Abstract
While there are several secure concurrency control protocols for multilevel database management systems, most of them employ timestamp ordering or multiple versions of data or a hybrid protocol that utilizes both. The only known secure locking protocol that maintains single version data and can guarantee serializability, immediately aborts a higher level transaction whenever any of its locks at the lower levels is broken.
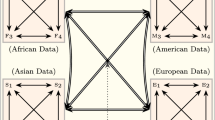
In this paper, we offer two secure locking protocols. The first protocol produces pairwise serializable histories. The second protocol generates serializable histories if the security levels form a total order; however, in general, when the security levels form a partial order, it generates MLS-serializable histories, a notion of correctness that we introduce. The proposed protocols maintains single version data and require only the lock manager to be trusted; a higher level transaction can continue its execution and commit successfully even if some of its locks at the lower levels are broken. Rather than immediately aborting the high transaction when any of its low lock is broken, our protocols wait until such time as executing a high level action will actually create a cycle in the serialization graph, not merely whenever there is the possibility of a cycle being formed. These protocols work by a method of “painting” certain transactions and the data items accessed by these transactions and by detecting a cycle at the moment it is imminent in the serialization graph.
Chapter PDF
Similar content being viewed by others
Keywords
References
Ammann, P., Jaeckle, F. & Jajodia, S. (1995), ‘Concurrency control in secure multi-level databases via a two-snapshot algorithm’, Journal of Computer Security 3 (3), 87–113.
Ammann, P. & Jajodia, S. (1992), A timestamp ordering algorithm for secure, single-version multilevel databases, in C. E. Landwehr, ed., ‘Database Security, V: Status and Prospects’, North-Holland, Amsterdam, pp. 191–202.
Ammann, P. & Jajodia, S. (1994), Planar lattice security structures for multilevel replicated databases, in T. F. Keefe & C. E. Landwehr, eds, ‘Database Security VII: Status and Prospects’, North-Holland, Amsterdam, pp. 125–134.
Ammann, P, Jajodia, S. & Prankl, P (1996), ‘Globally consistent event ordering in one-directional distributed environments’, IEEE Trans. on Parallel and Distributed Systems 7 (6), 665–670.
Bernstein, P. A., Hadzilacos, V. & Goodman, N. (1987), Concurrency Control and Recovery in Database Systems, Addison-Wesley, Reading.
Denning, D. E. (1982), Cryptography and Data Security, Addison-Wesley, Reading.
Gray, J. & Reuter, A. (1993), Transaction Processing: Concept and Techniques, Morgan Kaufmann, San Mateo, CA.
Jajodia, S. & Atluri, V. (1992), Alternative correctness criteria for concurrent execution of transactions in multilevel secure database systems, in ‘Proc. IEEE Symposium on Security and Privacy’, Oakland, CA, pp. 216–224.
Jajodia, S. & Kogan, B. (1990), Transaction Processing in multilevel secure databases using replicated architecture, in ‘Proc. IEEE Symp. on Research in Security and Privacy’, Oakland, CA, pp. 369–383.
Kang, I. E. & Keefe, T. F. (1995), ‘Transaction management for multilevel secure replicated databases’, Journal of Computer Security 3, 115–145.
Keefe, T. F. & Tsai, W. T. (1990), Multiversion concurrency control for multilevel secure database systems, in ‘Proc. IEEE Symp. on Research in Security and Privacy’, Oakland, California, pp. 369–383.
Lamport, L. (1977), ‘Concurrent reading and writing’, Comm. ACM 20 (11), 806–811.
McDermott, J. & Jajodia, S. (1993), Orange locking: Channel-free database concurrency control via locking, in B. Thuraisingham & C. Landwehr, eds, ‘Database Security, VI: Status and Prospects’, North-Holland, Amsterdam, pp. 267–284.
Reed, D. P. & Kanodia, R. K. (1979), ‘Synchronization with eventcounts and sequencers’, Comm. ACM 22 (5), 115–123.
Sankarachary, K. B. (1996), Concurrency control in multilevel secure database management system, based on serialization graph testing, Master’s thesis, Pennsylvania State University.
Schaefer, M. (1974), Quasi-synchronization of readers and writers in a secure multi-level environment, Technical Report TM-5407/003, System Development Corporation.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 1997 IFIP International Federation for Information Processing
About this chapter
Cite this chapter
Jajodia, S., Mancini, L.V., Ray, I. (1997). Secure Locking Protocols for Multilevel Database Management Systems. In: Samarati, P., Sandhu, R.S. (eds) Database Security. IFIP Advances in Information and Communication Technology. Springer, Boston, MA. https://doi.org/10.1007/978-0-387-35167-4_11
Download citation
DOI: https://doi.org/10.1007/978-0-387-35167-4_11
Publisher Name: Springer, Boston, MA
Print ISBN: 978-1-5041-2900-8
Online ISBN: 978-0-387-35167-4
eBook Packages: Springer Book Archive