Abstract
In this paper, we propose a two-stage stochastic optimization model for the provision services in a multi-tiered network, consisting in user or devices on the ground requiring services to controller UAVs in flight. The requested services are executed by a fleet of pre-existing and additional UAVs. The possible occurrence of disaster scenarios and the related uncertainty and severity could cause an unexpected and sudden increase in demand. Hence, the aim of the proposed model is to optimize the management of the pre-existing and additional resources in order to maximize the total profit of service providers and, simultaneously, minimize the expected loss related to a possible unmet demand. A variational approach is proposed, and some numerical examples are performed to validate the effectiveness of our model.
Similar content being viewed by others
Avoid common mistakes on your manuscript.
1 Introduction
The 5G technology (fifth-generation technology), whose worldwide distribution started in 2019, aims to achieve greater efficiency and versatility in the support of network applications (see [1]). Through the optimization of the use of network resources (see [2]), the definition of virtual subnets, the virtualization of most of the network devices (see [3]), the ability to manage a greater number of devices per unit of surface area, the support of more advanced features in terms of latency to ensure real-time response times, higher data rates and a significant reduction in power consumption, 5G networks are used primarily as general internet service providers, competing with existing ISPs providing networked services, and enable new applications in the Internet of Things, IoT (see [4]), and machine-to-machine areas. In less than a year, 81 operators in 42 countries have launched commercial 5G services and 386 operators in 97 countries have invested in the new networks. The 5G technologies and their features are currently used in all possible fields of application, from retail to education, transportation to entertainment, smart homes to healthcare, agricultural sector to supply chain management (see [5,6,7,8]).
Parallel to the advent and growth of 5G networks around the world, COVID-19 pandemic rapidly spread around the world affecting almost all countries and 179 million people, including 3 million deaths (see [9]) and raising enormous health, economic and social challenges (see [10, 11]). The strong containment measures, the nation-wide lockdowns and the social distancing norms, have resulted in increased Internet traffic demands (see [12]) and in the use of digital technologies in the daily lives. Work, education and all human activities have been profoundly changed by the advent of the pandemic and, for instance, educational institutions shift to distance learning to guarantee the education at all levels (see [13]). The need to move all normal activities into a secure and virtual environment is an evidence of the digital acceleration process. In this contest, 5G technologies and their ability to manage a greater number of heterogeneous users or devices and digital traffic can play a vital role to address the wide spectrum of challenges due to COVID-19. (see [14]).
In general, when a disaster occurs, it is plausible to assume that the physical connections that guarantee certain types of services are compromised (for example in the event of an earthquake, landslide, tsunami). In such cases, it is necessary that these types of services are restored quickly or introduced for the first time and the introduction of a 5G network could be the only way to have the provision of services in the event of serious disruptions at ground level, especially if these services are requested by emergency services. The restoration of such services requires that service providers be able to cover the sudden and increasing demand from users or devices on some areas of the ground and this could be challenging and expensive especially if the service providers are totally unprepared for this event. For these reasons, to help the providers to supply the requested services in disasters scenarios, the Unmanned Aerial Vehicles (UAVs) can be very useful (if not even necessary) to monitor hard-to-reach areas and also provide services in rural or energy-deprived areas (see [15] for a survey collecting much earlier work in the intersection of UAVs and communications). The UAVs, such as drones, can be connected to each other and form a real network capable of receiving requests, such as automotive applications, data sharing, wearable health sensors, video calling, smart -traffic control systems, Video Monitoring or video surveillance (see [16] for an extended 5G network slice for video monitoring with a FANET), managing them and executing them through the computer elements they have above (see [17,18,19,20] for optimization models for 5G network with UAVs).
Many authors, in their works, are dealt with the use of UAVs in managing a disaster (see [21] for an interesting review of the state-of-the-art optimization approaches in the civil application of drone operations and drone-truck combined operations including construction/infrastructure, agriculture, transportation/logistics, security/disaster management, entertainment/media, etc.). In [22], authors deal with the problem of locating trapped people and routing aid to them after a disaster event. To address the issues associated with the probable failures in the transportation and telecommunications networks, which are often rendered unusable by the disaster at hand, the authors propose two-echelon vehicle routing frameworks for performing these operations using aerial uncrewed autonomous vehicles (UAVs or drones). Specifically, they present two decision frameworks, in which the resulting optimization problem is formulated as a two-echelon vehicle routing problem. The first framework addresses the problem in two stages: providing telecommunications capabilities in the first stage and satisfying the resulting demands in the second. The second framework, on the other hand, addresses the problem as a stochastic emergency aid delivery problem, which uses a two- stage robust optimization model to handle demand uncertainty. Zhao et al. in [23], propose a unified framework of UAV-assisted emergency network in disasters. Particularly, first the trajectory and scheduling of UAV are jointly optimized to provide wireless service to ground devices with surviving BSs and, then, the transceiver design of UAV and establishment of multi-hop ground device-to-device (D2D) communication are studied to extend the wireless coverage of UAV.
Moreover, another aspect of fundamental importance, especially in a disaster situation, is represented by the possibility of adding resources to those already present (see [24]). Such additional resources could be, for instance, new UAVs put into flight and added to the network or they also may consist of increasing the capabilities of pre-existing UAVs. The additional resources make it possible to satisfy a greater quantity of requests (which during disastrous events, as already mentioned above, generally tend to increase or move to zones).
In this paper we propose a two-stage stochastic optimization model, where the first stage is the deterministic stage while the second one depends on the disaster scenario that may occur. Both the preparation stage and the response stage are important in managing a disaster. Particularly, the consideration of uncertainty of possible disaster scenarios and their severity, with the appropriate management of additional resources, could guarantee service providers greater efficiency in their response to a disaster advent.
The paper is organized as follows. In Sect. 2, we present the mathematical network model and derive a two-stage stochastic constrained optimization model whose solutions are obtained through the variational formulation, presented in Sect. 3. Through the Lagrange theory, in Sect. 4, we get an equivalent variational formulation to the one obtained that we will use in the resolution of some numerical examples, contained in Sect. 5, together with a discussion of the results. Finally, Sect. 6 is devoted to the conclusions.
2 The Mathematical Model
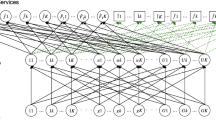
The two-stage stochastic optimization model consists of G users or devices on the ground, with a typical one denoted by g; K types of services, with a generic one denoted by k; U controller UAVs in flight, with a generic one denoted by u; \(\hat{F}_1\) pre-existing UAVs, with a generic one denoted by \(\hat{f}\) and \(\tilde{F}_2\) additional UAVs, with a typical one denoted by \(\tilde{f}\). We consider the following sets:
that are, respectively, the set of pre-existing UAVs, the set of possible additional UAVs and the set of all the UAVs, where \(|\mathcal {F}|=F_3=\hat{F}_1+\tilde{F}_2\).
Services requested by a user or device on the ground are received by the controller UAVs, which are spatially distributed in the considered geographical area, and each controller UAV sends the requests for execution of the services to the fleet of UAVs at the higher level which performs the executions. Moreover, we consider the possibility to add additional drones to the fleet of UAVs and additional capacities to controller UAVs.
The supply chain network, consisting of a fleet of UAVs, controller UAVs and users or devices on the ground, is depicted in Fig. 1.
As mentioned in the Introduction, when a disaster scenario occurs, there may be the need to restore or introduce some services to cope with a possible growth in request. The total unpreparedness of the service providers could make this process expensive, difficult and time-consuming. For these reasons, in this paper, we provide a two-stage stochastic optimization model where the first stage represents the pre-crisis phase and the second one represents the critical phase. In the first stage that represents the preparedness phase, a service provider has to solve a deterministic optimization problem. In the second stage, a service provider considers several scenarios with different probabilities to better face a probable subsequent critical phase, trying to maximize its total profit (defined by the difference between the revenue and the sum of costs and penalties). Hence, the actions that a service provider takes in Stage 2, as soon as the disaster has occurred, depend on the possible scenario and the realization of probabilistic parameters.
Let us consider \(\Omega\) the set of all possible disastrous scenarios and \(\omega \in \Omega\) a typical disaster scenario.
As previously mentioned, in this model we provide a system stochastic optimization perspective, determining a profit maximization problem for service providers.
The variables and parameters for the model both in Stages 1 and 2 are reported in Tables 1 and 2, respectively.
The cost functions, both in the first and in the second stage, are now described. Let:
-
\(c_{gu}^1\) be the transmission cost of the service requests from user or device g to controller UAV u in Stage 1 and let us assume \(c_{gu}^1\) is a function of \(\displaystyle \sum _{k=1}^K{x_{guk}^1}\):
$$c_{gu}^1=c_{gu}^1\left( \sum _{k=1}^K{x_{guk}^1}\right) = c_{gu}^1( {X_{gu}^1}), \quad \forall g=1,\ldots ,G,\; \forall u=1,\ldots ,U;$$ -
\(c_{gu}^{2\omega }\) the transmission cost of the service requests from user or device g to controller UAV u in Stage 2 under scenario \(\omega \in \Omega\) and let us assume \(c_{gu}^{2\omega }\) is a function of \(\displaystyle \sum _{k=1}^K{x_{guk}^{2\omega }}\):
$$c_{gu}^{2\omega }=c_{gu}^{2\omega }\left( \sum _{k=1}^K{x_{guk}^{2\omega }}\right) = c_{gu}^{2\omega }( {X_{gu}^{2\omega }}), \quad \forall g=1,\ldots ,G,\; \forall u=1,\ldots ,U,\; \forall \omega \in \Omega ;$$ -
\(c_{uf}^1\) be the transmission cost of the service requests from controller UAV u to any UAV \(f \in {\mathcal {F}}_{3}\) in the upper tier fleet (that could be represented by a pre-existing UAV \(\hat{f}\in \hat{\mathcal {F}}_{1}\) or an additional UAV \(\tilde{f}\in \tilde{\mathcal {F}}_{2}\)) in Stage 1 and let us assume \(c_{uf}^1\) is a function of \(\displaystyle \sum _{k=1}^K{x_{ufk}^1}\):
$$c_{uf}^1=c_{uf}^1\left( \sum _{k=1}^K{x_{ufk}^1}\right) , \quad \forall u=1,\ldots ,U,\; \forall f \in {\mathcal {F}}_{3},$$that is \(c_{u\hat{f}}^1=c_{u\hat{f}}^1({X_{u\hat{f}}^{2,1}}), \quad \forall u=1,\ldots ,U,\; \forall \hat{f}\in \hat{{\mathcal {F}}}_{1}\) and \(c_{u\tilde{f}}^1=c_{u\tilde{f}}^1({X_{u\tilde{f}}^{3,1}}), \quad \forall u=1,\ldots ,U,\; \forall \tilde{f}\in \tilde{{\mathcal {F}}}_{2}\);
-
\(c_{uf}^{2\omega }\) be the transmission cost of the service requests from controller UAV u to any UAV \(f \in {\mathcal {F}}_{3}\) in the upper tier fleet (that could be represented by a pre-existing UAV \(\hat{f}\in \hat{\mathcal {F}}_{1}\) or an additional UAV \(\tilde{f}\in \tilde{\mathcal {F}}_{2}\)) in Stage 2 under scenario \(\omega \in \Omega\) and let us assume \(c_{uf}^{2\omega }\) is a function of \(\displaystyle \sum _{k=1}^K{x_{ufk}^{2\omega }}\):
$$c_{uf}^{2\omega }=c_{uf}^{2\omega }\left( \sum _{k=1}^K{x_{ufk}^{2\omega }}\right) , \quad \forall u=1,\ldots ,U,\; \forall f \in {\mathcal {F}}_{3}\; \forall \omega \in \Omega ,$$that is \(c_{u\hat{f}}^{2\omega }=c_{u\hat{f}}^{2\omega }({X_{u\hat{f}}^{2,2\omega }}), \quad \forall u=1,\ldots ,U,\; \forall \hat{f}\in \hat{{\mathcal {F}}}_{1}\) and \(c_{u\tilde{f}}^{2\omega }=c_{u\tilde{f}}^{2\omega }({X_{u\tilde{f}}^{3,2\omega }})\), \(\forall u=1,\ldots ,U,\; \forall \tilde{f}\in \tilde{{\mathcal {F}}}_{2}\);
-
\(c_{f}^{(E),1}\) be the execution cost of requested services to the UAV \({f}\in {\mathcal {F}}_{3}\) in Stage 1 and let us assume \(c_{f}^{(E),1}\) is a function of the total amount of executed services, \(\displaystyle { \sum _{u=1}^{U}\sum _{k=1}^K x_{ufk}^1}\):
$$\displaystyle c_{f}^{(E),1}=c_{{f}}^{(E),1}\left( { \sum _{u=1}^{U}\sum _{k=1}^K x_{u{f}k}^1} \right) ,$$that is \(\displaystyle c_{\hat{f}}^{(E),1}\left( X^{2,1}_{\hat{f}} \right) , c_{\tilde{f}}^{(E),1}\left( X^{3,1}_{\tilde{f}} \right) \quad \forall f \in {\mathcal {F}}_{3}, \;\forall \hat{f} \in \hat{\mathcal {F}}_1,\; \forall \tilde{f}\in \tilde{\mathcal {F}}_2;\)
-
\(c_{f}^{(E),2\omega }\) be the execution cost of requested services to the UAV \({f}\in {\mathcal {F}}_{3}\) in Stage 2 under scenario \(\omega \in \Omega\) and let us assume \(c_{f}^{(E),2\omega }\) is a function of the total amount of executed services, \(\displaystyle { \sum _{u=1}^{U}\sum _{k=1}^K x_{ufk}^{2\omega }}\):
$$c_{f}^{(E),2\omega }=c_{{f}}^{(E),2\omega }\left( \sum _{u=1}^{U}\sum _{k=1}^K x_{u{f}k}^{2\omega } \right) ,$$that is \(c_{\hat{f}}^{(E),2\omega }\left( X^{2,2\omega }_{\hat{f}}\right) , c_{\tilde{f}}^{(E),2\omega }\left( {X^{3,2\omega }_{\tilde{f}}} \right) ,\) \(\forall f \in {\mathcal {F}}_{3}, \;\forall \hat{f} \in \hat{\mathcal {F}}_1,\; \forall \tilde{f}\in \tilde{\mathcal {F}}_2,\; \forall \omega \in \Omega ;\)
-
\(c_{u}^1\) be the cost due to add capacity to controller UAV u, \(\forall u=1,\ldots ,U\) in Stage 1 and let us assume \(c_u^1\) is a function of the additional capacity \(\gamma _u^1\), that is:
$$c_u^1=c_u^1(\gamma ^1_u),\quad \forall u=1,\ldots ,U;$$ -
\(c_{u}^{2\omega }\) be the cost due to add capacity to controller UAV u, \(\forall u=1,\ldots ,U\) in Stage 2 when scenario \(\omega\) occurs, \(\forall \omega \in \Omega\) and let us assume \(c_u^{2\omega }\) is a function of the additional capacity in Stage 2 under scenario \(\omega\), \(\gamma _u^{2\omega }\), that is:
$$c_u^{2\omega }=c_u^{2\omega }(\gamma ^1_u),\quad \forall u=1,\ldots ,U,\; \forall \omega \in \Omega ;$$ -
\(c_{\tilde{f}}^1\) be the cost due to add a new UAV \(\tilde{f}\in \tilde{\mathcal {F}}_{2}\) at the highest level of the network in Stage 1 and let us assume \(c_{\tilde{f}}^1\) is a function of the flow of requests received:
$$c_{\tilde{f}}^1\left( \sum _{u=1}^U\sum _{k=1}^K x_{u\tilde{f}k}^1\right) =c_{\tilde{f}}^1\left( X_{\tilde{f}}^{3,1}\right) , \quad \forall \tilde{f}\in \tilde{\mathcal {F}}_{2}.$$Note that, in this framework, we will suppose that there are not fixed costs to reserving the use of UAVs or they can be considered negligible. Therefore, in the event that no service request is sent to the UAV \(\tilde{f}\), we obtain that this function is null (\(c_{\tilde{f}}^1(0)=0\)).
-
\(c_{\tilde{f}}^{2\omega }\) be the cost due to add a new UAV \(\tilde{f}\in \tilde{\mathcal {F}}_{2}\) at the highest level of the network in Stage 2 under scenario \(\omega \in \Omega\) and let us assume \(c_{\tilde{f}}^{2\omega }\) is a function of the flow of requests received:
$$c_{\tilde{f}}^{2\omega }\left( \sum _{u=1}^U\sum _{k=1}^K x_{u\tilde{f}k}^{2\omega }\right) =c_{\tilde{f}}^{2\omega }\left( X_{\tilde{f}}^{3,2\omega }\right) , \quad \forall \tilde{f}\in \tilde{\mathcal {F}}_{2},\; \forall \omega \in \Omega .$$As in Stage 1, we will assume that these functions are determined such that they are null in the event that no service request is sent to the UAV \(\tilde{f}\) (\(c_{\tilde{f}}^{2\omega }(0)=0\)).
In this paper the limited flight duration due to the consumption of batteries, that is the limitation that distinguishes UAVs, is also taken into account since we integrated it in the execution cost of requested services and in the maximum capacity of each UAV. Moreover, since we consider the cost of handling requests, at the level of controller UAVs, negligible and we assume to be constant the cost to keep the UAVs u in flight, we do not include them in our model, but extension to a more general case is easy. We analyze the system from the point of view of the network and service provider. Therefore, the presented model aims at determining the optimal distributions of services requests flows from users and devices on the ground to the controller UAVs, the optimal distributions of services requests flows from the controller UAVs to the (pre-existing and additional) UAVs belonging to the fleet at the highest level of the network, but also the possible additional capacities to put in each controller UAV.
The objective function to maximize consists of the profit of both the two stages and is given by the total revenue, to which all transmission and execution costs are subtracted, as well as the costs for additional UAVs and to increase the capacities of the controller UAVs are subtracted. Also the expected value of the profit in the second stage is added.
A service provider is faced with the following two-stage stochastic optimization model, in which it seeks to maximize the total expected profit:
subject to:
Constraint (2) represents a conservation law in Stage 1 and establishes that the quantity of service k requested by user or device g on the ground to all controller UAVs cannot be less than the demand \(R_{gk}^1\), in Stage 1 (this allows us not only to meet the demand for Stage 1, but also to prepare for Stage 2).
Constraint (3) establishes that the quantity of service requests that the controller UAV u can receive in Stage 1 does not exceed its maximum capacity. Observe that constraint (2) must be verified, therefore, the total capacity of controller UAVs are such as to satisfy the demand of Stage 1 for services from all users and devices.
Constraint (4) states that, in Stage 1, the quantity of service k requests sent by the controller UAV u to all the pre-existing and additional UAVs is less than or equal to the quantity of service k requested by all users or devices on the ground to the controller UAV u.
Constraint (5) is a capacity constraint and it establishes that the requests of services that each pre-existing and additional UAV f, \(\forall f \in \mathcal {F}_3\), can receive in Stage 1 must not exceed the maximum allowed.
Constraint (6) is a budget constraint ([18, 25]) and it states that, in Stage 1, there is a budget limit, \(\overline{B}^1\), which represents the maximum available budget for adding new UAVs at the highest level of the network and additional capacities to the controller UAVs.
Constraint (7) states that, in Stage 1, it is possible to add a limited additional capacity to each controller UAV.
Finally, constraints (8) are non-negative constraints in Stage 1.
The last term of the objective function (1) represents the expected value of the profit of service provider in the second stage. Assuming a discrete probability distribution, the expected profit of service provider in the second stage can be written as follows:
namely the weighted sum of the profits in each disaster scenario in Stage 2, \(P^2(X^{1,2},X^{2,2},X^{3,2}, {\Gamma ^2,}\omega )\), where the weights are the probabilities \(p_{\omega }\) that the scenario \(\omega\) occurs, for each \(\omega \in \Omega\). This profit depends, in addition to the stochastic parameters and variables previously introduced, also on the unmet demand of services requested on the ground, for which the service provider is forced to pay a penalty cost, i.e.,
The profit in Stage 2, in turn, is determined as the solution to the following second stage stochastic maximization problem:
subject to constraints:
Constraint (12) ensures that the quantity of service k requested by user or device g on the ground to all controller UAVs in Stage 2 under scenario \(\omega\) does not exceed the demand \(R_{gk}^{2\omega }\) minus the amount of services executed and not provided at Stage 1, that is the quantity of services prepared at Stage 1 to supply at Stage 2. Constraints (13)-(18) have the same meaning as the constraints (3)-(8), defined for the first stage, except for the budget constraint (16) which is more complete than the equivalent constraint (6) because it includes the costs for additional UAVs and additional capacities of both Stages 1 and 2 and, hence, the sum of budgets (\(\overline{B}^1\) and \(\overline{B}^{2\omega }\)). Therefore, it is also possible to use part of the unspent budget in Stage 1, during the disastrous event in Stage 2. However, the parameters introduced in Stage 2 differ from the equivalent ones defined in Stage 1, because they are affected by the information about the severity of the disaster event.
Following [26, 27] and the standard stochastic programming theory (see [28, 29]), the first- and second-stage problems can be solved together through a unique maximization problem, that is:
3 Variational Formulation
In this section, we derive a variational inequality formulation ([30]) of the stochastic maximization problem described in the previous section. We assume that all the involved cost functions are continuously differentiable and convex. We have the following result.
Theorem 1
A vector \(\chi ^*\in \mathbb {K}\) is a solution to the stochastic maximization problem (19);(2)-(8);(12)-(18) if and only if it satisfies the variational inequality: Find \(\chi ^*=(\chi ^{1*},\chi ^{2*})\in \mathbb {K}\) such that:
where
is the feasible set of the problem.
The previous theorem allows us to utilize the well-known variational inequality theory to obtain the optimal solutions of the problem (see [30]).
We can put variational inequality (20) into standard form, that is: find a vector \(X^*\in \mathcal {K}\) such that:
where \(\mathcal {K}\) is a closed, convex set. In this regard, we set \(X=\chi\), \(F(X)=(F^i(X))_{i=1,\dots ,8}\) and \(\mathcal {K}\equiv \mathbb {K}\), where:
We note that, under the imposed assumptions for cost functions, F(X) is a continuous function. Moreover, the feasible set, \(\mathcal {K}\), is compact. Hence, from the classical theory of variational inequalities (see [31]), a solution to variational inequality (20) or, equivalently to variational inequality (22), is guaranteed to exist. Moreover, a uniqueness result is ensured since the strictly monotonicity of function F(X) is guaranteed by the following:
Theorem 2
Let all the involved time and cost functions strictly convex in their variables. Then, the vector function F(X), defined by (23), is strictly monotone, i.e.,
Proof
Let \(X_1=(X_1^{1,1},X^{2,1}_1,X^{3,1}_1,\Gamma _1^1,X^{1,2}_1,X^{2,2}_1,X^{3,2}_1,\Gamma _{1}^2)\in \mathcal {K}\) and \(X_2=(X_2^{1,1},X^{2,1}_2,\) \(X^{3,1}_2,\Gamma _2^1,X^{1,2}_2,X^{2,2}_2,X^{3,2}_2,\Gamma _{2}^2)\in \mathcal {K}\) be two admissible vectors such that \(X_1\ne X_2\). We evaluate the quantity:
Since all the involved cost functions are strictly convex, each of the eight terms in (24) are strictly greater than 0, if \(X_1\ne X_2\). Hence, F(X) is a strictly monotone function.
4 Lagrange Theory and Alternative Variational Inequality Formulation
In this section, we investigate the Lagrange theory associated with variational inequality (20) (see, for instance, [32,33,34,35,36] for an application of the Lagrange theory to various network models). Particularly, due to the non-linearity budget constraints (6) and (16), we relax such constraints into the objective function by associating to them the Lagrange multipliers. We also derive an alternative variational inequality to the one in (20) that we will use in the next section, devoted to numerical examples.
Let \(\lambda ^1\in \mathbb {R}_+\) be the Lagrange multiplier associated with budget constraint (6). Likewise, let \(\lambda ^{2\omega }\in \mathbb {R}_+\) be the Lagrange multipliers associated with budget constraints (16), for each scenario \(\omega \in \Omega\). Let \(\lambda ^2=(\lambda ^{2\omega })_{\omega \in \Omega }\in \mathbb {R}_+^{|\Omega |}\).
We set:
and we define:
Let us consider the Lagrange function:
Variational inequality (20) is equivalent to the following problem
This equivalence is justified because we have
We recall that all the involved functions are convex and continuously differentiable. Moreover, since \(\mathcal {K}\) is convex and the Slater condition is satisfied, if \(X^{*}\) is a minimal solution to problem (28), there exist \(\lambda ^{1*}\in \mathbb {R}_+\) and \(\lambda ^{2*}\in \mathbb {R}_+^{|\Omega |}\), such that the vector \((X^{*},\lambda ^{1*},\lambda ^{2*})\) is a saddle point of the Lagrange function (27):
and
The right-hand side of (29) ensures that \(X^*\) is a minimal point of the function \(\mathcal {L}(X,\lambda ^{1*},\lambda ^{2*})\). Hence, for all \(u,\ \tilde{f},\ k\) and for all \(\omega \in \Omega\), we have:
together with conditions (30).
Equations (31)-(34) and conditions (30) allow us to provide an alternative variational inequality formulation to the one in (20).
Theorem 3
Variational inequality (20) is equivalent to the following one: Determine \((X^*,\lambda ^{1*},\lambda ^{2*})\in \mathbb {K}\) such that
where
5 Numerical Examples
In this section, we provide some numerical examples to illustrate some key aspects of the model.
5.1 Network Topology and Data
As depicted in Fig. 2, we consider three users and devices on the ground (\(G=3\)) requiring a 5G service (\(K=1\)), two controller UAVs (\(U=2\)) which receive the service requests (from users and devices) and send them to the two UAVs belonging to the fleet at the highest level of the network (\(\hat{F}_1=2\)) where services are performed. We also analyze the possibility to add the capacity at each controller UAV and to add a new UAV to the fleet (\(\tilde{F}_2=1\)).
Moreover, in these examples we assume that 2 different scenarios (see [37] and [27]), \(\omega _1=1\) and \(\omega _2=2\), can occur with different probabilities:
-
Case 1: \(p_{1}=0.8\) and \(p_2=0.2\);
-
Case 2: \(p_{1}=0.2\) and \(p_2=0.8\);
-
Case 3: \(p_{1}=1.0\) and \(p_2=0.0\).
Note that in Case 1 it is estimated that the first scenario has a higher probability of occurrence than the second scenario; vice versa in Case 2. Finally, in Case 3 it is estimated that only the first scenario can occur (indeed the probability that the second scenario occurs is zero).
We suppose the following general expressions for the cost functions, for all \(g,u,\hat{f},\tilde{f}\):
Observe that, as mentioned above, no constant term appears in these functions. Therefore, if there is no flow in a link of the network (from a user or device on the ground to a controller UAV or from a controller UAV to a UAV in the upper tier fleet), the cost of transmission in that link is zero. Similarly, if a UAV does not execute any service, the execution cost for that UAV is zero. The same for the cost needed for additional UAVs and capacities.
For the numerical setting, we consider the coefficients for the cost functions involved in the formulation as in Table 3. Moreover, we select the parameters as follows:
We have made the choice of this data assuming that the second user or device on the ground (\(g=2\)) is in a central position and is closest to both the controller UAVs, indeed, the coefficients of its transmission cost functions (\(a_{gu}\) and \(b_{gu}\)) are the smallest: \(a_{21}=b_{21}=a_{22}=b_{22}=1\). The first user or device on the ground (\(g=1\)) is closer to the first controller UAV, and it is the furthest away from the second one (\(a_{11}=b_{11}=3,\;a_{12}=b_{12}=4\)). On the contrary, the third user or device (\(g=3\)) is closer to the controller UAV \(u=2\) than to the controller UAV \(u=1\) (\(a_{31}=4,\;b_{31}=3,\;a_{32}=b_{32}=2\)). In a similar way, we are assuming that the second UAV belonging to the fleet, \(\hat{f}=\hat{2}\) is geographically positioned in such a way that it is central and, hence, it is the closest one to both the controller UAVs, indeed, the coefficients of its transmission cost functions (\(d_{uf}\) and \(e_{uf}\)) are the smallest: \(d_{1\hat{2}}=e_{1\hat{2}}=d_{2\hat{2}}=e_{2\hat{2}}=1\). The first UAV belonging to the fleet, \(\hat{f}=\hat{1}\), is closer to the first controller UAV than to the second (\(d_{1\hat{1}}=e_{1\hat{1}}=2,\;d_{2\hat{1}}=e_{2\hat{1}}=3\)). Moreover, we assume that the additional UAV \(\tilde{f}=\tilde{1}\) can be positioned to be equally distant from both the controller UAVs (\(d_{1\tilde{1}}=e_{1\tilde{1}}=d_{2\tilde{1}}=e_{2\tilde{1}}=2\)). In this way we have represented the different geographical scenarios that can arise, and it is easy to understand how to represent and extend further real cases.
Since all the coefficients, \(g_{f}\) and \(h_f,\; \forall f\in \mathcal {F}_3\), are the same, in these numerical examples we are assuming that all the UAVs have the same unit execution cost but it is clear that this does not constitute a limit since it is sufficient to replace these coefficients with more appropriate ones.
Furthermore, all the costs, included the costs due to insert additional UAVs into the network and adding capacity to the controller UAVs are the same for both stages but we are assuming adding capacity to the second controller UAV is slightly more expensive (because \(k_2=2\) while \(k_1=1\)).
Regarding the capacity limits, we suppose a difference only on the maximum execution capacity of the additional UAV, \(S_{\tilde{1}}=7\), that is greater than the maximum execution capacities of the pre-existing ones (\(S_{\hat{1}}=S_{\hat{2}}=4\)). Observe that the total demand in Stage 1, when no disastrous event occurs, is equal to 6; while in Stage 2, that is when a disastrous event occurs, in both scenarios \(\omega _1\) and \(\omega _2\), the total demand \(\displaystyle \sum _{g=1}^G\sum _{u=1}^UR_{gu}^{2\omega }\) is greater than that of the first stage. Particularly, in the first scenario there is a total demand equal to 16, while in the second scenario it is equal to 10. Therefore, Scenario 1 is more severe than Scenario 2. Moreover, we are assuming that in Scenario 1 the increase in demand is not constant, but actually decreases in one user or device and increases consistently in another user or device. On the other hand, in Scenario 2, the increase in demand is fairly uniform for all users and devices on the ground. Such data are in keeping with reality as disaster scenarios can be of different types: some have a zeroing of requests in one area and simultaneously an increase in other areas while other scenarios have a uniform increase in all areas.
We suppose two different situations: in the Situation 1 we assume that the maximum available budgets (for additional UAVs at the highest level of the network and the additional capacities at the controller UAVs) are the same for each stage and for each scenario (that is \(\overline{B}^1=\overline{B}^{21}=\overline{B}^{22}=200\)); instead, in Situation 2 we assume different maximum available budgets. Particularly, we presume that the budget for the first stage (when no disaster event occurs) is less than the available budgets for both the scenarios, \(\omega _1\) and \(\omega _2\), of the second stage and that the budget available for \(\omega _1\), the most serious scenario, is greater than that for \(\omega _2\) (\(\overline{B}^1=50,\overline{B}^{21}=200,\overline{B}^{22}=120\)).
5.2 Optimal Solutions
For each of the 6 numerical examples (three cases and two situations), in Tables 4, 5 and 6 are reported the values of the optimal solutions for Stage 1, Stage 2 - Scenario 1 and Stage 2 - Scenario 2, respectively. We obtain these optimal solutions by solving the Variational Inequality (35) and are computed through the Euler Method (see [38] for a detailed description) using the MATLAB program on an HP laptop with an AMD compute cores 2C+3G processor, 8 GB RAM.
The main optimal solutions are also reported in Fig. 3, in which we have indicated the use (or not) of the additional UAV, graphing the sum of the optimal variables relating to the flows toward the additional UAV (\(\displaystyle \sum _{u=1}^U x_{u\tilde{f}k}\)) in Fig. 3a and the optimal variables relating to the additional capacities of each controller UAV (\(\gamma _u\)) in Fig. 3b.
5.3 Analysis of the Results
We highlight that in Stage 1 of the first situation, Case 1 (second column of Table 4), 7 more services are performed (6 was the total demand requested and 13 was the one executed) which are provided at Stage 2. To execute such services, both the additional capacities and additional UAVs are used at the first stage, while, additional capacity of only one controller UAV is used at the first scenario of Stage 2 (whose severity is greater), and no additional UAVs and additional capacities are used at Stage 2, Scenario 2.
When the maximum budget for additional UAVs and additional capacities is tight (Situation 2) we get a different optimal solution where no additional UAVs and additional capacities are used in Stage 1; while they are used (for all the UAVs) in Scenario 1 of Stage 2 (see Table 5 and Fig. 3).
We also emphasize that, unlike Case 1 (Situation 1), in Case 2, since the probability of occurrence of the most serious disaster scenario is lower (0.2 rather than 0.8), in Stage 1 no additional UAVs and capacities are used while additional UAVs are used in both scenarios of Stage 2 and the additional capacities of both the controller UAVs in the first scenario of Stage 2 are used.
Moreover, in Scenario 2 of Case 2, it is convenient to use the additional UAVs in Situation 1 (in which we have the necessary budget), instead, in Situation 2 we cannot use the additional UAVs because the available budget is not enough to add new UAVs (see columns 3 and 6 of Table 6).
Case 3 is very similar to Case 1, but the second scenario cannot happen (as \(p_2 = 0\)), therefore, all optimal solutions related to the second scenario are null.
Finally, we observe that, unlike Cases 1 and 3 of Situation 1, in the other cases and situations, in the first stage fewer more services are performed (only 2 more services); this is explained because either there are not enough budgets (Situation 2) or the disastrous scenario, in which the demand is lower, is more likely to occur (Case 2).
5.3.1 Additional Discussion On the Results
From the analysis of the obtained optimal solutions, it is possible to deduce some key findings that we will summarize here.
The results reveal that the management of both the preparation and the response phases has a significant impact when a disaster scenario occurs. In this paper we firstly analyzed the effects that scenarios of different severity could cause. Particularly, we assume that the severity of each scenario is represented by an unexpected and sudden increase in demand which can be more or less intense. Therefore, we supposed that in both the considered disaster scenarios the service requests increase, and that the first scenario is more severe, since the total quantity of requests in \(\omega =1\) increases dramatically, especially is some areas (while in other areas the demand is zeroed), meanwhile, in the second scenario, requests for services increase fairly equally for all areas. So, even if with only two scenarios, we represented the most common types of demand changes.
We also underline that each of these scenarios can occur with different probabilities. Therefore, in our numerical examples we have analyzed three different cases, in which such occurrence probabilities vary. Particularly, in Case 1 we supposed that the more severe scenario has a higher occurrence probability than the other scenario; on the contrary, in Case 2 we assumed that the scenario with higher probability is the softer one. Finally, in Case 3 we analyzed the situation in which only a scenario can occur.
The main aim of the model proposed in this paper is to optimize the management of the pre-existing and additional resources. Therefore, in our illustrative examples we investigated the behavior of the service provider (that seeks to maximize his total profit and to minimize the expected loss related to a possible unmet demand), paying particular attention to the possibility that he has to use or not additional resources. More specifically, we analyzed the obtained optimal results, observing if it is convenient, for the service provider, to use additional resources that means to put into flight new UAVs and, hence, to add them to the network and/or to further increase the capabilities of pre-existing controller UAVs (at the first and/or second stage), making possible to satisfy a greater number of requests.
Another fundamental aspect, especially in a disaster situation, not to be underestimated, is represented not only by the costs needed to add such resources, namely the costs due to add new UAVs at the highest level of the network and the costs due to add capacity to the controller UAVs, but also by the maximum available budget for additional resources: there exists a budget constraint which states that the overall cost for additional UAVs at the highest level of the network and additional capacities at the controller UAVs must not exceed the budget limit, \(\overline{B}^1\) or \(\overline{B}^{2\omega }\) (in the first or second stage, respectively). Therefore, in our illustrative numerical experimentation we also analyzed some managerial insights obtained by not only the aforementioned cases but also by two different situations in which the maximum budget limits (\(\overline{B}^1\) and \(\overline{B}^{2\omega }\)) vary.
Therefore, from the overall analysis of the examples, cases and situations that we have examined, and of the optimal solutions we found and reported above, we can deduce some key aspects that can provide support in managerial decisions.
We observed that during the preparation phase (Stage 1), that is when no disastrous scenario has yet occurred, it may be convenient to use additional resources or not. Indeed, in the case in which the scenario with the highest probability is the least serious one (Case 2), it is not necessary to use the additional resources and, hence, there is no cost to add UAVs or further capacities. On the contrary, it is more convenient to use both the additional UAVs and the additional capacities, when the most serious scenario (the one with the highest total demands) has a high probability of occurrence (cases 1 and 3), in order to satisfy the greatest number of requests.
It is important to point out that, as mentioned above, the budget limit assumes a fundamental role, in fact it should be noted that when the available budget is limited, the additional resources cannot be used (see Situation 2, Stage 1). Similarly, when the second scenario \(\omega =2\) is the one with higher probability (Case 2), if the budget is enough, it is convenient to use additional UAVs. Indeed in Situation 1 (\(\overline{B}^{22}=200\)) they are used, while in Situation 2 (\(\overline{B}^{22}=120\)) they are not used. Therefore, it is clear that our model can also be used for simulations on the budgets by the service providers to estimate and establish if increasing the budget is suitable or not.
Further considerations can be expressed by comparing the results of the different stages and cases. When the most serious scenario has a high probability of occurrence (cases 1 and 3) and when the budget is enough, we have already observed that both the additional types of resources are used in Stage 1. In this situation, in stage 2, under scenario 1 it is convenient to use the additional UAVs, but to add capacity to just one of the controller UAVs while under scenario 2 it is not necessary to use additional resources (because the provider has fewer requests). If, instead, we are in Situation 2, where the budget was not sufficient (and therefore no additional resources were used in Stage 1), we obtain that in Stage 2, under Scenario 1 (the most serious), it is convenient to use all the additional resources, as is also if the less serious scenario is more likely (Case 2). Therefore, it is easy to guess that the proposed model is also useful for investigating the consequences of scenarios and their probability of occurrence, in the different stages, with a particular reference to the suitable use of additional resources.
6 Conclusions
In this paper, we proposed a two-stage stochastic optimization model describing the provision of services in case of a disaster scenarios. The uncertainty of a such events, their severity and the unpreparedness of service providers could make challenging, expensive and time consuming the provision of services in case of disaster. Hence, to mitigate the consequences of a disaster advent, it is of fundamental importance to provide mathematical models that can allow service providers to make predictions on possible disastrous scenarios and act in such a way as to minimize the loss associated with a possible unsatisfied demand. This challenges led us to the two-stage optimization model described in this paper, which aims to maximize the profits associated with the provision of 5G services and, simultaneously, minimize the expected loss associated with a sudden growth in request. A variational approach was used as a tool to obtain the optimal solution of some numerical examples. The obtained results show that not only the optimal distribution of flows, but also the optimal management of any additional resources assumes a main role, together with the maximum budget available for these additional resources and the different probabilities that disastrous scenarios (more or less serious) will occur. From the optimal solutions it emerges that the model turns out to be efficient, in case of prediction of one or more disastrous events (even different from each other), since it is able to help the services providers both in the preparation phase (Stage 1) and in the response phase (Stage 2). Indeed, it is possible to start preparing for the disastrous event even during Stage 1, always satisfying all constraints, including the nonlinear budget constraints. Summarizing the results obtained from the numerical examples, we can highlight the following key findings:
-
We have predisposed different scenarios able to represent the common situations that can occur in the event of a disaster: increase in requests in a fairly evenly distributed manner or movement of requests from one area to another;
-
We have conceived some cases in which the probabilities of occurrence of the scenarios vary;
-
We have simulated different situations in which the maximum budgets available for the costs due to add/use additional resources (additional UAVs and additional capacities) vary;
-
We have deduced the main features of the optimal behavior of service providers, regarding the convenience or otherwise on the use of additional resources. Such deductions provide us with some managerial insights and the results allow the service providers to carry out simulations and to make optimal decisions.
The model is very suitable to be applied to real-life situations, because all its components (variables, objective function and constraints, the cost functions) allow us to represent reality. Despite this, the difficulties we expect to face when applying the model to real-life situations are given by some computational aspects due to the large-scale instances and iterative computational times required to solve the problem. Therefore, in future works, another interesting research would be solving large-scale examples using real data and alternative computational methods to test the validity of our model. Furthermore, we are going to study and analyze a new heuristic approach and a new model with 3 stages.
This proposed model could also be useful for providing other services or things in emergency situations.
Data Availability
All data generated or analyzed during this study are included in this published article.
Change history
21 July 2022
Missing Open Access funding information has been added in the Funding Note.
References
Morgado A, Huq KMS, Mumtaz S, Rodriguez J (2018) A survey of 5G technologies: regulatory, standardization and industrial perspectives. Digital Communications and Networks, Vo 4(2):87–97
Fendt A, Mannweiler C, Schmelz LC, Bauer B (2018) A formal optimization model for 5G mobile network slice resource allocation, 2018 IEEE 9th Annual Information Technology, Electronics and Mobile Communication Conference (IEMCON), 101–106. https://doi.org/10.1109/IEMCON.2018.8615049
Feng Z, Qiu C, Feng Z, Wei Z, Li W, Zhang P (2015) An effective approach to 5G: Wireless network virtualization. IEEE Commun Mag 53(12):53–59
Li S, Da Xu L, Zhao S (2018) 5G Internet of Things: A survey. J Ind Inf Integr 10:1–9
5G-PPP, ERTICO, EFFRA, EUTC, NEM & Networld2020 ETP (2016) 5G Empowering Vertical Industries
Barat A, Haus G, Ludovico LA, Pagani E, Nello Scarabottolo N (2019) 5G technology for augmented and virtual reality in education. Proceedings of the International Conference on Education and New Developments, 512–516
Grasso C, Raftopoulos R, Schembra G (2021) Deep Q-Learning for Job Offloading Orchestration in a Fleet of MEC UAVs in 5G Environments, IEEE 7th International Conference on Network Softwarization (NetSoft), 186-190
Tang Y, Dananjayan S, Hou C, Guo Q, Luo S, He Y (2020) A survey on the 5G network and its impact on agriculture: Challenges and opportunities. Comput Electron Agric 180:105895
World Organization Health (2021) WHO Coronavirus (COVID-19) Dashboard, https://covid19.who.int/
Colajanni G, Daniele P, Biazzo V (2021) An optimization model for managing reagents and swab testing during the COVID-19 pandemic. In: Cerulli R., Dell’Amico M., Guerriero F., Pacciarelli D., Sforza A. (eds) Optimization and Decision Science. AIRO Springer Series, vol 7. Springer, Cham. https://doi.org/10.1007/978-3-030-86841-3_6
Daniele P, Sciacca D (2021) A dynamic supply chain network for PPE during COVID-19 pandemic. J Appl Numer Optim 3(2):403–424
Feldmann A, Gasser O, Lichtblau F, Pujol E, Poese I, Dietzel C, Wagner D, Wichtlhuber M, Tapiador J, Vallina-Rodriguez N, Hohlfeld O, Smaragdakis G (2021) Implications of the COVID-19 pandemic on the internet traffic. In Broadband Coverage in Germany; 15th ITG-Symposium, 1-5. VDE
Zheng F, Khan NA, Hussain S (2020) The COVID 19 pandemic and digital higher education: Exploring the impact of proactive personality on social capital through internet self-efficacy and online interaction quality. Child Youth Serv Rev 119:105694
Siriwardhana Y, De Alwis C, Gur G, Ylianttila M, Liyanage M (2020) The flight against the COVID-19 pandemic with 5G technologies. IEEE Eng Manage Rev 48(3):72–84
Otto A, Agatz N, Campbell J, Golden B, Pesch E (2018) Optimization approaches for civil applications of unmanned aerial vehicles (UAVs) or aerial drones: A survey. Networks 72(4):411–458
Grasso C, Schembra G (2019) A Fleet of MEC UAVs to Extend a 5G Network Slice for Video Monitoring with Low-Latency Constraints. J Sens Actuator Netw 8:3
Cappello GM, Colajanni G, Daniele P, Galluccio L, Grasso C, Schembra G, Scrimali L (2021) Optimizing FANET Lifetime for 5G Network Slice Provisioning. To appear
Cappello GM, Colajanni G, Daniele P, Sciacca D (2021) A constrained optimization model for the provision of services in a 5G network with multi-level cybersecurity investments. To appear
Colajanni G, Daniele P, Galluccio L, Grasso C, Schembra G (2021) Service-chain placement optimization in 5G FANET-based network edge. To appear
Colajanni G, Sciacca D (2021) An Optimization model for services requests management in a 5G network architecture. In: Masone A., Dal Sasso V., Morandi V. (eds) Optimization and Data Science: Trends and Applications. AIRO Springer Series, vol 6. Springer, Cham. https://doi.org/10.1007/978-3-030-86286-2_7
Chung SH, Sah B, Lee J (2020) Optimization for drone and drone-truck combined operations: A review of the state of the art and future directions. Comput Oper Res 123:105004
Faiz TI, Vogiatzis C (2020) Two-echelon vehicle and UAV routing for post-disaster humanitarian operations with uncertain demand.ArXiv:2001.06456
Zhao N, Sheng M, Tang J (2019) UAV-assisted emergency networks in disasters. IEEE Wirel Commun 26(1):45–51
Dighriri M, Saeed Dayem Alfoudi A, Myoung Lee G, Baker T, Pereira R (2018) Resource allocation scheme in 5G network slices. 32nd International Conference on Advanced Information Networking and Applications Workshops (WAINA), 275-280
Colajanni G, Daniele P, Sciacca D (2020) A projected dynamic system associated with a cybersecurity investment model with budget constraints and fixed demands. J. Nonlinear Var Anal 4(1):45-61. https://doi.org/10.23952/jnva.4.2020.1.05
Daniele P, Sciacca D (2021) A two-stage variational inequality formulation for a game theory network model for hospitalization in critic scenarios. In: Amorosi, L., Dell’Olmo, P., Lari, I. (eds) Optimization in Artificial Intelligence and Data Sciences: ODS, First Hybrid Conference, Rome, Italy, September 14-17, 2021. AIRO Springer Series, vol 8. Springer, Cham. To appear
Salarpour M, Nagurney A (2021) A multicountry, multicommodity stochastic game theory network model of competition for medical supplies inspired by the COVID-19 pandemic. Int J Prod Econ 236:108074
Birge J, Louveaux F (1997) Introduction to Stochastic Programming. Springer, New York, NY
Shapiro A, Dentcheva D, Ruszczynski A (2009) Lectures on Stochastic Programming: Modeling and Theory. Society for Industrial and Applied Mathematics, Philadelphia, Pennsylvania
Nagurney A (1993) Network Economics: A Variational Inequality Approach. Kluwer Academic Publishers, Boston, Massachusetts
Kinderlehrer D, Stampacchia G (1980) An introduction to variational inequalities and their applications. Academic Press, New York
Caruso V, Daniele P (2018) A network model for minimizing the total organ transplant costs. Eur J Oper Res 266(2):652–662
Colajanni G, Daniele P, Giuffr S, Nagurney A (2018) Cybersecurity investments with nonlinear budget constraints and conservation laws: variational equilibrium, marginal expected utilities, and Lagrange multipliers. Int Trans Oper Res 25:1443–1464
Daniele P, Maugeri A, Nagurney A (2017) Cybersecurity investments with nonlinear budget constraints: Analysis of the marginal expected utilities. In N. J. Daras, & T. M. Rassias (Eds.), Operations research, engineering, and cyber security. In Springer optimization and its applications: 113, 117-134
Daniele P, Sciacca D (2021) An optimization model for the management of green areas. Int Trans Oper Res 28:3094–3116
Nagurney A, Salarpour M, Daniele P (2019) An integrated financial and logistical game theory model for humanitarian organizations with purchasing costs, multiple freight service providers, and budget, capacity, and demand constraints. Int J Prod Econ 212:212–226
Nagurney A, Salarpour M, Dong J, Nagurney LS (2020) A stochastic disaster relief game theory network model. In SN Operations Research Forum (Vol. 1, No. 2, pp. 1-33). Springer International Publishing
Dupuis P, Nagurney A (1993) Dynamical systems and variational inequalities. Ann Oper Res 44:9–42
Acknowledgements
The research was supported by the research project “Programma ricerca di ateneo UNICT 2020-22 linea 2-OMNIA” of Catania and by the GNAMPA project Progetto di Ricerca 2020 - “Problemi di equilibrio: metodi variazionali e teoria dei giochi”. These supports are acknowledged.
Funding
Open access funding provided by Università degli Studi di Milano within the CRUI-CARE Agreement.
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of Interest
On behalf of all authors, the corresponding author states that there is no conflict of interest.
Additional information
Publisher’s Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
This article is part of the Topical Collection on Dynamics of Disasters
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made. The images or other third party material in this article are included in the article's Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article's Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Colajanni, G., Daniele, P. & Sciacca, D. On the Provision of Services With UAVs in Disaster Scenarios: A Two-Stage Stochastic Approach. Oper. Res. Forum 3, 18 (2022). https://doi.org/10.1007/s43069-022-00127-x
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s43069-022-00127-x