Abstract
The present study is an analysis of a Czech political corruption network known as the Rath affair reconstructed with publicly available data. We argue that for the study of criminal networks it is fruitful to follow a multiplex approach, i.e., to distinguish several interdependent network dimensions and study how they are interrelated. Relational elements in corruption are identified, and we propose three dimensions that are essential for understanding the Rath network: pre-existing ties (e.g., marriage or co-membership of the same party), resource transfer (e.g., bribing), and collaboration (e.g., communication). The aim of the study was threefold. We aimed to examine if the network exhibits the core/periphery structure, to investigate the multiplex structure of the network by assessing the overlap of the main dimensions of the network, and to determine the central and multiplex actors while considering the differentiation of centrality according to the three network dimensions. The core/periphery model appears to have a perfect fit to the aggregated network, leading to a four-block adjacency matrix. Studying the frequency of ties in these blocks shows that collaboration ties are present in all the blocks, while resource transfer ties are mainly located between the core and periphery, and pre-existing ties are rare generally. We also identify central actors, none of which are strategically positioned, occupying more visible positions instead. The majority of actors display strong multiplexity in the composition of their own ties. In the conclusion the potential usefulness of multiplex descriptive measures and of mixed methods approaches, implications of our results for trust incriminal networks, and potential merits of analytical sociology approach are discussed.
Similar content being viewed by others
Avoid common mistakes on your manuscript.
In the last decade, there has been a growing interest in covert and criminal networks. Particular attention has been paid to terrorist, smuggling, and trafficking networks (Morselli 2009; van der Hulst 2011). In comparison, corruption networks have gained far less attention in research and have been generally understudied. However, the consequences of corruption in terms of security, trust, welfare and justice warrant a closer look to understand how corruption is structured and organized.
In this study, we examine a case of a corruption network with a specific focus on the structure of the network, multiplexity of relations (i.e., the existence of several different types of ties between actors), and centrality of actors. Specifically, we applied social network analysis (SNA) to a case of political corruption in the Czech Republic, known as the Rath affair, reconstructed with publicly available data, resulting in a small network of 11 persons, who were involved in large scale abuse of EU subsidies, bribery, and manipulation of public contracts. We analyze the overall structure of the network, the multiplexity of ties in this structure, and the centrality of actors. We investigate how certain micro-level features (overlapping of multiple types of ties and activity of individual actors) bring about macro-level outcomes, in this case the overall structure of the network (Coleman 1990; Hedström 2005).
Corruption
Corruption is generally defined as an “abuse of public power for private gain” (Funderburk 2012; Silitonga et al. 2016; Uslaner 2008). While this general definition of corruption does not entail any particularly relational or interactional features, corruption as a phenomenon consists of a wide range of activities and some of them are intrinsically relational. For instance, bribery and blackmailing are based on a transfer of various resources, which are either offered or demanded in return for a desired service. Another form of corruption involving transfer or exchange of resources is the so-called kickback, which is a term for illegal provision of a public contract, which is “kicked”, i.e., boosted, to provide a share for the corrupted official. Nepotism and cronyism are based on pre-existing relationships with relatives or friends respectively, who are installed into influential or well-paid positions despite their incompetence. Although these are just the most common forms of corruption, there are more activities which could be labelled as such (for a detailed description, see Silitonga et al. 2016). What is shared by all the mentioned forms of corruption, however, is that these activities take place in human interactions and relationships.
Although some corruption involves just the exchange between two individuals in cases of abusing a single opportunity (Granovetter 2004; Uslaner 2008), there is also a type of corruption that disproportionately enriches a small number of rich and influential actors from the public as well as private sector. This form of corruption, labeled as grand corruption, involves far greater flows of financial resources or their material and immaterial equivalents, giving rise to severe envy, mistrust and perception of social inequalities (Uslaner 2008).
The danger of grand corruption lies in its potential for sophisticated collaboration and coordination among multiple actors, who can act in an organized manner to maximize their profit and minimize their risks. Such conspiracies of multiple individuals acting in concert to reach illegal goals are cases of organized crime (Albanese and Reichel 2014; Paoli 2014). This cooperation creates a network of transfers and relationships among these actors. To such structures of joint activities, social network analysis can be applied as an analytical tool apt to capture the underlying organizational principles (van der Hulst 2009). Here, we focus on the overall structure of the network and the way it is constituted by multiplex relations and by the activity of the individual actors involved.
Core/Periphery structure
Research on criminalFootnote 1 networks has generated a considerable body of knowledge (Carrington 2011; Gerdes 2015b; Morselli 2009; 2014a, b; Oliver et al. 2014). One network concept is especially relevant in the context of criminal networks: the so-called core/periphery structure (Borgatti and Everett 1999). Networks displaying this structure are composed of two sets of nodes. The core is a densely interconnected group of nodes, whereas the periphery is a set of nodes with ties to the core, but few or no ties within the periphery. This structure has been described in a variety of empirical networks, such as economic networks and international trade, formal organizations, scientific citations or even animal collectives (ibid.). Borgatti and Everett (1999) developed a formal way of examining the core/periphery structure, by trying to find the optimal partition of the node set reflecting the division in core and periphery. This optimal partition is then compared to the ideal core/periphery structured network with the same number of nodes and their similarity yields a measure of goodness of fit.
In criminal settings, features indicative of the presence of the core/periphery structure have been described in a number of cases, such as several Spanish cocaine trafficking networks (Gimenéz Salinas-Framis 2011), the Turkish terrorist organization Ergenekon (Demiroz and Kapucu 2012), price fixing conspiracies in electrical industry (Baker and Faulkner 1993), and the Watergate conspiracy (Faulkner and Cheney 2013). Most of these studies did not formally fit the core/periphery structure to the available data; an exception is the study of the inner circle of the Provisional Irish Republican Army (Stevenson and Crossley 2014). We follow a similar approach in modeling the network. In the case of corruption networks, a core/periphery structure resembles the structure of patron/client relationships, which are often thought to be the basis for political corruption with mutually beneficial quid-pro-quo exchanges between politicians (patrons – the core) and their supporters (clients – the periphery; della Porta and Vanucci 2012; Funderburk 2012; Granovetter 2004). Consequently, the first research question is to what extent does the corruption network in this study resemble a core/periphery structure?
Multiplexity in criminal networks
Social relationships are often based on more than one dimension, for instance, two individuals may be friends and co-workers simultaneously. MultiplexFootnote 2 networks describe multiple relationships among the same set of actors (Hanneman and Riddle 2005). The analysis of multiplex instead of simplexFootnote 3 networks provides a more realistic and more detailed picture of social reality and in turn deepens the understanding of the network under scrutiny (Bright et al. 2015; Faulkner and Cheney 2013; Gerdes 2015a; Hamill et al. 2008; Kivelä et al. 2014). Despite the attention to multiplexity in criminal networks given in the literature, starting already quite some time ago (Ianni 1972; Krohn et al. 1988), in many studies the relational information has been aggregated to a single network, without specifying the content of the relation, or of the exchanges taking place. The reason is the paucity of available information, so that the researcher already has made progress when there is evidence for at least some relationships between pairs of actors. However, multiplexity is a key component of the dyadic level of analysis in the network perspective (Robins 2009). Organized crime is in principle an embedded and multiplex phenomenon, created by individuals nested within multiple social relations held together by information, activities, obligations, and exchanges (Papachristos and Smith 2014). Distinguishing between these relational contents is essential for understanding criminal activities and how networks play a role in their organization. Papachristos and Smith (2014) suggest that multiplexity of relations is an important factor in illegal settings where it compensates for the lack of formal institutions. Therefore, when going more deeply in the explanation and analysis of the social organization of crime, a differentiation between different types of relations is important.
There are some published examples of multiplex criminal network analyses. Most prominently, a study by Krebs (2002) of the 9/11 terrorist attacks followed the example of overt organization analysis in mapping different types of ties, resulting in four types or dimensions; trust, tasks, money & resources, and strategy & goals. Another example is Faulkner and Cheney (2013) study of the Watergate conspiracy, where they distinguish five separate dimensions, emphasizing negative ties of enmity among actors, which could have been a stronger cause of eventual collapse of the conspiracy than an external disruption. In a study by Everton (2012) on the Indonesian terrorist network of Noordin Mohammad Top, trust (friendship, kinship or shared affiliation) and operational ties (communication, financing, common training) were distinguished. Papachristos and Smith (2014; 2016) analyzed a large network of criminal and legitimate actors surrounding the infamous gangster Al Capone, resulting in three types of relations; criminal, personal (e.g., kinship) and legal (e.g., non-criminal cooperation). Bright et al. (2015) base their analysis on the concept of tangible (e.g., money or material) and intangible (e.g., skills or information) resource transfers among co-offenders in the case of drug smuggling. They also underline the importance of multiplexity by warning for potentially misleading results of simplex analysis of aggregated networks as this may lead to over- or underestimation of prominence of individual actors. For example, an actor may be central in one dimension but peripheral in others, incorrectly making him seem unimportant in the overall aggregated simplex network. Finally, a review by Gerdes (2015a) described ten possible dimensions; direct operational links, logistic links, planning links, financial links, training links, ideological links, family, friendship, enmity and uncertain links.
Based on the previous research described above, we propose three dimensions. For each dimension, we provide a brief description, the content of ties, and a justification for its inclusion.
-
1)
Pre-existing ties. There has been a great emphasis on the importance of trust within covert networks (Erickson 1981; Krebs 2002; Milward and Raab 2006; Oliver et al. 2014; Robins 2009; van der Hulst 2011). By trust, we mean the expectation of reciprocation and of not defecting, that is, not breaking the concealment, in a covert environment (further see Campana and Varese 2013; von Lampe and Ole Johansen 2004). Pre-existing ties, meaning ties established before the criminal act itself, may be crucial sources of trust, which makes their analysis important (Morselli and Roy 2008). Specifically, pre-existing ties may take a form of kinship relations, friendships, or relations based on shared ideology or shared affiliation to the same organizations or institutions. Therefore, they are to a large extent overt, unlike the other types of ties presented below. In our case, pre-existing ties include marriage, being university classmates, and mutual membership in a board of directors of a company. However, it is important to acknowledge that the presence of such a tie does not automatically create trust between the two connected actors, and a pre-existing tie may only potentially facilitate a creation of a tie of another type; but we have no other information about trust between these individuals. The question is, to what extent was the criminal cooperation backed up by pre-existing ties. Ties in this dimension capture the notion of Krebs’ (2002) and Everton’s (2012) dimension of trust, Papachristos and Smith (2014; Smith and Papachristos 2016) personal ties and partly legal ties and Gerdes’ (2015a) links of training, ideology, family and friendship.
-
2)
Resource transfer. Resource transfer or exchange (if reciprocated) is the main component of numerous forms of organized criminal activity. It includes the transfer of illegal profits obtained. Resources to be transferred may be both material and immaterial, tangible (e.g., equipment) as well as intangible (permissions, skills; see Bright et al. 2015). This dimension covers the logistic, training, planning and financial links proposed by Gerdes (2015a). In our case, the main transferred resources are money in the form of bribes or kickbacks for politicians and manipulated contracts for businessmen.
-
3)
Collaboration. Ties in this dimension can be broadly defined as purposeful interactions, involving communication that can be both direct (face-to-face) and indirect (e.g., phone calls, e-mails). This dimension also includes collaboration on tasks or co-appearance at the same time in relevant places, which is consistent with the task and strategy and goals networks in the concept of Krebs (2002), operational ties as defined by Everton (2012), and the criminal dimension of Papachristos and Smith (2014; 2016).Footnote 4
For each of these three dimensions there could be negative ties, as in some cases, animosity or even outright enmity may exist among actors (Faulkner and Cheney 2013; Gerdes 2015a). These dimensions also allow tie weights to be taken into account. They also allow the specification of the direction of ties as directed or undirected based on the source of the data and the accuracy and detail of their recording. This framework is sufficiently general and flexible, which makes it potentially applicable to other cases of corruption networks. As will be mentioned below, in the analysis presented in this paper, we do not consider negative, directed, or weighted ties.
We examine different ties to assess the multiplexity in the corruption networks in this study. In a multiplex network, some dimensions may tend to overlap with other dimensions and this may also differ between the core and the periphery. Hence, the second research question is how do different types of ties overlap in the aggregated network?
Central actors in criminal networks
The analysis and identification of central actors is a crucial task for explanation of the structure of the criminal network, as it is the individual level where the intentionality (e.g., intention to remain covert or to maximize profit) resides (Robins 2009). Organizing activities of central actors have been related to the organization of the whole group, fostering its ability to adapt to a changing environment and to profit or survive in the face of disruption (see e.g., Bright et al. 2012; Morselli 2009; Oliver et al. 2014). Centrality is a concept which captures to which extent the actor is connected to many others, or connects many others, and thus may be influential for the organization of the entire group. In the core/periphery structure, central actors are those in the core. Centrality of actors in the network can be measured in different ways (Freeman 1978). Two of the most commonly used measures are degree and betweenness.Footnote 5 Whereas degree is a simple count of all ties of a node, betweenness captures the number of shortest paths between other pairs of nodes on which the actor stands, enabling to bridge different segments of the network. Actors with high betweenness, so-called brokers, are considered crucial in keeping the network connected (Morselli and Roy 2008). Degree and betweenness express the concept of centrality in quite distinct ways, and they do not necessarily correlate. It has been shown that in some cases leaders in criminal networks may hide in the background by having a low degree, as having high number of ties is easily detectible and thus vulnerable. By contrast, they compensate by having a brokerage position (a high betweenness score). Morselli (2010) calls this ‘strategic positioning’. In addition, there may be three more types of actors depending on their degree and betweenness. Actors with low values for both degree and betweenness are marginal in the network. Actors with a low betweenness but a high degree are more visible and therefore more at the risk of detection. Finally, actors with high values on both indices are highly central and as such visible. Even though they have a high betweenness, this potential advantage may be outweighed by the risks of high degree (ibid.).
The concept of centrality is more complicated when taking multiplexity into account. Battiston et al. (2014) point out that nodes may differ in terms of how dispersed their ties are between different dimensions of a multiplex network. They theorize three possible types of nodes in this regard. Focused nodes have ties in only one dimension and thus are unconnected in others. Multiplex nodes have ties spread evenly across all the dimensions. Lastly, mixed nodes have ties in multiple dimensions, yet their dispersion across them is uneven, that is, they have more ties in one dimension compared to other dimensions (ibid.).
We combine this approach with the strategic positioning introduced above. By doing so, we can identify central actors and take multiplexity of their ties into account. Some actors may be central in one dimension, but marginal in other dimensions, suggesting specialization in the network in a certain task, while being marginal in others (Bright et al. 2015). Other actors may occupy average or even marginal positions in terms of centrality in each dimension separately, but may be crucial by integrating different layers of the network into one single coherent whole due to multiplex spread of their ties.
Hence, the third research question is which actors are central in the corruption network and how do centralities of actors differ across network dimensions?
Case description - the Rath affair
For more information on this affair, see e. g. (both in Czech): http://www.lidovky.cz/infografika.aspx?grafika=korupcni-kauza-davida-ratha (Lidovky.cz 2016) or: http://zpravy.idnes.cz/soud-s-davidem-rathem-05r-/krimi.aspx?c=A130806_141944_krimi_klm(iDNES.cz 2013)
In this study we analyze a political corruption scandal from the Czech Republic. The analyzed case consists of actors involved in an affair surrounding a long-term controversial figure of Czech politics – David Rath,Footnote 7 a former minister of health, at the outbreak of this scandal a social democratic party (CSSD) deputy and governor of the Central Bohemia region. David Rath was arrested the 14th of May 2012 by anti-corruption police together with his close colleagues and two lovers, Petr Kott and Katerina Pancova, in the midst of being bribed. The main reasons for their arrest were embezzlement, kickbacks, abuse of EU subsidies, and manipulation of public contracts, mostly in the domain of hospital equipment and public estates reconstructions (e.g., chateaus or schools). As the investigation continued, it turned out that these three persons were not alone in their offences and another eight persons were arrested as well, mainly managers of firms involved in manipulated contracts or profiting on the abused subsidies. Together, these 11 actors were systematically cooperating on embezzlement, manipulation of contracts and abuse of EU subsidies and they mutually shared the profits of their action. The financial damage reached at least twenty million Czech crowns (almost one million Euros). Hence, this case matches the definition of grand corruption and organized crime presented above, as it entails both collaboration of a group of offenders and a large amount of transferred resources.
In order to alleviate otherwise severe problems of boundary definition in criminal networks, we adopted a nominalist approach (Borgatti et al. 2013, p. 33–34). The criterion for including an actor into the network is based on criminal justice circles (see Morselli 2009, p. 44–45). We define the criminal justice circle for the Rath affair as “being charged”, including as a node in the network everyone who was charged with any criminal act in connection to this affair. This resulted in the following eleven actors;
David Rath, − governor of the Central Bohemian Region and a deputy of the social democratic party (CSSD);
Petr Kott, Katerina Pancova (after marriage - Kottova) – a politician (CSSD) and his wife and the director of Kladno city hospital;
Pavel Drazdansky, Lucia Novanska, Martin Jires, Ivana Salacova, Tomas Mlady, Vaclav Kovanda, Jindrich Rehak, Jan Hajek – managers and representatives of various construction or medical equipment providing firms.
Methods
Data collection and coding
One of the most challenging tasks in research on covert networks is the collection of data (Morselli 2014b; van der Hulst 2009). Bright et al. (2012) compared five different data sources: offender databases, transcripts of physical or electronic surveillance, summaries of police interrogation, transcripts of court proceedings and online or print media. Apart from online or print media, most data sources are not publicly or freely accessible.
An objection against using online or print media is their lower validity, as they are always a secondary source of information dependent on the perspective and knowledge of the journalists, who produce it. This also limits researchers’ options to control their quality and credibility. Another possible pitfall of media-based data is the tendency of journalists to focus on what or who they deem to be interesting and, consequently, focusing their reports on specific persons, making the data derived from these reports centralized as a result. Nevertheless, if the reported information is sufficiently detailed and carefully processed, it may yield meaningful results (see e.g., Athey and Bouchard 2013; Bright et al. 2012; Krebs 2002; Milward and Raab 2006; Silitonga et al. 2016). However, it is important to keep the limitations of the data in mind when interpreting the results and drawing conclusions.
In our study, we rely on online and print media as a data source. We extracted the data from a Czech media database called Newton Media Search, searching for online or print articles containing the names of each pair of actors simultaneously (e.g., “David Rath” AND “Petr Kott” or “David Rath” AND “Lucia Novanska” and so on) and also for “kauza Rath”, which is the Czech name of the analyzed case. We then sorted out 20 most relevant articles for the whole case as well as for each pair of actors (based on the Newton Media Search criterion called relevance) from the period from 2011 to 2015 (i.e., from a year prior to the outbreak of the scandal), resulting in a total of 240 unique articles.Footnote 8 We have checked all these reports. In case there was a statement about a connection between any of the involved actors, we saved the source as well as the exact wording of the statement. After deleting multiplicities, for instance multiple mentions of Kott and Pancova being in an intimate relationship, we ended up with 49 records of ties between the actors, which is the total number of ties for all dimensions in the network.
Subsequently, we coded all ties into the three dimensions: pre-existing ties, resource transfer, and collaboration, based on their content. All coding was again conducted by a second, independent researcher. Only three ties were coded differently, which were then recoded based on mutual agreement between coders. Therefore, we consider the coding to be reliable.
Measures
Pre-existing ties are relations based on shared affiliations of actors (e.g. being members of the same party or of the directorial board of the same company) or their mutual involvement in a personal relation (e.g. being married or being university classmates). Resource transfer ties were derived from information about bribing, kickbacking or placing a manipulated contract between the actors. Collaboration ties were coded accordingly when two actors were reported to be meeting together, communicating with each other or cooperating on a certain task.
Because the pre-existing ties dimension is based on shared attributes or similarities between actors, this dimension is undirected by definition. Although ties in the resource transfer and collaboration dimensions can be thought of as directed, we decided to code these ties as undirected due to insufficient information about the direction of ties. Specifically, the data sources were rarely detailed enough to specify the direction of ties, for instance, who called whom or who encouraged a personal meeting with whom. Rather, these interactions are typically simply described as just happening, e.g. person A and person B met each other or were in contact with each other. Similarly, in some cases of resource transfer, it is possible to distinguish who bribes whom, but in other cases such as sharing profit from a manipulated contract, the direction is indistinguishable. The same reasoning leads to considering all ties as binary (i.e., absent or present) rather than weighted as detailed information about frequency of collaboration or volume of resource transfers is rarely, if ever, specified. Thus, all three dimensions are undirected and binary.
Analytic strategy
To obtain a first view of the network, the multiplexity is provisionally left out of consideration and these several dimensions are aggregated into a single simplex network. We aggregated the dimensions with the use of logical expression of union (Hanneman and Riddle 2005). This means that if there is a tie between two actors in at least one of the dimensions, then it exists in the aggregated network. This yields an aggregated network where ties represent any connection between the actors. This gives us a picture of the overall network structure. Subsequently, we decompose the aggregated network by looking at each dimension separately.
First, we describe all the three dimensions and the aggregated network by the number of participating (connected) nodes, number of ties, density, centralization, average degree and its standard deviation, average geodesic distance and diameter, using corresponding computations in the UCINET (Borgatti et al. 2002) software and the statnet (Handcock et al. 2003) package in R.
In order to answer the first research question concerning the core/periphery structure, we fitted the ideal core/periphery model to the data and compared its fit using the categorical core/periphery routine in the UCINET software package (Borgatti and Everett 1999). Put simply, this attempts to optimally partition nodes into two sets (i.e., core and periphery) and simultaneously uses (dis)similarity measures (e.g., correlation or Hamming distance) to show the goodness of fit of the empirical data to the ideal model, in which the core is a complete graph (a clique) and periphery is an empty graph. A good fit indicates that the observed network exhibits the core/periphery structure. We ran the routine with varying starting configurations in order to see if the resulting solution is robust.
To answer the second research question, about the multiplexity of ties, we analyzed overlapping ties between dimensions in two steps. First, we calculated similarities between the dimensions. For this purpose, we computed the Jaccard coefficients for each pair of dimensions, which is a ratio of ties being present in both compared networks to the number of ties present in at least one of them. This is 1 if the networks are identical and 0 if they have no ties in common. Second, we analyzed the overlap of ties in a similar way as Bright et al. (2015). We used the multiplexity coder function in the UCINET, which assigns different codes to each different combination of dimensions between each pair of actors. This allows us to see which dimensions overlap between which nodes.
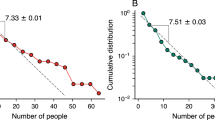
For the third research question, about centrality and multiplexity of the individual actors, we first computed the standard degree and betweenness centrality measures. Degree of a node is a simple count of all adjacent nodes. Betweenness of a node is the proportion of shortest paths between all other nodes that include the given node. In order to identify strategic positions, we also calculated means of both these measures. Following the same procedure as Morselli (2010) and Bright et al. (2015), we then deem nodes strategically positioned if their betweenness value is higher than the mean value and degree value lower than the average. Subsequently, we term actors with below average betweenness and above average degree as “visible”. Actors with values for both measures exceeding their mean are called “central”. Lastly, those with both values below the mean are labeled as “marginal”. In the second step, we computed the multiplex participation index (further see Battiston et al. 2014). Essentially, this index measures how ties of a node vary across different dimensions and is standardized with values ranging between 0 (absence of multiplexity with concentration of ties in one dimension) and 1 (perfect multiplexity with ties equally spread across all dimensions). If this range is divided into thirds, then the lower third values belong to uniplex or focused nodes, middle range values cover mixed nodes and the highest values reflect multiplex nodes (ibid.).
Visualization
As is usual in SNA, we use sociograms to visualize our network. The inclusion of multiplexity calls for some adjustments. We decided to adopt the visualization strategy for multiplex networks proposed by Kivelä et al. (2014). Their idea is to visualize the aggregated network first, save coordinates of the nodes in the aggregated network and then visualize each dimension separately with nodes anchored in these coordinates. This allows for easy visual comparisons between different dimensions and is less cluttered than visualizing all the dimensions in one graph with the use of different line colors or line types. Concerning the analysis of overlap, we decided to visualize the result using the well-known Venn diagram, which is suitable for capturing overlapping sets of objects (see e.g., Papachristos and Smith 2014).
We also present a permuted core/periphery matrix as a result of the model fitting. It is an adjacency matrix rearranged in such way that nodes belonging to the core are grouped together and nodes belonging to the periphery are also grouped together. These two groups are just visually distinguished by a dividing dashed line drawn in the matrix. For networks with small number of nodes, this is clear and offers the advantage to closely inspect particular ties or actors.
In order to display the strategic positioning, we also use a scatterplot of degree and betweenness with dashed lines representing the means of both these measures (Bright et al. 2015; Morselli 2010). This divides the graph into four parts corresponding to the “strategically positioned”, “visible”, “central” and “marginal” types of actors.
Results
Descriptive statistics
Table 1 shows descriptive statistics of all the three dimensions and the aggregated network (see also Figs. 1, 2, 3 and 4). Note the absence of average geodesic distance and diameter for the pre-existing ties network. Both measures are based on path lengths and connectivity of the network, but this particular network is disconnected and most of the shortest path lengths are undefined (or infinite) as a result, making it meaningless to include these calculations. This is the least dense and the least centralized dimension. It is also the only dimension in which some nodes do not participate (have no ties). There are five such nodes. The densest and most centralized dimension is collaboration. The high density reflects the small number of nodes, but the average degree indicates frequent activity of actors in this dimension. Centralization is high in the collaboration dimension, suggesting that all the activities were concentrated around a few influential actors. This makes the network effective in terms of cooperation due to good flow of information, yet vulnerable due to potential disintegration with removal of central actors. The resource transfer dimension is less dense and less centralized than collaboration. It has also longer geodesic distances on average. Nevertheless, all nodes are connected in this dimension, but due to lower average degree and longer distances, the flow of resources is less cohesive than collaboration. It is also worth mentioning that aggregating all the ties does not lead to dispersion or lesser centralization for the actors but even stronger centralization. Therefore, the network as a whole is neither polycentric (centralized around a few different locally central nodes) nor flat (with evenly spread centralities), which is consistent with findings from other studies (e.g., Varese 2012).
Core/Periphery
To answer our first research question about the core/periphery structure in the network, we fitted the ideal core/periphery matrix with the observed aggregated matrix and then looked at their correlation. This correlation was 1.0, showing that this network exhibits a perfect core/periphery structure. This is also shown in the permuted core/periphery matrix (Table 2). We see that indeed the core is fully connected, and the periphery is an empty graph. Further, no periphery member is connected to all core members. The core is composed of, first, the three politicians, Rath, Kott and Pancova, who were handing over all the corrupted contracts. Kott and Pancova are the only actors who are connected to all others in the network. The three were helped in manipulating these contracts by another member of the core – Novanska. The remaining two actors from the core are the most central managers, Drazdansky and Salacova, who were frequently connecting other actors from the core and from the periphery and cooperated on more than one manipulated contract with other members of the core (Denik.cz 2013; parlamentnilisty.cz 2013). The periphery consists of the remaining businessmen, who (unlike Drazdansky and Salacova) were involved in criminal activities only occasionally or ad hoc in order to exploit a single opportunity for kicking a contract or participating in a manipulated competition. This interpretation substantively validates this partition of the core and periphery as there is a clear dividing line between densely interconnected and active actors in the core and marginal actors in the periphery with only connections to the core. In corruption networks, politicians and officials who are in possession of demanded services and power, may become highly attractive and/or active and thus central. This is a mechanism of generalized social selection, where individuals with certain qualities tend to occupy adequate structural positions within the network (Robins 2009). This gives rise to the centralized network structure. In this case, the core has more members than the periphery, contrasting to what is mostly seen for core/periphery structures. We do not know if this is a true characteristic of this case; it is also possible that the periphery is larger and contains some more individuals, as yet undetected. It is also important to note that the perfect core/periphery structure in this case may be to some extent an artefact of the media-derived data. Specifically, there might be some ties missing among the peripheral actors in the network as a result of the “spotlight effect” (Smith and Papachristos 2016), that is, disproportionate attention of journalists towards the core actors of the case. However, because the core is so dense, the overall core-periphery would still be present, albeit not in perfect form, even if there were some ties present among the peripheral actors.
Multiplexity
As it can be seen in Table 3, the low values of Jaccard coefficients reveal that the three different dimensions do not overlap very much. The sparseness of pre-existing ties leads especially to low Jaccard coefficients for this network. In order to disentangle the overlap between dimensions, it is necessary to analyze the patterns of overlaps more closely. Results of this analysis are shown in the Table 4 and depicted in a Venn diagram (Fig. 5).
In total there are 55 dyads, pairs of actors, in the overall undirected network. These 55 dyads can be arranged into 8 different types based on their composition, that is, from empty null dyads to fully multiplex dyads containing a tie of each dimension and every possible combination in between (Fig. 5). 23 of all dyads are null, having no ties at all. The majority of the present ties are uniplex (20 out of 32, i.e., 62,5%), which corresponds with previous research findings (Bright et al. 2015; Papachristos and Smith 2014; Smith and Papachristos 2016). Even though there are only five ties overall in the pre-existing ties dimension, none of them is uniplex. This means that ties in this dimension are not functional by themselves, but rather serve as a basis or facilitation for ties in other dimensions, mostly (four of them) in the collaboration dimension.
On the contrary, collaboration was possible to be carried out mostly without a combination with any other type of tie. In seven dyads, it was also accompanied by transferred resources. Pure resource transfer without further cooperation or communication, and not combined with pre-existing ties, appeared in seven instances. Lastly, there is no fully multiplex dyad in the network. This together with the low number of pre-existing ties means that the dimensions of collaboration and resource transfer are vital to the functioning of the network as a whole, while the role of pre-existing ties is in reinforcing other relations and interactions.
Additional analyses
As an additional step, we combined the dimension overlaps with the core/periphery structure of the network. This shows which of the overlapping ties fall into the core, which into the periphery, and which cross between them. Table 4 shows all tie overlaps. First of all, the pre-existing ties are not exclusively located only in the core block – three of them are, but the remaining two are located in the core/periphery block. Although these ties link some of the important figures in the core, there is no evidence that these ties are exclusive to the most central actors. Specifically, some of the most central actors are not connected in this dimension (Novanska and Salacova) and other core members are, but there are also some peripheral actors participating in this dimension (Rehak and Mlady).
Collaboration ties are evenly spread across the network segments – exactly half of them are located within the core and the other half is a part of ties between core and periphery. However, this is not true for the dimension of resource transfer. Exactly two fifths of these ties (40%) are a part of relations between the core actors, whereas the remaining 60% of resource transfer is going on between core and periphery nodes. This further supports the theoretically expected notion of patron-client relationships (della Porta and Vanucci 2012; Funderburk 2012; Granovetter 2004), where patrons provide “favors” for clients in return for their support or resources. Therefore, even though we don’t have directionality of ties, we can say who is a patron and who is a client based on actors’ network position and their attributes. High density of collaboration among patrons in this regard may be explained as mutual attempts to strengthen their position and to protect themselves. It is also indicative of their organizing and coordinating efforts in terms of the activity of the whole group.
The overall core/periphery structure thus is built up from a dense collaboration within the core and a slightly sparser collaboration between the core and the periphery. The collaboration is cemented with the resource transfer between the members of the core and periphery, in accordance with the notion of patron-client relationships. While pre-existing ties reinforce other relations, they are not necessary for them – only a handful of resource transfer or collaboration ties were underlined by them. The multiplex overlap of collaboration and resource transfer is an important building block of the macro-structure.
Centrality measures
Table 5 shows the degree and betweenness of each actor in the aggregated network together with their multiplexity participation index. Surprisingly, Rath himself is not the most central actor in the overall network. The most central actors in terms of both degree and betweenness are the married couple Pancova and Kott, followed by Novanska. Kott and Pancova were behind all the manipulated contracts and bribes, which is reflected by their degree of 10. This means they have a tie in at least one dimension to every other actor in the network. Novanska was involved mainly because of her expertise in handling and corrupting contracts (Lidovky.cz 2014). The eponymous actor, Rath, was very well informed and consulted by Kott and Pancova, but this couple also took care of the majority of all the work (Lidovky.cz 2013). This probably also explains why they are more central and arguably also more important for integration of the group as a whole. Less central positions are held by managers and businessmen. This is quite logical, as they were mostly involved ad hoc for one specific task or contract. Furthermore, all the peripheral actors have a betweenness of zero, which is in fact a consequence of a perfect core/periphery structure.
The role of Rath begs the question whether he is strategically positioned within the network or not. As it turns out, there is neither a strategically positioned actor (with above average betweenness and below average degree) nor any actor close to being strategically positioned. The two centrality measures are highly correlated (r = .85), indicating that nodes are either central in both measures or not. This implies considerable visibility of central actors and thus also high exposure and the risk of detection.
The analysis of multiplexity of ties of each actor complements this picture. Overall, none of the actors is uniplex or focused. On the contrary, the majority of actors is multiplex as indicated by the multiplex participation index which exceeds the value of 0.66. On the one hand, with the highest values of this index, ties of Rath and Kott span across all dimensions and thus these actors bring the network together. On the other hand, Hajek and Jires are the least multiplex nodes. They are the only nodes with mixed ties and they also have low overall degree.
To gain further insight, we also combined the centrality measures with this multiplexity measure. Combinations of positions and multiplexity of nodes in the network are shown in Table 6. As we have already stated above, nodes are neither focused nor strategically positioned. The three multiplex and central nodes are Kott, Pancova and Novanska. They are the most active actors and furthermore, they are active across dimensions. Another set of three nodes are those, who are highly visible (high degree) and multiplex. This set consists of the remaining actors from the core ̶ Rath, Drazdansky and Salacova, although Salacova’s multiplex participation index is borderline (= 0.67). The last set of nodes is composed of the five marginal actors from the periphery of the network, who are either multiplex or mixed in terms of their multiplexity. In general, the centrality measures further confirm the fact that the network is core/periphery structured with the core consisting of politicians and officials, and the periphery of business people. All the central actors exhibit a strong tendency towards multiplexity, yet none of them exhibits tendencies towards the security of strategic positioning (Fig. 6).
Discussion
One question arising from our analysis is related to the theoretical discussion about the importance of trust in organized crime and covert networks. While the dimension of pre-existing ties − which in the literature is supposed to be the basis for trust − underlies and reinforces other types of ties, in the Rath case it seems very sparse, and dissimilar to other dimensions. Thus, our findings suggest that this criminal network operated without being firmly based on pre-existing ties, which contradicts results or assumptions of other researchers (e.g., Erickson 1981; Krebs 2002; van der Hulst 2011; Battiston et al. 2014). Which other bases for trust are there in the absence of pre-existing ties? Campana and Varese (2013) mention, for example, third party enforcement, cutting of options to defect, taking hostages, or threat and potential use of violence. For cases like the one studied here, the influence of third parties and cutting of the options by knowing about illegal deeds of others come to mind as ways to enforce cooperation and to prevent defection. Alternatively, von Lampe and Ole Johansen (2004) show cases where there is no fundamental need for trust at all in order to cooperate in criminal networks and defection is considered as a real possibility. Such cases may be for example purely risking the cooperation in adverse conditions with no feasible alternatives, or just accepting the possibility of others defecting as a natural or even thrilling part of the criminal activity. One especially important base for trust is worth mentioning in the light of other findings of our study. Smith and Papachristos (2016) argued that it is in fact the overlapping of multiple types of ties which builds trust and reduces uncertainty among the offenders in the network by rooting the relation in multiple bases. So in cases where pre-existing ties are not extensive, overlapping of resource transfer and collaboration may possibly be a mechanism compensating for the lack of pre-existing ties or other trust-enhancing mechanisms. If two actors engage in a lot of common activities, they may lose a lot by defecting in one of them. However, these modes of cooperation as well as the role of trust itself need to be further empirically investigated.
Another question arises from the results about the core/periphery structure of the network. Why did these persons act in a way that made their interactions so centralized and frequent, even though this was dangerous as it made the network vulnerable to the disruption in the core? From the network point of view, none of the actors tried to reduce the risk by seeking a strategic position, that is, by minimizing redundant connections. Of course, it is highly problematic to assume that actors themselves actually think about their activities in network terms, but they are still able to reflect upon their actions and tell whether they are not “taking it too far”. One possible explanation for this may be their reliance on their elite membership status (Demiroz and Kapucu 2012) such as being an official or a politician (for instance, Rath had the deputy immunityFootnote 9). This elite membership status in turn led actors to foster a belief and a strong confidence that they might not be arrested or even investigated at all (ihned.cz 2013). The core-periphery structure has an important implication for the disruption of such corruption networks. While actors in the core may be easier to detect, it is necessary to capture all the members of the core in order to effectively incapacitate the network, because all the members of the core are structurally equivalent and thus a single removed actor may be quickly replaced by another one. However, such network interventions should always take the shortcomings of the data into account. For example, prior to the intervention, the results obtained from one data source should ideally be triangulated with data obtained from other sources.
An interesting point connected to the “visible” actors is the fact that it allowed the police investigators and law enforcement representatives to take the advantage and make two crucial steps in the investigation – arresting Rath red-handed while taking a bribe, and later turning Salacova to become a star witness and subsequently provide critical evidence in the trial (ihned.cz 2013). We suppose this was enabled by the highly visible positioning of these two actors within the network. Because of their high degree, the role of Rath was easily traceable and Salacova could provide essential information about other actors in the network.
Conclusion
The goal of this study of a Czech political corruption network was to understand its structure by focusing on its characteristics as a multiplex network, distinguishing the three network dimensions of collaboration, resource transfer, and prior existing ties. Specifically, we aimed at answering three interconnected research questions – whether the network has a core/periphery structure, how the multiplex dimensions overlap in its structure, and which actors are central in the network. First, the aggregated network exhibits a perfect core/periphery structure with all the involved politicians located within the core, and businessmen in the periphery. Second, ties in the collaboration dimension are evenly split between the core block and core-periphery block, while resource transfer ties are mostly located between core and periphery. The dimension of pre-existing ties is very sparse and all of the pre-existing ties are combined with at least one of the other dimensions. Most of the ties are either collaboration or resource transfer, not both; not a single tie covers all three dimensions. Last, there is a clear distinction between prominent and marginal actors, but none of the more prominent actors occupies a strategic position in the sense of trying to hide by minimizing redundant connections. A vast majority of actors are multiplex in terms of spread of their ties across multiple dimensions.
We reviewed previous studies which employed the notion of multiplexity in covert settings. The findings of these studies together with ours show that the multiplex point of view may reveal important information. However, this gives rise to the question why there are not more studies of criminal networks highlighting multiplexity. This may be on the one hand due to difficulties of data availability and data validity. In the context of criminal networks, it is much more difficult to distinguish several network dimensions, because it is already so difficult just to determine if there is a tie or not in the first place (Gerdes 2015a). Most research about criminal networks is data-driven (Bright et al. 2012; Carrington 2011), and if the available data do not allow to specify different dimensions of interaction, the multiplex analysis is simply impossible to be carried out. The other reason may be a lack of suitable methods for description of multiple dimensions simultaneously – while conceptually and computationally more elaborated network analysis methods such as Exponential Random Graph Models (Robins et al. 2007) or Stochastic Actor-oriented Models (Snijders et al. 2010) have their extensions to multiplex data, simple descriptive measures such as centrality or cohesion measures for multiplex networks are in their “infancy” (Kivelä et al. 2014). And since the field of covert and criminal network analysis is mostly based on these more simple measures (probably because of unfamiliarity with statistical models as well as theoretical interest in network description; see Campana 2016), the possibility to include the aspect of multiplexity into the analysis might have been overlooked. We believe that the multiplex participation index of Battiston et al. (2014) and the dimensions overlap analysis are two of such potentially fruitful measures for description of multiplex networks.
An evident difficulty for our approach is data quality and reliability, as data on covert networks are in principle impossible to collect by standard means of observation or questionnaires. Thus, a researcher in this area is left to rely upon other sources of data, which may vary in their availability and validity (Bright et al. 2012). We have used publicly available open-source data from media. Clearly, data obtained from this source suffer from problems with validity and reliability. Therefore, the results should be taken with a grain of salt, as there may be some information missing. As was already pointed out above, such missing information may to some extent alter the results. In order to make the most of the available information, it is necessary to process the data carefully. We performed a content analysis with pre-specified coding categories. Content analysis not only fulfils requirements for careful data processing with its reliability check (see also Stevenson and Crossley 2014), van der Hulst (2009) also recommends content analysis as a suitable complement to SNA in criminal networks research, because it allows taking a more detailed look at the data and thus gaining more solid understanding of the studied case and its context and make the interpretation more valid (further see e.g., Campana and Varese 2012; Natarajan 2006). We complemented our quantitative findings with qualitative insights based on our content analysis. From this point, one possible extension for this research could be to incorporate qualitative methods even more with a fully mixed-methods design. Qualitative analysis allows to derive the meaning from the network or as Stevenson and Crossley (2014) aptly expressed it – if network analysis captures the structure, then qualitative methods complement it by capturing the agency.
Related to the discussion of proper methods for the analysis of multiplex criminal networks is the issue of theory-building to surpass the lack of feasible theoretical explanations in the field (Carrington 2011; van der Hulst 2011). The case presented in this study was analyzed with mechanism-based explanations in mind. This can be elaborated in further research. Mechanism-based explanations have been pioneered within analytical sociology (Hedström 2005; Hedström and Bearman 2011) and this analytical approach to the explanation of organized crime may be of good use to criminology. The mechanism approach seeks to explain a social phenomenon by identifying a constellation of entities and activities, typically actors and their actions, that are linked to one another in such a way that they regularly bring about the type of phenomenon in question (Hedström 2005, p. 2). There is an evident synergy between this approach and SNA, as they both are concerned with actors and their relations. Furthermore, analytical sociology explicitly relies on actor-oriented explanations (ibid.), which counterbalances the overemphasis on network topology in the analysis of criminal networks (Robins 2009). A synthesis of these approaches may help the field of criminal networks studies both in theorizing as well as in modelling. This study shows that looking at mechanisms such as multiplex overlap of ties is an important factor in explaining the structure of criminal networks and may help to advance our understanding of corruption.
Notes
Several different terms can be used for labelling this type of networks such as dark networks (Milward and Raab 2006), illicit networks (Bouchard and Amirault 2013), criminal networks (Morselli 2009, 2014a) or covert networks (Oliver et al. 2014; Stevenson and Crossley 2014). We use the term criminal here as it is clear and relates to the organized crime.
Multiplex networks are sometimes referred to as multivariate, multidimensional or multirelational, which are different from multilevel networks or multilayer networks.
For traditional networks with just one relation among nodes, the terms simplex, monoplex, or uniplex may be used.
In order to distinguish between the dimensions of collaboration and resource transfer, we consider an interaction to be a tie in the resource transfer dimension if it involves any transfer of resources. In order to be a tie in the dimension of collaboration, the interaction has to include any sign of collaboration different from a transfer of resources.
For more in depth introduction to SNA and its methods, see for example a recent textbook by Borgatti et al. (2013).
Czech names usually contain letters with diacritics such as „á“, „š“or „č“. In order to be consistent with the visualizations, which are made with a software package not supporting such letters, we do not include them in the text.
The total number of articles searched this way was 1120 (20 articles for 55 pairs of actors and 20 articles for the case as a whole), but due to overlap between the articles, some of the articles were found repeatedly. For example, a review article on the case contained “kauza Rath” and it also contained the names of each of the 11 actors and thus it appeared in results for the search for each pair (55 times) and in the search for the whole case (once). Hence, the number of unique papers is 240.
In the Czech Republic, deputies are protected by the law from being arrested or sentenced unless they are caught immediately after committing a crime.
References
Albanese JS, Reichel PL (eds) (2014) Transnational organized crime: an overview from six continents. SAGE Publications, Inc., Los Angeles
Athey NC, Bouchard M (2013) The BALCO scandal: the social structure of a steroid distribution network. Global Crime 14(2/3):216–237. https://doi.org/10.1080/17440572.2013.790312
Baker WE, Faulkner RR (1993) The social Organization of Conspiracy: illegal networks in the heavy electrical equipment industry. Am Sociol Rev 58(6):837–860
Battiston F, Nicosia V, Latora V (2014) Structural measures for multiplex networks. Phys Rev E 89(032804). https://doi.org/10.1103/PhysRevE.89.032804
Borgatti SP, Everett MG (1999) Models of core/periphery structures. Soc Networks 21(4):375–395. https://doi.org/10.1016/S0378-8733(99)00019-2
Borgatti SP, Everett MG, Freeman LC (2002) UCINET 6 for windows: software for social network analysis. Analytic Technologies, Harvard
Borgatti, S. P., Everett, M. G., & Johnson, J. C. (2013). Analyzing social networks. SAGE publications
Bouchard M, Amirault J (2013) Advances in research on illicit networks. Global crime. Retrieved from http://www.tandfonline.com/doi/abs/10.1080/17440572.2013.801316
Bright D, Hughes C, Chalmers J (2012) Illuminating dark networks: a social network analysis of an Australian drug trafficking syndicate. Crime Law Soc Chang 57(2):151–176. https://doi.org/10.1007/s10611-011-9336-z
Bright DA, Greenhill C, Ritter A, Morselli C (2015) Networks within networks: using multiple link types to examine network structure and identify key actors in a drug trafficking operation. Global Crime 16(3):219–237. https://doi.org/10.1080/17440572.2015.1039164
Campana P (2016) Explaining criminal networks: strategies and potential pitfalls. Methodological Innovations 9:1–10. https://doi.org/10.1177/2059799115622748
Campana P, Varese F (2012) Listening to the wire: criteria and techniques for the quantitative analysis of phone intercepts. Trends Organized Crime 15(1):13–30. https://doi.org/10.1007/s12117-011-9131-3
Campana P, Varese F (2013) Cooperation in criminal organizations: kinship and violence as credible commitments. Ration Soc 25(3):263–289. https://doi.org/10.1177/1043463113481202
Carrington PJ (2011) Crime and Social Network Analysis. In: The SAGE Handbook of Social Network Analysis ,vol 2011, pp 236–255
Coleman J (1990) Foundations of social theory. Belnap Press, Cambridge
Demiroz F, Kapucu N (2012) Anatomy of a dark network: the case of the Turkish Ergenekon terrorist organization. Trends Organized Crime 15(4):271–295. https://doi.org/10.1007/s12117-012-9151-7
Denik.cz. (2013) Kauza Rath: Stavební manažer Kovanda popřel úplatek 2,8 milionu. Retrieved November 29, 2016, From http://www.denik.cz/z_domova/soud-dokonci-vypovedi-11-obzalovanych-v-kauze-davida-ratha-20130829.html
iDNES.cz. (2013) Tlačenice, špitání s právníky, čtení obžaloby. Začal soud s Rathem - iDNES.cz. Retrieved November 29, 2016, From http://zpravy.idnes.cz/soud-s-davidem-rathem-05r-/krimi.aspx?c=A130806_141944_krimi_klm
Erickson BH (1981) Secret societies and social structure. Soc Forces 60(1):188–210
Everton SF (2012) Disrupting dark networks. Cambridge: Cambridge University Press
Faulkner RR, Cheney ER (2013) The multiplexity of political conspiracy: illegal networks and the collapse of Watergate. Global Crime 14(2–3):197–215. https://doi.org/10.1080/17440572.2013.790313
Freeman LC (1978) Centrality in social networks conceptual clarification. Soc Networks 1(3):215–239. https://doi.org/10.1016/0378-8733(78)90021-7
Funderburk C (ed) (2012) Political Corruption in Comparative Perspective: Sources, Status and Prospects (new edition edition). Routledge, Burlington
Gerdes LM (2015a) Dark dimensions: classifying relationships among clandestine actors. In: Illuminating dark networks: the study of clandestine groups and organizations. Cambridge University Press, Cambridge, pp 19–38
Gerdes LM (2015b) Illuminating dark networks: the study of clandestine groups and organizations. Cambridge University Press, Cambridge
Gimenéz Salinas-Framis A (2011) Illegal networks or criminal organizations: power, roles and facilitators in four cocaine trafficikng structures. Universidad Autonóma de Madrid
Granovetter M (2004) The Social Construction of Corruption. Deprtment of Sociology, Stanford University. Retrieved from https://iis-db.stanford.edu/evnts/4117/The_Social_Construction_of_Corruption_Oct04.pdf
Hamill TJ, Deckro RF, Chrissis JW, Mills RF (2008) Analysis of Layered Networks. IOSphere,pp 27–33
Handcock MS, Hunter DR, Butts CT, Goodreau SM, Morris M (2003) statnet: Software tools for the Statistical Modeling of Network Data. Retrieved from http://statnetproject.org
Hanneman R, Riddle M (2005) Introduction to Social Network Methods. Retrieved April 3, 2016, from http://faculty.ucr.edu/~hanneman/nettext/
Hedström P (2005) Dissecting the social: on the principles of analytical sociology, 1st edn. Cambridge University Press, Cambridge
Hedström P, Bearman P (eds) (2011) The Oxford Handbook of Analytical Sociology (1 edition). Oxford. Oxford University Press, New York
van der Hulst RC (2009) Introduction to social network analysis (SNA) as an investigative tool. Trends Organized Crime 12(2):101–121. https://doi.org/10.1007/s12117-008-9057-6
van der Hulst RC (2011) Terrorist networks: the threat of connectivity. In: The SAGE handbook of social network analysis, pp 256–270
Ianni FAJ (1972) A family business: kinship and social control in organized crime. Russell Sage Foundation, New York
ihned.cz. (2013) Bradáčová, Pancová, Kott, Řehák. Podívejte se, kdo je kdo v Rathově korupční kauze. Retrieved November 29, 2016, From http://domaci.ihned.cz/c1-59638040-kdo-je-kdo-v-rathove-kauze
Kivelä M, Arenas A, Barthelemy M, Gleeson JP, Moreno Y, Porter MA (2014) Multilayer networks. J Complex Networks. https://doi.org/10.1093/comnet/cnu016
Krebs V (2002) Uncloaking terrorist networks. First Monday, 7(4). Retrieved from http://firstmonday.org/ojs/index.php/fm/article/view/941
Krohn MD, Massey JL, Zielinski M (1988) Role overlap, network multiplexity, and adolescent deviant behavior. Soc Psychol Q 51(4):346–356
von Lampe K, Ole Johansen P (2004) Organized crime and trust: on the conceptualization and empirical relevance of trust in the context of criminal networks. Global Crime 6(2):159–184. https://doi.org/10.1080/17440570500096734
Lidovky.cz. (2013) Jak se uplácelo v kauze Rath. Obžaloba odhaluje zločineckou symbiózu | Domov. Retrieved November 29, 2016, From http://www.lidovky.cz/jak-se-uplacelo-v-kauze-rath-obzaloba-odhalila-zlocineckou-symbiozu-115-/zpravy-domov.aspx?c=A130417_161021_ln_domov_ogo
Lidovky.cz. (2014) Obžalovaná v kauze Rath mění advokáta. Jako jediná dosud nevypovídala | Domov. Retrieved November 29, 2016, From http://www.lidovky.cz/novanska-v-kauze-rath-meni-advokata-jako-jedina-dosud-nevypovidala-1d1-/zpravy-domov.aspx?c=A140911_155036_ln_domov_spa
Lidovky.cz. (2016) Infografiky - Lidovky.cz. Retrieved November 29, 2016, From http://www.lidovky.cz/infografika.aspx?grafika=korupcni-kauza-davida-ratha
Milward HB, Raab J (2006) Dark networks as organizational problems: elements of a theory. Int Public Manag J 9(3):333–360. https://doi.org/10.1080/10967490600899747
Morselli C (2009) Inside Criminal Networks (Vol. 8). Springer New York, New York
Morselli C (2010) Assessing vulnerable and strategic positions in a criminal network. J Contemp Crim Just 26(4):382–392. https://doi.org/10.1177/1043986210377105
Morselli C (2014a) Crime and networks. Routledge, New York
Morselli, C. (2014b). Introduction. In Crime and Networks (pp. 1–9). Routledge
Morselli C, Roy J (2008) Brokerage qualifications in ringing operations. Criminology 46(1):71–98. https://doi.org/10.1111/j.1745-9125.2008.00103.x
Natarajan M (2006) Understanding the structure of a large heroin distribution network: a quantitative analysis of qualitative data. J Quant Criminol 22(2):171–192. https://doi.org/10.1007/s10940-006-9007-x
Oliver K, Crossley N, Everett MG, Edwards G, Koskinen J (2014) Covert networks: structures, processes and types. The Mitchell Center for Social Network Analysis working paper. Retrieved from http://www.socialsciences.manchester.ac.uk/medialibrary/research/mitchell/covertnetworks/wp/working_paper1.pdf
parlamentnilisty.cz. (2013) Drážďanský: Cítím se nevinen, výpověď Salačové je účelová. Retrieved November 29, 2016, From http://www.parlamentnilisty.cz/arena/monitor/Drazdansky-Citim-se-nevinen-vypoved-Salacove-je-ucelova-283474?beta=error
Paoli L (ed) (2014) The Oxford handbook of organized crime, 1st edn. Oxford University Press, Oxford
Papachristos AV, Smith C (2014) The embedded and multiplex nature of al Capone. In: Crime and networks. Routledge, New York, pp 97–115
della Porta D, Vanucci A (2012) The hidden order of corruption: an institutional approach. Farnham: Ashgate. Retrieved from https://www.routledge.com/The-Hidden-Order-of-Corruption-An-Institutional-Approach/Porta-Vannucci/p/book/9780754678991
Robins G (2009) Understanding individual behaviors within covert networks: the interplay of individual qualities, psychological predispositions, and network effects. Trends Organized Crime 12(2):166–187. https://doi.org/10.1007/s12117-008-9059-4
Robins G, Pattison P, Kalish Y, Lusher D (2007) An introduction to exponential random graph (p*) models for social networks. Soc Networks 29(2):173–191. https://doi.org/10.1016/j.socnet.2006.08.002
Silitonga MS, Anthonio G, Heyse L, Wittek R (2016) Institutional change and corruption of public leaders: a social capital perspective on Indonesia. In: Decentralization and governance in Indonesia. Springer, Berlin, pp 233–258
Smith CM, Papachristos AV (2016) Trust thy crooked neighbor Multiplexity in Chicago organized crime networks. Am Sociol Rev 81(4):617–643. https://doi.org/10.1177/0003122416650149
Snijders TAB, van de Bunt GG, Steglich CEG (2010) Introduction to stochastic actor-based models for network dynamics. Soc Networks 32(1):44–60. https://doi.org/10.1016/j.socnet.2009.02.004
Stevenson R, Crossley N (2014) Change in covert social movement networks: the ‘inner circle’ of the provisional Irish republican Army. Soc Mov Stud 13(1):70–91. https://doi.org/10.1080/14742837.2013.832622
Uslaner EM (2008) Corruption, inequality, and the rule of law. Cambridge University Press, Cambridge
Varese F (2012) The Structure and the Content of Criminal Connections: The Russian Mafia in Italy. Eur Sociol Rev. https://doi.org/10.1093/esr/jcs067
Funding
Work on this paper was partially funded by a contribution from Hlávkova nadace and by internal student grant “Networks of organized crime” awarded to the main author by the Faculty of Arts of Charles University in Prague.
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Ethical approval
This article does not contain any studies with human participants or animals performed by any of the authors.
Rights and permissions
Open Access This article is distributed under the terms of the Creative Commons Attribution 4.0 International License (http://creativecommons.org/licenses/by/4.0/), which permits unrestricted use, distribution, and reproduction in any medium, provided you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons license, and indicate if changes were made.
About this article
Cite this article
Diviák, T., Dijkstra, J.K. & Snijders, T.A.B. Structure, multiplexity, and centrality in a corruption network: the Czech Rath affair. Trends Organ Crim 22, 274–297 (2019). https://doi.org/10.1007/s12117-018-9334-y
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12117-018-9334-y