Abstract
When addressing the problem of detecting malicious activities within network traffic, one of the main concerns is the reliability of the packet classification. Furthermore, a system able to detect the so-called zero-day attacks is desirable. Pattern recognition techniques have proven their generalization ability in detecting intrusions, and systems based on multiple classifiers can enforce the detection reliability by combining and correlating the results obtained by different classifiers.
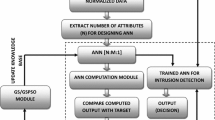
In this paper we present a system exploiting genetic algorithms for deploying both a misuse-based and an anomaly-based classifier. Hence, by suitably combining the results obtained by means of such techniques, we aim at attaining a highly reliable classification system, still with a significant degree of new attack prediction ability. In order to improve classification reliability, we introduce the concept of rejection: instead of emitting an unreliable verdict, an ambiguous packet can be logged for further analysis. Tests of the proposed system on a standard database for benchmarking intrusion detection systems are also reported.
This work has been partially supported by the Ministero dell’Istruzione, dell’Università e della Ricerca (MIUR) in the framework of the FIRB Project “Middleware for advanced services over large-scale, wired-wireless distributed systems (WEB-MINDS)”.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Vigna, G., Kemmerer, R.: Netstat: a network based intrusion detection system. Journal of Computer Security 7(1) (1999)
Axelsson, S.: Research in Intrusion Detection Systems: A Survey, TR 98-17, Chalmers University of Technology (1999)
Kumar, R., Spafford, E.H.: A Software Architecture to Support Misuse Intrusion Detection. In: Proceedings of the 18th National Information Security Conference, pp. 194–204 (1995)
Ghosh, A.K., Schwartzbard, A.: A Study in Using Neural Networks for Anomaly and Misuse Detection. In: Proc. 8’th USENIX Security Symposium, Washington DC, August 26-29 (1999)
Lane, T., Brodley, C.E.: Temporal Sequence learning and data reduction for anomaly detection. ACM Trans. on Inform. and System Security 2(3), 295–361 (1999)
Lee, W., Stolfo, S.J.: A framework for constructing features and models for intrusion detection systems. ACM Transactions on Inform. System Security 3(4), 227–261 (2000)
Esposito, M., Mazzariello, C., Oliviero, F., Romano, S.P., Sansone, C.: Real Time Detection of Novel Attacks by Means of Data Mining Techniques. In: Proceedings of the 7th International Conference on Enterprise Information Systems, Miami (USA), May 24-28 (2005) (in press)
Lee, S.C., Heinbuch, D.V.: Training a neural Network based intrusion detector to recognize novel attack. IEEE Trans. Syst, Man., and Cybernetic, Part-A 31, 294–299 (2001)
Fugate, M., Gattiker, J.R.: Computer Intrusion Detection with Classification and Anomaly Detection, using SVMs. International Journal of Pattern Recognition and artificial Intelligence 17(3), 441–458 (2003)
Giacinto, G., Roli, F., Didaci, L.: Fusion of multiple classifiers for intrusion detection in computer networks. Pattern Recognition Letters 24, 1795–1803 (2003)
Giacinto, G., Roli, F., Didaci, L.: A Modular Multiple Classifier System for the Detection of Intrusions. In: Windeatt, T., Roli, F. (eds.) MCS 2003. LNCS, vol. 2709, pp. 346–355. Springer, Heidelberg (2003)
Cordella, L.P., Limongiello, A., Sansone, C.: Network Intrusion Detection by a Multi Stage Classification System. In: Roli, F., Kittler, J., Windeatt, T. (eds.) MCS 2004. LNCS, vol. 3077, pp. 324–333. Springer, Heidelberg (2004)
Axelsson, S.: The Base-Rate Fallacy and the Difficulty of Intrusion Detection. ACM Trans. on Information and System Security 3(3), 186–205 (2000)
Cohen, W.W.: Fast effective rule induction. In: Proc. of the 12th International Machine Learning Conference. Morgan Kaufmann, San Francisco (1995)
McHugh, J.: Testing Intrusion Detection Systems: A Critique of the 1998 and 1999 DARPA Intrusion Detection System Evaluations as Performed by Lincoln Laboratory. ACM Transactions on Information and System Security 3(4), 262–294 (2000)
Liu, Y., Chen, K., Liao, X., Zhang, W.: A genetic clustering method for intrusion detection. Pattern Recognition 37 (2004)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2005 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Finizio, I., Mazzariello, C., Sansone, C. (2005). Combining Genetic-Based Misuse and Anomaly Detection for Reliably Detecting Intrusions in Computer Networks. In: Roli, F., Vitulano, S. (eds) Image Analysis and Processing – ICIAP 2005. ICIAP 2005. Lecture Notes in Computer Science, vol 3617. Springer, Berlin, Heidelberg. https://doi.org/10.1007/11553595_8
Download citation
DOI: https://doi.org/10.1007/11553595_8
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-28869-5
Online ISBN: 978-3-540-31866-8
eBook Packages: Computer ScienceComputer Science (R0)