Abstract
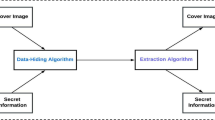
Recent advancements in digital technologies has greatly facilitated the huge growth of complex images over the internet channels leading to security threats causing unauthorised information access. Such complex images are perceived as a reliable means for secret communication. Hence an active research is carried out for steganalysis – a method to determine the presence of hidden information in the multimedia files. The primary challenge faced by the existing steganalysis approaches is, to be able to extract and learn high level feature representations from images of high texture complexity which is somewhat difficult to be achieved by a single deep learning(DL)-based steganalyzer. In this work, we expound an ensemble of deep models with decision level fusion strategy in predicting an image as cover or stego. The ensemble of validated reference models aims to achieve better performance than using a single CNN architecture. The proposed model comprises of three potent pre-trained deep fine-tuned models- VGG19, ResNet50 and Inceptionv3 followed by a majority voting scheme for spatial image steganalysis task. In comparison to convolution neural networks (CNN) specifically created for steganalysis, such as Qian-Net[22],XU-Net[25],Ye-Net[30],Yedroudj-Net[31], Zhu-Net[29], SR-Net[52], GBRASNet[34], trained from scratch, the suggested model performs significantly better. The proposed framework is compared against eight existing competitive state-of-the-art (SOTA) models over a two class dataset. Experiments are conducted on benchmark image dataset BOSSBase1.01 and BOWS2. This claim is substantiated experimentally on two well known content-adaptive steganographic algorithms WOW and S-UNIWARD with payloads 0.2bpp and 0.4bpp respectively. Extensive experiments and evaluations reveal that our proposed approach yields an accuracy of 99.16% on WOW (0.2bpp), 99.21% on WOW (0.4bpp), 99.07% on S-UNIWARD (0.2bpp), and 99.69% on S-UNIWARD (0.4bpp) steganography algorithms. Moreover, our approach results in better generalization performance, reduced training time and increases accuracy (ACC) over the existing state-of-the-art (SOTA) steganalytic architectures.












Similar content being viewed by others
Data availability
Data will be made available on reasonable request.
References
Conway M (2003) Code wars: Steganography, signals intelligence, and terrorism. Know Techn Pol 16:45–62. https://doi.org/10.1007/s12130-003-1026-4
Kolade O, Olayinka AA, Sunday F, Adesoji O, Olubusola IF (2015) Detection of stego-images in communication among the terrorist Boko-Haram sect in Nigeria. J Data Anal Inf Process 3(04):168
Pevný T, Bas P, Fridrich J (2009) Steganalysis by subtractive pixel adjacency matrix. In Proceedings of the 11th ACM workshop on Multimedia and security (pp. 75–84)
Kodovsky J, Binghamton S, Fridrich J (2009) Calibration revisited. Proceedings of the 11th ACM Multimedia & Security Workshop. https://doi.org/10.1145/1597817.1597830
Yedroudj M, Chaumont M, Comby F, Oulad Amara A, Bas P (2020) Pixels-off: Data-augmentation complementary solution for deep-learning steganalysis. https://doi.org/10.1145/3369412.3395061
Tang W, Tan S, Li B, Huang J (2017) Automatic steganographic distortion learning using a generative adversarial network. IEEE Signal Processing Letters, pp 1–1. https://doi.org/10.1109/LSP.2017.2745572.
Qian Y, Dong J, Wang W, Tan T (2016) Learning and transferring representations for image steganalysis using convolutional neural network. In 2016 IEEE international conference on image processing (ICIP) (pp. 2752–2756). Ieee
Ozcan S, Mustaçoglu AF (2018) Transfer learning effects on image steganalysis with pre-trained deep residual neural network model. 2018 IEEE International Conference on Big Data (Big Data), 2280–2287
Yang H, He H, Zhang W, Cao X (2021) FedSteg: a federated transfer learning framework for secure image steganalysis. In: IEEE Transactions on Network Science and Engineering 8(2):1084–1094. https://doi.org/10.1109/TNSE.2020.2996612
Avcibas I, Memon N, Sankur B (2003) Steganalysis using image quality metrics. IEEE Trans Image Process 12(2):221–229
Fridrich, J. (2004). Feature-based steganalysis for JPEG images and its implications for future design of steganographic schemes. In International Workshop on Information Hiding (pp. 67–81). Berlin: Springer Berlin Heidelberg
Shi YQ, Chen C, Chen W (2006) A Markov process based approach to effective attacking JPEG steganography. Information Hiding
Zhou Z, Hui M (2009) Steganalysis for Markov feature of difference array in DCT domain. 2009 Sixth International Conference on Fuzzy Systems and Knowledge Discovery 7:581–584
Holotyak T, Fridrich J, Voloshynovskiy S (2005) Blind statistical steganalysis of additive steganography using wavelet higher order statistics, pp 273–274. https://doi.org/10.1007/11552055_31
Villa Estrada HF, Jaramillo Pérez JC (2015) Aplicaciones de la esteganografía en la seguridad informática. Available: https://www.sans.org/readingroom/whitepapers/stenganography/hiding-plain-view-steganography-terrorist-tool-551
Thampi SM (2008) Information hiding techniques: a tutorial review. arXiv preprint arXiv:0802.3746
Anderson RJ, Petitcolas FAP (1998) On the limits of steganography. In: IEEE Journal on Selected Areas in Communications 16(4):474–481. https://doi.org/10.1109/49.668971
Salakhutdinov R, Hinton G (2009) Deep boltzmann machines. In Artificial intelligence and statistics (pp. 448–455). PMLR
Larochelle H, Bengio Y, Louradour J, Lamblin P (2009) Exploring strategies for training deep neural networks. J Mach Learn Res 10(1):40. https://doi.org/10.1145/1577069.1577070
Qian Y, Dong J, Wang W, Tan T (2015) Deep learning for steganalysis via convolutional neural networks. Proceedings of SPIE - The International Society for Optical Engineering, 9409. https://doi.org/10.1117/12.2083479
Fridrich J, Kodovsky J (2012) Rich models for steganalysis of digital images. IEEE Trans Inf Forensics Secur 7(3):868–882
Xu G, Wu HZ, Shi YQ (2016) Structural design of convolutional neural networks for steganalysis. IEEE Signal Process Lett 23(5):708–712
Yang S, Sun Y, Tang G, Jiang M (2018) Analysis for Influence of Training Data Sequence on CNN-based Steganalysis. In 2018 IEEE 4th International Conference on Computer and Communications (ICCC) (pp. 2110–2114). IEEE. Zhang, R., Zhu, F., Liu, J., & Liu, G. (2018). Efficient feature learning and multi-size image steganalysis based on CNN. ArXiv, abs/1807.11428
Ni J, Ye J, Yi Y (2017) Deep learning hierarchical representations for image steganalysis. IEEE Transactions on Information Forensics and Security, pp 1–1. https://doi.org/10.1109/TIFS.2017.2710946
Yedroudj M, Comby F, Chaumont M (2018) Yedroudj-net: An efficient CNN for spatial steganalysis. In: 2018 IEEE International Conference on Acoustics, Speech and Signal Processing (ICASSP) (pp 2092–2096). IEEE
He K, Zhang X, Ren S, Sun J (2015) Spatial pyramid pooling in deep convolutional networks for visual recognition. IEEE Trans Pattern Anal Mach Intell 37(9):1904–1916
Rubio Alejandro, Grisales Jesus, Tabares Soto Reinel, Ramos-Pollán Raúl, Ortíz Mario, Arteaga Arteaga Harold, Isaza Gustavo, Arias Daniel, Orozco Arias, Simon, Burbano Jàcome Alejandro (2021) GBRAS-Net: a convolutional neural network architecture for spatial image steganalysis. IEEE Access 9:14340–14350. https://doi.org/10.1109/ACCESS.2021.3052494.
Szegedy C, Vanhoucke V, Ioffe S, Shlens J, Wojna Z (2016) Rethinking the inception architecture for computer vision. In Proceedings of the IEEE conference on computer vision and pattern recognition (pp. 2818–2826)
He K, Zhang X, Ren S, Sun J (2016) Deep residual learning for image recognition. In: Proceedings of the IEEE conference on computer vision and pattern recognition (pp 770–778)
Simonyan K, Zisserman A (2014) Very deep convolutional networks for large-scale image recognition. arXiv preprint arXiv:1409.1556
Krizhevsky Alex, Sutskever I, Hinton G (2012) Imagenet classification with deep convolutional neural networks, pp 1097–1105
Holub V, Fridrich J (2013) Designing steganographic distortion using directional filters. IEEE International Workshop on Information Forensics and Security 2:234–239
Holub V, Fridrich J, Denemark T (2014) Universal distortion function for steganography in an arbitrary domain. EURASIP J Inf Secur 1. https://doi.org/10.1186/1687-417X-2014-1
Tan S, Li B (2015) Stacked convolutional auto-encoders for steganalysis of digital images. https://doi.org/10.1109/APSIPA.2014.7041565
Boroumand M, Chen M, Fridrich J (2018) Deep residual network for steganalysis of digital images. IEEE Trans Inf Forensics Secur 14(5):1181–1193
Liao X, Yin J, Chen M, Qin Z (2020) Adaptive payload distribution in multiple images steganography based on image texture features. IEEE Transactions on Dependable and Secure Computing, pp 1–1. https://doi.org/10.1109/TDSC.2020.3004708
Liao X, Yu Y, Li B, Li Z, Qin Z (2019) A new payload partition strategy in color image steganography. IEEE Trans Circuits Syst Video Technol 30(3):685–696
Tan J, Liao X, Liu J, Cao Y, Jiang H (2021) Channel attention image steganography with generative adversarial networks. IEEE Trans Netw Sci Eng 9(2):888–903
Binghamton University (2015) Steganographic algorithms. Available at http://dde.binghamton.edu/download/stego_algorithms/. Accessed Oct 2022
Sedighi V, Cogranne R, Fridrich J (2015) Content-adaptive steganography by minimizing statistical detectability. IEEE Trans Inf Forensics Secur 11(2):221–234
Pevný T, Filler T, Bas P (2010) Using high-dimensional image models to perform highly undetectable steganography. In Information Hiding: 12th International Conference, IH 2010, Calgary, AB, Canada, June 28-30, 2010, Revised Selected Papers 12 (pp. 161-177). Springer, Berlin. Accessed 2022
Denemark T, Sedighi V, Holub V, Cogranne R, Fridrich J (2014) Selection-channel-aware rich model for steganalysis of digital images. In 2014 IEEE International Workshop on Information Forensics and Security (WIFS) (pp. 48–53). IEEE
Tang W, Li H, Luo W, Huang J (2014) Adaptive steganalysis against WOW embedding algorithm. In: Proceedings of the 2nd ACM workshop on Information hiding and multimedia security (IH&MMSec ’14). Association for Computing Machinery, New York, NY, USA, pp 91–96. https://doi.org/10.1145/2600918.2600935
Tang W, Li H, Luo W, Huang J (2016) Adaptive steganalysis based on embedding probabilities of pixels. IEEE Trans Inf Forensics Secur 11:734–745
Denemark T, Fridrich J, Comesaña P (2016) Improving selection-channel-aware steganalysis features. Electron Imaging 2016:1–8. https://doi.org/10.2352/ISSN.2470-1173.2016.8.MWSF-080
Kadhim IJ, Premaratne P, Vial PJ, Al-Qershi OM, Al-Shebani Q (2020) Towards a Universal Steganalyser Using Convolutional Neural Networks. In Intelligent Computing Methodologies: 16th International Conference, ICIC 2020, Bari, Italy, October 2–5, 2020, Proceedings, Part III 16 (pp. 611–623). Springer International Publishing
Agarwal S, Kim C, Jung KH (2022) Steganalysis of Context-Aware Image Steganography Techniques Using Convolutional Neural Network. Appl Sci 12(21):10793
Dwaik A, Belkhouche Y (2022) Analysis of Deep Learning-Based Image Steganalysis Methods Under Different Steganographic Algorithms. In International Symposium on Visual Computing (pp. 284–294). Cham: Springer
Liu F, Zhou X, Yan X, Lu Y, Wang S (2021) Image steganalysis via diverse filters and squeeze-and-excitation convolutional neural network. Mathematics 9(2):189. https://doi.org/10.3390/math9020189
Zhang H, Liu F, Song Z, Zhang X, Zhao Y, (2022) "AG-Net: An Advanced General CNN Model for Steganalysis," in IEEE Access, vol. 10, pp. 44116-44122. https://doi.org/10.1109/ACCESS.2022.3150276.
Su H, Han M, Liang J, Yu S (2022) Steganalysis of image with adaptively parametric activation. arXiv preprint arXiv:2203.12843
Swarnkar N, Rawal A, Patel G (2021) A paradigm shift for computational excellence from traditional machine learning to modern deep learning-based image steganalysis. In: Data Science and Innovations for Intelligent Systems (pp 209–240). CRC Press
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflicts of Interest
The authors declare that there are no conflicts of interest.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Swarnkar, N., Thomas, A. & Selwal, A. A generalized image steganalysis approach via decision level fusion of deep models. Multimed Tools Appl 83, 43513–43538 (2024). https://doi.org/10.1007/s11042-023-17068-0
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-023-17068-0