assumption that the legitimate users can characterize their sources exactly, which might not be satisfied in practice. Later, some MDI-QKD protocols with uncharacterized qubit sources are proposed to remove the assumption that legitimate users must characterize their encoding states. Here we propose a MDI-QKD with uncharacterized coherent sources. The assumption is that legitimate users only ensure that sources, for encoding, are coherent sources (can be expressed as a mixture of Fock states), while the accuracy of the encoding operations and the intensity of the coherent sources cannot be characterized exactly by them. Based on this assumption, we derived the formulas of the security bounds for it under collective attacks, and simulation results of the security bounds are also presented by employing parameters of current QKD technology. It shows that the lower bound of performance can cover long distances.




Similar content being viewed by others
References
Bennett, C. H., Brassard, G.: Quantum cryptography: public-key distribution and coin tossing. In Proceedings of IEEE International Conference on Computers, Systems, and Signal Processing Bangalore, India, pp. 175–179. IEEE, New York (1984)
Ekert, A.K.: Quantum cryptography based on Bell’s theorem. Phys. Rev. Lett. 67(6), 661–663 (1991)
Lo, H.-K., Chau, H.F.: Unconditional security of quantum key distribution over arbitrarily long distances. Science 283(5410), 2050–2056 (1999)
Mayers, D.: Advances in Cryptology-CRYPTO’96, pp. 343–357. Springer, Berlin (1996)
Shor, P.W., Preskill, J.: Simple proof of security of the BB84 quantum key distribution protocol. Phys. Rev. Lett. 85(2), 441–444 (2000)
Gisin, N., Ribordy, G., Tittel, W., Zbinden, H.G.: Quantum cryptography. Rev. Mod. Phys. 74(1), 145–200 (2001)
Boaron, A., Boso, G., Rusca, D., Vulliez, C., Autebert, C., Caloz, M., Perrenoud, M., Gras, G., Bussières, F., Li, M.-J., Nolan, D., Martin, A., Zbinden, H.: Secure quantum key distribution over 421 km of optical fiber. Phys. Rev. Lett. 121(19), 9–13 (2018)
Liao, S.-K., Cai, W.-Q., Liu, W.-Y., Zhang, L., Li, Y., Ren, J.-G., Yin, J., Shen, Q., Cao, Y., Li, Z.-P., Li, F.-Z., Chen, X.-W., Sun, L.-H., Jia, J.-J., Wu, J.-C., Jiang, X.-J., Wang, J.-F., Huang, Y.-M., Wang, Q., Zhou, Y.-L., Deng, L., Xi, T., Ma, L., Hu, T., Zhang, Q., Chen, Y.-A., Liu, N.-L., Wang, X.-B., Zhu, Z.-C., Lu, C.-Y., Shu, Rong, Peng, C.-Z., Wang, J.-Y., Pan, J.-W.: Satellite-to-ground quantum key distribution. Nature 549(7670), 43–47 (2017)
Makarov, V., Anisimov, A., Skaar, J.: Erratum: effects of detector efficiency mismatch on security of quantum cryptosystems. Phys. Rev. A 78(1), 011905–011915 (2008)
Makarov, V., Skaar, J.: Fakes states attack using detector efficiency mismatch on SARG04, phase-time, DPSK, and Ekert protocols. Quantum Inf. Comput. 8(67), 622–635 (2008)
Qi, B., Fung, C.-H.F., Lo, H.-K., Ma, X.: Time-shift attack in practical quantum cryptosystems. Quantum Inf. Comput. 7(12), 73–82 (2007)
Zhao, Y., Fung, C.-H.F., Qi, B., Chen, C., Lo, H.-K.: Quantum hacking: experimental demonstration of time-shift attack against practical quantum key distribution systems. Phys. Rev. A 78(4), 042333–042337 (2008)
Lydersen, L., Wiechers, C., Wittmann, C., Elser, D., Skaar, J., Makarov, V.: Hacking commercial quantum cryptography systems by tailored bright illumination. Nat. Photonics 4(10), 686–689 (2010)
Gerhardt, I., Liu, Q., Lamas-Linares, A., Skaar, J., Kurtsiefer, C., Makarov, V.: Full-field implementation of a perfect eavesdropper on a quantum cryptography system. Nat. Commun. 2, 349 (2011)
Tang, Y.-L., Yin, H.-L., Ma, X., Fung, C.-H.F., Liu, Y., Yong, H.-L., Chen, T.-Y., Peng, C.-Z., Chen, Z.-B., Pan, J.-W.: Source attack of decoy-state quantum key distribution using phase information. Phys. Rev. A 88(2), 022308–022319 (2013)
Mayers, D., Yao, A.: In FOCS, 39th Annual Symposium on Foundations of Computer Science. IEEE, Computer Society Press, Los Alamitos, p. 503 (1998)
Acín, A., Gisin, N., Masanes, L.: From Bell’s theorem to secure quantum key distribution. Phys. Rev. Lett. 97(12), 120405–120408 (2006)
Acín, A., Brunner, N., Gisin, N., Massar, S., Pironio, S., Scarani, V.: Device-independent security of quantum cryptography against collective attacks. Phys. Rev. Lett. 98(23), 230501–230504 (2007)
McKague, M., Mosca, M.: In Proceedings of the Fifth Conference on Theory of Quantum Computation, Communication, and Cryptography, TQC’10, pp. 113–130. Springer, Berlin (2011)
Lim, C.C.W., Portmann, C., Tomamichel, M., Renner, R., Gisin, N.: Device-independent quantum key distribution with local Bell test. Phys. Rev. X 3(3), 031006–031016 (2013)
Lo, H.-K., Curty, M., Qi, B.: Measurement-device-independent quantum key distribution. Phys. Rev. Lett. 108(13), 130503–130519 (2012)
Kaltenbaek, R., Prevedel, R., Aspelmeyer, M., Zeilinger, A.: High-fidelity entanglement swapping with fully independent sources. Phys. Rev. A 79(4), 040302–040305 (2009)
Biham, E., Huttner, B., Mor, T.: Quantum cryptographic network based on quantum memories. Phys. Rev. A 54(4), 2651–2658 (1996)
Rubenok, A., Slater, J., Chan, P., Lucio-Martinez, I., Tittel, W.: A quantum key distribution system immune to detector attacks. Arxiv preprint arXiv:1204.0738 (2012)
T, Ferreira da Silva, Vitoreti, D., Xavier, G.B., do Amaral, G.C., Temporão, G.P., von der Weid, J.P.: Proof-of-principle demonstration of measurement-device-independent quantum key distribution using polarization qubits. Phys. Rev. A 88(5), 052303–052309 (2013)
Liu, Y., Chen, T.-Y., Wang, L.-J., Liang, H., Shentu, G.-L., Wang, J., Cui, K., Yin, H.-L., Liu, N.-L., Li, L., Ma, X., Pelc, J.S., Fejer, M.M., Zhang, Q., Pan, J.-W.: Experimental measurement-device-independent quantum key distribution. Phys. Rev. Lett. 111(13), 130502–130505 (2013)
Tang, Z., Liao, Z., Xu, F., Qi, B., Qian, L., Lo, H.-K.: Experimental demonstration of polarization encoding measurement-device-independent quantum key distribution. Phys. Rev. Lett. 112(19), 190503–190506 (2014)
Yin, H.-L., Chen, T.-Y., Yu, Z.-W., Liu, H., You, L.-X., Zhou, Y.-H., Chen, S.-J., Mao, Y.Q., Huang, M.-Q., Zhang, W.-J., Chen, H., Li, M.-J., Nolan, D., Zhou, F., Jiang, X., Wang, Z., Zhang, Q., Wang, X.-B., Pan, J.-W.: Measurement-device-independent quantum key distribution over a 404 km optical fiber. Phys. Rev. Lett. 117(19), 190501–190515 (2016)
Lucamarini, M., Yuan, Z.L., Dynes, J.F., Shields, A.J.: Overcoming the rate-distance limit of quantum key distribution without quantum repeaters. Nature 557, 400–403 (2018)
Wang, X.-B., Yu, Z.-W., Hu, X.-L.: Twin-field quantum key distribution with large misalignment error. Phys. Rev. A 98(6), 062323–062334 (2018)
Yin, H.L., Fu, Y.: Measurement-device-independent twin-field quantum key distribution. Sci. Rep. 9(1), 3045–3057 (2019)
Yin, Z.Q., Fung, C.-H.F., Ma, X., Zhang, C.-M., Li, H.-W., Chen, W., Wang, S., Guo, G.-C., Han, Z.-F.: Measurement-device-independent quantum key distribution with uncharacterized qubit sources. Phys. Rev. A 88(6), 062322–062330 (2013)
Hwang, W.Y., Su, H.Y., Bae, J.: Improved measurement-device-independent quantum key distribution with uncharacterized qubits. Phys. Rev. A 95(6), 062313–062316 (2017)
Ma, X., Razavi, M.: Alternative schemes for measurement-device-independent quantum key distribution. Phys. Rev. A 86(6), 062319–062330 (2012)
Zhao, Y., Qi, B., Lo, H.-K.: Quantum key distribution with an unknown and untrusted source. Phys. Rev. A 77(5), 052327–052356 (2008)
Liu, Y., Zhao, Qi, Li, M.-H., Guan, J.-Y., Zhang, Y.-B., Bai, B., Zhang, W.-J., Liu, W.-Z., Wu, C., Yuan, X., Li, H., Munro, W.J., Wang, Z., You, L.-X., Zhang, J., Ma, X., Fan, J.-Y., Zhang, Q., Pan, J.-W.: Device-independent quantum random-number generation. Nature 562, 548–551 (2018)
Bennett, C.H.: Quantum cryptography using any two nonorthogonal states. Phys. Rev. Lett. 68(21), 3121–3124 (1992)
Duan, L.-M., Lukin, M.D., Cirac, J.I., Zoller, P.: Long-distance quantum communication with atomic ensembles and linear optics. Nature 414, 413–418 (2001)
Sangouard, N., Simon, C., Minar, J., Zbinden, H., Riedmatten, H.D., Gisin, N.: Long-distance entanglement distribution with single-photon sources. Phys. Rev. A 76(5), 050301–050304 (2007)
Tamaki, K., Lo, H.-K., Fung, C.-H.F., Qi, B.: Phase encoding schemes for measurement-device-independent quantum key distribution with basis-dependent flaw. Phys. Rev. A 85(4), 042307–042323 (2012)
Lo, H.-K., Ma, X., Chen, K.: Decoy state quantum key distribution. Phys. Rev. Lett. 94(23), 230504–230507 (2005)
Hwang, W.-Y.: Quantum key distribution with high loss: toward global secure communication. Phys. Rev. Lett. 91(5), 057901–057904 (2003)
Ma, X., Qi, B., Zhao, Y., Lo, H.-K.: Practical decoy state for quantum key distribution. Phys. Rev. A 72(1), 012326–012356 (2005)
Wang, X.-B.: Beating the photon-number-splitting attack in practical quantum cryptography. Phys. Rev. Lett. 94(23), 230503–230506 (2005)
Wang, X.-B.: Decoy-state protocol for quantum cryptography with four different intensities of coherent light. Phys. Rev. A 72(1), 012322–012333 (2005)
Lo, H.-K., Preskill, J.: Security of quantum key distribution using weak coherent states with nonrandom phases. Quantum Inf. Comput. 7(5), 431–458 (2007)
Lo, H.-K.: Getting something out of nothing. Quantum Inf. Comput. 5(4), 413–418 (2005)
Koashi, M.: Simple security proof of quantum key distribution based on complementarity. New J. Phys. 11(4), 045018–045029 (2009)
Ma, X., Fung, C.-H.F., Boileau, J.-C., Chau, H.: Universally composable and customizable post-processing for practical quantum key distribution. Comput. Secur. 30(4), 172–177 (2011)
Ursin, R., Tiefenbacher, F., Schmitt-Manderbach, T., Weier, H., Scheidl, T., Lindenthal, M., Blauensteiner, B., Jennewein, T., Perdigues, J., Trojek, P., Oemer, B., Fuerst, M., Meyenburg, M., Rarity, J., Sodnik, Z., Barbieri, C., Weinfurter, H., Zeilinger, A.: Entanglement-based quantum communication over 144km. Nature Phys. 3, 481–486 (2007)
Ma, X., Lo, H.-K.: Quantum key distribution with triggering parametric down-conversion sources. New J. Phys. 10(7), 073018–073039 (2008)
Kimble, H.J.: The quantum internet. Nature 453, 1023–1030 (2008)
Razavi, M.: Multiple-access quantum key distribution networks. IEEE Trans. Commun. 60(10), 3071–3079 (2012)
Derka, R., Buzk, V., Ekert, A.K.: Universal algorithm for optimal estimation of quantum states from finite ensembles via realizable generalized measurement. Phys. Rev. Lett. 80(8), 1571–1575 (1998)
Csiszar, I., KÄorner, J.: Broadcast channels with confidential messages. IEEE Trans. Inf. Theory 24(3), 339–348 (1978)
Tsurumaru, T., Tamaki, K.: Security proof for quantum-key-distribution systems with threshold detectors. Phys. Rev. A 78(3), 032302–032309 (2008)
Beaudry, N.J., Moroder, T., Lutkenhaus, N.: Squashing models for optical measurements in quantum communication. Phys. Rev. Lett. 101(9), 093601–093604 (2008)
Ma, X., Lutkenhaus, N.: Improved data post-processing in quantum key distributions and application to loss thresholds in device independent QKD. Quantum Inf. Comput. 12(34), 203–214 (2012)
Wang, C., Song, X.-T., Yin, Z.-Q., Wang, S., Chen, W., Zhang, C.-M., Guo, G.-C., Han, Z.-F.: Phase-reference-free experiment of measurement-device-independent quantum key distribution. Phys. Rev. Lett. 115(16), 160502–160506 (2015)
Ma, X., Zeng, P., Zhou, H.-Y.: Phase-matching quantum key distribution. Phys. Rev. X 8(3), 031043–031070 (2018)
Acknowledgements
The work was supported by the National Natural Science Foundation of China under Grant No. 11464015, the Natural Science Foundation of Hunan Province under Grant No. 14jj6035 and the Science Research Foundation of Education Department of Hunan Province under Grant Nos. (14B147,18C0585).
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Kang, GD., Zhou, QP. & Fang, MF. Measurement-device-independent quantum key distribution with uncharacterized coherent sources. Quantum Inf Process 19, 1 (2020). https://doi.org/10.1007/s11128-019-2494-0
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11128-019-2494-0