Abstract
The MAC (medium access control) of CSMA (carrier sense multiple access) is widely used in distributed wireless networks with random node locations. In CSMA MAC, two nodes that are within the range of one another cannot transmit packets simultaneously. Modeling the concurrently transmitting nodes is crucial for the performance analysis of the CSMA networks. In this paper, we study the density of concurrently transmitting nodes and propose another modification of classical hard core point process to accurately estimate the density of concurrently transmitting nodes, in the absence and in the presence of fading conditions. The MMHCP model we propose outperforms the popular Matérn type II model and the existing modified hard core point (MHCP) process model by avoiding the underestimation and alleviating the overestimation issues, respectively. We conduct extensive numerical analysis and simulations to evaluate the accuracy of our MMHCP model. Furthermore, we study the impact of the density of initial Poisson Point Process (PPP) and fading factor on the mean probability of successful reception and on the transmission capacity of networks from numerical analysis and simulations.
Similar content being viewed by others
1 Introduction
In distributed wireless networks with random node locations, such as ad-hoc networks or sensor networks, cognitive femtocell networks, a decentralized medium access control (MAC) protocol is required to control the access of the network nodes to the shared wireless spectrum in order to limit the mutual interference. With the low cost of the wireless network technologies, the nodes deployed in wireless networks are becoming denser and denser. For example, the last few years have witnessed the proliferation of WiFi Access Points (APs) in many urban areas, and it is very common that several APs are in the communication range of each other. In other examples such as in the hot-spot networks [1] or cyber-physical systems [2], with a growing number of sensors being deployed, more and more data will be transmitted over wireless links.
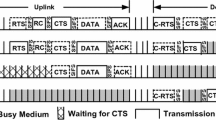
For this type of networks, carrier-sense multiple access (CSMA) protocols are very popular to avoid collisions and improve the network performance. CSMA distinguishes itself with its distributed nature in coordinating the spectrum access. Under CSMA/CA (Carrier sense multiple access with collision avoidance), a transmitter continuously senses the channel state prior to transmitting. If the channel state is idle, the transmitter starts to transmit packets. Otherwise, it waits for a while before it starts sensing the status. By this way, the network can reduce the interference to achieve a higher probability of successful transmissions and higher network capacity.
In the studies of CSMA protocol, there are several problems that must be considered, such as hidden terminals [3], starvation, or fairness in heavily loaded networks [4, 5]. Many work focus on designing a better MAC protocol to overcome some flaws or improve some performance, for example [4,5,6,7]. In light of modeling the CSMA networks, traditional method typically rely on Markovian approaches. However, Markovian models fail to represent physical layer effect, such as the impact of fading and cumulative interference. In this paper of our work, we focus on modeling the concurrently transmitting nodes under CSMA protocol and analyzing interference via stochastic geometry. The modeling and analysis on the concurrently transmitting nodes can be used in many distributed wireless networks with CSMA protocol to evaluate the interference and the relevant network performance.
The introduction of stochastic geometry to analyze the network performance from a statistical perspective has been more than three decades [8]. In stochastic geometry, the Poisson Point Process (PPP) is widely used in modeling the topology of networks, such as cellular networks in [8,9,10] and ad-hoc networks in [11], for its tractability in analyzing the network performance. However, the PPP is accurate for very sparse networks as the distribution of the atoms of a PPP is independent, which is not always the exact case in wireless networks. For example, in heterogeneous cellular networks, the locations of base stations are modeled by Poisson Cluster Process (PCP) in [12] or by Ginibre Point Process (GPP) in [13], in order to reflect the dependence of the locations of the base stations. Similarly, due to the exclusion of CSMA nodes, the hard core point process (HCPP), instead of PPP, is usually applied to model the simultaneously transmitting nodes.
Among the hard core point processes, Matérn type II model is most widely used in modeling CSMA networks. Although Matérn type I model can get a legitimate HCPP, it is proved that this model only accounts for retaining the isolated points (i.e., points which are at least fixed distance away from every other point in the process). While Matérn type II model captures the contention among the initial points to be retained in the HCPP. Furthermore, the author in [14] proved that Matérn type II model can be approximated by a non-homogeneous PPP. Many work such as [15,16,17,18,19] modeled the CSMA networks by Matérn type II model.
The Matérn type II model can be obtained by thinning a PPP as follows. Let Φ = {x i }i ∈ (1, n) be a homogeneous PPP. Each point x i is marked by a random variable m i that is uniformly distributed between [0,1]. The marks are independent and identically distributed, or i.i.d, and independent of the positions of x i . If the ball that centers at x i with radius h does not consist of any points with mark less than m i , the point x i is retained in the hard core point process. The points that are not retained will be deleted from the PPP in the end. Since whether a point is retained or not is determined by points around it, the thinning process is not independent.
As stated in many literatures such as [15, 17, 20, 21], Matérn type II model tends to lead an underestimation of the transmitting nodes’ density. As shown in Fig. 1, node x1 is not retained as it detects its neighbor x2; moreover, node x2 is not retained either, as it detects its neighbor x3, i.e., m1 > m2 > m3, where m i is the mark of x i . As a result, neither x1 nor x2 can be retained in the thinning scheme. However, if x3 is not the neighbor of x1, and if x3 does not detect any on-going transmissions of its neighbors, a more reasonable MAC will allow x1 and x3 to transmit simultaneously.
That is mainly because the freezing property of the backoff timer in the CSMA protocol is not captured to calculate the density of the simultaneously active transmitters in the Matérn type II model. In a CSMA network, a transmitter still can access the channel if it does not have the lowest backoff time in its contention domain given that all of the transmitters with lower backoff time have frozen their timers. A model named Matérn type III is defined as completely capturing the freezing property, while it involves a chain of correlations among the initial points (potential transmitters). The chain terminates when it reaches a point (transmitter) which is definitely retained or not. Therefore, Matérn did not discuss such a model more and regarded it “rather formidable” [20].
In [20, 21], the authors investigated the problem of underestimation of the Matérn type II model and proposed a second-order density estimation model, named MHCP, that partially takes the backoff timer freezing property into consideration and reduces the underestimation of density due to Matérn type II modeling. This model is called to “go one step in the correlation chain” and gives corresponding expression on the density, outage probability, and transmission capacity in [20]. However, their model tends to overestimate the transmitting node density in dense CSMA networks, especially in fading environment.
In this paper, we propose a new idea on the correlation chain and restrain that any nodes in the network have a same retaining probability in statistical meaning, or take the mean probability of retaining a node in the network to make the density analysis tractable, which is proved that our model can also avoid the transmitting density underestimation of Matérn type II model and alleviate the overestimation of MHCP in [20, 21]. The constraints make the model still applicable in the distributed wireless network, such as in bipolar model of MANET [17], wireless sensor networks [22,23,24], or one tier of multi-tier heterogeneous networks [10] where the nodes in the same tier have same properties.
The multi-fold contributions can be summarized as follows.
-
(i).
We analyze the Matérn type II model and the MHCP model to demonstrate that the Matérn type II model underestimates while the MHCP tends to overestimate the density in dense networks and fading environment.
-
(ii).
We propose another modification of Matérn type II model based on MHCP to estimate the retaining probability for a node in the initial PPP and then the transmitting density for the CSMA networks.
-
(iii).
We get the density expression for the simultaneously transmitting nodes in dense CSMA networks given that nodes being retained by a same probability in statistical meaning. This is another partial solution for the “correlation chain” of Matérn type III model, other than [20, 21]. Furthermore, we generalize the model in Rayleigh fading.
-
(iv).
We analyze the mean probability of successful reception and transmission capacity in CSMA networks based on the proposed model and reveal the mean probability of successful reception being almost immune to the fading and the initial intensity, while the transmission capacity of the network tends to be closer to our proposed model with the increased fading factor.
The rest of our paper is organized as follows. Section 2 reviews the related work. In Section 3, we give the network model, assumptions, and the methodology of analyzing models. Section 4 gives the retaining probability and network transmitting density of the proposed model in the deterministic fading, and Section 5 generalizes the model under Rayleigh fading. The network performance including the successful reception probability and transmission capacity is given in Section 6. Section 7 demonstrates the numerical and simulation results, and the last section concludes this paper. A list of the key mathematical notations used in this paper is given in Table 1.
2 Related work
There are many work on the interference management and performance analysis using stochastic geometry, mainly for the PPP model, such as [9,10,11]. For the added complexity, there are not so many results on the HCPP modeling and analysis. In this section, we review the work closely related to the HCPP and our work.
The author in [14] proved that there is no known expression for the probability generating functional for the HCPP, and it is extremely difficult to find the exact distribution of the aggregate interference. The author compared the Matérn type I and Matérn type II model and proved that the Matérn type II model can be safely approximated by an inhomogeneous PPP model for interference-based performance analysis.
In [16], the authors used the Matérn type II to model the spatial distribution of access points (APs) in a dense IEEE 802.11 network, and the users were modeled as a PPP. A modified version of the HCPP, namely, the modified Matérn CSMA process was introduced. Their model captured the fact that CSMA/CA will grant a transmission opportunity to a given AP if this AP has the minimal backoff time among all APs in its contention domain and the fact that an AP will refrain transmitting if another AP already transmits in its contention domain. In [15], the authors extended the model presented in [16] and obtained the distribution of the throughput (rather than just the spatial average) achieved by the nodes, where the retaining probability was defined in terms of channel gains rather than distances. In [17], the authors formulated the Matérn point process for networks using CSMA and derived the probability of joint medium access and the coverage. In [19], the Matérn hard core point process was used to model the CSMA protocol in order to study the maximum throughput that could be obtained in multi-hop MANETs. Recently, the authors in [25] used the Matérn hard core point process to analyze the performance of a cloud radio access network (CRAN) to get a more realistic result. However, the contention resolution process presented by above literatures all follows the Matérn type II model. Some of them mentioned the underestimation of density for the active nodes [15,16,17], but no essential improvement of the underestimation is mentioned.
Simple Sequential Inhabitation (SSI) is an alternative to model the dense CSMA networks. It is derived from the packing and space-filling problems. The authors in [26, 27] used SSI to model the spatial distribution of potential interference sources. However, analyzing the model turned out to be very challenging as SSI gives the point density only when the underlying PPP density tends to be infinity and cannot derive an analytical expression.
To overcome the underestimation for density of Matérn type II model, the authors in [20, 21] proposed a modified hard core point (MHCP) process. In MHCP, a node x i has the privilege to transmit in a time slot for the following two reasons. First, node x i has the lowest mark in its contention domain, which is as same as that in the Matérn type II model. Second, node x i has the second lowest mark in its contention domain, and node x j has the lowest mark while x j is not the node with the lowest mark in contention domain of itself. Such a scheme is called “go one step in correlation chain” [20], which actually can avoid omitting some nodes. With channel conditions deteriorate, especially in a network with dense nodes, the MHCP model tends to overestimate the transmitting density of the network [20], as shown in Fig. 2. The nodes x3 and x4 are retained for they have the lowest mark in their contention domains, and nodes x1, x2, x5, and x6 are retained for they have the second lowest mark in their contention domains, while the corresponding nodes with the lowest mark (x2, x5, x6, x7) are not the one with the lowest mark in the contention domain of themselves. But a reasonable scheme would retain x3, x4, x1, and x5 or x3, x4, x2, and x6. That is because when they considered the nodes with second lowest mark, the nodes with the lowest mark may be retained for the same reason, resulting in two nodes being retained at the same time in one domain.
Density overestimation in MHCP model. Nodes around red circle would be retained. The nodes x3 and x4 are retained for they have the lowest mark in their contention domain, and nodes x1, x2, and x5, x6 are retained for they have the second lowest mark in their contention domains, while the corresponding nodes with the lowest mark (x2, x5, x6, x7) are not the one with the lowest mark in their contention domains. A reasonable scheme would retain x3, x4, x1, and x5 or x3, x4, x2, and x6
In this paper, we consider the problem of underestimation and overestimation from a new perspective. That is, in the initial PPP, a node x i is retained under the following conditions: (1) x i has the lowest mark in its contention domain; (2) x i has the second lowest mark in its contention domain; and meanwhile, node x j has the lowest mark in the contention domain of x i , and x j is not retained. We name our proposed model as modification of MHCP (MMHCP). The idea seems like the correlation chain in Matérn type III at first sight. Then, we analyze it by adding the constraint that nodes in a network have a same retaining probability in statistical meaning.
3 Network model, method, and notations
3.1 Network model
We use a marked Poisson point process \( \overset{\sim }{\Phi}=\left\{\left({x}_i,{m}_i\right)\right\} \) to indicate the potential transmitters contending to access the spectrum, where {x i } is a homogeneous PPP over the plane with density λ p , denoting the locations of the potential transmitters. The {m i } denotes the backoff time of a node, that is uniformly distributed in the range [0,1], similar as in [15, 17, 20, 21]. Although the backoff time is usually not uniformly distributed between [0,1] in the actual protocol (binary exponential backoff, for example), it is proved in [28] that assuming a uniform distribution for the time marks does not affect the generality of the model. The power emitted from x i (provided it is authorized by the MAC mechanism) towards x j is denoted by \( {F}_i^j={P}_t.{g}_i^j \), where P t is the transmitting power and \( {g}_i^j \) is the fading channel gain of the link between node x i and node x j .
Assume the transmitting power being same, the value of \( {F}_i^j \) is same for all nodes if we consider the fixed fading or no fading. In this paper, we also consider the fading environment, named Rayleigh fading, of which the fading channel gain is subject to an exponential distribution with parameter μ, μ > 0. Generally, due to the characteristic of Rayleigh fading, \( {g}_i^j \)is independent for different links.
The neighborhood of a node is defined as \( N\left({x}_i\right)=\left\{j\mid \left({x}_i,{m}_i\right)\in \overset{\sim }{\Phi}:{F}_i^j/l\right(\left|{x}_i-{x}_j|\right)\ge {P}_0\Big\} \), where P0>0 is the sensing threshold of the network and l(.) is the path loss function, which is usually taken as l(r) = rβ, β > 2, where r is the distance between a transmitter and its receiver. For simplicity, we denote the contention domain of node x i as C i . It is easy to see that if we consider the fixed fading, the same transmitting power and the same sensing threshold for each node, the contention domain is actually a disk with a certain radius r e . On the other hand, in a fading environment, the contention domain is not a regular shape due to the random channel gain, as stated in [20].
We assume that the receivers are randomly distributed over the plane with another PPP, which is irrelevant to the transmitters. The number of receivers is enough to guarantee each active transmitter has one receiver at least in a time slot. A receiver associates with the transmitter that provides the strongest average received power conditioned that the receiver can be sensed by the transmitter. This means that each active transmitter associates with the nearest receiver. Once an association is fixed, other active transmitters are treated as interference. Figure 3 illustrates an example of the model, where the potential transmitters are denoted by red stars, the transmitting nodes and the receivers are denoted by blue circles and blue triangles respectively. The intended links are denoted by solid arrows, and some interference links of a receiver are denoted by dot lines.
Model of transmitters, receivers and corresponding links. The red stars are the potential transmitters distributed as a PPP, the blue circles are the concurrently transmitting nodes by CSMA protocol, and the blue triangles are the receivers distributed as another PPP. Solid arrows are the intended links, and dotted lines denote some of the interference links
As previous work, in recent research of wireless network such as [29,30,31], the signal to interference plus noise ratio (SINR) is taken as a metric of successful transmission for an intended link. In dense networks of this paper, the influence of noise can be neglected, namely, interference-limited network. The probability of successful reception can be expressed as ps = Pro[SIR > T], where SIR is the ratio of intended signal to the aggregate interference, and T is the threshold that the receiving node can successfully decode.
3.2 Method
In this paper, we firstly focus on the model of the transmission without fading. Under such a case, there is only one source of randomness due to the spatial distribution of the nodes. It is easy to analyze the retaining probability of a node from the potential transmitters, since the distance threshold for a node sensing other transmitters is fixed, as r e = (P t . g/P0)1/β (in Matérn type hard core point process, the exclusion radius is given as a fixed value). The contention domain, or the neighborhood of a node, can be regarded as a disk with fixed radius as r e . Meanwhile, the area of the domain sensed by two nodes simultaneously, and the area of the domain sensed by node x i and not sensed by another node x j (when x i has the second lowest mark, and x j has the lowest mark in the contention domain of x i ) can be derived based on the probability and statistics information. We can calculate the average number of nodes in above domains, respectively. The transmitting density and the aggregate interference can be derived accordingly, as [21].
However, when the model is applied to fading scenarios, another randomness due to the random channel gains is added in the network model. In such a case, the receiving power is not determined, even both the transmitting power and the link distance are fixed. Accordingly, the distance threshold for a node sensing another node is random. Neither the contention domain of one node, nor the domain sensed by two nodes simultaneously, is not a region with a fixed area or fixed shape. Fortunately, the randomness stems from the fading, so we can catch it from the fading factors. Knowing the fading factor, the average number of nodes sensed by a node x i , or the average number of nodes sensed by two nodes x i , x j simultaneously (when x i has the second lowest mark, and x j has the lowest mark in the contention domain of x i ) can be expressed with the instantaneous distance threshold r e . Therefore, the result on the retaining probability, transmitting density, and related metric in the model without fading can be extended to the model with fading condition. The difference from the model without fading is that the distance threshold r e is random following with the fading factor at different directions, and at any time slot. In [20], the authors utilized a circular bounding box around the irregular contention domain to make the analysis tractable and derived a lower bound to the number of transmitters in the neighborhood of a node. Different from the bounding approach, our method considers the average number of the transmitters in the contention domain of a node following with the random variable(r e and μ) and derive the mean retaining probability and the transmitting density, which is consistent with the constraint added in our model. Such analysis is applicable to the overall performance of the network.
3.3 Notations
For the sake of argument, we specify some of the key mathematical notations listed in Table 1. Node x i is abbreviated as i, and i, j, and k are used to denote different nodes. We use C i to denote both the nodes set in the contention domain of node i and the contention domain itself. The following probabilities are essential to determine whether a node is privileged to transmit.
Probability of a node i being retained is denoted by Pretain[i] = Pro[i is retained].
Probability of a node i having the lowest mark in C i is denoted by P1[i] = Pmin[i].
Probability of a node i having the second lowest mark in C i is denoted by P2[i].
Probability of a node i with the second lowest mark in C i being retained is denoted by P2_retain[i].
Probability of a node j having the lowest mark in C i and not being retained, conditioned on that node i has the second lowest mark, is denoted by \( {\overline{P}}_i\left[j\right] \).
Suppose there are n nodes coexisting with node x i in its contention domain. Due to the uniform distribution of the marks among the n + 1 points in C i , and the marks are irrelevant to the points, the probability that x i has a certain mark (among the n + 1 marks) equals to 1/(n + 1). At the same time, since we adopt a homogeneous PPP, the average number of points in C i is λ p S Ci , where S Ci is the area of C i . With the fixed fading, S Ci can be the area of a disc with radius r e . Hence, the probability P1[i] and P2[i] can be derived as follows.
where |.| denotes the size of a set. If we let N = λ p πr e 2, the above probability can be written as \( \frac{1-{e}^{-N}}{N} \).
Suppose x i has the second lowest mark in C i , and x j has the lowest mark, while there is at least one node x k in C j with a lower mark than m j . It is equivlant to say that there is at least one node with lower mark than m j in C j −C i (shadow of Fig. 4). The probability is \( \mathrm{Pro}\left[\exists k\in \left({C}_j-{C}_i\right),{m}_k<{m}_j\right]=\sum \limits_{t=1}^{\infty}\frac{t}{n+t+1}\frac{M^t{e}^{-M}}{t!} \), where M is the average number of the C j − C i . The derivations can be found in [21]. We use \( {P}_{C_j-{C}_i}\left[k\right] \) to indicate this similar scenario in the rest of the paper. Therefore, the probability of a node being retained on that having the second lowest mark is
Correlation chain of retaining probability. Assume m i > m j , node i is retained, if m j is the only mark lower than m i in C i and j is not retained. The reason for j not being retained (j has the second lowest mark) is that k is retained, if m k is the only mark lower than mj in C j . The solution is transformed to the retaining probability of node k
Here, M is the average number of nodes in C j − C i . When we consider the fixed fading or no fading conditions, the deduction of M can be found in [21]: \( M={\lambda}_p{\int}_0^r\left(2\pi z-4z{\cos}^{-1}\left(\frac{z}{2r}\right)+\frac{z}{r^2}\sqrt{4{r}^2-{z}^2}\right) dz \).
The above expression can be manipulated in a closed form. We can further plug it into (2) to get the probability of a node with the second lowest mark being retained in MHCP. The whole retaining probability for a node is PMHCP = Pmin + P2_retain.
4 Base analysis of MMHCP
Combining the analysis of Matérn type II model and the MHCP model, we propose the MMHCP model to estimate the retaining probability of initial deployed nodes. In this section, we firstly focus on the condition that fading is uniform, or fixed fading. In MMHCP model, we consider the simultaneously transmitting nodes (retained nodes) under CSMA protocol include those nodes with the lowest mark and the nodes that have the second lowest mark in the domain of itself while the node with the lowest mark has not been retained. It can be formally expressed as follows: \( {\overset{\sim }{\Phi}}_{\mathrm{t}}=\left\{{x}_i:\forall {x}_j\in N\left({x}_i\right),{x}_i\ne {x}_j,{m}_i<{m}_j\right\}\cup \left\{{x}_i:\exists {x}_j\in N\left({x}_i\right),{m}_i>{m}_j,\forall {x}_k\in N\left({x}_i\right)\backslash \left\{{x}_i,{x}_j\right\},{m}_k>{m}_i,{x}_j\ \mathrm{is}\ \mathrm{not}\ \mathrm{retained}\right\} \). The probability of a node been granted to transmit is \( {P}_{\mathrm{retain}}\left[i\right]={P}_1\left[i\right]+{P}_2\left[i\right]\times {\overline{P}}_i\left[j\right] \), where \( {\overline{P}}_i\left[j\right] \) is the probability of node j having the lowest mark in C i and not being retained.
The difference between MMHCP and MHCP is the retaining probability of the node with the second lowest mark in its contention domain. In MHCP, if a node x i has the second lowest mark in C i , it is retained only if the node with the lowest mark x j is not the one with the lowest mark in C j . In MMHCP, a node x i with the second lowest mark in C i is retained because node x j with the lowest mark is not retained. Even if node j does not have the lowest mark in C j , it may be retained for the same reason as node i. When this occurs, node i should not be retained. However, in MHCP model, node i will be retained in the same case, which leads to the overestimation of the number of retained nodes.
For \( {\overline{P}}_i\left[j\right] \), it can be interpreted as the condition that node i has the second lowest mark in C i , while node j has the lowest mark in C i and is not retained. In other words, node i has the second lowest mark in C i , and node j is not retained only because there is at least a node k in C j −C i (shadow of Fig. 4) and k is retained (node k may have the lowest mark, or k has the second lowest mark while the node with the lowest mark in C k is not retained). The authors in [21] considered the reason for j not being retained is that there exist nodes in shadow of Fig. 4. However, even there exist nodes in shadow, j may be retained. Namely, when m j is the second lowest and the k with the lowest mark is not retained, j is retained, which makes i not to be retained.
We further modify the probability in [21] as follows. Suppose there are n nodes and node i coexisting in C i , and t nodes in the shadow, where both n and t follow Poisson distribution with parameter N and M, respectively. Firstly, we analyze the probability of j not being retained given that j has the second lowest mark in C i . Following the analysis above, we know j is not retained for the following reasons: m j is not the lowest mark of a node in C j , except the case that although m j is not the lowest mark of a node in C j , m j is the second lowest while the lowest mark of node k is not retained. Because in such a case, j should be retained, too. According to [21], we know that the probability of j not having the lowest mark in C j equals to P2_retain[i] in (2). We consider the probability of m j being the second lowest mark of a node in C j under the condition that m j being the lowest mark of a node in C i . It equals to the probability of j having the second lowest mark in (n + t + 1) nodes: \( P\left({x}_j\ \mathrm{has}\ \mathrm{second}\ \mathrm{lowest}\ \mathrm{mark}\ \mathrm{in}\ {C}_j|{x}_j\ \mathrm{has}\ \mathrm{the}\ \mathrm{lowest}\ \mathrm{mark}\ \mathrm{in}\ {C}_i\right)\triangleq {P}_2^{\prime}\left[j\right]=\frac{1}{n+t+1} \).
Hence, the probability of i being retained is \( {P}_{\mathrm{retain}}\left[i\right]={P}_1\left[i\right]+{P}_2\left[i\right]\times {\overline{P}}_i\left[j\right]={P}_1\left[i\right]+{P}_2\left[i\right]\times \left({P}_{\left({\mathrm{C}}_i-{\mathrm{C}}_j\right)}\left[{m}_j\ \mathrm{is}\ \mathrm{not}\ \mathrm{lowest}\right]-{P}_2^{\prime}\left[j\right]\times \left(1-{P}_{\mathrm{retain}}\left[k\right]\right)\right)={P}_1\left[i\right]+{P}_{2\_\mathrm{retain}}\left[i\right]-{P}_2\left[i\right]\times {P}_2^{\prime}\left[j\right]\times \left(1-{P}_{\mathrm{retain}}\left[k\right]\right) \). Pretain[k] is the probability of node k being retained and can be obtained in the same way as Pretain[i]. In a dense node distributed network, the rule is iterated until the current node is definitely to be retained or not. However, for the random distribution of the nodes in a network, we cannot know the exact number of the nodes in such an iteration chain beforehand. Thus, the ultimate result is hard to obtain.
To simplify such a problem, we assume the probability of each node being retained is uniform in a statistical meaning. By this way, we can get an average probability of retaining a node. This constraint makes the model tractable and still applicable in ad-hoc networks, wireless sensor networks, and one tier of multi-tier heterogeneous wireless networks. Therefore, let Pretain[i] = Pretain[j] = Pretain[k] = …, and the problem is simplified as Pretain[i] = Pmin[i] + P2_retain[i] − P2[i] × P2′[j] × (1 − Pretain[i]). We get
Here, P2_retain[i] is given in Eq. (2); we denote \( {P}^{\prime }={P}_2\left[i\right]\times {P}_2^{\prime}\left[j\right] \). Since n and t are distributed as Poisson with parameters N and M, we get
According to the deduction of P2_retain[i] from [21], we can obtain \( {P}^{\prime }=\frac{M{e}^{-\left(N+M\right)}}{N}\left(\sum \limits_{n=1}^{\infty}\frac{N^{n+1}}{\left(n+1\right)!}\sum \limits_{t=1}^{\infty}\frac{M^{t-1}}{t!}\frac{1}{n+t+1}\right)=\frac{1}{M}\left({P}_{2\_\mathrm{retain}}\left[i\right]-\frac{M{e}^{-\left(N+M\right)}}{N}.\frac{e^N-1}{N}\right) \). Finally, we get
where P min [i] and P2_retain[i] are given by (1) and (2) and P′ can be obtained by
Proposition 1 If the probability of a node being retained in MMHCP is denoted by P MMHCP = P retain [i] as (3), the probability of a node being retained in MHCP of [21] is \( {P}_{MHCP}={P}_{min}\left[i\right]+{P}_2\left[i\right]\times {P}_{C_j-{C}_i}\left[k\right] \), and the probability of a node being retained in Matérn type II model is \( {P}_{Matern} \), then we get \( {P}_{Matern}\le {P}_{MMHCP}\le {P}_{MHCP}\le 1 \).
Proof The last “≤”: The retaining probability is obviously less than 1 in a network, and ‘=‘holds only when the network is sparse enough. Then, let us prove that \( {P}_{Matern}\le {P}_{\mathrm{MMHCP}} \), namely \( \frac{P_{\mathrm{min}}\left[i\right]+{P}_{2\_\mathrm{retain}}\left[i\right]-{P}^{\prime }}{1-{P}^{\prime }}\ge {P}_{\mathrm{min}}\left[i\right] \). We need that Pmin[i] + P2_retain[i] − P′ ≥ Pmin[i] − Pmin[i]P′ holds. Since P′ reflects the probability of j having the second lowest mark in shadow while P2_retain[i] reflects the probability of node j having not the lowest mark among more than 2 nodes, P2_retain[i] ≥ P′.
Then, we prove PMMHCP ≤ PMHCP, namely \( \frac{P_{\mathrm{min}}\left[i\right]+{P}_{2\_\mathrm{retain}}\left[i\right]-{P}^{\prime }}{1-{P}^{\prime }}\le {P}_{\mathrm{min}}\left[i\right]+{P}_{2\_\mathrm{retain}}\left[i\right] \). Since Pmin[i] + P2_retain[i] is the probability of a node been retained and is less than 1, then let a = Pmin[i] + P2_retain[i], b = P′; we know \( \frac{a-b}{1-b}<a \) because both a and b are less than 1. This completes the proof.
We can conclude that the probability of a node being retained in MMHCP is lower than that in MHCP, and higher than that in Matérn type II model. The underlying reasons are as follows. Matérn type II model does not retain any nodes other than the nodes with the lowest mark in the contention domain. The MHCP model retains the node with second lowest mark only because the neighbor with the lowest mark of such a node has a neighbor with a lower mark. While in MMHCP model, when we consider a node with the second lowest mark being retained or not, we check whether any neighbor of the lowest mark neighbor is retained. Hence, the MMHCP model can alleviate the overestimation in MHCP. Knowing the probability of being retained, the density of simultaneously transmitting nodes in CSMA networks can be represented as λ csma = λ p . Pretain[i]. Such a density is affected both by the initial nodes density λ p and the exclusion r e when we consider the fixed fading, illustrated in Figs. 5 and 9, respectively. The retaining probability in the fading condition is given in the following section.
5 General analysis on retaining probability with Rayleigh fading
In this section, we analyze the retaining probability of a node under fading conditions. In real radio propagation, fading is usually variable for each transmission. Therefore, the contention domain is not always a disk with fixed exclusion radius, but is an area with irregular shape in different time slots, as stated in [20]. In this section, we focus on the channel fading follows the Rayleigh fading, in which the fading factor is exponentially distributed with parameter μ and the mean 1/μ.
Similar to the previous analysis, we use \( N\left({x}_i\right)=\left\{j|\frac{P_t{g}_i^j}{l\left({x}_i-{x}_j\right)}\ge {P}_0,j\ne i\right\} \) to denote the neighbor set of i. Here, \( {g}_i^j \) is the fading factor from node i to node j. In Matérn type II model, the average number of neighbor nodes for node i is denoted by \( \overset{\sim }{N}={\mathrm{E}}^0\left[\sum 1\left(\frac{P_t{g}_i^j}{l\left({x}_i-{x}_j\right)}\ge {P}_0\right)\right]={\lambda}_p{\int}_{R^2} Pro\left[\ {g}_i^j\ge \frac{P_0}{P_t}l\left({x}_i-{x}_j\right)\right] dx=2\uppi {\lambda}_p{\int}_0^{\infty}\left(1-G\left(\frac{P_0}{P_t}l(r)\right)\right) rdr \) . With the Rayleigh fading, we get \( \overset{\sim }{N}=\frac{2\pi {\lambda}_p\Gamma \left(2/\beta \right)}{\beta {\left({\mathrm{P}}_0.\mu /{P}_t\right)}^{2/\beta }} \) .
To get the retaining probability of a node, we need to know the mean number of the nodes in the portion similar to the shadow of Fig. 4 under fading conditions. These nodes can be sensed by node j and cannot be sensed by node i, on condition that node j can be sensed by node i and m j < m i . We use \( \overset{\sim }{M} \) to denote the mean number of those nodes. It is easy to see that \( \overset{\sim }{M} \) equals the number of nodes sensed by node j subtracts the number of nodes that can be sensed both by i and j simultaneously, which is denoted by \( \overset{\sim }{P} \). We have \( \overset{\sim }{M}=\overset{\sim }{N}-\overset{\sim }{P} \). Plugging \( \overset{\sim }{M} \) and \( \overset{\sim }{N} \) into (3), we can get the retaining probability for a node under fading condition.
The rest thing is to compute \( \overset{\sim }{P} \).
Assume the distance between node i and its receiving node is r, and the distance between i and j is x. Then, the distance between j and the receiving node is \( y=\sqrt{r^2+{x}^2-2 rxcos\theta} \), where θ is the angle between the line from i to its receiving node and the line from node i to node j. Following the definition of \( \overset{\sim }{P} \), we know
Since θ is the interior angle of a triangle, and g is the fading variable with g~exp.(μ), we compute the value of \( \overset{\sim }{P} \) on θ and g:
It is noted that in the presence of fading, the retaining probability of a node decreases with the increasing density of initial PPP, which is as same as that in the absence of fading. However, for the density of concurrently transmitting nodes, namely the transmitting density in a time slot, it tends to be stable much faster than that under no fading or fixed fading condition, especially when the density of initial PPP increases, as shown in Figs. 7 and 8 of Section 7.1.
6 Mean probability of successful reception and transmission capacity
In wireless networks, the probability of successful reception for a node is an important metric used to guide the configuration of network parameters. The transmission is mainly affected by the aggregate interference that is the accumulated signals sent by concurrent transmitters at the same time. Based on the analysis in [14] that the Matérn type II model can be safely approximated by an inhomogeneous PPP to model for interference-based performance analysis, many literatures analyzed the probability of successful reception based on the link distance, such as [15, 17]. Authors in [21] statistically modeled the aggregate interference based on the MHCP transmitting density using a homogeneous PPP. According to the shot noise theory in [32, 33], the Laplace transform of the pdf (probability density function) of the aggregate interference, the mean and variance can be expressed in closed form. The authors in [34] characterized the interference distribution in Poisson networks, both in the absence and in the presence of fading. In [35], the CSMA protocol was modeled by excluding interference from a guard zone around the typical receiver in a Poisson model. The authors in [36] provided a Taylor-series type expansion of functions to approximate the interference and illustrated that the approach could be used to find outage probability in both Poisson and non-Poisson wireless networks.
In this section, we also assume that the interference is produced only by transmitters located outside a distance equal to the sensing range in CSMA networks, as in [34]. Different from [15, 17], in this paper, we consider the mean probability of successful reception over the distance r of a link. We assume the successful reception is only related to the receiving node, or the transmitting is successful if the node is granted to transmit. Following the well-known Slivnyak theorem in [17, 37], we assume the typical receiver at origin, which experiences the same interference as any other coexisting receivers.
In the absence of fading, the probability of successful reception is easy and is determined only by the link distance r. Under fading condition, we have the following result.
Theorem 1 Assume the retaining probability of a node from initial PPP is P retain , with the fixed transmitting power, and fading distribution is exponential with parameter μ, the mean probability of successful reception in a CSMA network can be approximated as:
where \( {f}_{r_e}\left({r}_e\right)={P}_0{\mu}^2\beta {r_e}^{\beta -1}\mathit{\exp}\left(-{P}_0\mu {r_e}^{\beta}\right) \), and \( {f}_r(r)=\left\{\begin{array}{c}2\pi {\lambda}_pr{P}_{retain}\kern1em 2r\le {r}_e\\ {}2\pi {\lambda}_pr{P}_{retain}{e}^{M_s}\kern2.25em 2r>{r}_e\end{array}\right. \), M s is the area of the shadow in Fig. 4 in fading environment.
Proof From the definition of ps and the exponential distribution of the fading, we get \( e\_ ps=E\left[ ps\right]=\mathrm{E}\left(\mathrm{Pro}\left[\frac{P_t{g}_i{r_i}^{-\beta }}{\sum_{j\ne i}{P}_t{g}_j{r_j}^{-\beta }}>T|{\mathrm{r}}_i=\mathrm{r}\right]\right)={\int}_{R^2} Pro\left[{g}_i>\frac{T{\sum}_{j\ne i}{g}_j{r_j}^{-\beta }}{{r_i}^{-\beta }}\right]{f}_{\mathrm{r}}\left(\mathrm{r}\right)d\mathrm{r}={\int}_{R^2}\exp \left(-\upmu \mathrm{T}{r}^{\beta}\mathrm{I}\right){f}_{\mathrm{r}}\left(\mathrm{r}\right)d\mathrm{r}={\int}_{R^2}{\mathcal{L}}_I\left(\upmu \mathrm{T}{r}^{\beta}\right){f}_{\mathrm{r}}\left(\mathrm{r}\right)d\mathrm{r} \), where g i is the fading gain from the transmitter to the receiver i, \( {\mathcal{L}}_I(s) \) is the Laplace functional of I, and I=\( {\sum}_{j\ne i}{g}_j{r_j}^{-\beta } \) is aggregate interference with unit transmitting power (even if the transmitting power is not unit, it is a common factor and can be removed from the numerator and the denominator in the SIR expression). For \( {\mathcal{L}}_I(s) \), there is not a closed form because the transmitting nodes form a hard core point process. But from the Compbell theorem [17], the mean of the aggregate interference is same for any stationary point process with same density and is irrelevant to the distribution of them. Therefore, we approximate I as the aggregate interference under a PPP deployed network and compute it in a closed form. The difference is that the interference nodes are distributed out of r e − r, and r e is the exclusion distance on current fading. So we get
And let s = μTrβ, we get \( {\mathcal{L}}_I\left(\upmu \mathrm{T}{r}^{\beta}\right)=\exp \left(-{\lambda}_p{P}_{\mathrm{retain}}.2\pi {\int}_{re-r}^{\infty}\frac{\mu \left(\mu +\mu T{\left(r/x\right)}^{\beta}\right)-1}{\mu \left(\mu +\mu T{\left(r/x\right)}^{\beta}\right)} xdx\right) \).
In this expression, r e is a variable affected by the fading and the sensing threshold of the network. We can get the probability density function (pdf) of r e by the fading distribution as \( {f}_{r_e}\left({r}_e\right)= t\mu \beta {r_e}^{\beta -1}\exp \left(-t{r_e}^{\beta}\right) \), where t = P0μ. When r > r e , the receiving node cannot sense the transmitter, so we consider r e ≥ r, and get \( {\mathcal{L}}_I\left(\mu T{r}^{\beta}\right)={\int}_r^{\infty}\exp \left(-{\lambda}_p{P}_{\mathrm{retain}}.2\pi {\int}_{re-r}^{\infty}\frac{\mu \left(\mu +\mu T{\left(\frac{r}{x}\right)}^{-\beta}\right)-1}{\mu \left(\mu +\mu T{\left(\frac{r}{x}\right)}^{-\beta}\right)} xdx\right){f}_{r_e}\left({r}_e\right)d{r}_{e.} \)
Then, f r (r) is the pdf of the distance between the intended transmitter and the receiver, or the pdf of nearest distance between two nodes in a hard core point process. From [15], we know that in hard core point model, the nearest distance between two nodes can be expressed as \( {f}_r(r)=\left\{\begin{array}{c}2\pi {\lambda}_pr{P}_{\mathrm{retain}}\kern1em 2r\le {r}_e\\ {}2\pi {\lambda}_pr{P}_{\mathrm{retain}}{e}^{M_s}\kern2.25em 2r>{r}_e\end{array}\right. \), where λ p is the density of the initial PPP, P retain is the retaining probability of a node in hard core point process, and M s is the area of shadow in Fig. 4. The proof is completed.
In this paper, we take the same process as Matérn type II model in MHCP model and MMHCP model and use PMHCP and PMMHCP to replace Pretain in (5) to approximate the pdf of distance between two nearest nodes. Generally, the expression (5) is not closed, but when the fading parameter μ = 1, \( {\mathcal{L}}_I \) has the closed form as \( {{\mathcal{L}}_I}^1(s)=\exp \Big(-{\lambda}_p{P}_{\mathrm{retain}}\pi {\int}_{re-r}^{\infty}\frac{v}{1+{s}^{-1}{v}^{\beta }} dv=\exp \left(-{\lambda}_p{P}_{\mathrm{retain}}{\pi s}^{\delta }.C\left({s}^{-\delta }{\left({r}_e-r\right)}^2,\beta \right)\right) \).
Plugging s = Tr i β, we get \( {\mathcal{L}}_I\left(T{r_i}^{\beta}\right)=\exp \left(-{\lambda}_p{P}_{\mathrm{retain}}\pi {T}^{\delta }{r}^2.C\left({T}^{-\delta }{r}^{-2}{\left({r}_e-r\right)}^2,\beta \right)\right) \), where δ = 2/β, and \( C\left(b,\alpha \right)={\int}_b^{\infty}\frac{1}{1+{u}^{\alpha /2}} du=\frac{2\pi }{\alpha}\csc \left(2\pi /\alpha \right)-b\ {}_2{F}_1\left(1,\frac{2}{\alpha };\frac{2+\alpha }{\alpha };-{b}^{\alpha /2}\right) \), where 2F1(.) is the hypergeometric function. At the same time, we have \( {f}_{r_e}^1\left({r}_e\right)={P}_0\beta {r_e}^{\beta -1}\exp \left(-{P}_0{r_e}^{\beta}\right) \) with μ = 1. The mean probability of successful reception can be approximated as:
Actually, due to the transmitting power P t has no influence on the successful transmission probability ps, we can let the transmitting power P t equals to 1/μ when the fading parameter μ ≠ 1. The virtual power \( {F}_i^j={P}_t.{g}_i^j \) still follows the exponential distribution with parameter 1 and can be analyzed by expression (6). From (6), it is clear that the fading parameter μ has no effect on the mean probability of successful reception for the whole network. In other words, the influence of fading on the successful reception probability in hard core point process deployed networks is same as that in the PPP deployed networks as [9]. The simulations in Section 7.1 also confirm this.
Another important metric for the network is the transmission capacity (TC), which captures the global effect of interference on the network throughput and many important features of a wireless network. In our paper, we define the transmission capacity as the mean number of successful transmissions per unit area, similar as [20], and denote it by TC = λ p × Pretain × e_ps. In the metric of transmission capacity, there still exists underestimation for the Matérn type II model. It is noticeable that when the nodes of the network is not so dense, the overestimation of MHCP model is not so obvious. But with the potential transmitting nodes becoming denser, the transmission capacity tends to be overestimated by the MHCP model. Since e_ps is almost immune to the initial transmitters density and the fading, the impact of the two factors on the transmission capacity stems from Pretain and λ p . Based on previous analysis on Pretain, the transmission capacity by our MMHCP model is also more accurate than the other two models, which is also shown in simulations of Section 7.1.
7 Results and discussions
7.1 Results
The retaining probability, transmitting density, probability of successful reception and the transmission capacity can be numerically evaluated and simulated via Monte Carlo method using MATLAB.
At first, we realize CSMA networks inherited from PPP with different densities in a rectangle with 10 × 10. In the absence of fading, a node is retained if the minimum distance between it and all of the previously retained nodes is greater than r e . Under fading condition, a node is retained if it has the lowest mark among its neighbors that can be sensed. Figure 3 is an example of the network in fading environment with initial PPP density λ p = 0.4, and fading parameter μ = 1, where the red stars are the initial nodes distributed as the PPP, and the blue circles are the retaining nodes in a time slot.
The retaining probability of a node decreases with the initial PPP density, while the transmitting density of the network varies not so much with it. To analyze the slope of the retaining probability and transmitting density with the density of initial PPP, we repeat 300 times by setting the initial PPP density from 0.2 to 2. The trend of retaining probability with the initial PPP density in the absence of fading is shown in Fig. 5, where r e = 1. The trend under Rayleigh fading condition is shown in Fig. 6. It is clear from both figures that the retaining probability decreases with the initial PPP density. At the same time, we can see from both figures that the simulation results are closer to the MMHCP model than Matérn type II model and MHCP model.
The transmitting node density in a time slot varies with the initial PPP density λ p when λ p is small, but the slope tends to be flat when λ p is large, which is consistent with our analysis. And from Figs. 7 and 8, we can see that the slope becomes flat much faster in the presence of fading (when λ p ≥ 0.8 or so) than that in the absence of fading (when λ p ≥ 2.5 or so). This concludes that fading makes the transmitting node density tends to be stable much faster. From the figures, the transmitting density of MMHCP model is also closer to the simulation than the other two models.
In the absence of fading, for the trend of the estimated density following the exclusion r e , we take a fixed density of initial PPP as 0.5 and set the exclusion radius from 0.1 to 1, and repeat the simulation for 300 times. The curves are shown in Fig. 9, where we can see the trend of transmitting density following r e . Meanwhile in the presence of fading, we demonstrate the retaining probability following with the fading parameter μ from 1 to 10 in Fig. 10.
From the analysis in Section 6, we know the mean probability of successful reception in the models of this paper does not change with the fading parameter μ. We repeat the simulation for 300 times for μ, setting SIR threshold from − 5 to 10 dB. The result is shown in Fig. 11. An interesting fact is that the density of initial PPP has little effect on the e_ps, as illustrated in Fig. 12, which is as same as that in a PPP deployed network.
For transmission capacity, we simulated the impact of the initial PPP density and the fading parameter on the metric. According to the expression of the transmission capacity and the analysis about the probability of successful reception, we know the initial PPP density and fading parameter affect the metric only from the transmitting node density. The Matérn type II model still has the flaw of underestimation. An example is shown as Fig. 13, that the transmission capacity increases with the density of the potential transmitters, where the density of the potential transmitters is set from 0.1 to 1, the fading parameter μ is set 10 and the SIR threshold is set 0 dB. Under such a channel condition, we can see that the MMHCP model is closer to the simulation result than the MHCP model. Figure 14 is an example of transmission capacity following with the fading parameter, where the initial PPP density is set 0.6 and SIR threshold is 2 dB. This figure also shows that the simulation is closer to the analysis by MMHCP model.
7.2 Discussions
For the result of transmitting node density of the network, it varies little with the initial PPP density, and the underlying reason is intuitive. Whether fading is fixed or not, when the density of initial PPP increases, the retaining probability of each node decreases for the characteristic of exclusion in hard core point process. But the transmitting node density of the whole network varies little when the initial PPP tends dense. Here, we take Matérn type II model in fading condition as an example. The transmitting density can be expressed as \( {\lambda^1}_{\mathrm{CSMA}}={\lambda}_p.{P}_{Matern}={\lambda}_p.\frac{1-\exp \left(-\overset{\sim }{N}\right)}{\overset{\sim }{N}}=\frac{1-\exp \left(-\frac{2\pi {\lambda}_p\Gamma \left(2/\beta \right)}{\beta {\left({P}_0\mu /{P}_t\right)}^{2/\beta }}\right)}{\frac{2\pi \Gamma \left(2/\beta \right)}{\beta {\left({P}_0\mu /{P}_t\right)}^{2/\beta }}} \). From the expression, we can see that the density λ p only affects the exponent in the numerator, and when it tends to infinity, the transmitting density tends to be \( \frac{\beta {\left({P}_0\mu /{P}_t\right)}^{2/\beta }}{2\pi \Gamma \left(2/\beta \right)} \), which tends to be irrelevant to λ p .
For the probability of successful reception, we know in a PPP deployed network, it has been proved in [9, 10] that the density of nodes has no impact on the probability of successful reception. Similarly, in a CSMA network deployed by granting hard core points transmitting simultaneously from an initial PPP, we can see from Fig. 12 that the probability e_ps varies little with the initial PPP density. From (6), we know that the probability e_ps is affected by λ p from \( {\mathcal{L}}_I \) and f r (r). In our analysis, the retaining probability Pretain decreases with λ p , but the product of λ p and Pretain actually varies little for a fixed point process. That is why the initial PPP density has little effect on the final probability of successful reception when λ p tends to infinity.
Finally, it should be noted that the reason of MMHCP model outperforming the MHCP model is the network nodes becoming denser or the channel condition becoming worse. In fact, when the network is sparse and the fading is not so serious, the overestimation of MHCP model is not so obvious, even the intensity underestimation flaw still exists in the MHCP, as stated in [20]. That is why the curve of simulation (magenta) is not far from the blue curve (MHCP model) when the fading parameter μ is small (≤6). But with the fading parameter μ becoming large, the curve tends to be close to the red curve (MMHCP model). From this discussion, we know the MMHCP model is more suitable for the dense network and with bad fading condition.
8 Conclusions
In this paper, we study the model of dense CSMA networks with randomly distributed nodes and analyze the transmitting density, mean probability of successful reception, and transmission capacity. In view of that the Matérn type II model underestimates and MHCP model overestimates the density of the simultaneously transmitting nodes, we propose another modification on the traditional model to alleviate the overestimation of the density. We give a more accurate density estimation for the simultaneously transmitting nodes in dense networks and in fading environment. In the absence of fading, given the initial density of the PPP and exclusion radius, we express the density estimation in a closed form by regarding the retaining probability of each node being same. Under Rayleigh fading condition, we express the retaining probability of a node with fading parameter and initial PPP density. The simulation results demonstrate that the density from MMHCP model is closer to the actual distribution of nodes in CSMA than Matérn type II model and MHCP model. The impact of the density of nodes and fading factor on the mean probability of successful reception and transmission capacity are also studied in our numerical analysis and simulations, from which we can see that the fading parameter has no effect on the probability of successful reception, which is same as that in the PPP deployed network. And the density of initial PPP also has little effect on the probability under Rayleigh fading when the network becomes dense. The density of initial nodes and the fading conditions affect the transmission capacity as they affect the active nodes density, and with the nodes becoming denser or the fading deteriorates, the simulation tends to be close to the MMHCP model. All simulations confirm that the proposed model can be used to accurately model the network behavior than Matérn type II and MHCP models in many situations.
References
L Feng, J Yu, X Cheng, M Atiquzzaman, A novel contention-on-demand design for wifi hotspots. Pers. Ubiquit. Comput. 20(5), 1–12 (2016)
L Feng, J Yu, X Cheng, S Wang, Analysis and optimization of delayed channel access for wireless cyber-physical systems. EURASIP J. Wirel. Commun. Netw. 60, 1–13 (2016)
M Garetto, T Salonidis, EW Knightly, Modeling per-flow throughput and capturing starvation in csma multi-hop wireless networks. IEEE/ACM Trans. Networking 16(4), 864–877 (2008)
M Durvy, O Dousse, P Thiran, On the fairness of large csma networks. IEEE Selected Areas in Comm. 27(7), 1093–1104 (2009)
Y Kim, F Baccelli, G de Veciana, Spatial reuse and fairness in mobile ad-hoc networks with channel-aware CSMA protocols. Int. Symp. Model. Optim. Mob. 60(7), 360–365 (2011)
G Wang, J Yu, D Yu, H Yu, L Feng, P Liu, Ds-mac: An energy efficient demand sleep mac protocol with low latency for wireless sensor networks. J. Netw. Comput. Appl. 58, 155–164 (2015)
Q Zhao, T Sakurai, J Yu, L Sun, Maximizing the stable throughput of high-priority traffic for wireless cyber-physical systems. EURASIP J. Wirel. Commun. Netw. 2016, 1–12 (2016)
H Elsawy, E Hossain, M Haenggi, Stochastic geometry for modeling, analysis, and design of multi-tier and cognitive cellular wireless networks: a survey. IEEE Commun. Surv. Tutorials 15(3), 996–1019 (2013)
JG Andrews, F Baccelli, RK Ganti, A tractable approach to coverage and rate in cellular networks. IEEE Trans. Commun. 59(11), 3122–3134 (2011)
H Dhillon, R Ganti, F Baccelli, JG Andrews, Modeling and analysis of k-tier downlink heterogeneous cellular networks. IEEE J. Sel. Areas Commun. 30(3), 550–560 (2012)
S Weber, JG Andrews, N Jindal, An overview of the transmission capacity of wireless networks. IEEE Trans. Commun. 58(12), 3593–3604 (2010)
V Suryaprakash, J Møller, G Fettweis, On the modeling and analysis of heterogeneous radio access networks using a Poisson cluster process. IEEE Trans. Wirel. Commun. 14(2), 1035–1047 (2015)
N Deng, W Zhou, M Haenggi, The Ginibre point process as a model for wireless networks with repulsion. IEEE Trans. Wirel. Commun. 14(1), 107–121 (2015)
M Haenggi, Mean interference in hard-core wireless networks. IEEE Commun. Lett. 15, 792–794 (2011)
G Alfano, M Garetto, E Leonardi, New directions into the stochastic geometry analysis of dense csma networks. IEEE Trans. Mob. Comput. 13(2), 324–336 (2014)
HQ Nguyen, F Baccelli, D Kofman, A Stochastic Geometry Analysis of Dense IEEE 802.11 Networks, Proc. 26th IEEE International Conference on Computer Communications (Infocom 07) (2007), pp. 1199–1207
F. Baccelli, B. Blaszczyszyn: Stochastic Geometry and Wireless Networks, Volume II: Applications. Now, Paris (2009). 69–77
Y Kim, F Baccelli, G De, Veciana: Spatial reuse and fairness in mobile ad-hoc networks with channel-aware CSMA protocols. IEEE Trans. Information Theory 60(7), 360–365 (2011)
F Baccelli, B Blaszczyszyn, P Mühlethaler, An aloha protocol for multihop mobile wireless networks. IEEE Trans. Information Theory 52(2), 421–436 (2006)
H ElSawy, E Hossain, A modified hard core point process for analysis of random csma wireless networks in general fading environments. IEEE Trans. Commun. 61(4), 1520–1533 (2013)
H. ElSawy, E. Hossain, S. Camorlinga: Characterizing Random CSMA Wireless Networks: A Stochastic Geometry Approach. IEEE ICC 2012- Wireless Networks. Symposium, 5000–5004 (2012)
L Ji, S Cheng, Z Cai, J Yu, C Wang, Y Li, Approximate holistic aggregation in wireless sensor networks. ACM transactions on sensor. Networks 607(3), 381–390 (2015)
Z He, Z Cai, S Cheng, X Wang, Approximate aggregation for tracking quantiles and range countings in wireless sensor networks. Theor. Comput. Sci. 13(2), 11–11124 (2017)
S Cheng, Z Cai, J Li, Curve query processing in wireless sensor networks. IEEE Trans. Veh. Technol. 64(11), 5198–5209 (2015)
H He, J Xue, T Ratnarajah, FA Khan, CB Papadias, Modeling and analysis of cloud radio access networks using matérn hard-core point processes. IEEE Trans. Wirel. Commun. 15(6), 4074–4087 (2016)
A Busson, G Chelius, JM Gorce, Interference Modeling in Csma Multi-Hop Wireless Networks. INRIA, Research. Report, vol 6624 (2008)
A Busson, G Chelius, Point Processes for Interference Modeling in CSMA/CA Ad-Hoc Networks, Sixth ACM Symp. Performance Evaluation of Wireless Ad Hoc, Sensor, and Ubiquitous. Networks (2009), pp. 33–40
ML Huber, RL Wolpert, Likelihood based inference for matérn type iii repulsive point processes. Adv. Appl. Probab. 41(4), 958–977 (2009)
J Yu, B Huang, X Cheng, M Atiquzzaman, Shortest link scheduling algorithms in wireless networks under sinr. IEEE Trans. Veh. Technol. 66(3), 2643–2657 (2017)
X Zhang, J Yu, W Li, X Cheng, D Yu, F Zhao, Localized algorithms for Yao graph-based spanner construction in wireless networks under sinr. IEEE/ACM Trans. Networking 25(4), 2459-2472 (2017)
K Yu, J Yu, X Cheng, T Song, Theoretical Analysis of Secrecy Transmission Capacity in Wireless Ad Hoc Networks, IEEE. Wireless Communications and Networking Conference (2017), pp. 1–6
J. Venkataraman, M. Haenggi, O. Collins: Shot Noise Models for the Dual Problems of Cooperative Coverage and Outage in Random. Networks. 44th Annual Allerton Conf. Commun., Control, and Comput., 2642–2650 (2006)
J Venkataraman, M Haenggi, O Collins, Shot Noise Models for Outage and Throughput Analyses in Wireless Ad Hoc Networks, Proc. IEEE Military Commun. Conf. (MILCOM 06) (2006), pp. 1–7
M Haenggi, RK Ganti, Interference in large wireless networks. Found. Trends Networking 3(2), 127–248 (2009)
A Hasan, JG Andrews, The guard zone in wireless ad hoc networks. IEEE Trans. Wirel. Commun. 6, 897–906 (2007)
RK Ganti, F Baccelli, JG Andrews, Series expansion for interference in wireless networks. IEEE Trans. Inf. Theory 58(4), 2194–2205 (2012)
M Haenggi, Stochastic Geometry for Wireless Networks (Cambridge University Press, Cambridge, 2012), pp. 1–298
Acknowledgements
This work is supported by the NSF of China under Grant 61373027, 61672321, and 61771289 and Shandong Province Higher Educational Science and Technology Program under Grant J15LN06.
Availability of data and materials
All data in this paper are fully available without restriction.
Author information
Authors and Affiliations
Contributions
YS and RL designed and analyzed the models. YS, HJ, and JZ designed and performed the simulations. YS, RL, and LN wrote the paper. All authors read and approved the final manuscript.
Corresponding author
Ethics declarations
Competing interests
The authors declare that they have no competing interests.
Publisher’s Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is distributed under the terms of the Creative Commons Attribution 4.0 International License (http://creativecommons.org/licenses/by/4.0/), which permits unrestricted use, distribution, and reproduction in any medium, provided you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons license, and indicate if changes were made.
About this article
Cite this article
Sun, Y., Li, R., Jiang, H. et al. Modeling and analysis of random dense CSMA networks. J Wireless Com Network 2018, 121 (2018). https://doi.org/10.1186/s13638-018-1107-4
Received:
Accepted:
Published:
DOI: https://doi.org/10.1186/s13638-018-1107-4