Abstract
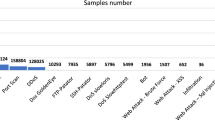
In the study of Intrusion Detection System (IDS) choosing proper combination of features is of great importance. Many researchers seek to obtain appropriate features with optimization algorithms. There are several optimization algorithms that can properly select a near-optimal combination of features to reach an improved IDS. Genetic Algorithms (GA) as one of the most powerful methods have been used in this research for feature selection. In this paper, voted outputs of built models on the GA suggested features of a more recent version of KDD CUP 99 dataset, NSL KDD, based on five different labels, have been gathered as a new dataset. Kernel Extreme Learning Machine (KELM), whose parameters have been optimally set by GA, is executed on the obtained dataset and results are collected. Based on IDS criteria, our proposed method can easily outperform general classification algorithms which use all the features of the employed dataset, especially in R2L and U2R with the accuracy of 98.73% and 98.22% respectively which is the highest among the current literature.





Similar content being viewed by others
Abbreviations
- IDS:
-
Intrusion detection system
- GA:
-
Genetic algorithms
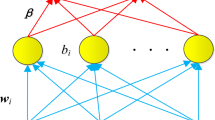
- KELM:
-
Kernel extreme learning machine
- DT:
-
Decision TREE
- KNN:
-
K-nearest neighbor
- MLP:
-
Multilayer perceptron
- SVM:
-
Support vector machine
- KPCA:
-
Kernel principle component analysis
- CFA:
-
Cuttlefish algorithm
- GHSOMs:
-
Growing hierarchical self-organizing maps
- FDR:
-
Fisher discriminant ratio
- OS-ELM:
-
Online sequential extreme learning machine
- TVCPSO:
-
Time-varying chaos particle swarm optimization
- MCLP:
-
Multiple criteria linear programming
- R2L:
-
Remote-to-local
- U2:
-
User-to-root
References
Inayat Z, Gani A, Anuar N B, Khan M K and Anwar S 2016 Intrusion response systems: Foundations, design, and challenges. J. Netw. Comput. Appl. 62: 53–74
Elhag S, Fernández A, Bawakid A, Alshomrani S and Herrera F 2015 On the combination of genetic fuzzy systems and pairwise learning for improving detection rates on intrusion detection systems. Expert Syst. Appl. 42: 193–202
http://kdd.ics.uci.edu/databases/kddcup99/kddcup99/ Accessed 10.28.99
http://www.unb.ca/research/iscx/dataset/iscx-NSL-KDD-dataset/Accessed 2015
Tavallaee M, Bagheri E, Lu W and Ghorbani A 2009 A detailed analysis of the KDD CUP 99 data set. In: Proceeding of the IEEE Symposium on Computational Intelligence for Security and Defense Applications, pp. 53–58
de la Hoz E et al 2013 Network anomaly classification by support vector classifiers ensemble and non-linear projection techniques. Hybrid Artif. Intell. Syst. 103–111
Singh R, Kumar H and Singla R 2015 An intrusion detection system using network traffic profiling and online sequential extreme learning machine. Expert Syst. Appl. 42: 8609–8624
Lakhina S, Joseph S and Verma B 2010 Feature reduction using principal component analysis for effective anomaly–based intrusion detection on NSL-KDD. Int. J. Eng. Sci. Technol. 2: 1790–1799
Jain A K, Duin R P W and Jianchang M 2000 Statistical pattern recognition: a review. Pattern Anal. Mach. Intell. 22: 4–37
Trunk G V 1979 A problem of dimensionality: a simple example. Pattern Anal. Mach. Intell. PAMI 1: 306–307
Goldberg D E et al 1989 Genetic Algorithms in Search Optimization and Machine Learning, vol. 412 pp. 211
Li W 2004 Using genetic algorithm for network intrusion detection. In: Proceedings of the United States Department of Energy Cyber Security Group, pp. 1–8
Fidelis M V, Lopes H and Freitas A 2000 Discovering comprehensible classification rules with a genetic algorithm. In: Proceedings of the 2000 Congress on Evolutionary Computation 1, pp. 805–810
Rastegari S, Hingston P and Lam C-P 2015 Evolving statistical rule sets for network intrusion detection. Appl. Soft Comput. 33: 348–359
Eesa A S, Orman Z and Brifcani A M A 2015 Novel feature-selection approach based on the cuttlefish optimization algorithm for intrusion detection systems. Expert Syst. Appl. 42: 2670–2679
Sindhu S S S, Geetha S and Kannan A 2012 Decision tree based light weight intrusion detection using a wrapper approach. Expert Syst. Appl. 39: 129–141
Kim G, Lee S B and Kim S 2014 A novel hybrid intrusion detection method integrating anomaly detection with misuse detection. Expert Syst. Appl. 41: 1690–1700
Saied A, Overill R E and Radzik T 2016 Detection of known and unknown DDoS attacks using artificial neural networks. Neurocomputing 172: 385–393
Wang G, Hao J, Mab J and Huang L 2010 A new approach to intrusion detection using artificial neural networks and fuzzy clustering. Expert Syst. Appl. 37: 6225–6232
Meng W, Li W and Kwok L-F 2014 EFM: enhancing the performance of signature-based network intrusion detection systems using enhanced filter mechanism. Comput. Secur. 43: 189–204
Lin W-C, Ke S-W and Tsai C-F 2015 CANN: an intrusion detection system based on combining cluster centers and nearest neighbors. Knowl. Based Syst. 78: 13–21
Erfani S M, Rajasegarar S, Karunasekera S and Leckie C 2016 High-dimensional and large-scale anomaly detection using a linear one-class SVM with deep learning. Pattern Recognit. 58: 121–134
Catania C A, Bromberg F and Garino CG 2012 An autonomous labeling approach to support vector machines algorithms for network traffic anomaly detection. Expert Syst. Appl. 39: 1822–1829
Kuanga F, Xua W and Zhang S 2014 A novel hybrid KPCA and SVM with GA model for intrusion detection. Appl. Soft Comput. 18: 178–184
Tsang C-H, Kwong S and Wang H 2007 Genetic-fuzzy rule mining approach and evaluation of feature selection techniques for anomaly intrusion detection. Pattern Recognit. 40: 2373–2391
Shafi K and Abbass HA 2009 An adaptive genetic-based signature learning system for intrusion detection. Expert Syst. Appl. 36: 12036–12043
de la Hoz E, de la Hoz E, Ortiz A, Ortega J and Martínez-Álvarez A 2014 Feature selection by multi-objective optimization: application to network anomaly detection by hierarchical self-organizing maps. Knowl. Based Syst. 71: 322–338
De la Hoz E, De La Hoz E, Ortiz A, Ortega J and Prieto B 2015 PCA filtering and probabilistic SOM for network intrusion detection. Neurocomputing 164: 71–78
Monowar, Bhuyan H, Bhattacharyya D K and Kalita J K 2016 A multi-step outlier-based anomaly detection approach to network-wide traffic. Inf. Sci. 348: 243–271
Bamakan S M H, Wang H, Yingjie T and Shi Y 2016 An effective intrusion detection framework based on MCLP/SVM optimized by time-varying chaos particle swarm optimization. Neurocomputing 199: 90–102
Fossaceca J M , Mazzuchi T A and Sarkani S 2015 MARK-ELM: application of a novel multiple kernel learning framework for improving the robustness of network intrusion detection. Expert Syst. Appl. 42: 4062–4080
Reeves C R and Rowe J E 2003 Genetic algorithms: principles and perspectives: a guide to GA theory. US: Springer, vol. 20, pp 112
Avci E and Coteli R 2012 A new automatic target recognition system based on wavelet extreme learning machine. Expert Syst. Appl. 39: 12340–12348
Cheng C, Tay W P and Huang G B 2012 Extreme learning machines for intrusion detection. In: The 2012 International Joint Conference on Neural Networks (IJCNN), pp. 1–8
Creech G and Jiang F 2012 The application of extreme learning machines to the network intrusion detection problem. In: Numerical Analysis and Applied Mathematics ICNAAM: International Conference of Numerical Analysis and Applied Mathematics 1479, pp. 1506–1511
de Farias G P M, de Oliveira A L and Cabral G G 2012 Extreme learning machines for intrusion detection systems. Neural Inf. Process. 535–543
Amiri F, Rezaei Yousefi M, Lucas C, Shakery A and Yazdani N 2011 Mutual information-based feature selection for intrusion detection systems. J. Netw. Comput. Appl. 34: 1184–1199
Sangkatsanee P, Wattanapongsakorn N and Charnsripinyo C 2011 Practical real-time intrusion detection using machine learning approaches. Comput. Commun. 34: 2227–2235
Pereira C R, Nakamura R Y M, Costa K A P and Papa J P 2012 An optimum-path forest framework for intrusion detection in computer networks. Eng. Appl. Artif. Intell. 25: 1226–1234
Liu Y, Liu S and Zhao X 2017 Intrusion detection algorithm based on convolutional neural network. In: State Key Laboratory of Mathematical Engineering and Advanced Computing, Zhengzhou, Henan, China 2017 4th International Conference on Engineering Technology and Application ISBN: 978-1-60595-527-8
Shone N, Ngoc T N , Phai V D and Shi Q 2017 A deep learning approach to network intrusion detection. IEEE Trans. Emerg. Top. Comput. Intell. 2: 1–16
Xin Y, Kong L, Liu Z, Chen Y, Li Y, Zhu H, Gao M, Hou H and Wang C 2017 Machine learning and deep learning methods for cybersecurity. IEEE Transl. Content Min. 1: 1–10
http://www.ntu.edu.sg/home/egbhuang/elm_kernel/ Accessed 2013
Acknowledgements
The authors would like to express their gratitude toward reference [43] for putting NSL-KDD dataset in public access.
Author information
Authors and Affiliations
Corresponding author
Appendix A: Proposed feature by GA
Appendix A: Proposed feature by GA
Rights and permissions
About this article
Cite this article
Ghasemi, J., Esmaily, J. & Moradinezhad, R. Intrusion detection system using an optimized kernel extreme learning machine and efficient features. Sādhanā 45, 2 (2020). https://doi.org/10.1007/s12046-019-1230-x
Received:
Revised:
Accepted:
Published:
DOI: https://doi.org/10.1007/s12046-019-1230-x