Abstract
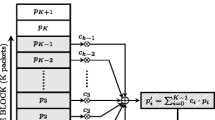
In this paper, we propose Cloak—a new class of reliable timing channels—which is fundamentally different from other timing channels in several aspects. First, Cloak encodes a message by a unique distribution of N packets over X TCP flows. The combinatorial nature of the encoding methods increases the channel capacity largely with (N,X). Second, Cloak offers ten different encoding and decoding methods, each of which has a unique tradeoff among several important considerations, such as channel capacity and the need for packet marking. Third, the packet transmissions modulated by Cloak could be carefully crafted to mimic the normal TCP flows in a typical TCP-based application session. Although Cloak’s basic idea is simple, we show in this paper how we tackle a number of challenging issues systematically. Our experiment results collected from PlanetLab nodes and a test bed suggest that Cloak is feasible under various network conditions and different round-trip delays.
Chapter PDF
Similar content being viewed by others
References
Shah, G., Molina, A., Blaze, M.: Keyboards and covert channels. In: Proc. USENIX Security (2006)
Singh, A., Nordstro, O., Lu, C., Santos, A.: Malicious ICMP tunneling: Defense against the vulnerability. In: Safavi-Naini, R., Seberry, J. (eds.) ACISP 2003. LNCS, vol. 2727, Springer, Heidelberg (2003)
Schechter, S., Smith, M.: Access for sale: A new class of worm. In: Proc. ACM Workshop on Rapid Malcode (WORM), ACM Press, New York (2003)
Rogers, R., Devost, M.: Hacking a Terror Network: The Silence Threat of Covert Channels. Syngress (2005)
Borders, K., Prakash, A.: Web Tap: Detecting covert Web traffic. In: Proc. ACM CCS, ACM Press, New York (2004)
Feamster, N., Balazinska, M., Harfst, G., Balakrishnan, H., Karger, D.: Infranet: Circumventing censorship and surveillance. In: Proc. USENIX Security (2002)
Wang, X., Reeves, D.: Robust correlation of encrypted attack traffic through stepping stones by watermarking the interpacket timing. In: Proc. ACM CCS, ACM Press, New York (2003)
Wang, X., Chen, S., Jajodia, S.: Tracking anonymous peer-to-peer VoIP calls on the Internet. In: Proc. ACM CCS, ACM Press, New York (2005)
Gligor, V.: A guide to understanding covert channel analysis of trusted systems (light pink book). Technical Report NCSC-TG-030, National Computer Security Center (1993)
DoD US: Department of defense trusted computer system evaluation criteria (orange book). Technical Report DoD 5200.28-STD, National Computer Security Center (1985)
Bishop, M.: Introduction to Computer Security. Addison-Wesley, Reading (2005)
Cabuk, S., Brodley, C., Shields, C.: IP covert timing channels: Design and detection. In: Proc. ACM CCS, ACM Press, New York (2004)
Watson, D., Smart, M., Malan, G., Jahanian, F.: Protocol scrubbing: Network security through transparent flow modification. In: IEEE/ACM Trans. Networking (2004)
Handley, M., Kreibich, C., Paxson, V.: Network intrusion detection: Evasion, traffic normalization, and end-to-end protocol semantics. In: Proc. USENIX Security Symp. (2001)
Fisk, G., Fisk, M., Papadopoulos, C., Neil, J.: Eliminating steganography in Internet traffic with active wardens. In: Proc. Information Hiding Workshop (2002)
Stanley, R.: Enumerative Combinatorics. Cambridge University Press, Cambridge (1997)
Ahsan, K., Kundur, D.: Practical data hiding in TCP/IP. In: Proc. Workshop on Multimedia Security (2002)
Chakinala, R., Kumarasubramanian, A., Manokaran, R., Noubir, G., Rangan, C., Sundaram, R.: Steganographic communication in ordered channels. In: Proc. Information Hiding Workshop (2006)
Berk, V., Giani, A., Cybenko, G.: Detection of covert channel encoding in network packet delays. Technical Report TR2005536, Department of Computer Science, Dartmouth College (2005)
Luo, X., Chan, E., Chang, R.: Cloak: A ten-fold way for reliable covert communications (full version) (2007), http://www.comp.polyu.edu.hk/~csrchang/CloakFull07.pdf
Yeung, R.: A First Course in Information Theory. Kluwer Academic, Dordrecht (2002)
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2007 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Luo, X., Chan, E.W.W., Chang, R.K.C. (2007). Cloak: A Ten-Fold Way for Reliable Covert Communications. In: Biskup, J., López, J. (eds) Computer Security – ESORICS 2007. ESORICS 2007. Lecture Notes in Computer Science, vol 4734. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-74835-9_19
Download citation
DOI: https://doi.org/10.1007/978-3-540-74835-9_19
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-74834-2
Online ISBN: 978-3-540-74835-9
eBook Packages: Computer ScienceComputer Science (R0)