Abstract
The Internet of Things (IoT) is a new para-digm for achieving ubiquitous connectivity by enormously deploying physical objects like sensors, actuators, and controllers. Wireless communication is one of the main enabling technologies that make the IoT a reality. However, due to the open nature of wireless communication and constraints on energy consumption, this raises concerns about the security of the IoT. Eavesdropping is a major threat to the wireless communications security. To counteract such an attack, physical layer security is among the promising solutions. The aim of this work is to evaluate the secrecy performance of two-hop wireless communication systems. This evaluation is done in the presence of potential eavesdropping threats over Nakagami-m and mixed Rayleigh–Nakagami-m fading channels. To enhance the security of the system, the use of cooperative jamming and opportunistic relaying has been considered. In particular, based on classical probability theory, we first analyze the secrecy outage performance for scenario 1, where all channels (S-R, R-D, R-R, S-E, R-E) experience Nakagami-m fading. Then, we examine the secrecy performance for scenario 2, where the channel coefficients for links (S-R, R-D, S-E, R-E) are subject to Nakagami-m fading and the channel coefficients for the link (R-R) follow Rayleigh fading. Finally, simulation and numerical results are presented to validate our theoretical achievements. The results suggest that as the fading parameter m increases, the probability of secrecy outages decreases, leading to an improvement in the security performance of the wireless IoT data collection process.







Similar content being viewed by others
References
Zanella, A., et al. (2014). Internet of things for smart cities. IEEE Internet of Things Journal, 1(1), 22–32.
Akpakwu, G. A., et al. (2018). A survey on 5G networks for the internet of things: Communication technologies and challenges. IEEE Access, 6, 3619–3647.
Wang, H. M., & Xia, X.-G. (2015). Enhancing wireless secrecy via cooperation: Signal design and optimization. IEEE Communications Magazine, 53(12), 47–53.
Koyluoglu, O. O., & El Gamal, H. (2012). Polar coding for secure transmission and key agreement. IEEE Transactions on Information Forensics and Security, 7(5), 1472–1483.
Atzori, L., Iera, A., et al. (2010). The internet of things: A survey. Computer networks, 54(15), 2787–2805.
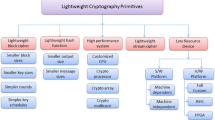
Mousavi, S. K., et al. (2021). Security of internet of things based on cryptographic algorithms: A survey. Wireless Networks, 27(2), 1515–1555.
Gao, H., Qiu, B., Barroso, R., Duranm J., Hussain, W., Xu, Y., & Wang, X. (2022). TSMAE: A novel anomaly detection approach for Internet of Things time series data using memory-augmented autoencoder. IEEE Transactions on Network Science and Engineering.PP. 1-1.
Bloch, M., et al. (2012). Special issue on physical-layer security. Journal of Communications and Networks, 14(4), 349–351.
Mathur, S., et al. (2010). Exploiting the physical layer for enhanced security [security and privacy in emerging wireless networks]. IEEE Wireless Communications, 17(5), 63–70.
Dong, L., Han, Z., Petropulu, A. P., & Poor, H. V. (2010). Improving wireless physical layer security via cooperating relays. IEEE Transactions on Signal Processing, 58(3), 1875–1888.
Bloch, M., et al. (2008). Wireless information-theoretic security. IEEE Transactions on Information Theory, 54(6), 2515–2534.
Cai, C., Cai, Y., Zhou, X., Yang, W., & Yang, W. (2014). When does relay transmission give a more secure connection in wireless ad hoc networks? IEEE Transactions on Information Forensics and Security, 9(4), 624–632.
Lei, H., Gao, C., Guo, Y., & Pan, G. (2015). On physical layer security over generalized gamma fading channels. IEEE Communications Letters, 19(7), 1257–1260.
Mathur, A., Ai, Y., Bhatnagar, M. R., Cheffena, M., & Ohtsuki, T. (2018). On physical layer security of \(\alpha -\eta -\kappa -\mu\) fading channels. IEEE Communications Letters, 22(10), 2168–2171.
Pandey, A., & Yadav, S. (2018). Physical layer security in cooperative AF relaying networks with direct links over mixed Rayleigh and double-Rayleigh fading channels. IEEE Transactions on Vehicular Technology, 67(11), 10615–10630.
Si, J., Li, Z., Cheng, J., & Zhong, C. (2019). Secrecy performance of multi-antenna wiretap channels with diversity combining over correlated Rayleigh fading channels. IEEE Transactions on Wireless Communications, 18(1), 444–458.
Tang, J., et al. (2020). On the security-reliability and secrecy throughput of random mobile user in internet of things. IEEE Internet of Things Journal, 7(10), 10635–10649.
Lei, H., et al. (2020). Safeguarding UAV IoT communication systems against randomly located eavesdroppers. IEEE Internet of Things Journal, 7(2), 1230–1244.
Lee, D. (2021). Secrecy analysis of relay-user selection in AS-AF systems over Nakagami fading channels. IEEE Transactions on Vehicular Technology, 70(3), 2378–2388.
Gao, H., Liu, C., Yin, Y., Xu, Y., & Li, Y. (2022). A hybrid approach to trust node assessment and management for VANETs cooperative data communication: Historical interaction perspective. IEEE Transactions on Intelligent Transportation Systems, 23(9), 16504–16513.
Lee, D. (2022). The impact of channel imperfection and multiple eavesdroppers on security of dual-signal selection in AF-relay systems. Wireless Networks, 28(4), 1531–1540.
Gao, H., Liu, C., Li, Y., & Yang, X. (2021). V2VR: Reliable hybrid-network-oriented V2V data transmission and routing considering RSUs and connectivity probability. IEEE Transactions on Intelligent Transportation Systems, 22(6), 3533–3546.
Dongo, I., et al. (2021). A qualitative and quantitative comparison between Web scraping and API methods for Twitter credibility analysis. International Journal of Web Information Systems, 17(6), 580–606.
Dhanani, J., Mehta, R., & Rana, D. P. (2021). Legal document recommendation system: A dictionary based approach. International Journal of Web Information Systems, 17(3), 187–203.
Zhang, X., Wang, W., & Ji, X. (2009). Multiuser diversity in multiuser two-hop cooperative relay wireless networks: System model and performance analysis. IEEE Transactions on Vehicular Technology, 58(2), 1031–1036.
Ram, M. C. (2004). Ad hoc wireless networks: Architectures and protocols .... Portable Documents, Pearson Education.
Lin, Z., et al. (2016). Opportunistic relaying and jamming with robust design in hybrid full/half-duplex relay system. EURASIP Journal on Wireless Communications and Networking, 2016(1), 1–10.
Zheng, G., Choo, L., & Wong, K. (2011). Optimal cooperative jamming to enhance physical layer security using relays. IEEE Transactions on Signal Processing, 59(3), 1317–1322.
Zwillinger, D., & Jeffrey, A. (Eds.). (2007). Table of integrals, series, and products. Amsterdam: Elsevier.
Zhang, Y., Shen, Y., Wang, H., Yong, J., & Jiang, X. (2016). On secure wireless communications for IoT under eavesdropper collusion. IEEE Transactions on Automation Science and Engineering, 13(3), 1281–1293.
Funding
No funds, grants, or other support was received.
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest
Authors declare that they have no conflict of interest.
Ethical approval
This article does not contain any studies with human participants or animals performed by any of the authors.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendix A: Proof of Lemma 2
Appendix A: Proof of Lemma 2
From the definition of event B, we can write
In this scenario 2, the channel coefficients \(|h_{i,j}|^{2}\) for (S-R, R-D, S-E, R-E) are Gamma distributed, whereas the channel coefficients \(|h_{i,j}|^{2}\) for (R-R) are exponentially distributed. Therefore, the cdf, i.e., \(P (V_{j} \le V_{i})\) in (8), will also be exponentially distributed. By following the same procedure as for scenario 1, \(P(|h_{S,R_{c}}|^{2}<z)\) in (8), becomes equal to \(\int _{0}^{\infty }uP\Big (\vert h_{S,R_{i}}\vert ^{2}<z, V_{i}=t\Big ) (1-e^{-2t})^{u-1}dt\) for scenario 2. Now, by applying the total probability law, we obtain
After substituting \(z = \alpha \sum \limits _{j\in \mathcal {J}}|h_{R_{j},R_{c}}|^{2}|J^{n}_{1}\) in (29), rearranging and taking expectation by using the pdf of \(|h_{R_{j},R_{c}}|^{2}\) for any \(j\in \mathcal {J}\) given below, Lemma 2 follows.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Devi, P., Bharti, M.R. Physical layer security for IoT over Nakagami-m and mixed Rayleigh–Nakagami-m fading channels. Wireless Netw 29, 3479–3491 (2023). https://doi.org/10.1007/s11276-023-03422-5
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11276-023-03422-5