Abstract
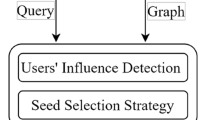
In destination-dependent utility-based schemes, data forwarding is stimulated when a node presents next-hop fitness to destination higher than the current custodian of a message. However, these schemes do not enforce any mechanism to ensure cooperative participation, and altruistic behavior is taken as an assumption, instead. Therefore, a wide range of existing schemes known to provide effective performance may fail in pragmatic settings afflicted with selfish participants. In this paper, we propose a novel cooperation framework which is deployed as an overlay to assist data forwarding utility-based schemes. Effectiveness of our framework is evaluated through intensive simulations with PRoPHET and MARS routing.
Similar content being viewed by others
References
Grasic, S.; Davies, E.; Lindgren, A.; Doria, A. In: Proceedings of the 6th ACM workshop on Challenged networks (ACM, 2011), pp. 27–30
Nelson, S.C.; Bakht, M.; Kravets, R. In: INFOCOM 2009 (IEEE, 2009), pp. 846–854
Balasubramanian A., Levine B.N., Venkataramani A.: Replication routing in DTNs: a resource allocation approach. Netw. IEEE/ACM Trans. 18(2), 596 (2010)
Vahdat, A.; Becker, D., et al.: Epidemic routing for partially connected ad hoc networks. Tech. rep., Technical Report CS-200006, Duke University (2000)
Cerf, V.; Burleigh, S.; Hooke, A.; Torgerson, L.; Durst, R.; Scott, K.; Fall, K.; Weiss, H.: IRTF DTN Research Group 2(4), 6 (2007)
Yasmin, S.; Rais, R.N.B.; Qayyum, A. In: International Conference on Computer Communications and Networks (IEEE, August 7, 2014)
Elwhishi, A.; Ho, P.H. In: Global Telecommunications Conference, GLOBECOM (IEEE, 2009), pp. 1–7
Panagakis, A.; Vaios, A.; Stavrakakis, I. In: Communication Systems Software and Middleware, 2007. COMSWARE 2007. 2nd International Conference on (IEEE, 2007), pp. 1–6
Miao J., Hasan O., Mokhtar S.B., Brunie L., Yim K.: An investigation on the unwillingness of nodes to participate in mobile delay tolerant network routing. Int. J. Inf. Manag. 33(2), 252 (2013)
Zhu, H.; Lin, X.; Lu, R.; Fan, Y.; Shen, X.: SMART: a secure multilayer credit-based incentive scheme for delay-tolerant networks. Veh. Technol. IEEE Trans. 58(8), 4628 (2009)
Chen, B.B.; Chan, M.C. In: INFOCOM, 2010 Proceedings IEEE (IEEE, 2010), pp. 1–9
Liu G., Ji S., Cai Z.: Strengthen nodal cooperation for data dissemination in mobile social networks. Pers. Ubiquitous Comput. 18(8), 1797 (2014)
Lu R., Lin X., Zhu H., Shen X., Preiss B.: Pi: A practical incentive protocol for delay tolerant networks. Wirel. Commun. IEEE Trans. 9(4), 1483 (2010)
Mei A., Stefa J.: Give2Get: forwarding in social mobile wireless networks of selfish individuals. Dependable Secur. Comput. IEEE Trans. 9(4), 569 (2012)
Li N., Das S.K.: A trust-based framework for data forwarding in opportunistic networks. Ad Hoc Netw. 11(4), 1497 (2013)
Dini G., Lo Duca A.: Towards a reputation-based routing protocol to contrast blackholes in a delay tolerant network. Ad Hoc Netw. 10(7), 1167 (2012)
Wei L., Zhu H., Cao Z., Shen X.S.: Ad-hoc, Mobile, and Wireless Networks, pp. 177–190. Springer, Berlin Heidelberg (1976)
Bigwood, G.; Henderson, T. In: Privacy, Security, Risk and Trust (PASSAT) and 2011 IEEE Third International Conference on Social Computing (SocialCom), 2011 IEEE Third International Conference on (IEEE, 2011), pp. 65–72
Marti, S.; Giuli, T.J.; Lai, K.; Baker, M. In: Proceedings of the 6th annual international conference on Mobile computing and networking (ACM, 2000), pp. 255–265
Li, F.; Wu, J. In: INFOCOM 2007. 26th IEEE International Conference on Computer Communications. IEEE (IEEE, 2007), pp. 1946–1954
Nagrath, P.; Aneja, S.; Gupta, N.; Madria, S.: Wireless Networks, pp. 1–12 (2015)
Buttyán L., Dóra L., Félegyházi M., Vajda I.: Barter trade improves message delivery in opportunistic networks. Ad Hoc Netw. 8(1), 1 (2010)
Shevade, U.; Song, H.H.; Qiu, L.; Zhang, Y. In: Network Protocols, 2008. ICNP 2008. IEEE International Conference on (IEEE, 2008), pp. 238–247
Fishbein M.: Mathematical Models in Marketing, pp. 87–88. Springer, Berlin Heidelberg (1976)
Ganeriwal S., Balzano L.K., Srivastava M.B.: Reputation-based framework for high integrity sensor networks. ACM Trans. Sensor Netw. (TOSN) 4(3), 15 (2008)
Jsang, A.; Ismail, R. In: In Proceedings of the 15th Bled Electronic Commerce Conference (Citeseer, 2002)
Liu Y., Li K., Jin Y., Zhang Y., Qu W.: A novel reputation computation model based on subjective logic for mobile ad hoc networks. Future Gener. Comput. Syst. 27(5), 547 (2011)
Shafer G. et al.: A mathematical theory of evidence, vol. 1. Princeton university press, Princeton (1976)
Musolesi M., Mascolo C.: Car: context-aware adaptive routing for delay-tolerant mobile networks. Mobile Comput. IEEE Trans. 8(2), 246 (2009)
Burgess, J.; Gallagher, B.; Jensen, D.; Levine, B.N. In: INFOCOM, vol. 6 (2006), vol. 6, pp. 1–11
Karlof C., Wagner D.: Secure routing in wireless sensor networks: Attacks and countermeasures. Ad hoc Netw. 1(2), 293 (2003)
Fall, K. In: Proceedings of the 2003 conference on Applications, technologies, architectures, and protocols for computer communications (ACM, 2003), pp. 27–34
Liu, A.; Ning, P. In: Information Processing in Sensor Networks, 2008. IPSN’08. International Conference on (IEEE, 2008), pp. 245–256
Shamir A.: Advances in cryptology, pp. 47–53. Springer, Berlin Heidelberg (1976)
Spyropoulos, T.; Psounis, K.; Raghavendra, C.S. In: Proceedings of the 2005 ACM SIGCOMM workshop on Delay-tolerant networking (ACM, 2005), pp. 252–259
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Yasmin, S., Qayyum, A. & Rais, R.N.B. Cooperation in Opportunistic Networks: An Overlay Approach for Destination-Dependent Utility-Based Schemes. Arab J Sci Eng 42, 467–482 (2017). https://doi.org/10.1007/s13369-016-2253-9
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s13369-016-2253-9