Abstract
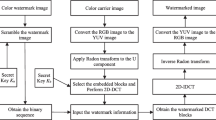
In this paper a new invisible watermarking algorithm using vector quantization (VQ) approach for image content authentication application is proposed. At the first stage, a robust verification watermark is embedded using properties of indices of vector quantized image using key based approach. At the second stage, the semi-fragile watermark is embedded by using modified index key based (MIKB) method. Robust watermark andVQenhance the security of the system by providing its double protection. The semi-fragile watermark is utilized for the authentication of the received image. Blind extraction of the watermark is performed independently in two successive steps i.e. in the order of embedding. Further, in oder to classify quantitatively an incidental or intentional attack, which at present is not being followed, a quantitative threshold approach using pixel neighborhood clustering is suggested. The existing methods employ the qualitative approach of identifying incidental or intentional attacks. Imperceptibility of watermarked image is 41 dB on the average, and it is also possible to detect and locate tamper with very high sensitivity. The present scheme is compared with the existing algorithms. The performance of proposed algorithm has been tested on various practical images. It outperforms in distinguishing malicious tampering from content preserving changes and the tampered regions are accurately localized.
Similar content being viewed by others
References
Ingemar J. Cox, Matt L. Miller, “Review of watermarking and the importance of perceptual modeling,” Proc. SPIE 3016, 92 (1997), DOI: 10.1117/12.274502.
Matt L. Miller, Ingemar J. Cox, Jean-Paul M. G. Linnartz, Ton Kalker, “A review of watermarking principles and practices,” in Digital Signal Processing for Multimedia Systems (CRC Press, 1999), pp. 461–485 [ed. by K. K. Parhi, T. Nishitami], ISBN: 0824719247.
Abdullah M. Iliyasu, Phuc Q. Le, Fandyan Dong, Kaoru Hirota, “Watermarking and authentication of quantum images based on restricted geometric transformations,” Information Sciences 186, No. 1, 126 (Mar. 2012), DOI: 10.1016/j.ins.2011.09.028.
Luis Rosales-Roldan, Manuel Cedillo-Hernandez, Mariko Nakano-Miyatake, Hector Perez-Meana, Brian Kurkoski, “Watermarking-based image authentication with recovery capability using halftoning technique,” Signal Processing: Image Communication 28, No. 1, 69 (Jan. 2013), DOI: 10.1016/j.image.2012.11.006.
Mohammed S. Khalil, Fajri Kurniawan, Muhammad Khurram Khan, Yasser M. Alginahi, “Two-layer fragile watermarking method secured with chaotic map for authentication of digital holy Quran,” The Scientific World Journal 2014, Article ID 803983 (2014), DOI: 10.1155/2014/803983.
Ming Li, Di Xiao, Yushu Zhang, “Attack and improvement of the fidelity preserved fragile watermarking of digital images,” Arabian Journal for Science and Engineering 41, No. 3, 941 (Mar. 2016), DOI: 10.1007/s13369-015-1941-1.
Chia-Chen Lin, Yuehong Huang, Wei-Liang Tai, “A novel hybrid image authentication scheme based on absolute moment block truncation coding,” Multimedia Tools and Applications, 21 (2015), DOI: 10.1007/s11042-015-3059-6.
Chuan Qin, Ping Ji, Jinwei Wang, Chin-Chen Chang, “Fragile image watermarking scheme based on VQ index sharing and self-embedding,” Multimedia Tools and Applications, 1 (2016), DOI: 10.1007/s11042-015-3218-9.
Z. M. Lu, S. H. Sun, “Digital image watermarking technique based on vector quantisation,” Electron. Lett. 36, No. 4, 303 (Feb. 2000), DOI: 10.1049/el:20000309.
P. S. L. M. Barreto, H. Y. Kim, V. Rijmen, “Toward secure public-key blockwise fragile authentication watermarking,” IEE Proc. Vision, Image and Signal Process. 149, No. 2, 57 (Apr. 2002), DOI: 10.1049/ ip-vis:20020168.
Zhe-Ming Lu, Dian-Guo Xu, Sheng-He Sun, “Multipurpose image watermarking algorithm based on multistage vector quantization,” IEEE Trans. Image Processing 14, No. 6, 822 (Jun. 2005), DOI: 10.1109/TIP.2005.847324.
Wei-Che Chen, Ming-Shi Wang, “A fuzzy c-means clustering-based fragile watermarking scheme for image authentication,” Expert Systems with Applications 36, No. 2, 1300 (Mar. 2009), DOI: 10.1016/j.eswa.2007.11.018.
K. Maeno, Qibin Sun, Shih-Fu Chang, M. Suto, “New semi-fragile image authentication watermarking techniques using random bias and nonuniform quantization,” IEEE Trans. Multimedia 8, No. 1, 32 (Feb. 2006), DOI: 10.1109/TMM.2005.861293.
Zhe-Ming Lu, Chun-He Liu, Dian-Guo Xu, Sheng-He Sun, “Semi-fragile image watermarking method based on index constrained vector quantization,” Electron. Lett. 39, No. 1, 35 (Jan. 2003), DOI: 10.1049/el:20030041.
Ching-Yung Lin, Shih-Fu Chang, “Semifragile watermarking for authenticating JPEG visual content,” Proc. SPIE 3971, 140 (2000), DOI: 10.1117/12.384968.
Hsien-Chu Wu, Chin-Chen Chang, “A novel digital image watermarking scheme based on the vector quantization technique,” Computers & Security 24, No. 6, 460 (Sept. 2005), DOI: 10.1016/j.cose.2005.05.001.
Jau-Ji Shen, Jia-Min Ren, “A robust associative watermarking technique based on vector quantization,” Digital Signal Processing 20, No. 5, 1408 (Sept. 2010), DOI: 10.1016/j.dsp.2009.10.015.
Chun-Wei Yang, Jau-Jhen Shen, “Recover the tampered based on VQ indexing,” Signal Processing 90, No. 1, 331 (Jan. 2010), DOI: 10.1016/j.sigpro.2009.07.007.
Jun-Chou Chuang, Yu-Chen Hu, “An adaptive image authentication scheme for vector quantization compressed image,” Journal of Visual Communication and Image Representation 22, No. 5, 440 (Jul. 2011), DOI: 10.1016/j.jvcir.2011.03.011.
Y. Linde, A. Buzo, R. Gray, “An algorithm for vector quantizer design,” IEEE Trans. Commun. 28, No. 1, 84 (Jan. 1980), DOI: 10.1109/TCOM.1980.1094577.
Jeng-Shyang Pan, Hsiang-Cheh Huang, Feng-Hsing Wang, “A VQ-based robust multi-watermarking algorithm,” Proc. of TENCON, 28–31 Oct. 2002 (IEEE, 2002), pp. 1719–1726, DOI: 10.1109/TENCON.2002.1181228.
Author information
Authors and Affiliations
Corresponding author
Additional information
Russian Text © A. Tiwari, M. Sharma, 2017, published in Izvestiya Vysshikh Uchebnykh Zavedenii, Radioelektronika, 2017, Vol. 60, No. 4, pp. 206–221.
ORCID: 0000-0002-5921-0956
About this article
Cite this article
Tiwari, A., Sharma, M. Novel watermarking scheme for image authentication using vector quantization approach. Radioelectron.Commun.Syst. 60, 161–172 (2017). https://doi.org/10.3103/S0735272717040021
Revised:
Published:
Issue Date:
DOI: https://doi.org/10.3103/S0735272717040021