Abstract
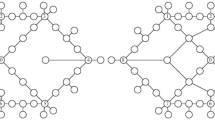
In the computational experiments on a flow model of a communication and control network, changes in the system’s functional characteristics under destructive effects are studied. The removal of a subset of edges is considered to be critical damage if it results in the absence of connection paths for at least one pair of source-sink nodes. For each case of damage, both the total number of disconnected pairs and all communication directions, the throughput of which is less than the specified standard value, are determined. Based on the data obtained, multiparameter diagrams are constructed for assessing changes in the maximum flows for each dividing cut and all pairs of vertices. The boundary points on the diagrams correspond to the most dangerous damage not dominated by at least one damage indicator. The results of the effects of destructive effects on network systems with various structural features are analyzed.






Similar content being viewed by others
REFERENCES
P. Jensen and W. J. P. Barnes, Network Flow Programming (Krieger, Malabar, FL, 1987).
H. Frank and I. T. Frisch, Communication, Transmission, and Transportation Networks (Addison-Wesley, Reading, MA, 1971).
Yu. B. Germeier, Introduction to the Theory of Operations Research (Nauka, Moscow, 1971) [in Russian].
T. N. Dinh and M. T. Thai, “Assessing attack vulnerability in networks with uncertainty,” in Proceedings of the IEEE Conference on Computer Communications (INFOCOM), Kowloon,2015, pp. 2380–2388.
Yu. E. Malashenko, I. A. Nazarova, and N. M. Novikova, “An approach to the analysis of possible structural damages in multicommodity network systems,” Comput. Math. Math. Phys. 59, 1562 (2019).
M. Lalou, M. A. Tahraoui, and H. Kheddouci, “The critical node detection problem in networks: A survey,” Comput. Sci. Rev. 28, 92–117 (2018).
J. Walteros and P. Pardalos, “Selected topics in critical element detection,” Optimiz. Appl. 71, 9–26 (2012).
A. Veremyev, O. A. Prokipyev, and E. L. Pasiliao, “Critical nodes for distance-based connectivity and related problems in graphs,” Networks 66, 170–195 (2015).
M. Ventresca, K. R. Harrison, and B. M. Ombuki-Berman, “The bi-objective critical node detection problem,” Eur. J. Oper. Res. 265, 895–908 (2018).
J. Li, P. M. Pardalos, B. Xin, and J. Chen, “The bi-objective critical node detection problem with minimum pairwise connectivity and cost: Theory and algorithms,” Soft Comput. 23, 1–16 (2019).
A. Kuhnle, N. P. Nguyen, T. N. Dinh, and M. T. Thai, “Vulnerability of clustering under nodes failure in complex networks,” Social Network Anal. Mining 7, 8–24 (2017).
Yu. E. Malashenko, I. A. Nazarova, and N. M. Novikova, “Analysis of cluster damages in network systems,” Comput. Math. Math. Phys. 60, 341 (2020).
T. H. Grubesic, T. C. Matisziw, A. T. Murray, et al., “Comparative approaches for assessing network vulnerability,” Int. Regional Sci. Rev. 31, 88 (2008).
A. T. Murray, “An overview of network vulnerability modeling approaches,” Geo J. 78, 209–221 (2013).
J. Johansson, “Risk and vulnerability analysis of interdependent technical infrastructures. Addressing socio-technical systems,” Doctoral Thesis in Industrial Automation (Lund Univ., Lund, 2010).
T. Gomes, C. Esposito, D. Hutchison, F. Kuipers, J. Rak, and M. Tornatore, “A survey of strategies for communication networks to protect against large-scale natural disasters,” in Proceedings of the International Workshop on Reliable Networks Design and Modeling (RNDM), Halmstad,2016, pp. 11–22.
V. Velichko, V. Popkov, and G. Popkov, Models and Methods for Increasing the Survivability of Modern Communication Systems (Goryachaya Liniya - Telekom, Moscow, 2017) [in Russian].
A. K. Levakov, Features of the Functioning of Next-Generation Telecommunication Networks in Emergency Situations (IRIAS, Moscow, 2012) [in Russian].
S. I. Noskov, A. A. Butin, and L. E. Sokolova, “Multicriterial assessment of the level of vulnerability of the objects of infomatization,” Dokl. TUSURa, No. 2 (32), 137–142 (2014).
S. Wang, J. Zhang, and N. Duana, “Multipleperspective vulnerability analysis of the power network,” Phys. A (Amsterdam, Neth.) 492, 1581–1590 (2018).
A. M. Faddeev, “Vulnerability of transmission systems of Russia, other post-soviet states and european countries to the cascade faults,” Vestn. MGU. Ser. 5: Geogr., No. 1, 46–53 (2016).
Y. E. Malashenko, I. A. Nazarova, N. M. Novikova, and I. I. Pospelova, “A network flow model for power and energy system with changing capabilities,” Int. J. Public Administr. 42, 1323–1332 (2019).
Yu. E. Malashenko, I. A. Nazarova, and N. M. Novikova, “Fuel and energy system control at large-scale damages. IV. A priori estimates of structural and functional vulnerability,” J. Comput. Syst. Sci. Int. 57, 907–920 (2018).
J. O. Royset and R. K. Wood, “Solving the bi-objective maximum-flow network-interdiction problem,” INFORMS J. Comput. 19, 175–184 (2007).
C. D. Nicholson, K. Kashbarker, and J. E. Ramirez-Marquez, “Flow-based vulnerability measures for network component importance: Experimentation with preparedness planning,” Reliab. Eng. Syst. Safety 145, 62–73 (2016).
T. Cormen, Ch. Leiserson, R. Rivest, and C. Stein, Introduction to Algorithms (MIT Press, Boston, MA, 2009).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Malashenko, Y.E., Nazarova, I.A. Analysis of Critical Damage in the Communication Network: I. Model and Computational Experiment. J. Comput. Syst. Sci. Int. 59, 745–754 (2020). https://doi.org/10.1134/S106423072005010X
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1134/S106423072005010X