Abstract
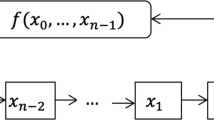
In this paper, we present the rainbow attack on stream ciphers filtered by Maiorana-McFarland functions. This can be considered as a generalization of the time-memory-data trade-off attack of Mihaljevic and Imai on Toyocrypt. First, we substitute the filter function in Toyocrypt (which has the same size as the LFSR) with a general Maiorana-McFarland function. This allows us to apply the attack to a wider class of stream ciphers. Moreover, our description replaces the time-memory-data trade-off attack with the rainbow attack of Oeshlin, which offers better performance and implementation advantages. Second, we highlight how the choice of different Maiorana-McFarland functions can affect the effectiveness of our attack. Third, we show that the attack can be modified to apply on filter functions which are smaller than the LFSR or on filter-combiner stream ciphers. This allows us to cryptanalyze other configurations commonly found in practice. Finally, filter functions with vector output are sometimes used in stream ciphers to improve the throughput. Therefore the case when the Maiorana-McFarland functions have vector output is investigated. We found that the extra speed comes at the price of additional weaknesses which make the attacks easier.
Chapter PDF
Similar content being viewed by others
References
Adams, C.: The CAST-128 Encryption Algorithm. RFC 2144
Biryukov, A., Shamir, A.: Cryptanalytic Time/Memory/Data Tradeoffs for Stream Ciphers. In: Okamoto, T. (ed.) ASIACRYPT 2000. LNCS, vol. 1976, pp. 1–13. Springer, Heidelberg (2000)
Canteaut, A., Trabbia, M.: Improved Fast Correlation Attacks Using Parity-Check Equations of Weight 4 and 5. In: Preneel, B. (ed.) EUROCRYPT 2000. LNCS, vol. 1807, pp. 573–588. Springer, Heidelberg (2000)
Carlet, C.: A Larger Class of Cryptographic Boolean Functions via a Study of the Maiorana-McFarland Construction. In: Yung, M. (ed.) CRYPTO 2002. LNCS, vol. 2442, pp. 549–564. Springer, Heidelberg (2002)
Fiat, A., Naor, M.: Rigorous Time/Space Tradeoffs for Inverting Functions. In: STOC 1991, pp. 534–541 (1991)
Gong, G., Khoo, K.: Additive Autocorrelation of Resilient Boolean Functions. In: Matsui, M., Zuccherato, R.J. (eds.) SAC 2003. LNCS, vol. 3006, pp. 275–290. Springer, Heidelberg (2004)
Hellman, M.: A Cryptanalytic Time-Memory Trade-Off. IEEE Trans. on Information Theory 26, 401–406 (1980)
Matsui, M.: Linear Cryptanalysis Method for DES Cipher. In: Helleseth, T. (ed.) EUROCRYPT 1993. LNCS, vol. 765, pp. 386–397. Springer, Heidelberg (1994)
Mihaljevic, M.J., Imai, H.: Cryptanalysis of Toyocrypt-HS1 Stream Cipher. IEICE Trans. Fundamentals, E85-A(1), 66–73 (2002)
Mukhopadyay, S., Sarkar, P.: Application of LFSRs in Time/Memory Trade-Off Cryptanalysis, Indian Statistical Institute Technical Report No. ASD/04/9 (Revised Version) (2005)
Oechslin, P.: Making a Faster Cryptanalytic Time-Memory Trade-Off. In: Boneh, D. (ed.) CRYPTO 2003. LNCS, vol. 2729, pp. 617–630. Springer, Heidelberg (2003)
Pasalic, E., Maitra, S.: Linear Codes in Constructing Resilient Functions with High Nonlinearity. In: Vaudenay, S., Youssef, A.M. (eds.) SAC 2001. LNCS, vol. 2259, pp. 60–74. Springer, Heidelberg (2001)
Sarkar, P.: The Filter-Combiner Model for Memoryless Synchronous Stream Ciphers. In: Yung, M. (ed.) CRYPTO 2002. LNCS, vol. 2442, pp. 533–548. Springer, Heidelberg (2002)
Sarkar, P., Maitra, S.: Nonlinearity Bounds and Constructions of Resilient Boolean Functions. In: Bellare, M. (ed.) CRYPTO 2000. LNCS, vol. 1880, pp. 515–532. Springer, Heidelberg (2000)
Sarkar, P., Maitra, S.: Construction of Nonlinear Boolean Functions with Important Cryptographic Properties. In: Preneel, B. (ed.) EUROCRYPT 2000. LNCS, vol. 1807, pp. 485–506. Springer, Heidelberg (2000)
Seberry, J., Zhang, X.-M., Zheng, Y.: On Constructions and Nonlinearity of Correlation Immune Functions. In: Helleseth, T. (ed.) EUROCRYPT 1993. LNCS, vol. 765, pp. 181–199. Springer, Heidelberg (1994)
Siegenthaler, T.: Decrypting a Class of Stream Ciphers using Ciphertexts only. IEEE Transactions on Computers C34(1), 81–85 (1985)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2006 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Khoo, K., Gong, G., Lee, HK. (2006). The Rainbow Attack on Stream Ciphers Based on Maiorana-McFarland Functions. In: Zhou, J., Yung, M., Bao, F. (eds) Applied Cryptography and Network Security. ACNS 2006. Lecture Notes in Computer Science, vol 3989. Springer, Berlin, Heidelberg. https://doi.org/10.1007/11767480_13
Download citation
DOI: https://doi.org/10.1007/11767480_13
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-34703-3
Online ISBN: 978-3-540-34704-0
eBook Packages: Computer ScienceComputer Science (R0)