Abstract
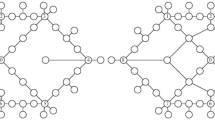
In the computational experiments on a model of a multiuser communication and control network, changes in the system’s performance under destructive effects are studied. The vector of the maximal flows that can be transmitted independently between all nodes is used for the multicriteria assessment of the system’s functionality. The set of damage of various types is considered, consisting of specially selected vertices and minimal cuts; when they are removed, the maximal possible flow turns out to be zero for at least one source–sink pair. To assess the consequences and impact on the quality of communication of a specific destructive effect for each pair of nodes, the characteristic vector of the maximal permissible flows is formed. Computational experiments are carried out for all the damage from the given set and make it possible to determine a representative set of characteristic vectors. To obtain guaranteed estimates, a component-by-component analysis, sorting, and comparison by several criteria of all the performance indicators is performed. Final diagrams are constructed, reflecting the changes in the initial functional characteristics for the given set of targeted destructive actions. The aggregated assessments and indicators allow comparing the vulnerability and survivability of network systems with different structural features.






Similar content being viewed by others
REFERENCES
Yu. E. Malashenko and I. A. Nazarova, “Analysis of critical damage in the communication network. I. Model and computational experiment,” J. Comput. Syst. Sci. Int. 59, 745 (2020).
Yu. B. Germeier, Introduction to Operations Research Theory (Nauka, Moscow, 1971) [in Russian].
Yu. E. Malashenko, I. A. Nazarova, and N. M. Novikova, “An approach to the analysis of possible structural damages in multicommodity network systems,” Comput. Math. Math. Phys. 59, 1562 (2019).
Yu. E. Malashenko, I. A. Nazarova, and N. M. Novikova, “Fuel and energy system control at large-scale damages. IV. A priori estimates of structural and functional vulnerability,” J. Comput. Syst. Sci. Int. 57, 907 (2018).
P. Jensen and J. Barnes, Network Flow Programming (Wiley, New York, 1980).
Th. H. Cormen, Ch. I. Leiserson, R. L. Rivest, et al., Introduction to Algorithms (Prentice Hall, Englewood Cliffs, 2005).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Malashenko, Y.E., Nazarova, I.A. Analysis of Critical Damage in the Communication Network. II. Guaranteed Functional Performance Estimates. J. Comput. Syst. Sci. Int. 59, 918–927 (2020). https://doi.org/10.1134/S106423072006009X
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1134/S106423072006009X