Abstract
We consider the problem of testing whether the points in a complex or real variety with non-zero coordinates form a multiplicative group or, more generally, a coset of a multiplicative group. For the coset case, we study the notion of shifted toric varieties which generalizes the notion of toric varieties. This requires a geometric view on the varieties rather than an algebraic view on the ideals. We present algorithms and computations on 129 models from the BioModels repository testing for group and coset structures over both the complex numbers and the real numbers. Our methods over the complex numbers are based on Gröbner basis techniques and binomiality tests. Over the real numbers we use first-order characterizations and employ real quantifier elimination. In combination with suitable prime decompositions and restrictions to subspaces it turns out that almost all models show coset structure. Beyond our practical computations, we give upper bounds on the asymptotic worst-case complexity of the corresponding problems by proposing single exponential algorithms that test complex or real varieties for toricity or shifted toricity. In the positive case, these algorithms produce generating binomials. In addition, we propose an asymptotically fast algorithm for testing membership in a binomial variety over the algebraic closure of the rational numbers.
Similar content being viewed by others
Avoid common mistakes on your manuscript.
1 Introduction
We are interested in situations where the points with non-zero coordinates in a given complex or real variety form a multiplicative group or, more generally, a coset. We illustrate this by means of a simple example. For \(K\in \{{\mathbb {C}},{\mathbb {R}}\}\), \((K^*)^n\) denotes the direct power of the multiplicative group of the respective field. Consider a family of ideals
with a rational parameter k. Let \(V_k\) be the complex variety of \(I_k\), and let \(V^*_k=V_k \cap ({\mathbb {C}}^*)^2\). Then \(V^*_1\) forms a group, but \(V^*_{-1}\) does not, because it does not contain (1, 1). However, \(V^*_{-1}=(1,i) \cdot V^*_1\) forms a coset of \(V^*_1\). Over the reals, \(V_1^*\cap ({\mathbb {R}}^*)^2\) is again a group, but \(V_{-1}^*\cap ({\mathbb {R}}^*)^2 = \varnothing \) is not a coset of any group. Consider now \(V_1 = V_{11} \cup V_{12}\), where \(V_{11}\) and \(V_{12}\) are given by \(\langle x-y \rangle \) and \(\langle x+y \rangle \), respectively. Notice that \(V^*_{11}\) is itself a group, and \(V^*_{12}\) is a coset of \(V^*_{11}\). Both \(V^*_{11}\) and \(V^*_{12}\) are irreducible because their generating ideals are prime. Under the additional condition of irreducibility \(V^*_{11}\) forms a torus and \(V^*_{12}\) forms a shifted torus. We then call the varieties \(V_{11}\) and \(V_{12}\) toric and shifted toric, respectively.
Toric varieties are well established and have an important role in algebraic geometry [24, 32]. However, our principal motivation to study generalizations of toricity comes from the sciences, specifically chemical reaction networks such as the following:

Assuming, e.g., mass action kinetics [66] one can derive a system of autonomous ordinary differential equations describing the development of concentrations of the species A and B as functions of time [29, Section 2.1.2]. For the given reaction network one obtains a polynomial vector field generating exactly our ideals \(I_k\) in (1). Our methods thus detect whether equilibrium points with non-zero coordinates form a group or a coset.
Detecting toricity of a variety in general, and of the steady state varieties of chemical reaction networks in particular, is a difficult problem [7]. The first issue in this regard is finding suitable notions to describe the structure of the steady states. Existing work typically addresses algebraic properties of the steady state ideal, e.g., the existence of binomial Gröbner bases. In this article, in contrast, we take a geometric approach, focusing on varieties rather than ideals. We propose to study toricity and shifted toricity of varieties V over \(K\in \{{\mathbb {C}},{\mathbb {R}}\}\), which for irreducible varieties coincides with \(V\cap (K^*)^n\) forming a multiplicative group or coset, respectively. It is noteworthy that chemical reaction network theory generally takes place in the interior of the first orthant of \({\mathbb {R}}^n\), i.e., all species concentrations and reaction rates are assumed to be strictly positive [29]. Our considering \(({\mathbb {C}}^*)^n\) in contrast to \({\mathbb {C}}^n\) is a first step in this direction, considering also \(({\mathbb {R}}^*)^n\) is another step.
Toric dynamical systems have been studied by Feinberg [27] and by Horn and Jackson [44]. Craciun et al. [17] showed that toric dynamical systems correspond to complex balancing [29]. Our generalized notions of toricity are inspired by Grigoriev and Milman’s work on binomial varieties [40]. There are further definitions in the literature, where the use of the term “toric” is well motivated. Gatermann et al. considered deformed toricity for steady state ideals [33]. The exact relation between the principle of complex balancing and various definitions of toricity has obtained considerable attention in the last years [34, 51, 55].
Complex balancing itself generalizes detailed balancing, which has widely been used in the context of chemical reaction networks [28, 29, 44]. Gorban et al. [35, 36] related reversibility of chemical reactions in detailed balance to binomiality of the corresponding varieties. Historically, the principle of detailed balancing has attracted considerable attention in the sciences. It was used by Boltzmann in 1872 in order to prove his H-theorem [4], by Einstein in 1916 for his quantum theory of emission and absorption of radiation [23], and by Wegscheider [68] and Onsager [53] in the context of chemical kinetics, which lead to Onsager’s Nobel prize in Chemistry in 1968. Pérez-Millán et al. [55] consider steady state ideals with binomial generators. They present a sufficient linear algebra condition on the stoichiometry matrix of a chemical reaction network in order to test whether the steady state ideal has binomial generators. Conradi and Kahle proposed a corresponding heuristic algorithm. They furthermore showed that the sufficient condition is even equivalent when the ideal is homogenous [15, 46, 47]. Based on the above-mentioned linear algebra condition, MESSI systems have been introduced in [54]. Recently, binomiality of steady state ideals was used to infer network structure of chemical reaction networks out of measurement data [67].
Besides its scientific adequacy as a generalization of complex balancing there are practical motivations for studying toricity. Relevant models are typically quite large. For instance, with our comprehensive computations in this article we will encounter systems up to 90 polynomials in dimension 71. This potentially takes symbolic computation to its limits. A possible approach to overcome this is to discover systematic occurrences of certain structural properties in the input, and to exploit those structural properties towards more efficient algorithms. From this point of view, toricity and shifted toricity are interesting concepts because tools from toric geometry can be used as a complexity reduction step in the multistationarity problem. Grigoriev and Weber [41] gave a complexity analysis for solving binomial varieties, based on the computation of Smith normal forms. More interestingly, toric and shifted toric models are known to have scale invariant multistationarity in the space of linear conserved quantities, which further reduces the dimension of the multistationarity problem [14].
Our original contributions in this article are the following. Interested in the geometric structure of real and complex varieties V rather than the algebraic structure of the corresponding ideals, we study primarily \(V^*=V\cap (K^*)^n\). We call V shifted toric when V is irreducible and \(V^*\) is a coset. This generalizes the notion of toric varieties V for groups \(V^*\). Within this setting, we have two principal results:
-
Relating our novel geometric view to the established algebraic view, we give a characterization in terms of Gröbner bases for \(V^*\) to be a group or coset (Proposition 7).
-
We show that Zariski closures of groups in \(({\mathbb {C}}^*)^n\) are binomial varieties (Proposition 6). The converse had been shown in [40].
We propose practical algorithms testing for given polynomial systems F whether their varieties contain group or coset structures.
-
We consider over the complex numbers \(V(F)^*\) (Algorithm 1) and \(V(P_i)^*\) for prime components \(\langle P_i\rangle \) of \(\langle F\rangle \) (Algorithm 3).
-
We consider the same over the real numbers, \(V(F)^*\) (Algorithm 4) and \(V(P_i)^*\) (Algorithm 6).
-
With prime decomposition we find that for up to 98% of the prime components \(V_K(P_i)^*\) is either empty or a coset.
Our algorithms are implemented in MapleFootnote 1 and ReduceFootnote 2 [42, 43] and systematically applied to the steady state varieties of 129 models from the BioModels repository.Footnote 3 Our objective was to build on robust, off-the-shelf software, which has a chance to be accepted by scientific communities outside symbolic computation in the foreseeable future. As a consequence, our proposed algorithms must rely on existing implementations. Over \({\mathbb {C}}\) we use Gröbner bases [8, 25, 26], and over \({\mathbb {R}}\) we use real quantifier elimination techniques.
Gröbner bases and real quantifier elimination mentioned above come with high intrinsic complexity. The former are complete for exponential space [50]. The latter are double exponential [18, 38, 69]. From a more theoretical point of view we study the intrinsic complexity of the problems actually addressed. We follow Chistov–Grigoriev’s complexity results for first-order quantifier elimination over algebraically closed fields [11], the algorithm constructing irreducible components of a variety [11, 37] and Grigoriev–Vorobjov’s algorithm for solving polynomial system of inequalities [39]. These results are used to propose an algorithm to test within single exponential complexity bounds whether:
-
a given complex variety is toric or shifted toric (Theorem 25);
-
a given real variety is toric or shifted toric (Theorem 26);
-
a given point belongs to a given binomial variety (Theorem 27).
The plan of the article is as follows. In Sect. 2 we present preliminaries from the literature and introduce our new notions and related results. In Sect. 3, we present new algorithms for group and coset tests over \({\mathbb {C}}\) and \({\mathbb {R}}\). As a first step towards irreducible varieties we also use prime decompositions over the coefficient field, i.e., rational numbers. For the sake of a concise discussion, the major part of our rather comprehensive computation results can be found in Appendix Appendix A. In Sect. 4 we propose asymptotically fast algorithms for the practical computations in Sect. 3. The proposed algorithms induce upper complexity bounds on the corresponding problems. In Sect. 5 we summarize our findings and mention perspectives for future work.
2 Toric, Shifted Toric and Binomial Varieties
We use K to denote either \({\mathbb {C}}\) or \({\mathbb {R}}\) when definitions or results hold for both fields. The natural numbers \({\mathbb {N}}\) include 0. For positive \(n\in {\mathbb {N}}\) and \(X=(x_1,\dots ,x_n)\), the polynomial ring with coefficients in \({\mathbb {Q}}\) and variables \(x_1\), ..., \(x_n\) is written \({\mathbb {Q}}[X]={\mathbb {Q}}[x_1,\dots ,x_n]\). For \(\alpha =(\alpha _1,\dots ,\alpha _n) \in {\mathbb {N}}^n, X^\alpha =x_1^{\alpha _1}\dots x_n^{\alpha _n}\) is a monomial in \({\mathbb {Q}}[X]\). When mentioning Gröbner bases of ideals we always mean reduced Gröbner bases; when not mentioned explicitly the term order is not relevant. Given a polynomial \(f \in {\mathbb {Q}}[X]\), the variety of a f over K is \(V(f)=\{\,z\in K\mid f(z)=0\,\}\subseteq K^n\); this naturally generalizes to sets F of polynomials and ideals I. Vice versa, given a variety \(V\subseteq K^n\), we define the ideal of V to be \(I(V)=\{\,f\in {\mathbb {Q}}[X]\mid f(z)=0\text { for all }z\in V\,\}\). Recall that over algebraically closed fields, \(I(V(J)) = \sqrt{J}\), the radical of J.
Let \(K^*\) be the multiplicative group of \(K\). A subgroup \(G \subseteq (K^*)^n\) is called a torus over the direct product \((K^*)^n\), where multiplication is coordinate-wise, if there exists \(m \in {\mathbb {N}}\) such that G is isomorphic to \((K^*)^m\). A variety \(V \subseteq K^n\) is called toric if it is irreducible and there exists a torus \(G \subseteq (K^*)^n\) such that \(V=\overline{G}\), the Zariski closure of G [63]. It is noteworthy that there are alternative definitions that requires the variety to be normal as well [32].
For a variety \(V \subseteq K^n\), by \(V^*\) we denote \(V \cap (K^*)^n\), i.e., the points in V with non-zero coordinates. It is well-known that every torus is the (irreducible) zero set of a set of Laurent binomials of the form \(X^\gamma -1\) where \(\gamma \in {\mathbb {Z}}\) [32]. We are going to make use of the following proposition, which is a consequence of results in [32, 63].
Proposition 1
Let \(V \subseteq {\mathbb {C}}^n\) be a variety. V is a toric variety if and only I(V) is prime and the reduced Gröbner basis (with respect to any term order) of I(V) contains only binomials of the form \(X^\alpha -X^\beta \) where \(\alpha \), \(\beta \in {\mathbb {N}}^n\).
By definition, V is toric if and only if V is irreducible and there exists a torus T such that \(V=\overline{T}\). Assume that V is given by a set of generators of I(V). Since V is irreducible, then \(V^*\) is irreducible, hence \(T=V^*\), \(V = \overline{V^*}\), and \(I(V)=I(\overline{V^*})\). Therefore, it suffices to compute a Gröbner basis of I(V) instead of \(I(V^*)\) and use Proposition 1 in order to check if \(V^*\) is a group. Note that if there is a Gröbner basis of I(V) where all elements are of the form \(X^\alpha -X^\beta \) and the ideal is prime, then \(V^*\) is clearly non-empty. For more detailed study of toric varieties refer to [32] and [63].
Not all subgroups of \((K^*)^n\) are reducible. For example if \(K={\mathbb {C}}\) and \(V=V(x^2-y^2) \subseteq {\mathbb {C}}^n\), one can check that \(V^*= V \cap ({\mathbb {C}}^*)^2\) is a group, however it is not irreducible, hence not a torus. Actually V can be decomposed into the torus \(V_1=V(x-y)\cap ({\mathbb {C}}^*)^2\) and \(V_2=V(x+y) \cap ({\mathbb {C}}^*)^2\), which is a coset of \(V_1\). Varieties that admit a group structure have interesting properties. A class of such varieties, called binomial varieties are studied by Grigoriev and Milman [40], where the authors present a structure theorem for them and discuss the complexity of their Nash resolution. We remind ourselves of the definition and the structure theorem of binomial varieties, which will be used for classifying steady state ideals.
Definition 2
(Binomial Variety) A variety \(V \subseteq {\mathbb {C}}^n\) is called binomial if \(V^*:= V \cap ({\mathbb {C}}^*)^n\) is the zero set of a finite set of binomials of the form \(X^\alpha - 1 \in K[x_1^{\pm 1},\ldots , x_n^{\pm 1}]\) and \(V = \overline{V^*}\).
Using Gröbner bases instead of Laurent polynomials, one can see that if a variety \(V \subseteq {\mathbb {C}}^n\) is binomial then all elements of every Gröbner basis of I(V) are binomials of the form \(X^\alpha -X^\beta \), where \(\alpha ,\beta \in {\mathbb {N}}\setminus \{0\}\). The following theorem by Grigoriev and Milman shows the structure of the binomial varieties by precisely describing their irreducible components.
Theorem 3
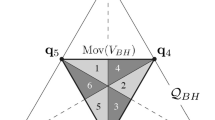
[40, Theorem 3.7] The irreducible components of a binomial variety \(V \subseteq {\mathbb {C}}^n\) include exactly one toric variety \(\overline{T}\), where \(T \subseteq ({\mathbb {C}}^*)^n\) is a torus, and several varieties \(V_1=\overline{x_1T}\), ..., \(V_r=\overline{x_rT}\), where \(x_1T\), ..., \(x_rT \subseteq ({\mathbb {C}}^*)^n\) are cosets of T as a group, with respect to \(x_1\), ..., \(x_r \in ({\mathbb {C}}^*)^n\), respectively.
Later in this section we will show that the closure of any subgroup of \(({\mathbb {C}}^*)^n\) is a binomial variety. Proposition 1 gives the form of the polynomials in a Gröbner basis of the ideal describing the toric component of a binomial variety. For the components that are cosets of the torus, one can easily derive the form of the reduced Gröbner basis from the definition of the torus and Proposition 1. This is stated precisely in the following proposition. Intuitively, non-toric components of a binomial variety can be considered as the shifts of the toric component. This motivates us to define shifted toric varieties.
Definition 4
(Shifted Toric Variety) A shifted torus in \((K^*)^n\) is defined to be a coset of a torus in \((K^*)^n\). A variety \(V\subseteq K^n\) is called shifted toric if it is the closure of a shifted torus.
Since every group is a coset of itself, every torus is a shifted torus, and therefore every toric variety is a shifted toric variety. However, a shifted toric variety is not necessarily a toric variety. Following the definition of shifted toric varieties and using Proposition 1, we show in the following proposition that ideals of shifted toric varieties have Gröbner bases of a specific form.
Proposition 5
\(V^*\subseteq {\mathbb {C}}^n\) is a shifted torus if and only if \(V^*\) is a zero set of Laurent binomials of the form \(\left( \frac{X}{g}\right) ^{\alpha } -1\), where \(g \in V^*\) and \(\alpha \in {\mathbb {Z}}^n\). Similarly, V is shifted toric if and only if I(V) is prime and the reduced Gröbner basis (with respect to any term order) of I(V) contains only binomials of the form \(X^\alpha + c X^\beta \) where \(c \in {\mathbb {C}}^*\), \(\alpha \), \(\beta \in {\mathbb {N}}^n\setminus \{(0,\dots ,0)\}\).
Proof
V is shifted toric if and only if there exists a torus T and a coset C of T with respect to some \(g \in K^n\) (i.e., \(C=gT\)), such that \(V = \overline{C}\). Since V is irreducible, then \(\overline{V^*} = \overline{C} =V\) and \(I(V)=I(\overline{V^*}) = I(\overline{C})\), and this ideal is prime. Assume that V given by a set of generators of I(V). V is shifted toric if and only if \(I(\overline{V^*})=I(V)\) is prime and \(V^*\) is a coset. This holds if and only if \(I(V^*)\) is prime and \(g^{-1}V^*\) is a group. Note that \(\overline{g^{-1}V^*}\) is irreducible if and only if \(\overline{V^*}\) is irreducible. This holds if and only if \(I(V^*)\) is prime, or equivalently I(V) is prime. Therefore, by Proposition 1, V is shifted toric if and only if I(V) is prime and all the elements of every Gröbner basis of \(I(\overline{g^{-1}V^*})\) is of the form \(X^\alpha -X^\beta \), for \(\alpha ,\beta \in {\mathbb {N}}^n \setminus \{(0,\dots ,0)\}\). Equivalently, all the elements of I(V) are of the form \(\left( \frac{X}{g}\right) ^\alpha -\left( \frac{X}{g}\right) ^\beta \). Cleaning the denominator, we have the desired form of the Gröbner basis elements. \(\square \)
Proposition 5 along with the structure theorem for binomial ideals imply that the primary decomposition of an ideal generated by binomials of the form \(X^\alpha -X^\beta \) include an ideal generated by binomials of the form \(X^\alpha -X^\beta \) and several ideals generated by binomials of the form \(X^\alpha -c X^\beta \).
Using Proposition 5, one can design a randomised algorithm for testing shifted toricity of a variety \(V = \overline{V^*}\). Let \(g_1,\dots ,g_m\) be generic points in \(V^*\) and consider the set of Laurent binomials \( G=\left\{ \,\left( \frac{X}{g_i} \right) ^{\gamma _i} -1\ \big \vert \ i=1,\dots ,m\, \right\} \) with symbolic exponents \(\gamma _i =(\gamma _{i1},\ldots , \gamma _{in})\). Let
be the matrix of exponents of the Laurent binomials and make it row reduced. This leads to a linear combination of rows with coefficients in \({\mathbb {Z}}\), say \(d_i\). Then \(V\) is shifted toric if and only if
which holds if and only if \(\prod \nolimits _{i=1}^m \left( g_{i1}^{d_{i1}}\ldots g_{in}^{d_{in}} \right) =1\). Solving the linear equations (3) will give us the exponents of the Laurent polynomials. Note that G obtained in this way is a reduced Gröbner basis.
One can see that a binomial variety is the closure of a group and furthermore, by Proposition 3, it can be decomposed into toric and shifted toric varieties as its irreducible components. A natural question is whether this property holds for every variety that is the closure of a group. The answer to this question is positive and indeed such varieties are precisely binomial varieties. This is explicitly formulated in a remark in [24, after Proposition 2.3].
Proposition 6
Let W be a subgroup of \(({\mathbb {C}}^*)^n\). Then \(\overline{W}\) is a binomial variety.
Proof
By definition of binomial variety, we have to prove that \(\overline{W}\) is the zero set of binomials of the form \(X^\alpha -X^\beta \) and \(\overline{\left( \overline{W}\right) ^*}=\overline{W}\). The equality \(\overline{\left( \overline{W}\right) ^*}=\overline{W}\) directly comes from the definition of Zariski closure.
For proving that the generators of \(I(\overline{W})\) have the desired form, we use the notations of [24]. By Proposition 2.3(a) in the latter reference, \({\mathbb {C}}[X^{\pm 1}]I(W)=I(\rho )\), for some partial character \(\rho \in \text {Hom}({\mathbb {Z}}^{n},{\mathbb {C}}^{*})\). By Theorem 2.1(b) in the same reference, \(I(\rho )=\langle x^{m_{1}}-\rho (m_{1}),\ldots , x^{m_{r}}-\rho (m_{r})\rangle \) where \(m_{1},\ldots ,m_{r} \in {\mathbb {Z}}^n\) is a basis of \(L_{\rho }\). As W is a group, \((1,\dots ,1)\in W\); hence \(\rho (m_{1})=\cdots =\rho (m_{r})=1\) and therefore I(W) is generated by binomials of the form \(X^{\alpha }-X^{\beta }\) where \(\alpha ,\beta \in {\mathbb {N}}\). Since \(\overline{W} = V(I(W))\), we have proved the proposition.
Proposition 6 can also be proved over the positive real numbers by considering the logarithm map on \(({\mathbb {R}}_{>0})^n\) acting coordinate-wise. The image of this map forms a linear space. A basis of this linear space provides a parametrization of a group.
From a computational point of view, a variety \(V=V(I)\) is usually given by a set of generators of I and we would like to derive information about toricity, binomiality or coset property of V by computations over the generators of I. This can be done via Gröbner bases. Assume that G is a Gröbner basis of I, hence \(V=V(G)\), and \(V^*\ne \varnothing \). If all elements of G are of the form \(X^\alpha -X^\beta \), then \(V^*\) is a subgroup of \(({\mathbb {C}}^*)^n\). If all elements of G are of the form \(c_\alpha X^\alpha -c_\beta X^\beta \) where \(c_\alpha \ne 0\) and \(c_\beta \ne 0\), then \(V^*\) is a coset of a subgroup of \(({\mathbb {C}}^*)^n\). Note that the converse of the above does not hold. This is because \(\overline{V^*}\) and V may not be equal and therefore \(I(\overline{V^*})\) and I(V) may not be equal, which means that a Gröbner basis of I(V) does not give information about group or coset structure of \(V^*\). In case V is irreducible, we have that \(\overline{V^*}=V\), e.g., when V is toric or shifted toric. In order to solve this problem one needs to saturate I with the multiplication of the variables and then consider the radical of this saturation. Saturation removes the points that are in V but not in \(\overline{V^*}\). The following proposition states this precisely and is the essence of this section for computations over complex numbers.
Proposition 7
Let I be an ideal in \({\mathbb {Q}}[x_1,\dots ,x_n]\), let \(V:=V(I) \subseteq {\mathbb {C}}^n\) be the variety of I, and let \(G \subseteq {\mathbb {Q}}[x_1,\dots ,x_n]\) be a reduced Gröbner basis of the radical of \(I:\langle x_1\dots x_n \rangle ^\infty \). Then \(V^*=\varnothing \) if and only if \(G=\{1\}\). If \(V^*\ne \varnothing \), then the following hold:
-
(i)
\(V^*\) is a subgroup of \(({\mathbb {C}}^*)^n\) if and only if all elements of G are of the form \(X^\alpha -X^\beta \).
-
(ii)
\(V^*\) is a coset of a subgroup of \(({\mathbb {C}}^*)^n\) if and only if all elements of G are of the form \(c_\alpha X^\alpha -c_\beta X^\beta \) where \(c_\alpha \ne 0\) and \(c_\beta \ne 0\).
Proof
In order to prove the proposition we use [16, Chapter 4, Theorem 10 (iii)], which states that over an algebraically closed field, we have that \(\overline{V(J_1)\setminus V(J_2)} = V(J_1:J_2^\infty )\) for ideals \(J_1\) and \(J_2\). Set \(J_1=I\) and \(J_2=\langle x_1\dots x_n \rangle \). Since \(V^*= V(I) \setminus V(x_1\dots x_n)\), and V is a variety over \({\mathbb {C}}\) which is algebraically closed, we have that \( \overline{V^*} = V(I:\langle x_1\dots x_n \rangle ^\infty )\). Then
\(V^*= \varnothing \) if and only if \(V(I) \setminus V(x_1\dots x_n) = \varnothing \), which is the case if and only if \(V(I) \subseteq V(x_1\dots x_n)\). This happens if and only if \(I(V(I)) = I(V(x_1\dots x_n))\), if and only if \(\langle x_1,\dots ,x_n \rangle \subseteq \sqrt{I}\), which is the case if and only if some product of the variables is in I, or equivalently \(I:\langle x_1\dots x_n \rangle ^\infty = \langle 1 \rangle \), i.e., \(G={1}\).
For proving (i), let \(V^*\) be a group. By Proposition 6, we have that all the elements of every Gröbner basis of \(I(\overline{V^*})\) are of the form \(X^\alpha - X^\beta \). But according to (4) and the assumption that G is a Gröbner basis of \(\sqrt{I:\langle x_1\dots x_n \rangle ^\infty }\), this condition holds.
For the converse, let the elements of G have the desired form. Then \(V(\sqrt{I:\langle x_1\dots x_n \rangle ^\infty })^*\) is obviously a group. But \(V(\sqrt{I:\langle x_1\dots x_n \rangle ^\infty })^*=V(I:\langle x_1\dots x_n \rangle ^\infty )^*\) and therefore the latter is a group. Now using [16, Chapter 4, Theorem 10 (iii)], we have that \(V(I:\langle x_1\dots x_n \rangle ^\infty )^* = (\overline{V(I)\setminus V(x_1\dots x_n)})^*\). One can easily check that the latter is equal to \(V(I)^*\). Hence \(V^*=V(I)^*\) is a group and we are done.
The proof of part (ii) is analogous to that of part (i) above. \(\square \)
For the rest of this section, we present the monomial parametrization of a torus and state propositions that allow one to find the cosets of a torus as irreducible components of a binomial variety using roots of unity. Readers primarily interested in our algorithms in Sect. 3 can safely skip this part.
We start with introducing the monomial parametrization of shifted toric varieties. Let \(T\subseteq (K^*)^n\) be a torus of dimension m, hence \(T \simeq (K^*)^m\), and let \(x_0\in (K^*)^n\). Following the monomial parametrization of a torus given in [24, Corollary 2.6], one can see that the coset \(x_0T\) of T can be seen as the image of the following monomial map, which is the monomial parametrization of \(x_0T\).
where \(A\in {\mathbb {Z}}^{d\times n}\)is a rank m matrix. Note that while the matrix A is not unique, it only depends on T and not on \(x_0\). In particular, T is its own coset with respect to the unity \(\mathbf{1} := (1,\ldots ,1) \in (K^*)^n\). Note that if \(B\in {\mathbb {Z}}^{d\times n}\) is another matrix such that T equals the image of \(\varphi _{(\mathbf{1} ,B)}\), then B corresponds to a re-parametrization of T.
Example 8
\(V(xy-1)\cap \left( {\mathbb {C}}^*\right) ^2\) can be seen as the image of \(\varphi _{(\mathbf{1} ,(1,-1))} :{\mathbb {C}}^*\rightarrow ({\mathbb {C}}^*)^2\) with \(\varphi _{(\mathbf{1} ,(1,-1))} (t)= (t,t^{-1})\) or as the image of \(\varphi _{(\mathbf{1} ,(-1,1))}:{\mathbb {C}}^*\rightarrow ({\mathbb {C}}^*)^2 \) with \(\varphi _{(\mathbf{1} ,(-1,1))} (t)= (t^{-1},t)\).
Proposition 9
If \(G\subseteq ({\mathbb {C}}^*)^n\) is a group and reducible into \(r \in {\mathbb {N}}\) cosets of a torus T, then there exist \(y_1,\ldots , y_r \in ({\mathbb {C}}^*)^n\) whose coordinates are roots of unity and \(G = \bigcup _{i=1}^r y_iT\) is the irreducible decomposition of G.
Proof
If \(G=T\), then it is its own coset with respect to \(\mathbf{1} \) and we are done. Otherwise, let \(S_i = \tilde{y}_iT\) be a proper coset of T and suppose that there is no \(\xi \in ({\mathbb {C}}^*)^n\) such that the coordinates of \(\xi \) are roots of unity and \(S_i=\xi T\). This means that for all such \(\xi \) the image of \(\varphi _{(\tilde{y}_i,T)}\) is different from the image of \(\varphi _{(\xi , T)}\). Hence there exists \(t\in ({\mathbb {C}}^*)^m\) such that for all \(s\in ({\mathbb {C}}^*)^m\) one has \(\varphi _{(\tilde{y}_i,T)}(t)\ne \varphi _{(\xi ,T)}(s)\). In other words, there exists \(t\in ({\mathbb {C}}^*)^m\) such that for all \(s \in ({\mathbb {C}}^*)^m\) one has \(\tilde{y}_i t^{A} \ne \xi s^{A}\) for some \(i\in \{1,\ldots ,n\}\). As the coordinates of \(\xi \) are roots of unity, there is a natural number N such that \(\xi ^N = \mathbf{1} \). Therefore, for all \(s\in ({\mathbb {C}}^*)^m\) one has \(\tilde{y}_i^{N} t^{NA} \ne s^{NA}\) for some \(i\in \{1,\ldots ,n\}\). As the image of \(\varphi \) is invariant under \(A \mapsto NA\), the cosets \(\tilde{y}_i^NT\) and T are distinct. By using a similar argument and induction, one can prove that \(T, \tilde{y}_i^NT\), \(\tilde{y}_i^{2N}T, \ldots \) are distinct. As G is closed under multiplication, it contains all these cosets. However, this contradicts the assumption that G is reducible into a torus and a finite number of its cosets. \(\square \)
Remark 10
Let \(S_1\) and \(S_2\) be two cosets of a torus \(T \subseteq ({\mathbb {C}}^*)^n\). The coset \(S_1\) is called the complex conjugate of the coset \(S_2\), written \(S_1=S_2^+\), when every point of \(S_1\) is the complex conjugate of a point of \(S_2\) and every point of \(S_2\) is the complex conjugate of a point of \(S_1\). As the complex conjugate is an automorphism of \(({\mathbb {C}}^*)^m\), \(S_1\) is the complex conjugate of \(S_2\) if and only if \(S_1\) contains the complex conjugate of some point of \(S_2\). A pair \(S_1,S_2\) is called a pair of complex conjugates if \(S_1=S_2^+\). If \(G\subseteq ({\mathbb {C}}^*)^n\) is reducible into a finite number of cosets of a torus then they come in pairs of complex conjugates. To see this, denote the toric component of G by T. If \(G=T\), then clearly \(G=G^+\). Suppose that G contains a proper coset S of T. By Lemma 9 there is a point \(\xi \in S\) whose coordinates are roots of unity. Then \(\xi \xi ^+=\mathbf{1} \). As G is a group, \(\xi ^+\) is an element of G. As \(S=\xi T\) and \(\xi ^+T=(\xi T)^+=S^+\), we conclude that \(S^+\) is contained in G.
Proposition 11
Let \(P=(X/\xi )^u- (X/\xi )^v\in {\mathbb {C}}[X]\) be a non-zero irreducible polynomial, where the coordinates of \(\xi \in ({\mathbb {C}}^*)^n\) are roots of unity. Then for all i in \({\mathbb {N}}\) there exist \(g_i\) in \({\mathbb {C}}[X]\) and \(\alpha _i\), \(\beta _i\) in \({\mathbb {N}}^n\) such that \(g_iP=X^{i\alpha _i}-X^{i\beta _i}\).
Proof
Note that \(P=(X^{u}-\xi ^{u-v}X^v)/\xi ^u\). As the coordinates of \(\xi \) are roots of unity, \(\gamma =\xi ^{u-v}\) is also a root of unity. Let m be the smallest positive integer such that \(\gamma ^m=1\). As \(\mathfrak U_m =\{\gamma ,\gamma ^2,\ldots ,\gamma ^m\}\) is a group of roots of unity of order m, it is clear that
Hence one can take
Substituting \(\mathfrak U_m\) with the group \(\mathfrak U_{mi}\), i.e., the group of roots of unity of order mi, and following the steps for constructing \(g_1\) accordingly, one can construct \(g_i\) for all \(i \ge 2\). \(\square \)
3 Algorithmic Classification of Biomodels
We want to apply our concept of shifted toricity to biomodels focusing on the BioModelsFootnote 4 repository of mathematical models of biological and biomedical systems [9]. The BioModels repository uses the Systems Biology Markup Language (SBML) [30, 45]. SBML is a representation format, based on XML, for communicating and storing computational models of biological processes. It is a free and open standard with widespread software support and a community of users and developers. SBML models have been typically created in the context of numerical computations or simulations and must be processed carefully with symbolic computation. For instance, numerical values, like reaction rate constants, contained in the models are often represented as truncated fixed point floats, and the available SBML parsers possibly introduce further rounding errors when implicitly performing substitutions with those values. Such issues are addressed by ODEbase,Footnote 5 which provides pre-processed versions of BioModels for use in symbolic computation. We consider here all models from ODEbase where the vector field of the ODE is polynomial over \({\mathbb {Q}}\) after application of certain SBML-specific rules and substitution of parameter values. This amounts to a total of 129 models considered in this article.
Following a convention often used in publications on chemical reaction network theory in the context of symbolic computation, ODEbase replaces names of species concentrations by more abstract names \(x_i\) using numbers as indices. With the application of SBML rules some of those \(x_i\) vanish in the ODEbase toolchain. We therefore consider, more abstractly, ordered sets X of variables, tacitly assuming that the order establishes a mapping between indeterminates in \({\mathbb {Q}}[X]\) and coordinates in \(K^{|X|}\). As a matter of fact, the variables will also vanish during our own algorithms discussed throughout this section. The following example illustrates this.
Example 12
(BIOMD0000000198) Consider the following system in \({\mathbb {Q}}[x_{2}, \dots , x_{10}]\):
From its Gröbner basis \(G=\{x_{2}, x_{6}, x_{5}-100 x_{4}, 8 x_{8}-x_{10}, x_{7}, x_{3}, -x_{10}+80 x_{9}\}\) we can read off that for every point in \(V_{\mathbb {C}}(F)\subseteq {\mathbb {C}}^9\), e.g., the \(x_2\)-coordinate must be 0. It follows that \(V_{\mathbb {C}}(F)^*=\varnothing \). Geometrically, \(V_{\mathbb {C}}(F)\) lives in \({\mathbb {C}}^5\) with coordinates \(x_4\), \(x_5\), \(x_8\), \(x_9\), \(x_{10}\). Thinking about toricity as a geometric notion, it makes sense to study the variety as an object in that lower dimensional space. Hence, consider
It turns out that \(V_{\mathbb {C}}(\hat{G})\) is shifted toric in \({\mathbb {C}}^5\).
Definition 13
(Compatible and canonical projection spaces) Let \(K \in \{{\mathbb {R}},{\mathbb {C}}\}\), let X be an ordered set of variables, and let \(V_K \ne \varnothing \) be a variety in \(K^{|X|}\). We say that a subset \(\hat{X} \subseteq X\) describes a compatible projection space \(K^{|\hat{X}|} \subseteq K^{|X|}\) with respect to \(V_K\) if for the projection \(\pi _{X \setminus \hat{X}}: K^{|X|} \rightarrow K^{|X \setminus \hat{X}|}\) into the complement of \(K^{|\hat{X}|}\) we have \(\pi _{X \setminus \hat{X}}(V_k) = \{\mathbf {0}\}\). In other words, for all \(x \in X \setminus \hat{X}\) and \(a \in V_K\) the x-coordinate of a equals 0. It is easy to see that there is a unique such \(\hat{X}\) with minimum cardinality, which, we say, describes the canonical projection space with respect to \(V_K\).
If \(\hat{X}\) describes a canonical projection space and \(\hat{X} \ne \varnothing \), then \(\pi _{\hat{X}}(V_K)^* \ne \varnothing \). On the other hand, if \(V_K^*\) is empty, and \(\hat{X}\) describes a compatible but not canonical projection space, then still \(\pi _{\hat{X}}(V_k)^* = \varnothing \). In that latter case the intuition is that the projection does not remove information from \(V_K\) that is relevant for obtaining \(\pi _{\hat{Y}}(V_K)^*\) in the canonical projection space described by \(Y \subseteq X\). When \(V_K\) is given as \(V_K(F)\) for \(F \subseteq {\mathbb {Q}}[X]\), then we write \(\hat{F} = F \cap {\mathbb {Q}}[\hat{X}]\), as we did with the Gröbner basis G in Example 12.
The principle domain of interest for us is \({\mathbb {R}}\)-space, where, e.g., concentrations of species are located in the interior of the first orthant. In the literature there has been considerable attention to \({\mathbb {C}}\)-space. We therefore start our algorithmic considerations over \({\mathbb {C}}\) in Sect. 3.1, and then turn to \({\mathbb {R}}\) in Sect. 3.2.
In Example 12 we could conclude that \(V_{\mathbb {C}}(\hat{F})^*\) is shifted toric because \(\hat{F}\) consists of binomials of the characteristic shape according to Proposition 7, and one can easily see from its linearity that it generates a prime ideal over \({\mathbb {C}}\). As prime ideal decomposition is related to polynomial factorization, decomposition or even primeness tests over our fields \({\mathbb {C}}\) and \({\mathbb {R}}\) of interest are not well supported in off-the-shelf computer algebra systems. In our algorithms we therefore limit ourselves to the properties “group” and “coset” rather than “toric” and “shifted toric”. Nevertheless, we will consider prime decompositions over \({\mathbb {Q}}\), which are well supported in software and provide at least partial decompositions over \({\mathbb {C}}\) and \({\mathbb {R}}\). Note that for us the relevant notion is prime decomposition in contrast to primary decomposition, as the former corresponds to the irreducibility of the corresponding varieties.
Example 14
(Comparison of \(V_{\mathbb {C}}^*\) with \(V_{\mathbb {R}}^*\)) For \(F_1=\langle x^2+2\rangle \), \(F_2=\langle (x^2-1)(x^2+2)\rangle \) the following holds:
-
(i)
\(V_{\mathbb {C}}(F_1)^*=\{i\sqrt{2},-i\sqrt{2}\}\) is a coset in \({\mathbb {C}}^*\), because \((-i\sqrt{2})^{-1}V_{\mathbb {C}}(F_1)^*=\{1, -1\}\) is a group. In contrast, \(V_{\mathbb {R}}(F_1)^*=\varnothing \) is not a coset in \({\mathbb {R}}^*\).
-
(ii)
\(V_{\mathbb {C}}(F_2)^*=\{1,-1,i\sqrt{2},-i\sqrt{2}\}\) is a coset in \({\mathbb {C}}^*\) if and only if it is group, due to \(1\in V_{\mathbb {C}}(F_2)^*\). This is not the case because it is not closed under multiplication: \((i\sqrt{2})(-i\sqrt{2})=2\notin V_{\mathbb {C}}(F_2)^*\). In contrast, \(V_{\mathbb {R}}(F_2)^*=\{1,-1\}\) is a group.
3.1 Classification over \({\mathbb {C}}\)
Our methods over \({\mathbb {C}}\) are, naturally, based on Gröbner bases [8, 25, 26], for which we rely on the commercial computer algebra system Maple. We generally leave it to Maple to find a good term order. Our classifications hold over any algebraically closed extension field of the coefficient field \({\mathbb {Q}}\), including \({\mathbb {C}}\) as well as, e.g., the countable algebraic closure of \({\mathbb {Q}}\).
With the following discussion of Algorithm 1 we will introduce some textbook facts from commutative algebra as lemmas, together with short proofs. The algorithm recognizes for a given ideal basis F whether \(V_{\mathbb {C}}(F)^*\) is a coset.

In line 1 we compute a Gröbner basis G of F. Recall from the previous section that we generally consider reduced Gröbner bases. We may safely assume that \({\text {vars}}(G)\subseteq {\text {vars}}(F)\). In line 2, the variables \(X'\) occurring as elements of G are exactly those that must be zero for all points in \(V_{\mathbb {C}}(F)\). Removing \(X'\) from X in line 3 yields \(\hat{X}\) which describes a compatible but not necessarily canonical projection space according to Definition 13, as the following example illustrates.
Example 15
Consider \(F = \{x_2^2, x_1+x_2, x_2+x_3+1\}\). Then for \(\hat{X} \subseteq X\) to describe the canonical projection space with respect to V(F) it must not contain \(x_2\). However, \(x_2\) does not show up in the Gröbner basis \(G = \{x_3^2+2x_3+1, x_2+x_3+1, x_1-x_3-1\}\) of F.
This idea of line 3 is to have a good heuristic method at no extra computational cost. Removing \(X'\) from G in line 4 is equivalent to plugging 0 into all \(X'\) in G, which in turn realizes the projection of \(V_{\mathbb {C}}(F)=V_{\mathbb {C}}(G)\) into \(\hat{X}\)-space. Note that we follow the convention that the empty set is a generator of the trivial ideal [3, Definition 1.36]. In line 5 we obtain \(\tilde{G}\) by saturating \(\hat{G}\) and subsequently taking the radical. In line 6 we call Algorithm 2 in order to apply Proposition 7 with \(I=\langle \hat{G}\rangle \) and \(G=\tilde{G}\).

In line 1 of Algorithm 2, if \(\hat{X}=\varnothing \), then we are in zero-dimensional \({\mathbb {C}}\)-space and certainly \(V_{\mathbb {C}}(\hat{G})^*=\varnothing \). Otherwise \(\tilde{G}=\{1\}\) is an equivalent criterion for \(V_{\mathbb {C}}(\hat{G})^*=\varnothing \) by Proposition 7. From line 3 on we know that \(V_{\mathbb {C}}(\hat{G})^*\ne \varnothing \) and apply in line 3 and line 5 the criteria from part (i) and (ii) of Proposition 7, respectively. In the negative case we return \(\texttt {X} \) in line 8.
This takes us back to line 7 of Algorithm 1. For convenience, we patch the classification letter \(\gamma \) from upper case to lower case when proper projection has taken place. That information could alternatively be reconstructed by comparing X with \(\hat{X}\), which is returned in line 10 along with \(\gamma \).
Example 16
(BIOMD0000000519) Consider \(F=\{f_1,f_2,f_3\}\subseteq {\mathbb {Q}}[X]\), where \(X=\{x_1,x_2,x_3\}\):
We obtain \(\hat{X}=X\) and \(\hat{G}=G=\{\hat{g}_1,\dots ,\hat{g}_4\}\). For space reasons, we present \(\hat{g}_1\), ..., \(\hat{g}_4\) with approximate coefficients here:
Notice that \(g_4\) is not binomial. After saturation we obtain \(\tilde{G}=\{\tilde{g}_1,\tilde{g}_2,\tilde{g}_3\}\) with
which is classified as \(\gamma =\texttt {C} \). Again, for \(\tilde{g}_3\) we computed exactly but present here only approximate coefficients.
It is important to understand that, although we are using tools from ideal theory, our results in Sect. 2 clarify that our classification solely depends on geometry. In particular, results are invariant with respect to the input ideal basis F in Algorithm 1.
In Appendix A.1 we discuss practical aspects of our implementation and give in Table 1 classification results from applying Algorithm 1 to the 129 models introduced at the beginning of this section. We also address there the quality of our heuristic method for computing the description \(\hat{X}\) of the projection space in Algorithm 1. For our discussion here we note that our algorithm terminates within a time limit of 6 hours per model on 104 out of the 129 models. We obtain 2 \(\texttt {G} \), 20 \(\texttt {C} \), and 6 \(\texttt {c} \), which can be summarized as \(V_{\mathbb {C}}(\tilde{G})^*\) forming a coset. Furthermore we have 4 \(\texttt {O} \) and 42 \(\texttt {o} \), i.e., \(V_{\mathbb {C}}(\tilde{G})^*=\varnothing \). The rest is 29 \(\texttt {X} \) and one single \(\texttt {x} \). In terms of percentages of the 104 successful computations this yields the following picture:

We are now going to turn to prime decompositions over \({\mathbb {Q}}\) of the generating ideals F of our varieties \(V_{\mathbb {C}}(F)\). Recall that shifted toricity requires, in addition to the coset structure of \(V_{\mathbb {C}}(F)^*\), irreducibility of \(V_{\mathbb {C}}(F)\), which in turn corresponds to prime decompositions of F even over \({\mathbb {C}}\). From that point of view, our decompositions considered here are only a heuristic step into the right direction. On the other hand, the following example suggests that beyond the irreducibility issue, prime decompositions over \({\mathbb {Q}}\) can improve our hit rate on cosets.
Example 17
Consider \(F\subseteq {\mathbb {Q}}[X]\), where \(X=\{x_1,\dots ,x_7, x_9\}\):
Applying Algorithm 1 to X and F yields \(\hat{X}=\{x_{1}, x_{2}, x_{4},\dots , x_{7}\}\), \(\hat{G}=\{x_{1} x_{7}, x_{4} x_{7}, x_{1} x_{5}-154 x_{4}, x_{1} x_{2}, x_{4} x_{6}, 27 x_{5} x_{6}-10 x_{7}, x_{2} x_{4}\}\), and the saturated radical basis \(\tilde{G}=\{1\}\). The classification result is \(\hat{X}\) together with \(\gamma =\texttt {o} \).
The following is a prime decomposition of F over \({\mathbb {Q}}\):
Considering each prime component individually yields respective compatible subsets of variables \(\hat{\mathcal {X}}=(\{x_{5}, x_{6}, x_{7}\}, \varnothing , \varnothing , \varnothing , \{x_{1}, x_{4}, x_{5}\})\) and Gröbner bases
which are already saturated. Application of Algorithm 2 to pairs of elements of \(\hat{\mathcal {X}}\) and \(\tilde{\mathcal {G}}\) yields \(\Gamma =(\texttt {c} ,\texttt {o} ,\texttt {o} ,\texttt {o} ,\texttt {c} )\). This tells us that \(V_{\mathbb {C}}(F)^*\) has two components, which live in different 3-dimensional subspaces of \({\mathbb {C}}^8\). Both of them are cosets.

Algorithm 3 formalizes the approach outlined in Example 17. We use the Weierstrass \(\wp \) for power sets. The algorithm starts with the computation of a prime decomposition in line 1. We have
Note that the obtained prime ideals \(\langle P_i \rangle \) are also radical.
Lemma 18
Let \(I\subseteq {\mathbb {Q}}[X]\) be a prime ideal. Then I is a radical ideal.
Proof
Let \(f^s\in I\). We show by induction on s that \(f\in I\). If \(s=1\), then we are done. Otherwise consider \(f^s=ff^{s-1}\in I\). Since I is prime, we have \(f\in I\) or \(f^{s-1}\in I\). In the latter case, \(f\in I\) by the induction hypothesis.
In lines 3–10, Algorithm 3 follows in a for-loop essentially Algorithm 1 for each prime component basis \(P_i\). In line 5 we note that \(\langle \hat{P}_i\rangle \) is prime by the following lemma.
Lemma 19
Let \(G\subseteq {\mathbb {Q}}[X]\) be a reduced Gröbner basis of a prime ideal \(\langle G\rangle \), and let \(x\in G\cap X\). Then \(\langle G\setminus \{x\}\rangle \) is prime.
Proof
Notice that \(\langle G\setminus \{x\}\rangle \) is the elimination ideal \(\langle G\rangle _x=\langle G\rangle \cap {\mathbb {Q}}[X\setminus \{x\}]\). Let \(fg\in \langle G\rangle _x\subseteq \langle G\rangle \). Then w.l.o.g. \(f\in \langle G\rangle \), because \(\langle G\rangle \) is prime. Since x does not occur in fg, it does not occur in f either. Hence \(f\in \langle G\rangle _x\). \(\square \)
It follows that \(\langle \hat{P}_i\rangle \) is also radical by Lemma 18. When computing \(\tilde{P}_i\) in line 6 primality is again preserved, as the following lemma shows.
Lemma 20
Let \(I\subseteq {\mathbb {Q}}[X]\) be a prime ideal, and let \(f\in {\mathbb {Q}}[X]\). Then \(I:\langle f\rangle ^\infty \) is a prime ideal.
Proof
Recall that \(I\subseteq I:\langle f\rangle ^\infty \). Let \(gh\in I:\langle f\rangle ^\infty \). We must show that \(g\in I:\langle f\rangle ^\infty \) or \(h\in I:\langle f\rangle ^\infty \). By definition there is \(s\in {\mathbb {N}}\) such that \(f^sgh\in I\). If \(f^s\in I\), then \(I:\langle f\rangle ^\infty =\langle 1\rangle \), which is prime. Otherwise \(gh\in I\) and therefore \(g\in I\subseteq I:\langle f\rangle ^\infty \) or \(h\in I\subseteq I:\langle f\rangle ^\infty \). \(\square \)
We once more call Lemma 18 to obtain that \(\langle \tilde{P}_i\rangle \) is also radical. Therefore, the radical ideal computation in line 5 of Algorithm 1 is not necessary here.
In Appendix A.2 we discuss practical aspects of our computations and give in Table 3 classification results using Algorithm 3 on the 129 models introduced at the beginning of this section. We succeed on 105 out of the 129 models within a time limit of 6 hours per model. This yields 3426 prime components to test altogether. We obtain 2 \(\texttt {G} \), 22 \(\texttt {C} \), and 1085 \(\texttt {c} \), which can be summarized as \(V_{\mathbb {C}}(\tilde{P}_i)^*\) forming a coset. Furthermore, we have 2242 \(\texttt {o} \), i.e., \(V_{\mathbb {C}}(\tilde{P}_i)^*=\varnothing \). The rest is only 34 \(\texttt {X} \) and 41 \(\texttt {x} \). Again we visualize these results in terms of percentages of the total of 3426 prime components:

Recall that our selection from the BioModels repository presented here is essentially complete with respect to polynomial examples. This comes with the disadvantage that our data is somewhat dominated by BIOMD0000000281, which contributes 1008 \(\texttt {c} \) and 2136 \(\texttt {o} \). We have verified that the ideal dimensions for the 1008 \(\texttt {c} \) components are positive, pointing at non-trivial coset structures in contrast to isolated points. For the sake of scientific rigor we also present the statistics without BIOMD0000000281:

3.2 Classification over \({\mathbb {R}}\)
Our primary tool over \({\mathbb {R}}\) is real quantifier elimination [12, 13, 38, 65, 69, 70]. We use implementations by the fourth author and his students [21, 59] in Redlog [20, 57, 60,61,62], which is integrated with the open-source computer algebra system Reduce [42, 43]. Our strategy is to apply virtual substitution methods [48, 49, 70] for quantifier elimination within the relevant degree bounds and fall back into partial cylindrical algebraic decomposition [19, 56] with subproblems where this is not possible. Our results hold over any real-closed field, including \({\mathbb {R}}\) as well as, e.g, the countable field of real algebraic numbers.
Algorithm 4 is the real counterpart to Algorithm 1 in Sect. 3.1.

In line 4 we construct for each \(x_i\in X\) the first-order \(L_\text {OR}\)-formula, where \(L_\text {OR}\) denotes the language of ordered rings:
The underlined universal quantifier denotes the universal closure, which universally quantifies all variables freely occurring within its scope. Our formula \(\psi \) straightforwardly states that for all points in \(V_{\mathbb {R}}(\hat{F})\) with coordinates \(x_j\in X\), which occur as variables in the polynomials \(f\in \hat{F}\), the specific coordinate \(x_i\) is zero. The if-condition \({\mathbb {R}}\models \psi \) expresses that \({\mathbb {R}}\) is a model of this formula, meaning that the formula holds in \({\mathbb {R}}\) or, equivalently, in the model class of real closed fields.
A real quantifier elimination procedure computes for any given first-order \(L_\text {OR}\)-formula \(\varphi \) an equivalent quantifier-free \(L_\text {OR}\)-formula \(\varphi '\), where the variables in \(\varphi '\) are a subset of the variables freely occurring in \(\varphi \). Since \(\psi \) contains no free occurrences of variables, the corresponding \(\psi '\) will be variable-free and can be easily simplified to either \({\text {true}}\) or \({\text {false}}\). In the former case the if-condition holds, in the latter case it does not.
When some \(x_i\) is identified to vanish in all points of \(V_{\mathbb {R}}(\hat{F})\) it is removed from \(\hat{X}\) in line 5. Notice that in contrast to Algorithm 1 the final \(\hat{X}\) describes not only a compatible but the canonical projection space with respect to \(V_{\mathbb {R}}(F)\). Accordingly, \(x_i\) is set to zero within \(\hat{F}\) in line 6, where \([x_i/0]\) is a postfix operator substituting the term 0 for the variable \(x_i\) in its argument \(\hat{F}\). From line 9 on, Algorithm 4 proceeds like its complex counterpart Algorithm 1 but using Algorithm 5 for real classification.

In line 1 we define \(\Phi (t_1,\dots ,t_n)\) to generate a first order \(L_\text {OR}\)-formula which states that \((t_1,\dots ,t_n)\in V_{\mathbb {R}}(\hat{F})\), where the \(t_i\) are \(L_\text {OR}\)-terms. In lines 2–4 we handle the case \(V_{\mathbb {R}}(\hat{F})^*=\varnothing \). Hence in line 5 we know \(V_{\mathbb {R}}(\hat{F})^*\ne \varnothing \). We are going to use the following characterization of cosets.
Proposition 21
Let \(K^*\) be a multiplicative group. Let \(C\subseteq (K^*)^n\), \(C\ne \varnothing \). Then the following are equivalent:
-
(i)
C is a coset;
-
(ii)
there exists \(g_0\in (K^*)^n\) such that \(g_0^{-1}C\) is a group;
-
(iii)
there exists \(g_0\in C\) such that \(g_0^{-1}C\) is a group;
-
(iv)
for all \(g\in C\) we have that \(g^{-1}C\) is a group.
Proof
The equivalence between (i) and (ii) is the definition of a coset. When (ii) holds, then \(C=g_0G\) for a group G, hence \(g_0\cdot 1\in C\), which shows (iii). The implication from (iii) to (ii) is obvious, and so is the implication from (iv) to (iii). It remains to be shown that (iii) implies (iv).
Assume that \(g_0\in C\) and \(G=g_0^{-1}C\) is a group; equivalently \(C = g_0G\). Let \(g\in C\). Then there is \(y\in G\) such that \(g=g_0y\). It follows that \(g^{-1}C=(g_0y)^{-1}C=y^{-1}g_0^{-1}C=y^{-1}G=G\). \(\square \)
Proposition 21(iv) yields a first-order characterization for \(V_{\mathbb {R}}(\hat{F})^*\) to be a coset, which could be informally stated as follows:
As a first-order \(L_\text {OR}\)-formula this yields:
In the equations originating from \(\Phi (g_1x_1^{-1},\dots ,g_nx_n^{-1})\) principal denominators containing variables from \(x_1\), ..., \(x_n\) can be equivalently dropped, because the left hand side of the implication requires those variables to be different from zero. The first-order \(L_\text {OR}\)-formula \(\tau \) can be equivalently transformed into \(\tau _{\text {inv}}\wedge \tau _{\text {mult}}\) with \(\tau _{\text {inv}}\) and \(\tau _{\text {mult}}\) as in line 5 and line 9 of Algorithm 5, respectively. Therefore it is correct to exit with \(\gamma =\texttt {X} \) in line 7 or 11 when either part does not hold. This splitting into subproblems has two advantages. First, separate quantifier eliminations on smaller problems are more efficient. Second, when \(\tau _{\text {inv}}\) does not hold in line 6, then \( \tau _{\text {mult}}\) need not be considered at all.
When reaching line 13, we know that \(V_{\mathbb {R}}(\hat{F})^*\) is a coset and apply the following corollary, which concludes our discussion of Algorithm 5.
Corollary 22
Let C be a coset. Then C is group if and only if \(1\in C\).
Proof
If \(1\in C\), then \(C=1^{-1}C\) is a group by Proposition 21(iv). The converse implication follows from the definition of a group.
Remark 23
As an alternative to (5), Proposition 21(iii) yields the following characterization of cosets, which might appear more natural because it is closer to the original definition of cosets:
The first difference to observe is that in (6) in contrast to (5) there is quantifier alternation from \(\exists \) to \(\forall \). The number of quantifier alternations is known to be a critical parameter for asymptotic complexity of the real quantifier elimination problem [38, 69]. Furthermore, in the presence of the leading existential quantifier prohibits our splitting into two independent smaller problems. Experimental computations on the complete dataset considered here have confirmed that formulation (5) is clearly preferable.
Example 24
(BIOMD0000000159) Consider \(F\subseteq {\mathbb {Q}}[X]\), where \(X=\{x_1,\dots ,x_3\}\):
In lines 3–8 of Algorithm 4 we consecutively apply real quantifier elimination to the following formulas:
Neither of them holds in \({\mathbb {R}}\) so that in line 9 we enter Algorithm 5 with \(\hat{X}=X\) and \(\hat{F}=F\).
In line 2 of Algorithm 5 we test
Real quantifier elimination [48] confirms that (7) holds in \({\mathbb {R}}\), and extended quantifier elimination [49] even gives us a witness
Therefore we set up \(\tau _{\text {inv}}\) in line 5 as follows:
Notice that in the three equations in last line of (9) we have equivalently dropped denominators \(x_1x_2\), \(x_2x_3\), and \(x_1x_3\), respectively. The inequalities for \(x_1\), ..., \(x_3\) in first line of (9) ensure that those denominators do not vanish. In line 10, quantifier elimination confirms that \(\tau _{\text {inv}}\) holds in \({\mathbb {R}}\), and so does \(\tau _{\text {mult}}\) in line 10. Thus we reach line 13 and set up the following formula to test whether our coset \(\hat{F}\) is even a group:
This is obviously not the case. Algorithm 5 returns ‘\(\texttt {C} \)’ in line 17, and Algorithm 4 finally returns \(\{x_1,x_2,x_3\}\) and ‘\(\texttt {C} \)’ in line 13.
In Appendix A.1 we discuss practical aspects of our implementation and give in Table 1 classification results from applying Algorithm 4 to the 129 models introduced at the beginning of this section. For our discussion here we note that our algorithm terminates within a time limit of 6 hours per model on 94 out of the 129 models. We obtain 20 \(\texttt {C} \) and 6 \(\texttt {c} \), which can be summarized as \(V_{\mathbb {R}}(\tilde{G})^*\) forming a coset. Furthermore we have 4 \(\texttt {O} \) and 42 \(\texttt {o} \), i.e., \(V_{\mathbb {R}}(\tilde{G})^*=\varnothing \). The rest is 21 \(\texttt {X} \) and one single \(\texttt {x} \). In terms of percentages of the 94 successful computations this gives the following picture:

In analogy to Algorithm 3 in Sect. 3.1, Algorithm 6 applies prime decompositions over \({\mathbb {Q}}\) also in the real case.

It starts with the computation of a prime decomposition in line 1. We then have
In lines 3–4 we apply Algorithm 4 to each component and collect the results.
In Appendix A.2 we discuss practical aspects of our computations and give in Table 3 classification results using Algorithm 6 on the 129 models introduced at the beginning of this section. We succeed on 88 out of the 129 models within a time limit of 6 hours per model. This yields 3390 prime components to test altogether. We obtain 2 \(\texttt {G} \), 22 \(\texttt {C} \), and 1083 \(\texttt {c} \), which can be summarized as \(V_{\mathbb {R}}(\tilde{P}_i)^*\) forming a coset. Furthermore, we have 7 \(\texttt {O} \) and 2232 \(\texttt {o} \), i.e., \(V_{\mathbb {R}}(\tilde{P}_i)^*=\varnothing \). The rest is only 18 \(\texttt {X} \) and 26 \(\texttt {x} \). In left hand side picture below, we visualize these results in terms of percentages of the total of 3390 prime components. In the right hand side picture, we see the corresponding statistics without BIOMD0000000281:

Recall from the discussion at the end of Sect. 3.1 that we consider the left hand side picture more adequate and add the right hand side one for the sake of scientific rigor.
4 Upper Complexity Bounds
In this section we give asymptotic upper bounds on the worst case complexity of problems addressed in this paper. In Sect. 4.1 we derive bounds for recognizing toric and shifted toric varieties over algebraically closed fields of characteristic zero. In Sect. 4.2 we derive corresponding bounds for toric varieties over real closed fields. Section 4.3 finally gives bounds for the membership problem in subgroups of \(({\overline{{\mathbb {Q}}}}^*)^n\), which correspond to binomial varieties.
4.1 Toricity over Algebraically Closed Fields of Characteristic Zero
As mentioned in Sect. 2, a torus G can be represented as the set of solutions of binomials of the form \(x_1^{a_{1i}}\cdots x_n^{a_{ni}}=1\), \(1\le i\le n-m\), where \(a_{ji}\in {\mathbb {Z}}\) and m is equal to the dimension of G and every Gröbner basis of a toric variety \(\overline{G}\) consists only of binomials of the form \(x_1^{b_{1i}}\cdots x_n^{b_{ni}}- x_1^{c_{1i}}\cdots x_n^{c_{ni}}\) where integers \(b_{ji}\), \(c_{ji}\) are non-negative [63].
Let \(f_1\), ..., \(f_k\in {\mathbb {Z}}[x_1,\ldots ,x_n]\) and \(V\subseteq {\mathbb {C}}^n\) be the algebraic variety of common zeroes of \(f_1\), ..., \(f_k\). We design an algorithm which recognizes whether \(V\) is toric. Note that \(f_1\), ..., \(f_k\) are not necessary binomials. To estimate the complexity of the algorithm we suppose that \(\deg (f_i)\le d\), \(1\le i\le k\) and that the bit-size of each integer coefficient of \(f_1\), ..., \(f_k\) does not exceed L. Invoking [10, 37] we first verify whether \(V\) is irreducible and \(\overline{V^*}=V\) (if this is not true then \(V\) is not toric). The complexity of the algorithms from [10, 37] can be bounded by \((Ld^{n^2})^{O(1)}\). Then we verify that \(V^*\) is a group. This holds if and only if we have the following first-order formula in the theory of algebraically closed fields of characteristic zero:
This can be verified via the algorithm in [11]. The complexity of this step is bounded by \((Ld^{n^2})^{O(1)}\) as well.
So far, the algorithm has verified whether \(V\) is toric. Now we show how to find a system of binomial equations determining \(V^*\). In order to do so, in this subsection we find a set of Laurent binomials determining \(V^*\) instead of binomials in \({\mathbb {C}}[X]\) whose set of solutions is \(V\). This is because as it has been shown by Mayr and Meyer in their seminal work, the number of binomials and their degrees in a Gröbner basis of \(I(V)\) can be double-exponential [50]. Using the algorithms from [10, 37] one can produce \(m=\dim V\) coordinates among \(x_1\), ..., \(x_n\) which form a transcendental basis of \(V^*\). Without loss of generality, assume that \(\{x_1,\dots ,x_m\}\) be a transcendental basis. Fix an integer j, \(m<j\le n\) and project \(V^*\) on the space generated by \(x_1\), ..., \(x_m\), \(x_j\), which is isomorphic to \(({\mathbb {C}}^*)^{m+1}\) invoking again [11]. Let \(W\subseteq ({\mathbb {C}}^*)^{m+1}\) be image of the projection. Due to the choice of the transcendental basis, we have that \(\dim W=m\) and W is a hypersurface. Therefore, W can be determined by a single polynomial \(h:=h_j\in {\mathbb {Z}}[x_1,\dots ,x_m, x_j]\) (c.f. e.g., [58]). Moreover, \(\deg W\le \deg V^*\le d^n\); the latter follows from Bezout inequality [58]. The algorithm from [11] constructs h and a generic point of W within the complexity \((Ld^{n^2})^{O(1)}\).
Observe that W is also a group. Hence h can be rewritten as a binomial of the form \(x_1^{q_{j1}}\cdots x_m^{q_{jm}}\cdot x_j^{q_j} -1 \in {\mathbb {Z}}[x_1^{\pm },\ldots ,x_n^{\pm }]\) for suitable relatively prime integers \(q_{j1}\), ..., \(q_{jm}\), \(q_j \in {\mathbb {Z}}\). Doing so for every j, \(m<j\le n\), the algorithm yields polynomials \(h_j \in {\mathbb {Z}}[x_1,\ldots ,x_n]\). Denote by \(H \subseteq ({\mathbb {C}}^*)^n\) the variety given by equations \(h_j\), \(m<j\le n\). Clearly, \(V^*\subseteq H\), \(\dim H=m\) and H is a group, therefore, \(V^*\) is an irreducible component of H. Moreover, H is a binomial variety and hence, \(V^*\) is its subgroup (of a finite index). In particular, \((1,\dots ,1)\in V^*\), and every irreducible component \(H_1\) of H has the form \(H_1=gV^*\) for an arbitrary element \(g\in H_1\). Moreover, one can choose g such that its coordinates are roots of unity [40, Remark 3.1, Remark 5.2].
In addition, in order to obtain the Laurent binomials defining \(V^*\), the algorithm finds a \({\mathbb {Z}}\)-basis of the intersection \({\mathbb {Q}}(Q_{m+1},\dots ,Q_n) \cap {\mathbb {Z}}^n\) of the \({\mathbb {Q}}\)-linear space generated by vectors \(Q_j=(q_{j1},\dots ,q_{jm},0,\dots ,0,q_j,0\dots ,0)\), \(m<j\le n\) with the grid \({\mathbb {Z}}^n\) [40, Remark 3.1]. To find that \({\mathbb {Z}}\)-basis, the algorithm first applies [22, 31] to produce (within polynomial complexity) a \({\mathbb {Z}}\)-basis Z of the space of integer solutions of the linear system with rows \(Q_j\), \(m<j\le n\), and subsequently applies [22, 31] to construct a \({\mathbb {Z}}\)-basis of the linear system with the rows from Z.
Recall from the Definition 4 that for a torus \(V^*\subseteq ({\mathbb {C}}^*)^n\) and a point \(g\in ({\mathbb {C}}^*)^n\) we call \(gV^*\) a shifted torus, and \(\overline{gV^*}\subseteq {\mathbb {C}}^n\) a shifted toric variety. In particular, every irreducible component of a binomial variety in \(({\mathbb {C}}^*)^n\) is a shifted torus (Proposition 3). One can modify the described algorithm to test whether an input variety \(V\subseteq {\mathbb {C}}^n\) is shifted toric. To this end, pick an arbitrary point \(g=(g_1,\dots ,g_n)\in V^*\) and test whether \(g^{-1}V^*\) is a torus. If the latter holds, the algorithm produces binomial equations for \(g^{-1}V^*\). Clearly a binomial equation \(x_1^{s_1}\cdots x_n^{s_n}=1\) vanishes on \(g^{-1}V^*\) if and only if \(x_1^{s_1}\cdots x_n^{s_n}=g_1^{s_1}\cdots g_n^{s_n}\) vanishes on \(V^*\) .
The following theorem summarizes our algorithm.
Theorem 25
Let \(f_1\), ..., \(f_k\in {\mathbb {Z}}[x_1,\ldots ,x_n]\), \(\deg (f_i)\le d\), \(1\le i\le k\) with bit-sizes of integer coefficients of \(f_1\), ..., \(f_k\) at most L. One can design an algorithm which tests whether the variety \(V\subseteq {\mathbb {C}}^n\) determined by \(f_1\), ..., \(f_k\) is (shifted) toric. In the positive case, the algorithm yields a transcendental basis \(x_{i_1}\), ..., \(x_{i_m}\), \(m=\dim V\) of \(V\). It furthermore yields binomial equations defining \(V^*=V\cap ({\mathbb {C}}^*)^n\). Each binomial equation has the form \(x_1^{s_1}\cdots x_n^{s_n}=g_1^{s_1}\cdots g_n^{s_n}\) for all \((g_1,\dots ,g_n)\in V^*\) and for suitable integers \(s_1\), ..., \(s_n\in {\mathbb {Z}}\) satisfying \(|s_i|<O(d^{n^2})\). The complexity of the designed algorithm does not exceed \((Ld^{n^2})^{O(1)}\).
One can extend the algorithm in Theorem 25 so that it takes a reducible variety \(V\) and decomposes V into irreducible components and then tests whether its irreducible components are toric or shifted toric (following the lines of the algorithm for each irreducible component of \(V^*\) separately). Moreover, if the irreducible components of \(V\) are exclusively toric and shifted toric varieties and \(V^*\) is a group, then the extended algorithm yields the described representation of \(V^*\) by means of binomials. The complexity of the extended algorithm is still \((Ld^{n^2})^{O(1)}\).
Our discussion here can be straightforwardly generalized to any algebraically closed field with characteristic zero. Independently, the algorithm can be generalized to coefficients from a finite field extension of \({\mathbb {Q}}\) [10, 37].
4.2 Toricity over Real Closed Fields
In this subsection we design an algorithm that recognizes toricity of a semi-algebraic set over \({\mathbb {R}}\). We refer to [2] for the algorithms in real algebraic geometry. Let \({\mathbb {R}}_{>0}:=\{\,z\in {\mathbb {R}}\mid z>0\,\}\) denote the positive orthant. Keeping the notations from Sect. 4.1 consider the semi-algebraic set \(T:=\{\,x\in ({\mathbb {R}}_{>0})^n\mid f_i(x)\ge 0, 1\le i\le k\,\}\). Modify (10) replacing \({\mathbb {C}}^*\) by \({\mathbb {R}}_{>0}\) and equalities \(f_i=0\) by inequalities \(f_i\ge 0\), respectively. Also keep the first-order formula (10). This formula can be verified by applying the algorithms from [39]. Clearly, (10) is true if and only if T is a group (a torus). Thus, assume that (10) is true. Then the image of the coordinate-wise logarithm map \(\log (T)\subseteq {\mathbb {R}}^n\) is a linear subspace. Hence, in particular, T is connected.
First, compute \(m:=\dim (T)\) and produce m coordinates such that the projection U of T on m-dimensional space with these coordinates has the full dimension m. Without loss of generality assume that these coordinates are \(x_1\), ..., \(x_m\). Fix j, \(m<j\le n\) and denote by \(U_j\) the projection of T on the \((m+1)\)-dimensional space with coordinates \(x_1\), ..., \(x_m\), \(x_j\). Denote by p the projection map of the latter space along \(x_j\) onto m-dimensional space with the coordinates \(x_1,\dots ,x_m\). Then \(p(U_j)=U\). Since \(\dim (U_j)=\dim (U)=m\), we have that \(p(\log (U_j))=\log (U)={\mathbb {R}}^m\), and therefore we conclude that any point of U has a unique preimage of p in \(U_j\). Moreover, \(U_j\) is determined by a single binomial-type (analytic) equation of the form
for some reals \(t_{j1}\), ..., \(t_{jm}\), \(t_j\), \(c_j\). Since \(U_j\) is a group we get that \(c_j=1\).
On the other hand, applying the algorithm from [2], one can construct the projection \(p:U_j\rightarrow U\) and conclude that equation (11) is algebraic, thus \(t_{j1}\), ..., \(t_{jm}\), \(t_j \in {\mathbb {Z}}\). The algorithm also yields \(t_{j1}\), ..., \(t_{jm}\), \(t_j\). Note that without loss of generality one can assume that they are relatively prime, otherwise divide by their greatest common divisor. The complexity of the algorithm is again \((Ld^{n^2})^{O(1)}\). Doing so for each j, \(m<j\le n\), the algorithm yields binomial equations of the form (11) which determine T uniquely. Similar to Sect. 4.1 one can produce a \({\mathbb {Z}}\)-basis of the intersection of \({\mathbb {Q}}\)-linear space generated by vectors \((t_{j1},\dots ,t_{jm},0,\dots ,0,t_j,0\dots ,0)\) with the grid \({\mathbb {Z}}^n\). Then any vector \((s_1,\dots ,s_n)\) from this basis provides a binomial \(X_1^{s_1}\cdots X_n^{s_n}-1\) that vanishes on T. The above \({\mathbb {Z}}\)-basis need not be constructed, since binomials of the form (11) already determine T uniquely. We summarize the described algorithm in the following theorem.
Theorem 26
Let \(f_1\), ..., \(f_k\in {\mathbb {Z}}[x_1,\dots ,x_n]\), \(\deg (f_i)\le d\), \(1\le i\le k\) with bit-sizes of integer coefficients of \(f_1\), ..., \(f_k\) at most L. One can design an algorithm which tests whether the semi-algebraic set \(T:=\{\,x\in ({\mathbb {R}}_{>0})^n\mid f_i(x)\ge 0, 1\le i\le k\,\}\) is a group (a torus). In the positive case, the algorithm yields coordinates \(x_{i_1}\), ..., \(x_{i_m}\), where \(m=\dim (T)\), such that the dimension of the projection of T on the m-dimensional space with the coordinates \(x_{i_1}\), ..., \(x_{i_m}\) equals m. It furthermore yields for each \(j\notin \{i_1,\dots ,i_m\}\) a binomial equation of the form \(x_1^{t_{j1}}\cdots x_m^{t_{jm}}\cdot x_j^{t_j}=1\) which vanishes on T, with relatively prime \(t_{j1}\), ..., \(t_{jm}\), \(t_j \in {\mathbb {Z}}\), where \(|t_{j1}|+\cdots +|t_{jm}|+|t_j|\le d^{O(n)}\). The complexity of the algorithm does not exceed \((Ld^{n^2})^{O(1)}\).
Similar to Subsect. 4.1, our results here can be generalized to arbitrary real closed field.
4.3 Membership in Binomial Varieties
Let a group \(G\subset (\overline{{\mathbb {Q}}}^*)^n\) be given by binomial equations \(x_1^{a_{i,1}}\cdots x_n^{a_{i,n}}=1\), \(1\le i\le k\), where \(a_{i,j}\in {\mathbb {Z}}\), \(|a_{i,j}|\le d\). Let \(v=(v_1,\dots ,v_n)\in {\mathbb {Q}}^n\) be a point such that the absolute values of the numerators and denominators of \(v_1\), ..., \(v_n\) do not exceed M. We design an algorithm which tests whether \(v\in \overline{G}\). Recall that \(\overline{G}\) is a binomial variety, and it is a toric variety when G is irreducible.
Theorem 27
There is an algorithm which tests whether a point v belongs to a binomial variety \(\overline{G}\) with its complexity bounded by
-
(i)
\((k\cdot \log M \cdot (dn)^n)^{O(1)}\) and by
-
(ii)
\((k\cdot M\cdot n\cdot \log d)^{O(1)}\).
Proof
Permuting the coordinates, assume w.l.o.g. that \(v=(0,\dots ,0,v_{s+1},\dots ,v_n)\), where \(v_{s+1}\cdots v_n \ne 0\). Due to Claim 5.3 in [40], \(v\in \overline{G}\) if and only if there exist a point \(u=(u_1,\dots ,u_s,v_{s+1},\dots ,v_n)\in G\) and positive \(0<b_1,\dots ,b_s\in {\mathbb {Z}}\) such that
and for all \(t\ne 0\), i.e., a shift of a one-parametric subgroup, we have that \((u_1\cdot t^{b_1},\dots ,u_s\cdot t^{b_s},v_{s+1},\dots ,v_n) \in G\). Then (12) is equivalent to the existence of \(u\in G\) and a one-parametric subgroup \(\{\,(t^{b_1},\dots ,t^{b_s},1,\dots ,1) \mid t\ne 0\,\} \subseteq G\). The existence of the latter is equivalent to the existence of a non-negative vector \((b_1,\dots ,b_s,0,\dots ,0)\) orthogonal to the vectors \((a_{i,1},\dots ,a_{i,n})\), \(1\le i\le k\). This can be checked by means of linear programming.
The existence of a point \(u\in G\) satisfying (12) is equivalent to the existence of non-zero \(u_1\), ..., \(u_s\in \overline{{\mathbb {Q}}}^*\) satisfying the binomial equations
One can apply the algorithm in [41] to this system and transform the \(k\times s\) submatrix \(A=(a_{i,j})\), \(1\le i\le k\), \(1\le j\le s\) to its Smith form. Then solvability of (13) is equivalent to that the right-hand side of (13) fulfils (at most k) relations of the form
for some integers \(c_i\) being suitable minors of matrix A, hence \(|c_i|\le (ds)^{O(s)}\) by Hadamard’s inequality.
One can verify relations (14) using the binary form of the numerators and denominators of \(v_{s+1}\), ..., \(v_n\). This leads to the complexity bound (i). Alternatively, one can factorize the numerators and denominators of \(v_{s+1}\), ..., \(v_n\) and execute calculations in terms of exponents of their prime factors which leads to the complexity bound (ii). This completes the verification of (12) and the description of the algorithm. \(\square \)
One can extend the complexity bound (i) for \(v_j\in \overline{{\mathbb {Q}}}\), \(1\le j\le n\) being algebraic numbers. In this case \(\log M\) plays the role of the bit-size of the representation of v.
5 Conclusions and Future Work
We have taken a geometric approach to studying steady state varieties, which—besides significant theoretical results—generated comprehensive empirical data from computations on 129 networks from BioModels repository. We are not aware of any comparable systematic large scale symbolic computations on those data in the literature. We were indeed surprised by the success rate of Gröbner basis and real quantifier elimination techniques with input sizes up to 71 variables. We find this most encouraging and believe that robust and supported software tools for systems biology and medicine that include symbolic computation components are not out of reach.
It was important to learn that real methods do not significantly fall behind complex methods efficiency-wise. After all, chemical reaction network theory takes place in the interior of the positive first orthant. In a way, our consideration of \(V^*\) in favor of V here marks a first step in that direction by looking at points in the variety rather than polynomials in the ideal. Only real methods allow to go further and, e.g., identify prime components whose varieties reach into the first orthant.
Our work here gives a number of quite concrete challenges to be considered in subsequent work. To start with, one must complete the step from “coset” to “shifted toric” in practical software by producing suitable prime decompositions beyond decompositions over \({\mathbb {Q}}\). As mentioned above, real methods allow to explicitly refer to the interior of the first orthant, and our framework and the first-order descriptions we use should be refined in this direction. On the complex side, one should also test suitable elimination methods with the logic descriptions we developed here.
It is noteworthy that all quantifier elimination problems considered here were decision problems, even without quantifier alternation. On the one hand, this allows the application of methods and tools from Satisfiability Modulo Theories Solving [1, 52]. On the other hand, it shows that we are not yet using the full power of quantifier elimination methods. One could, e.g., leave a subset of reaction rates parametric and study invariance of shifted toricity under variation of those reaction rates.
Our input of 129 models considered here is in a way complete: We took all available models from BioModels/ODEbase for which we could straightforwardly produce polynomial vector fields. So far we did not consider systems with rational vector fields. Such systems come with interesting challenges on the algebraic side: While the variety V is blind for the presence or non-presence of polynomials factors from the denominators, those factors can still affect shifted toricity \(V^*\).
Notes
Maple (2019). Maplesoft, a division of Waterloo Maple Inc., Waterloo, Ontario.
References
Ábrahám, E., Abbott, J., Becker, B., Bigatti, A.M., Brain, M., Buchberger, B., Cimatti, A., Davenport, J.H., England, M., Fontaine, P., Forrest, S., Griggio, A., Kroening, D., Seiler, W.M., Sturm, T.: SC2: satisfiability checking meets symbolic computation. In: Kohlhase, M., Johansson, M., Miller, B., de Moura, L., Tompa, F. (eds.) Intelligent Computer Mathematics. CICM 2016. LNCS, vol. 9791, pp. 28–43. Springer, Berlin (2016). https://doi.org/10.1007/978-3-319-42547-4_3
Basu, S., Pollack, R., Roy, M.-F.: Algorithms in Real Algebraic Geometry. Algorithms and Computation in Mathematics, vol. 10. Springer, Berlin (2006). https://doi.org/10.1007/3-540-33099-2
Becker, T., Weispfenning, V., Kredel, H.: Gröbner Bases: A Computational Approach to Commutative Algebra. Graduate Texts in Mathematics, vol. 141. Springer, Berlin (1993). https://doi.org/10.1007/978-1-4612-0913-3
Boltzmann, L.: Lectures on Gas Theory. University of California Press, Berkeley (1964)
Boulier, F., Fages, F., Radulescu, O., Samal, S.S., Schuppert, A., Seiler, W., Sturm, T., Walcher, S., Weber, A.: The SYMBIONT project: symbolic methods for biological networks. ACM Commun. Comput. Algebra 52(3), 67–70 (2018). https://doi.org/10.1145/3313880.3313885
Boulier, F., Fages, F., Radulescu, O., Samal, S.S., Schuppert, A., Seiler, W., Sturm, T., Walcher, S., Weber, A.: The SYMBIONT project: symbolic methods for biological networks. F1000Research (2018). https://doi.org/10.7490/f1000research.1115995.1
Bradford, R.J., Davenport, J.H., England, M., Errami, H., Gerdt, V.P., Grigoriev, D., Hoyt, C., Košta, M., Radulescu, O., Sturm, T., Weber, A.: Identifying the parametric occurrence of multiple steady states for some biological networks. J. Symb. Comput. 98, 84–119 (2019). https://doi.org/10.1016/j.jsc.2019.07.008
Buchberger, B.: Ein Algorithmus zum Auffinden der Basiselemente des Restklassenringes nach einem nulldimensionalen Polynomideal. Doctoral dissertation, Mathematical Institute, University of Innsbruck, Austria (1965)
Chelliah, V., Juty, N., Ajmera, I., Ali, R., Dumousseau, M., Glont, M., Hucka, M., Jalowicki, G., Keating, S., Knight-Schrijver, V., Lloret-Villas, A., NathNatarajan, K., Pettit, J.-B., Rodriguez, N., Schubert, M., Wimalaratne, S.M., Zhao, Y., Hermjakob, H., Le Novère, N., Laibe, C.: BioModels: ten-year anniversary. Nucl. Acids Res. 43(D1), D542–D548 (2015). https://doi.org/10.1093/nar/gku1181
Chistov, A.L.: Algorithm of polynomial complexity for factoring polynomials and finding the components of varieties in subexponential time. J. Sov. Math. 34(4), 1838–1882 (1986). https://doi.org/10.1007/BF01095643
Chistov, A.L., Grigor’ev, D.Y.: Complexity of quantifier elimination in the theory of algebraically closed fields. In: Chytil, M.P., Koubek, V. (eds.) MFCS 1984: Mathematical Foundations of Computer Science. LNCS, vol. 176, pp. 17–31. Springer, Berlin (1984). https://doi.org/10.1007/BFb0030287
Collins, G.E.: Quantifier elimination for the elementary theory of real closed fields by cylindrical algebraic decomposition. In: Brakhage, H. (ed.) Automata Theory and Formal Languages. 2nd GI Conference. LNCS, vol. 33, pp. 134–183. Springer, Berlin (1975). https://doi.org/10.1007/3-540-07407-4_17
Collins, G.E., Hong, H.: Partial cylindrical algebraic decomposition for quantifier elimination. J. Symb. Comput. 12(3), 299–328 (1991). https://doi.org/10.1016/S0747-7171(08)80152-6
Conradi, C., Iosif, A., Kahle, T.: Multistationarity in the space of total concentrations for systems that admit a monomial parametrization. Bull. Math. Biol. 81(10), 4174–4209 (2019). https://doi.org/10.1007/s11538-019-00639-4
Conradi, C., Kahle, T.: Detecting binomiality. Adv. Appl. Math. 71, 52–67 (2015). https://doi.org/10.1016/j.aam.2015.08.004
Cox, D., Little, J., O’Shea, D.: Ideals, Varieties and Algorithms. Undergraduate Texts in Mathematics. Springer, Berlin (1992). https://doi.org/10.1007/978-1-4757-2181-2
Craciun, G., Dickenstein, A., Shiu, A., Sturmfels, B.: Toric dynamical systems. J. Symb. Comput. 44(11), 1551–1565 (2009). https://doi.org/10.1016/j.jsc.2008.08.006
Davenport, J.H., Heintz, J.: Real quantifier elimination is doubly exponential. J. Symb. Comput. 5(1–2), 29–35 (1988). https://doi.org/10.1016/S0747-7171(88)80004-X
Dolzmann, A., Seidl, A., Sturm, T.: Efficient projection orders for CAD. In: Gutierrez, J. (ed.) ISSAC 2004: Proceedings of the 2004 International Symposium on Symbolic and Algebraic Computation, pp. 111–118. ACM, New York, NY (2004). |https://doi.org/10.1145/1005285.1005303
Dolzmann, A., Sturm, T.: Redlog: computer algebra meets computer logic. ACM SIGSAM Bull. 31(2), 2–9 (1997). https://doi.org/10.1145/261320.261324
Dolzmann, A., Sturm, T.: Simplification of quantifier-free formulae over ordered fields. J. Symb. Comput. 24(2), 209–231 (1997). https://doi.org/10.1006/jsco.1997.0123
Dumas, J.-G., Saunders, B.D., Villard, G.: On efficient sparse integer matrix Smith normal form computations. J. Symb. Comput. 32(1–2), 71–99 (2001). https://doi.org/10.1006/jsco.2001.0451
Einstein, A.: Strahlungs-emission und -absorption nach der Quantentheorie. Verh. Dtsch. Phys. Ges. 18, 318–323 (1916)
Eisenbud, D., Sturmfels, B.: Binomial ideals. Duke Math. J. 84(1), 1–45 (1996). https://doi.org/10.1007/s10463-010-0290-9
Faugère, J.-C.: A new efficient algorithm for computing Gröbner bases (F4). J. Pure Appl. Algebra 139(1–3), 61–88 (1999). https://doi.org/10.1145/780506.780516
Faugère, J.-C.: A new efficient algorithm for computing gröbner bases without reduction to zero (F5). In: Mora, T. (ed.) ISSAC 2002: Proceedings of the 2002 International Symposium on Symbolic and Algebraic Computation, pp 75–83. ACM, New York, NY (2002) https://doi.org/10.1145/780506.780516
Feinberg, M.: Complex balancing in general kinetic systems. Arch. Ration. Mech. Anal. 49(3), 187–194 (1972). https://doi.org/10.1007/BF00255665
Feinberg, M.: Stability of complex isothermal reactors—I. The deficiency zero and deficiency one theorems. Chem. Eng. Sci. 42(10), 2229–2268 (1987). https://doi.org/10.1016/0009-2509(87)80099-4
Feinberg, M.: Foundations of Chemical Reaction Network Theory. Applied Mathematical Sciences, vol. 202. Springer, Berlin (2019). https://doi.org/10.1007/978-3-030-03858-8
Finney, A., Hucka, M.: Systems biology markup language: level 2 and beyond. Biochem. Soc. Trans. 31(6), 1472–1473 (2003). https://doi.org/10.1042/bst0311472
Frumkin, M.A.: An application of modular arithmetic to the construction of algorithms for solving systems of linear equations. Dokl. Akad. Nauk SSSR 229(5), 1067–1070 (1976)
Fulton, W.: Introduction to Toric Varieties. Annals of Mathematics Studies, vol. 131. Princeton University Press, Princeton, NJ (1993). https://doi.org/10.1515/9781400882526
Gatermann, K.: Counting stable solutions of sparse polynomial systems in chemistry. In: Green, E.L., Hoşten, S., Laubenbacher, R.C., Powers, V.A. (eds.) Symbolic Computation: Solving Equations in Algebra, Geometry, and Engineering. Contemporary Mathematics, vol. 286, pp. 53–69. AMS, Providence, RI (2001). https://doi.org/10.1090/conm/286/04754
Gatermann, K., Wolfrum, M.: Bernstein’s second theorem and Viro’s method for sparse polynomial systems in chemistry. Adv. Appl. Math. 34(2), 252–294 (2005). https://doi.org/10.1016/j.aam.2004.04.003
Gorban, A.N., Mirkes, E.M., Yablonski, G.S.: Thermodynamics in the limit of irreversible reactions. Physica A 392(6), 1318–1335 (2013). https://doi.org/10.1016/j.physa.2012.10.009
Gorban, A.N., Yablonski, G.S.: Extended detailed balance for systems with irreversible reactions. Chem. Eng. Sci. 66(21), 5388–5399 (2011). https://doi.org/10.1016/j.ces.2011.07.054
Grigor’ev, D.Y.: Factorization of polynomials over a finite field and the solution of systems of algebraic equations. J. Sov. Math. 34(4), 1762–1803 (1986). https://doi.org/10.1007/BF01095638
Grigor’ev, D.Y.: Complexity of deciding Tarski algebra. J. Symb. Comput. 5(1–2), 65–108 (1988). https://doi.org/10.1016/S0747-7171(88)80006-3
Grigor’ev, D.Y., Vorobjov, N.N.: Solving systems of polynomial inequalities in subexponential time. J. Symb. Comput. 5(1–2), 37–64 (1988). https://doi.org/10.1016/S0747-7171(88)80005-1
Grigoriev, D., Milman, P.D.: Nash resolution for binomial varieties as Euclidean division. A priori termination bound, polynomial complexity in essential dimension 2. Adv. Math. 231(6), 3389–3428 (2012). https://doi.org/10.1016/j.aim.2012.08.009
Grigoriev, D., Weber, A.: Complexity of solving systems with few independent monomials and applications to mass-action kinetics. In: Gerdt, V.P., Koepf, W., Mayr, E.W., Vorozhtsov, E.V. (eds.), Computer Algebra in Scientific Computing: 14th International Workshop, CASC 2012. Maribor, Slovenia, September 3–6, 2012. Proceedings, LNCS, vol. 7442, pp. 143–154. Springer (2012). https://doi.org/10.1007/978-3-642-32973-9_12
Hearn, A.C.: Reduce—a user-oriented system for algebraic simplification. ACM SIGSAM Bull. 1(6), 50–51 (1967)
Hearn, A.C.: Reduce: the first forty years. In: Dolzmann, A., Seidl, A., Sturm, T. (eds.) Algorithmic Algebra and Logic: Proceedings of the A3L 2005, April 3–6, Passau, Germany. Books on Demand, Norderstedt, Germany (2005)
Horn, F., Jackson, R.: General mass action kinetics. Arch. Ration. Mech. Anal. 47(2), 81–116 (1972). https://doi.org/10.1007/BF00251225
Hucka, M., Finney, A., Sauro, H.M., Bolouri, H., Doyle, J.C., Kitano, H., Arkin, A.P., Bornstein, B.J., Bray, D., Cornish-Bowden, A., Cuellar, A.A., Dronov, S., Gilles, E.D., Ginkel, M., Gor, V., Goryanin, I.I., Hedley, W.J., Hodgman, T.C., Hofmeyr, J.-H., Hunter, P.J., Juty, N.S., Kasberger, J.L., Kremling, A., Kummer, U., Le Novère, N., Loew, L.M., Lucio, D., Mendes, P., Minch, E., Mjolsness, E.D., Nakayama, Y., Nelson, M.R., Nielsen, P.F., Sakurada, T., Schaff, J.C., Shapiro, B.E., Shimizu, T.S., Spence, H.D., Stelling, J., Takahashi, K., Tomita, M., Wagner, J., Wang, J.: The systems biology markup language (SBML): a medium for representation and exchange of biochemical network models. Bioinformatics 19(4), 524–531 (2003). https://doi.org/10.1093/bioinformatics/btg015
Kahle, T.: Decompositions of binomial ideals. Ann. Inst. Stat. Math. 62(4), 727–745 (2010). https://doi.org/10.1007/s10463-010-0290-9
Kahle, T.: Decompositions of binomial ideals. J. Softw. Algebra Geom. 4(1), 1–5 (2012). https://doi.org/10.1007/s10463-010-0290-9
Košta, M.: New concepts for real quantifier elimination by virtual substitution. Doctoral dissertation, Saarland University, Germany (2016)
Košta, M., Sturm, T., Dolzmann, A.: Better answers to real questions. J. Symb. Comput. 74, 255–275 (2016). https://doi.org/10.1016/j.jsc.2015.07.002
Mayr, E.W., Meyer, A.R.: The complexity of the word problems for commutative semigroups and polynomial ideals. Adv. Math. 46(3), 305–329 (1982). https://doi.org/10.1016/0001-8708(82)90048-2
Müller, S., Feliu, E., Regensburger, G., Conradi, C., Shiu, A., Dickenstein, A.: Sign conditions for injectivity of generalized polynomial maps with applications to chemical reaction networks and real algebraic geometry. Found. Comput. Math. 16(1), 69–97 (2016). https://doi.org/10.1007/s10208-014-9239-3
Nieuwenhuis, R., Oliveras, A., Tinelli, C.: Solving SAT and SAT modulo theories: from an abstract Davis–Putnam–Logemann–Loveland procedure to DPLL(T). J. ACM 53(6), 937–977 (2006). https://doi.org/10.1145/1217856.1217859
Onsager, L.: Reciprocal relations in irreversible processes. I. Phys. Rev. 37(4), 405 (1931). https://doi.org/10.1103/PhysRev.37.405
PérezMillán, M., Dickenstein, A.: The structure of MESSI biological systems. SIAM J. Appl. Dyn. Syst. 17(2), 1650–1682 (2018). https://doi.org/10.1137/17M1113722
Pérez Millán, M., Dickenstein, A., Shiu, A., Conradi, C.: Chemical reaction systems with toric steady states. Bull. Math. Biol. 74(5), 1027–1065 (2012). https://doi.org/10.1007/s11538-011-9685-x
Seidl, A.: Cylindrical decomposition under application-oriented paradigms. Doctoral dissertation, University of Passau, Germany (2006)
Seidl, A.M., Sturm, T.: Boolean quantification in a first-order context. In: V.G. Ganzha, E.W. Mayr, E.V. Vorozhtsov (eds.) Proceedings of the 6th International Workshop on Computer Algebra in Scientific Computing, CASC 2003, pp. 329–345. Institut für Informatik, Technische Universität München, Garching, Germany (2003)
Shafarevich, I.R.: Basic Algebraic Geometry. Grundlehren der mathematischen Wissenschaften, vol. 213. Springer, Berlin (1974). https://doi.org/10.1007/978-3-642-96200-4
Sturm, T.: Real quantifier elimination in geometry. Doctoral dissertation, University of Passau, Germany (1999)
Sturm, T.: New domains for applied quantifier elimination. In: V.G. Ganzha, E.W. Mayr, E.V. Vorozhtsov (eds.) Computer Algebra in Scientific Computing: 9th International Workshop, CASC 2006, Chisinau, Moldova, September 11–15, 2006. Proceedings, LNCS, vol. 194, pp. 295–301. Springer (2006). https://doi.org/10.1007/11870814_25
Sturm, T.: REDLOG online resources for applied quantifier elimination. Acta Acad. Ab. 67(2), 177–191 (2007)
Sturm, T.: A survey of some methods for real quantifier elimination, decision, and satisfiability and their applications. Math. Comput. Sci. 11(3–4), 483–502 (2017). https://doi.org/10.1007/s11786-017-0319-z
Sturmfels, B.: Gröbner Bases and Convex Polytopes. University Lecture Series, vol. 8. AMS, Providence, RI (1996). https://doi.org/10.1090/ulect/008
Tange, O.: GNU parallel: the command-line power tool. login USENIX Mag. 36(1), 42–47 (2011)
Tarski, A.: Decision method for elementary algebra and geometry. Prepared for publication by J. C. C. McKinsey. RAND Report R109, August 1, 1948: Revised May 1951, 2nd edn. RAND, Santa Monica, CA, 1957
Voit, E.O., Martens, H.A., Omholt, S.W.: 150 years of the mass action law. PLoS Comput. Biol. 11(1), e1004012 (2015). https://doi.org/10.1371/journal.pcbi.1004012
Wang, S., Lin, J.-R., Sontag, E.D., Sorger, P.K.: Inferring reaction network structure from single-cell, multiplex data, using toric systems theory. PLoS Comput. Biol. 15(12), e1007311 (2019). https://doi.org/10.1371/journal.pcbi.1007311
Wegscheider, R.: Über simultane Gleichgewichte und die Beziehungen zwischen Thermodynamik und Reactionskinetik homogener Systeme. Monatsh. Chem. Verw. Tl. 22(8), 849–906 (1901). https://doi.org/10.1007/BF01517498
Weispfenning, V.: The complexity of linear problems in fields. J. Symb. Comput. 5(1–2), 3–27 (1988). https://doi.org/10.1016/S0747-7171(88)80003-8
Weispfenning, V.: Quantifier elimination for real algebra—the quadratic case and beyond. Appl. Algebra Eng. Commun. 8(2), 85–101 (1997). https://doi.org/10.1007/s002000050055
Acknowledgements
Open access funding provided by Projekt DEAL. This work has been supported by the bilateral project ANR-17-CE40-0036/DFG-391322026 SYMBIONT [5, 6]. The first author is grateful to grant RSF-16-11-10075 and to MCCME for the inspiring atmosphere. Stephen Forrest at Maplesoft and Arthur Norman at the University of Cambridge greatly helped with Maple- and Reduce-related technical issues, respectively. Christoph Lüders at the University of Bonn greatly supported the project with discussions around and generation of suitable input data.
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Electronic supplementary material
Below is the link to the electronic supplementary material.
Computations on 129 Models from the BioModels Repository
Computations on 129 Models from the BioModels Repository
We conducted our computations on a 2.40 GHz Intel Xeon E5-4640 with 512 GB RAM and 32 physical cores providing 64 CPUs via hyper-threading. For parallelization of the jobs for the individual models we used GNU Parallel [64]. Results are stored in an Sqlite3 database file, which contains considerably more information than can be presented here in print (Online Resource 1). Beyond our own computations the database imports data from BioModels and ODEbase, so that our models and the history of our input can be reliably tracked. For instance, we store the mappings between our variables and the original species names and even the original SBML file with each model.
Among the information imported from ODEbase there is a binary flag indicating whether or not a model has mass action kinetics [66] according to the following criterion [29, Section 2.1.2].
Definition 28
(Mass Action Test) A system is considered a mass action system when the kinetic law is made up of the product of the concentrations of the reactant species to the power of their respective stoichiometry times a constant.
1.1 Classifications of the Original Systems
We start with the classification over \({\mathbb {C}}\) and \({\mathbb {R}}\) of the original, not decomposed, systems using algorithms from Sects. 3.1 and 3.2, respectively. For comments on the tables from a theoretical point of view compare those sections.
Beyond the data presented here we generally save the sets X, \(\hat{X}\). Furthermore, over \({\mathbb {C}}\) we save the computed Gröbner bases G, \(\hat{G}\), \(\tilde{G}\) and their term orders, and over \({\mathbb {R}}\) we save witnesses for \(V_{\mathbb {R}}^*\ne \varnothing \).
Recall that over \({\mathbb {C}}\), \(\hat{X}\) describes only compatible projection spaces, while over \({\mathbb {R}}\) it describes the canonical projection space.
Remark 29
Let \(F \subseteq {\mathbb {Q}}[X]\). Let \(Y_{\mathbb {R}}\), \(Y_{\mathbb {C}}\subseteq X\) describe the canonical projection spaces with respect to \(V_{\mathbb {R}}(F)\), \(V_{\mathbb {C}}(F)\), respectively. Let furthermore \(\hat{X}\) describe any compatible projection space with respect to \(V_{\mathbb {C}}(F)\). Then \(Y_{\mathbb {R}}\subseteq Y_{\mathbb {C}}\subseteq \hat{X}\) and thus \(|Y_{\mathbb {R}}| \le |Y_{\mathbb {C}}| \le |\hat{X}|\). Using the fact that all sets are finite, \(|\hat{X}| = |Y_{\mathbb {R}}|\) implies \(\hat{X} = Y_{\mathbb {C}}\).
Recall that \(\hat{X}\) as computed in Algorithm 1 describes only a compatible projection space with respect to the complex variety, while \(\hat{X}\) as computed in Algorithm 4 describes the canonical projection space with respect to the real variety. The idea with Algorithm 1 was to have a heuristic method to efficiently obtain a description of the canonical projection space also there. Remark 29 tells us that whenever we find equal numbers for \(|\hat{X}|\) over \({\mathbb {C}}\) and \({\mathbb {R}}\) in Table 1 below, then that heuristic method was successful. This is the case with all models where the computation terminated over both \({\mathbb {C}}\) and \({\mathbb {R}}\) except for the models 243 and 289.
Since we obtain \(\texttt {X} \) in contrast to \(\texttt {O} \) with model 289, we know that \(\hat{X}\) describes a canonical projection space over \({\mathbb {C}}\) also there. With model 243, our obtained \(\hat{X}\) indeed does not describe the canonical projection space over \({\mathbb {C}}\). Inspection of the computation shows that the Gröbner basis G in l.1 of Algorithm 1 contains \(x_6^2\). An improved heuristic method could check for powers of variables occurring in G. However, Example 15 shows that this would still be only heuristic.
There are 15 models where the complex classification in Table 1 succeeded but the real classification timed out: 028, 030, 069, 102, 103, 122, 226, 230, 257, 287, 335, 365, 491, 492, 637. Among those, models 491 and 492 have classification \(\texttt {G} \) and models 230, 335, and 265 have classification \(\texttt {o} \) over \({\mathbb {C}}\), from which we can conclude that they have the same classification over \({\mathbb {R}}\), respectively.
Vice versa, there are 5 models where real classification succeeded but complex classification timed out: 332, 334, 430, 431, 581.
There is one single model where we succeeded over both \({\mathbb {C}}\) and \({\mathbb {R}}\) but obtained different classifications: model 289 has \(\texttt {X} \) over \({\mathbb {C}}\) but \(\texttt {o} \) over \({\mathbb {R}}\).
Table 2 collects some statistical information about the computations. Figure 1 provides some analysis of the computation times. Notice that many computations finish quite quickly.
1.2 Classifications of Rational Prime Decompositions
Recall that Algorithm 3 and Algorithm 6 compute prime decompositions \(\mathcal {P}\) over \({\mathbb {Q}}\) and then apply our classification approach to each prime component individually. This yields lists \(\mathcal {X}\), \(\hat{\mathcal {X}}\) containing in turn lists X and \(\hat{X}\) of variables before and after projection, respectively, as well as a list \(\Gamma \) of classifications \(\gamma \). We have \(|\mathcal {X}|=|\hat{\mathcal {X}}|=|\Gamma |=|\mathcal {P}|\), and elements can be matched by position. Since this information is too comprehensive to be displayed in a table, we give only \(|\mathcal {P}|\) and summarize the numbers of occurrences of the various classifications in \(\Gamma \). Our database, of course, stores the complete information.
There are 17 models where the complex classification in Table 3 succeeded but the real classification timed out: 002, 028, 030, 038, 046, 069, 102, 103, 108, 122, 173, 226, 230, 270, 287, 439, 637. Vice versa, there are no models where the classification succeeded over \({\mathbb {R}}\) but not over \({\mathbb {C}}\). There are 8 models where we succeeded over both \({\mathbb {C}}\) and \({\mathbb {R}}\) but obtained different classifications: 091, 105, 188, 189, 227, 289, 292, 559. All those differences are visible in the summaries \(\Gamma _{\text {summary}}\) in Table 3. Model 289 is \(\texttt {o} +\texttt {X} \) over \({\mathbb {C}}\) but \(2\texttt {o} \) over \({\mathbb {R}}\). We have addressed this difference already with the computations in Appendix A.1. With all other models listed above the difference is \(\texttt {o} \) over \({\mathbb {C}}\) in contrast to \(\texttt {O} \) over \({\mathbb {R}}\).
Table 4 collects some statistical information about the computations. Figure 2 provides some analysis of the computation times. Notice that many computations finish quite quickly.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Grigoriev, D., Iosif, A., Rahkooy, H. et al. Efficiently and Effectively Recognizing Toricity of Steady State Varieties. Math.Comput.Sci. 15, 199–232 (2021). https://doi.org/10.1007/s11786-020-00479-9
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11786-020-00479-9
Keywords
- Binomial ideals
- Chemical reaction networks
- Complexity bounds
- Complex balancing
- Gröbner bases
- Mass-action kinetics
- Real quantifier elimination
- Scientific computing
- Symbolic computation
- Toric varieties