Abstract
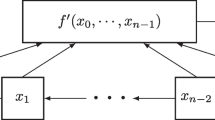
Designers of stream ciphers have generally used ad hoc meth- ods to build systems that are secure against known attacks. There is often a sense that this is the best that can be done, that any system will even- tually fall to a practical attack. In this paper we show that there are families of keystream generators that resist all possible attacks of a very general type in which a small number of known bits of a keystream are used to synthesize a generator of the keystream (called a synthesizing algorithm). Such attacks are exemplified by the Berlekamp-Massey at- tack. We first formalize the notions of a family of feedback registers and of a synthesizing algorithm. We then show that for any function h(n) that is in O(2n/d) for every d > 0, there is a secure family B of periodic sequences in the sense that any efficient synthesizing algorithm outputs a register of size h(log(period(B))) given the required number of bits of a sequence B ∈ B of large enough period. This result is tight in the sense it fails for any faster growing function h(n). We also consider several variations on this scenario.
This research funded in part by NSF grant #NCR-9400762.
Chapter PDF
Similar content being viewed by others
References
J. Balcázar, J. Diaz, and J. Gabarró: Structural Complexity I. Berlin: Springer 1988.
M. Blum and S. Micali: How to generate cryptographically strong sequences of pseudorandom bits. SIAM Journal on Computing 13, 850–864 (1984).
G. Cohen and S. Litsyn: On the covering radius of Reed-Muller codes. Discrete Mathematics 106–107, 147–155 (1992).
A.H. Chan and R.A. Games: On the linear span of binary sequences from finite geometries, q odd. IEEE Transactions on Information Theory 36, 548–552 (1990).
C. Ding: The differential cryptanalysis and design of natural stream ciphers. In: R. Anderson (ed.): Fast Software Encryption: Proceedings of 1993 Cambridge Security Workshop. Lecture Notes in Computer Science 809. Berlin: Springer 1994, pp. 101–120.
J. Golić: Linear cryptanalyis of stream ciphers. In: B. Preneel (ed.): Fast Software Encryption: Proceedings of 1994 Leuven Security Workshop. Lecture Notes in Computer Science 1008. Berlin: Springer 1995, pp. 154–169.
E.J. Groth: Generation of binary sequences with controllable complexity. IEEE Transactions on Information Theory IT-17, 288–296 (1971).
E.L. Key: An Analysis of the structure and complexity of nonlinear binary sequence generators. IEEE Transactions on Information Theory IT-22, 732–736 (1976).
A. Klapper: The Vulnerability of Geometric Sequences Based on Fields of Odd Characteristic. Journal of Cryptology 7, 33–51 (1994).
A. Klapper and M. Goresky: 2-Adic Shift Registers. In: R. Anderson (ed.): Fast Software Encryption: Proceedings of 1993 Cambridge Security Workshop. Lecture Notes in Computer Science 809. Berlin: Springer 1994, pp. 174–178.
A. Klapper and M. Goresky: Feedback Shift Registers, Combiners with Memory, and 2-Adic Span, University of Kentucky, Department of Computer Science Technical Report, 1995.
A. Klapper and M. Goresky: Cryptanalysis Based on 2-Adic Rational Approximation. In: D. Coppersmith (ed.) Advances in Cryptology — CRYPTO’ 95. Lecture Notes in Computer Science 963. Berlin: Springer 1994, pp. 262–273.
J.L. Massey: Shift register sequences and BCH decoding. IEEE Transactions on Information Theory IT-15, 122–127 (1969).
U. M. Maurer: A Provably-Secure Strongly-Randomized Cipher. In: S. Vanstone (ed.) Advances in Cryptology — CRYPTO’ 90. Lecture Notes in Computer Science 473. Berlin: Springer 1991, pp. 361–73.
R. Rueppel: Analysis and Design of Stream Ciphers. New York Springer, 1986.
R.A. Rueppel and O.J. Staffelbach: Products of linear recurring sequences sith maximum complexity, IEEE Transactions on Information Theory IT-33, 124–129 (1987).
T. Siegenthaler: Decrypting a class of stream ciphers using cipertext only. IEEE Transactions on Computing 34, 81–85 (1985).
A. Yao: Theory and applications of trapdoor functions. In: Proceedings, 23rd IEEE Symposium on Foundations of Computer Science, 1982, pp. 80–91.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 1996 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Klapper, A. (1996). On the Existence of Secure Feedback Registers. In: Maurer, U. (eds) Advances in Cryptology — EUROCRYPT ’96. EUROCRYPT 1996. Lecture Notes in Computer Science, vol 1070. Springer, Berlin, Heidelberg. https://doi.org/10.1007/3-540-68339-9_23
Download citation
DOI: https://doi.org/10.1007/3-540-68339-9_23
Published:
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-61186-8
Online ISBN: 978-3-540-68339-1
eBook Packages: Springer Book Archive