Abstract
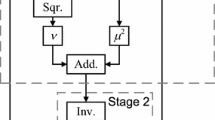
A lot of improvements and optimizations for the hardware implementation of SubBytes of Rijndael, in detail inversion in \({\mathbb F}_{2^8}\) have been reported. Instead of the Rijndael original \({\mathbb F}_{2^8}\), it is known that its isomorphic tower field \({{\mathbb F}{((2^2)^2)}{2}}\) has a more efficient inversion. For the towerings, several kinds of bases such as polynomial and normal bases can be used in mixture. Different from the meaning of this mixture of bases, this paper proposes another mixture that contributes to the reduction of the critical path delay of SubBytes. To the \({{\mathbb F}{(2^2)}{2}}\)–inversion architecture, for example, the proposed mixture inputs and outputs elements represented with normal and polynomial bases, respectively.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Bailey, D., Paar, C.: Optimal Extension Fields for Fast Arithmetic in Public–Key Algorithms. In: Krawczyk, H. (ed.) CRYPTO 1998. LNCS, vol. 1462, pp. 472–485. Springer, Heidelberg (1998)
Canright, D.: A Very Compact S-Box for AES. In: Rao, J.R., Sunar, B. (eds.) CHES 2005. LNCS, vol. 3659, pp. 441–455. Springer, Heidelberg (2005)
Canright, D.: Naval Postgraduate School Technical Report: NPS–MA–05–001 (2005), http://web.nps.navy.mil/~dcanrig/pub/NPS-MA-05-001.pdf
Canright, D., Batina, L.: A Very Compact ”Perfectly Masked” S–Box for AES. In: Bellovin, S.M., Gennaro, R., Keromytis, A.D., Yung, M. (eds.) ACNS 2008. LNCS, vol. 5037, pp. 446–459. Springer, Heidelberg (2008)
Itoh, T., Tsujii, S.: A Fast Algorithm for Computing Multiplicative Inverse in GF(2m) using Normal Basis. Inf. Comput. 78, 171–177 (1988)
Mentens, N.: Secure and Efficient Coprocessor Design for Cryptographic Applications on FPGAs, Doctor thesis, Katholieke Universiteit Leuven (2007)
Morioka, S., Satoh, A.: An optimized S–box circuit arthitecture for low power AES design. In: Kaliski Jr., B.S., Koç, Ç.K., Paar, C. (eds.) CHES 2002. LNCS, vol. 2523, pp. 172–186. Springer, Heidelberg (2003)
National Institute of Standards and Technology (NIST), Advanced Encryption Standard (AES), FIPS publication 197 (2001), http://csrc.nist.gov/encryption/aes/index.html
Satoh, A., Morioka, S., Takano, K., Munetoh, S.: A compact Rijndael hardware architecture with S-box optimization. In: Boyd, C. (ed.) ASIACRYPT 2001. LNCS, vol. 2248, pp. 239–254. Springer, Heidelberg (2001)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2010 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Nogami, Y., Nekado, K., Toyota, T., Hongo, N., Morikawa, Y. (2010). Mixed Bases for Efficient Inversion in \({{\mathbb F}{((2^2)^2)}{2}}\) and Conversion Matrices of SubBytes of AES. In: Mangard, S., Standaert, FX. (eds) Cryptographic Hardware and Embedded Systems, CHES 2010. CHES 2010. Lecture Notes in Computer Science, vol 6225. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-15031-9_16
Download citation
DOI: https://doi.org/10.1007/978-3-642-15031-9_16
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-15030-2
Online ISBN: 978-3-642-15031-9
eBook Packages: Computer ScienceComputer Science (R0)