Abstract
This article deals with the pricing of double-barrier options monitored discretely. A continuity correction method is established to provide an analytical approximation for the price of such discrete options under the Black–Scholes model. We achieve this by applying the smooth-fit principle simultaneously to the two flat boundaries (barriers) associated. The resulting correction form still involves adjustments in the levels of barriers, but the amounts adjusted can be different for different boundaries. More interestingly, the shift for each boundary can also be in different directions, which depends largely on the position of the current level relative to the two boundaries. Numerical examples are provided as well which support our theoretical achievements.
Similar content being viewed by others
Avoid common mistakes on your manuscript.
1 Introduction
In this paper, we seek to price discrete options with two barriers. In particular, a double-barrier option is a derivative contract that is activated or extinguished when the underlying asset goes far beyond a pre-specified price interval at least once during the option life. Options with barrier features are cheaper than plain options and hence are common in structured products. As mentioned in Bernard et al. (2008), 25.7% of equity-linked notes have their payments driven by a triggered event based on the trajectory of the underlying stock.
The pricing of double-barrier options has been studied for quite a long time, and dates back to Kunitomo and Ikeda (1992). Since then, various studies have been conducted, such as Geman and Yor (1996); Pelsser (2000) under the Black–Scholes (BS) model and Cai et al. (2009) under a jump diffusion model. A recent development for Lévy-driven models is found in Boyarchenkoy and Levendorskiĭ (2012). These works all posit that the barriers are monitored continuously. However, in most real cases, barriers are imposed only at discrete points of time. Such discretely monitored path-dependent options are usually referred to as discrete options.
A pioneer and famous work in mathematical finance for discrete options is Broadie et al. (1997), which documents that under the BS setting, there are significant price errors between barrier options with and without continuous monitoring. More importantly, they further show such errors can be mitigated by a technique called continuity correction. Specifically, the price of a discrete barrier option can be approximately determined by the corresponding continuous-time pricing formula with a simple shift in the barrier level. The amount of shift is related to the expectation of “overshoot,” the excess price of the underlying asset over the barrier when such a breach is observed for the first time. As far as we know, this is the only technique that gives analytical approximations; otherwise, we resort to numerical methods; see (Milev & Tagliani, 2010; Golbabai et al., 2014; Ahmadian & Ballestra, 2015; Ahmadian et al., 2021) for references.Footnote 1
Other applications of continuity correction to option pricing include (Broadie et al., 1999) for lookback options, Lai et al. (2007) for American options, Fuh et al. (2013) for a jump-diffusion model, and Dia and Lamberton (2011) for exponential Lévy models. Nevertheless, these studies concern only single barriers. For two barriers at a time, it is generally expected that applying the same result in Broadie et al. (1997) to each barrier separately would be sufficient. This is also conjectured in Hörfelt (2003), but we still lack solid estimates of the approximation error. Hence, in this article we attempt to fill this gap by showing that the correction for two simultaneous barriers is different from that for a single barrier. The method involves not only the expected overshoot but also the probabilities of hitting the barrier.
Indeed, continuity correction for so-called chained options was established in Jun (2013), which deals with a typical barrier option but activated by the hitting of another primary barrier. For example, the \(DIC _u\) is a down-and-in call option activated when the price of the underlying asset hits an upper barrier. This case belongs to a type of option with two barriers, but is not exactly the same as what we here call double-barrier options. Other types of options with two barriers can be found in Li (1999). Notice that correction for chained options seems to be more straightforward because it allows the reflection principle to be sequentially applied at each barrier. As for the double barrier, we instead follow the PDE (partial differential equation) approach initiated by Keener (2013), who (implicitly) introduces the principle of smooth fitFootnote 2 from free-boundary problems (see Shepp & Shiryaev 1993 for example) to the study of boundary effects such as ours. The central idea of Keener’s approach is that only “non-smoothness” on boundaries necessitates correction for the overshoot effect in order to improve the convergence brought about by discretization in the time domain. We here extend his technique from one boundary to two simultaneous boundary conditions.
The idea of continuity correction can also be utilized in the reverse fashion. For instance, if in a continuous-time structural form model we seek to estimate a default probability via a simulation approach, which is clearly of a discrete nature, then we can shrink the distance to default to improve the efficiency of estimation. This practice is usually termed boundary correction. One relevant example can be found in Gobet and Menozzi (2010), where the authors begin with a multidimensional framework with a finite time domain and consider a general diffusion process. They also conclude that one should shift the boundary inward along a normal by the same amount as the aforementioned expected overshoot when adopting a Euler discretization scheme in a Monte-Carlo simulation to estimate an expectation of a continuous entity. In this study, by contrast, we borrow a continuous-time formula through a joint Laplace transform to approximate its discrete counterpart. As a result, we face a problem with an infinite time domain which then yields different correction results. More briefly, their boundary-correction technique in a numerical scheme is not totally equivalent to the continuity correction we seek. Here, our concern is more about how the correction should be incorporated into the existing formula, which in turn requires further properties with respect to asymptotic independence.
This work contributes to the literature in three main aspects. First, this is the first study to establish continuity correction for the pricing of double-barrier options. The correction result also shifts the barrier but may do so either farther or closer, relatively to the initial starting point. Additionally, the shifted amount for each barrier can be uneven. We do not observe both in a single-barrier case. Second, the boundary effect from the overshoot is no longer sufficiently captured by a linear expansion; now, to simultaneously account for non-smoothness at two points, it is instead a cubic polynomial; see (2.19). Nevertheless, the price approximation achieved between a discrete double-barrier option and its continuous correspondent is still a first-order approximation in light of renewal theory. Namely, the improved convergence rate is merely \(o\left( 1/\sqrt{m}\right)\) per the literature. Here m stands for the boundary monitoring frequency during the contract life. Last, we extend asymptotic properties of a typical renewal measure to the double-boundary case; see a battery of lemmas in the appendix.
The rest of the article is organized as follows. Section 2 introduces the working model and formulates our correction problem relevant to the pricing of double-barrier options. Section 3 then presents the main theoretical results, especially of continuity correction for the joint moment generating function of the discrete first passage time and its associated overshoot. Simple illustrative numerical examples are given in Sect. 4, and the final section concludes the paper. Some proofs are deferred to the appendices.
2 Problem formulation
Here, we will formulate the correction problem associated with the pricing of discrete double-barrier options, during which we will also illustrate the methodology and outline the key steps to achieve our final correction goal.
2.1 Model
We start with the classic Black–Scholes (BS) model; that is to say, we consider an underlying asset \(S_t\) whose price dynamics under the risk-neutral measure are
where r is the constant risk-free rate, \(\sigma\) is the constant volatility, and \(W_t\) is a one-dimensional standard Brownian motion. Let \(X_t=\log (S_t/S_0)\) denote the log-return process; then it is well-known that
Also, by the celebrated Lévy–Khintchine formula, we have for \(\theta \in {\mathbb {R}}\), \(E[e^{\theta \,X_t}]=\exp \left\{ G(\theta )\,t\right\}\) with
Next, it is easy to see that for any \(\alpha >0\), the equation \(G(\theta )=\alpha\) has exactly two roots:
Clearly, \(\beta _{1,\alpha }<0<\beta _{2,\alpha }\). In addition, we have \(\beta _{2,\alpha }>1\) if \(\alpha >r\) and
in which
Note that \(\gamma\) has the same sign as the drift of \(X_t\). Finally, we will use \({\mathcal {F}}_t\) to denote the natural filtration generated by the process \(X_t\).
2.2 Option pricing
Throughout this paper, we will take the pricing of a knock-in double-barrier call (KIC) as our illustrative example to demonstrate the central idea and the correction results. The payoff of a such option at the maturity date T (\(>0\)) generally looks like
where K is the strike price, \(1_{\{\cdot \}}\) stands for the indicator function, and \(\tau\) is the associated first-hitting time. If the barriers are monitored continuously, \(\tau\) is
for two constants (barriers) L, H such that \(L<S_0<H\). Otherwise, it is
where \(\varDelta t=T/m\) for some given monitoring frequency m. Namely, the barriers are imposed only at m discrete points of time: \(\varDelta t\), \(2\varDelta t\), \(\ldots\), \(m\varDelta t=T\).
Note that both \(\tau _{\infty }\) and \(\tau _m\) are finite almost surely. However, in order to assure finite expectations as well, from now on we further assume
without loss of generality.Footnote 3
Let \(X>0\) be a scaling factor and \(k=\log (X/K)\); then the price of a KIC can be expressed as
Similar to Cai et al. (2009), we will compute this quantity in terms of a two-dimensional Laplace transform. Specifically, consider
and the price then can be obtained via the inversion algorithm as proposed by Cai and Kou (2012). Actually, after some algebraic manipulation, the last expression can be further simplified asFootnote 4
provided that \(0<\theta <\left( \beta _{2,r+\alpha }-1\right)\) and \(\alpha >\max \left( G(\theta +1)-r,0\right)\). Here \(G(\cdot )\) is defined in (2.2) and X being introduced is merely to satisfy the parameter constraints behind (2.7) when applying the inversion algorithm.
Therefore, to study the price of a KIC, one needs only the joint moment generating function (MGF) of \(\tau\) and \(X_\tau\). This is true for both continuous (\(\tau _{\infty }\)) and discrete (\(\tau _m\)) options. Hence, from now on, let
which will serve as our working function in the subsequent analyses. We will also confine our discussion to the case with
to assure the \(L^1\) finiteness to come. Finally, note that the events \(\left\{ S_t\notin \left( L,H\right) \right\}\) and \(\left\{ X_t\notin \left( a,b\right) \right\}\) are equivalent where \(a=\log (L/S_0)<0\) and \(b=\log (H/S_0)>0\).
2.3 Continuous-time joint distribution
For \(0\le t\le \tau _{\infty }\), consider
Then, \(M_t\) is a Doob’s martingale, and by the Markovian property there exists a function v(t, x) such that \(M_t=v(t,X_t)\). In fact, the function v admits the form
in which the function u satisfies the following PDE:
subject to the boundary conditions
For convenience, we will simply refer to such f as a terminal function to emphasize its role in the boundary conditions.
Recalling (2.8), u(0, 0) is clearly the desired joint MGF of \(\tau _{\infty }\) and \(X_{\tau _{\infty }}\). As suggested in Cai et al. (2009), one can easily check that the solution to (2.10) is given by
where \(\beta _{1,\alpha }\) and \(\beta _{2,\alpha }\) are given by (2.3), and
Thus, we have
Now, as a final remark, let us list two implications of this joint MGF of the continuous version, which will be used greatly in the sequel. First, the MGF of the continuous stopping time \(\tau _{\infty }\) can then be obtained by directly setting \(\theta =0\) in (2.14), which leads to
for \(\alpha >0\). On the other hand, when letting \(\alpha\) go to zero, together with the help of (2.4), we have
from which we further achieve
with
In fact, \(q_a=P(X_{\tau _{\infty }}=a)\) and \(q_b=P(X_{\tau _{\infty }}=b).\) Thus \(q_a\ge 0\), \(q_b\ge 0\) and \(q_a+q_b=1\), which can also be checked directly. Moreover, \(\lim _{b\rightarrow \infty }q_a=\lambda _a\) and \(\lim _{a\rightarrow -\infty }q_b=\lambda _b\), where
Note that \(\lambda _y\) is merely the probability that a standard Brownian motion with drift \(\sigma \,\gamma\) hits the boundary of level y. Although these results are rather standard, we include them here for future use.
2.4 Continuity correction
With discrete monitoring, however, it is generally not possible to obtain a closed-form expression for \(E\left[ f(\tau _m\varDelta t,X_{\tau _m\varDelta t})\right]\). Thereby, we seek an analytical approximation. Given the property of weak convergence, a straightforward approach is to adopt
as \(m\rightarrow \infty\). However, in practice, the convergence rate of (2.18) is too slow for accurate approximation, even given daily monitoring.
Our goal here is to improve the convergence rate in (2.18) from o(1) to \(o(1/\sqrt{m})\) via adjustments to the levels of boundaries a and b before applying the formula (2.14). In sequential analysis, this is typically termed first-order approximation. The intuition is to shift away the boundary levels to account for a lower boundary-crossing probability with discrete monitoring. The amount of correction is highly related to the expectation of the so-called overshoot, the amount of the stopped level of the underlying process in excess of the boundary. Note that under the BS model, overshoot occurs only when monitoring discretely.
Keener (2013) observes that the boundary effect (due to overshoot) only matters (in the first order) when criteria like smooth pasting do not hold at the boundaries in the PDE problem (2.10). Namely, \(\frac{\partial }{\partial x}\,u\) and \(\frac{\partial }{\partial x}\,f\) do not always match on the boundaries. Thereupon, he further conjectures and verifies that the (path-wise) correction term, in our notation, takes the form
for the upper boundary, and
for the lower boundary. Note that these are linear in the state variable x, they vanish at the respective boundary, and they have a first-order derivative (with respect to x) equaling the difference between \(\frac{\partial }{\partial x}\,u\) and \(\frac{\partial }{\partial x}\,f\).
Nevertheless, this correction is only true for the single-barrier problem. To simultaneously account for the boundary effects at a and b, this form should not be linear. Indeed, a polynomial p(x) that satisfies \(p(a)=p(b)=0\) and also meets the two derivative differences at a and b (i.e., a total of four conditions) is at least cubic. Therefore, we consider
where
measure the first-order non-smoothness upon the boundaries b and a, respectively. Indeed, from (2.8) and (2.12) we have the general expression
which is bounded for all \(x\in [a,b]\).
In this way,
As a result, if we let
then \(u(t,a)=f(t,a)=f^0(t,a)\), \(u(t,b)=f(t,b)=f^0(t,b)\), and
In other words, if we alter the terminal function from f to such a \(f^0\), then the continuity holds upon the boundaries in the PDE problem (2.10), as does the first-order smoothness.
In the next section, we will show that
Namely, there is no need (for order \(1/\sqrt{m}\)) for correction when smooth pasting holds upon the boundaries. This is exactly the core of Keener’s approach to extract the smoothing part that needs no correction from a general terminal function f via a decomposition like (2.22). Since clearly \(Ef=Ef^0+Ef^1\), the remaining task is to estimate \(E\left[ f^1(\tau _m\varDelta t,X_{\tau _m\varDelta t})\right]\) so that
Thus, the improved convergence rate established for \(f^0\) still succeeds. More importantly, the limit of \(Ef^1\) is precisely the key we seek for correction to speed convergence in (2.18).
As a final remark, recall that \(\varDelta t=T/m\); hence \(m\rightarrow \infty\) is equivalent to \(\varDelta t\rightarrow 0\) here. To make our derivation more straightforward, we will simply take \(\varDelta t\) to describe the rate of convergence as m goes to infinity. Hence, for example, we write \(o(\sqrt{\varDelta t})\) rather than \(o(1/\sqrt{m})\) hereafter. The same logic applies for other situations.
2.5 Relevant random walks and the overshoot
Now, we define a discrete version of the continuous-time model (2.1), given that the monitoring frequency is m. We do so to facilitate the upcoming discussion. Let \(X_{m,0}=0\), and for \(n\in {\mathbb {N}}\), define
Here, for each m, the \(Z^{(m)}_k\)’s are independently and identically distributed (i.i.d.) standard normal random variables. Clearly, the random walk \(X_{m,n}\) follows the same law as \(X_{n\varDelta t}\); thus
Also, we will symbolize the filtration associated with \(X_{m,n}\) by \({\mathcal {F}}^{(m)}_n\).
Next, the associated overshoot can be defined by
To study its asymptotic property as \(m\rightarrow \infty\), we often rescale the random walk as \(X_{m,n}=\sigma \sqrt{\varDelta t}\,W_{m,n}\), where
Thus, the overshoot is expressed as \(\max \left\{ \sigma \sqrt{\varDelta t}\,R_m(a),\;\sigma \sqrt{\varDelta t}\,R_m(b)\right\}\), in which
with \(a_m=\frac{a}{\sigma \sqrt{\varDelta t}}\) and \(b_m=\frac{b}{\sigma \sqrt{\varDelta t}}\).
The relevance of (2.28) to our problem can be observed from (2.19) via, for example, an expansion such as
provided that \(x\notin (a,b)\). Thus, applying the same technique to both summands of \(f^1\), we finally obtain
Thus, to estimate \(Ef^1\), we must study the conditional moments of the overshoot; in particular,
Coincidentally, the situation here fits the framework considered in Siegmund (1979), where the incremental mean goes to zero and the boundary level goes to infinity synchronously. More precisely, as \(m\rightarrow \infty\), \(\mu _m\rightarrow 0\), \(|a_m|\rightarrow \infty\), and \(b_m\rightarrow \infty\), whereas both \(\mu _m|a_m|\) and \(\mu _mb_m\) remain constant. Therefore, we will choose to extend Siegmund’s results to cover our conditional version.
Finally, we emphasize that the expansion (2.29) from (2.19) is crucial for achieving our final correction formula. This is in fact not straightforward and requires some effort to figure it out. To the best of our knowledge, such a design is new in the related fields.
3 Main results
We here establish our correction result, under the two presumptions (2.6) and (2.9). According to the discussion in the previous section, there are actually three main steps. First, we will show there is no need to call for correction with regard to the \(f^0\) part in the decomposition (2.22). Second, we determine the estimation of the expected value of \(f^1\), and then combine these two results to achieve our final continuity correction formula for the pricing of discrete options with double barriers.
3.1 Estimation of \(Ef^0\)
First, recall the notation related to (2.12) and (2.22). Let
and
Then,
By the i.i.d. property of \(V_{m,k}\), the last equation becomes
As a result, the key to estimating \(Ef^0\) lies in the sum of these \(e_m\) terms.
Theorem 3.1
Under the setting specified in Sect. 2, we have
as \(m\rightarrow \infty\).
Proof
First, by Lemma A.1 in the appendix,
and note from (2.27) and (2.28) that the following three events are equivalent:
whereFootnote 5
Therefore,
and hence
Then, together with Lemmas A.2 and (A.10) in Appendix A, (3.2) becomes
Finally, note that
by L’Hôpital’s rule. The desired result thus follows. \(\square\)
3.2 Estimation of \(Ef^1\)
Recalling the notation in § 2.5, consider the following two hitting times of a single boundary,
and define their associated overshoots as
respectively. It is known that for any \(p\in {\mathbb {N}}\) both
see Siegmund (1985, pp. 186, 215) for example. With this preliminary knowledge, we have
Theorem 3.2
Under the setting specified in Sect. 2, we have as \(m\rightarrow \infty\)
where \(q_a\) and \(q_b\) are given in (2.16), and \(\rho =-\zeta (1/2)/\sqrt{2\pi }\approx 0.5826\) which is defined in (A.13).
Proof
Because
the fact (3.7) also implies
That is, both
Also, it is easy to see from (2.21) that \(D_b(t)\) and \(D_a(t)\) are bounded uniformly in t; thus, we can conclude from (2.29) that
Then, the result follows from Lemma A.4. \(\square\)
Remark 3.1
It is possible to extend Theorems 3.1 and 3.2 to cases with time-dependent barriers; namely, consider \(a=a(t)=\log (L(t)/S_0)\) and \(b=b(t)=\log (H(t)/S_0)\) for some time-varying barriers L(t) and H(t) with \(L(0)<S_0<H(0)\). To this end, we must impose two further conditions on the barriers according to Keener (2013). First, a(t) and b(t) have bounded first derivatives. Second, for some \(\epsilon >0\),
or
such that the stopping times
are uniformly integrable. However, the applicability of such a setting to real finance problems is still unknown or questionable.
3.3 Discrete option pricing
We are now ready to study the pricing of a discrete KIC. First, recall \(A(\alpha ,\theta )\) and \(B(\alpha ,\theta )\) in (2.13). Then, by Theorems 3.1 and 3.2, we have
Corollary 3.1
Under the setting specified in Sect. 2,
as \(m\rightarrow \infty\), in which
and
with \(\phi (\alpha )\) being defined in (2.15).
Proof
What remains is to work out \(E\left[ {\mathcal {D}}_a(\tau _{\infty })\right]\) and \(E\left[ {\mathcal {D}}_b(\tau _{\infty })\right]\) explicitly. The details are deferred to the appendix. \(\square\)
Remark 3.2
Note that from (2.3) we have \(\beta _{1,\alpha }+\beta _{2,\alpha }=-2\gamma\) for any \(\alpha \ge 0\). The hitting probabilities in (2.16) hence can be rewritten as
With the aid of this form, further computation (detailed but straightforward) leads to
in which \(\lambda _a\) and \(\lambda _b\) are defined in (2.17). We then obtain the next two special cases of (3.8):
Note that when the drift is positive (negative), \(\lambda _b=1\) \((\lambda _a=1)\) indeed, and the above results are then in line with the literature on single barriers; see (Kou, 2008) for instance. Namely, our achievement here coincides with the single-barrier case.
Next, on the basis of (2.7), we re-symbolize the KIC price of a discrete version by
and the associated Laplace transform by
Recall that here \(k=\log (X/K)\) is the transformed strike price. Then, we have
Corollary 3.2
For \(0<\theta <\left( \beta _{2,r+\alpha }-1\right)\) and \(\alpha >\max \left( G(\theta +1)-r,\,0\right)\),
as \(m\rightarrow \infty\).
Proof
See the appendix. \(\square\)
As mentioned in § 2.2, we will adopt the algorithm proposed by Cai and Kou (2012) to invert the Laplace transforms in Corollary 3.2. Generally speaking, their method is a combination of a two-sided Euler inversion and an Euler transformation for alternating series. The inversion parameters we choose are \(A_1=A_2=28.3\), \(n_1=38\), and \(n_2=11\) as suggested in Cai et al. (2009). On the other hand, the criteria for parameters \(\alpha\) and \(\theta\) in the corollary actually can be reduced to \(0<\theta <\beta _{2,r+\alpha }-1\), provided that \(r>0\). Hence, when implementing the inversion algorithm, we simply set the scaling factor to
for some \(c>2\), where K is the original strike price and T is the time to maturity.
4 Numerical examples
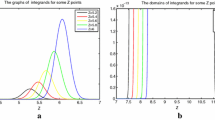
In this section, we will present examples to show the performance of our approximation formulas (CC). The benchmark values are obtained using Monte-Carlo (MC) simulation. One million trials were conducted in each simulation. We also report values directly from continuous formulas without correction (NC). Comparisons were made in terms of relative error (R.E.) defined by (“X”−MC)/MC, where X is NC or CC.
We first discuss the performance of (3.8). The outcomes are reported in Tables 1 and 2 for different considerations of incremental mean. Generally we see that our correction method does improve the rate of convergence, and that the improvement is quite stable across different boundary levels, regardless of whether the drift is positive or negative. Another important finding is that the signs of \(\varphi _1\) and \(\varphi _2\) in our correction formula are not necessarily positive. This means we do not always shift away each individual boundary to achieve continuity correction. In Table 2, for instance, when the lower boundary is \(a=-0.0175\) and the upper boundary is \(b=0.0225\), we must lower both boundary levels. By contrast, when \(a=-0.0225\), the upper barrier level is raised.
Additionally, the total amount adjusted at this point could be less than that in the single-boundary case. As hinted in Remark 3.2, the total adjustment is
when there is only one barrier. Here, interestingly, it is possible that \(|\varphi _1|+|\varphi _2|<1\) in the case of two simultaneous barriers. For example, in Table 1 with \(a=-0.0225\) and \(b=0.0175\), the total adjustment is just \(0.2781{\mathcal {V}}\). In other words, the shifted amount is only 28% of the single-barrier correction. However, the window length between barriers does widen after correction:
thanks to the positiveness of \(\varphi _1+\varphi _2\). To see this, note that
The outcome of the enlarged barrier window is consistent with the usual intuition that with discrete monitoring there is a smaller boundary-crossing probability than that in the continuous case. However, note that this argument is valid only given a fixed duration (time window).
On the other hand, for most cases in Tables 1 and 2, we see that the correction applied to each boundary is generally uneven. The only exception is when the lower and upper boundaries are equally far away (i.e., \(|a|=b\)). In this case, we see that \(\varphi _1=\varphi _2\). In fact, when taking \(a=-b\), we have
Then, it is easy to check \(0<\varphi (\alpha )<1\), and for each given \(\alpha\), \(\varphi (\alpha )\) increases in b. All observations from the tables with \(|a|=b\) meet these expectations. In fact, further graphical analysis shows that this seems to be the only situation for which \(\varphi _1(\alpha )=\varphi _2(\alpha )\). This special case also constitutes evidence against a common conjecture, that is, whether the correction tends to be greater for the boundary that is more likely to be reached. To illustrate, consider Table 1 where the drift is positive. In this case, we anticipate that the upper boundary \(b=0.0075\) is more likely to be hit earlier than the lower boundary \(a=-0.0075\). However, we see that the correction to each boundary requires the same level (\(\varphi _1=\varphi _2=0.0533\)). So far, these findings are specific to the case with two simultaneous boundaries.
Now we consider the performance for the proposed KIC pricing. Note that in Tables 1 and 2 we consider only one parameter setting for \(\alpha\) and \(\theta\). Since the option price is computed via Laplace inversion, the oncoming analysis can be viewed as an integrated evaluation of the approximation performance over a wide range of parameter levels. The results are presented in Tables 3 and 4 for positive and negative drift, respectively. For simplicity, we consider only those cases in which the two barriers are of equal distance, roughly corresponding to the situation behind (4.2).
As evidenced by the tables, we see that pricing errors do significantly improve with our approximation method, in comparison with that without correction. In some situations, we see relative errors within 1% even with monthly monitoring. (Assuming 250 trading days in a year, a \(\varDelta t\) of 1/10 is roughly equivalent to monthly monitoring.) For instance, in Table 4 with \(L=82\) and \(H=118\), the error is a mere 0.51% with \(\varDelta t=1/10\) for at-the-money case (Panel B). Finally, note that we also report the outcomes when one simply extends the correction idea from single barrier to double barrier. Namely, both barriers are shifted away by the same amount of \({\mathcal {V}}\) (i.e., \(\varphi _1=\varphi _2=1\)). This naive approach echoes the boundary correction result of Gobet and Menozzi (2010). From the tables, we clearly see that this is not an accurate continuity correction. Sometimes, it even does worse than that without correction; see Panel B of Table 3 with \(L=92\) and \(H=108\). That is, continuity correction should involve not only the overshoot expectation (represented by \({\mathcal {V}}\)) but also the boundary hitting probability (represented by \(\varphi _1\) and \(\varphi _2\)). This latter analysis again confirms the merit and necessity of our efforts here.
Finally, recall from Sect. 1 that the improved rate of convergence \(o(\sqrt{\varDelta t})\) is of the first order.Footnote 6 Hence the numerical outcomes obtained up to this point seem to reveal that the idea of first-order correction, in terms of an enlarged boundary window, takes effect mainly for the concern of boundary-hitting probabilities. This partly explains why the overall improvement brought by our correction method in Tables 1 and 2 is not as significant as that in Tables 3 and 4. The moment generating functions studied in the former two tables actually do not presume a duration; sooner or later, the boundary will be reached, regardless of the monitoring frequency. Since correction is not always outward, it is possible to see the boundary-hitting event occur earlier after the correction, especially when the boundary window is corrected in a direction opposite to the mean direction. For example, in Table 2, where a negative drift is considered, when \(a=-0.0075\) and \(b=0.0025\), the correction raises both boundaries, making it more likely to hit the lower boundary. As \(\varDelta t=1/10\), the corrected lower boundary even becomes positive, which further overestimates the stopped process level. Such an observation mainly accounts for why we see the correction result even underperforming that without correction. Nevertheless, this odd phenomenon ultimately disappears when increasing the monitoring frequency (i.e., as \(\varDelta t\rightarrow 0\)), consistent with the theorem.
Note that these findings also suggest the need for higher-order correction, in order to improve the weak convergence result as in (2.18) for practical applications. To account for the delay of the first hitting time with discrete monitoring, perhaps a rate of \(o(\varDelta t)\) is needed, requiring the moment calculation of the overshoot to the second. Still, at what order would the improved rate of convergence be satisfactory?—this remains an open question. By contrast, neither the hitting time nor the stopped price level matters with respect to option payoff. Only the barrier hitting probability plays a role in option valuation. This may explain why simple first-order correction suffices for the pricing of discrete options, per the existing literature.
5 Concluding remarks
Continuity correction in option pricing has been a classic challenge since the pioneer work of Broadie et al. (1997). The general idea is to approximate the price of a path-dependent option whose underlying process is monitored discretely by its associated pricing formula, assuming continuous monitoring, with adjustments to relevant barriers. In particular, for a single barrier option, the original barrier level is shifted away by an amount \({\mathcal {V}}\) in (4.1) before directly applying the continuous-time pricing formula. The quantity \({\mathcal {V}}\) is associated with the expectation of a pertinent overshoot. However, the correction for a double barrier option is a longstanding issue which is unsolved even for the classical Black–Scholes model. Here we draw to a close in part by extending the PDE approach of Keener (2013).
It is generally conjectured that for the double-barrier case, the correction method is the same as for the single-barrier case: one simply shifts away the amount \({\mathcal {V}}\) simultaneously to both barriers. Now, more than twenty years later, we show that this is not true. Continuity correction involves not only the overshoot expectation but also the boundary hitting probability. As a result, the correction amounts and even directionsFootnote 7 are highly dependent on the distances to each barrier from the current level. This constitutes the main contribution of our work to the literature. What remains unchanged is that the region within the barriers does widen after correction, to account for a lower boundary-crossing probability with discrete monitoring during a given period of time, as in the single-barrier case.
One clear limitation of the current work is the sophistication of the model. It is widely accepted that the Black–Scholes model is too simple to address real price processes. Nevertheless, due to its tractability, the BS model remains popular both in academia and in the industry. More specifically, many other numerical techniques can be used to price a discrete option under the BS model. Thus one relevant question concerning our study is: What is the advantage of our correction method? A preliminary answer is that the correction result produced indicates how to adjust the analytical formula not only between discrete and continuous monitoring, but also between different discrete monitoring frequencies. The latter is of particular use when the frequency adopted for payoff calculation differs from that for barrier monitoring. This is one popular design in a structured product, where the payoff is typically calculated on a low-frequency basis whereas the barrier monitoring is at a high frequency. Note that the payoff and the barrier can be imposed on different assets. Then, it is plausible to develop an efficient simulation procedure based on a low frequency but further weighted by the boundary crossing probability calculated at a high frequency. Our correction achievement may be helpful in such a scenario.
Other promising future studies include the following. First, how general is Keener’s PDE approach with respect to the model setting? In particular, does the same idea apply to the mixed-exponential jump diffusion model proposed by Cai and Kou (2011), given that the model is flexible enough to compete with all exponential Lévy models of finite activity while maintaining tractability? Second, is the approach adequate to other type of path-dependent options? We are particularly interested in the pricing of American options. As mentioned, the overshoot effect only matters when the boundary is not passed smoothly. However, this is the usual condition we impose to determine the price for an American option of finite maturity. One exception is the real option, where smooth pasting conditions are not always assumed. Thereby, it is likely that continuity correction will be of assistance in the valuation of real options.
Notes
Recently, a semi-analytical and efficient valuation method for discrete options was proposed by Lian et al. (2017).
This principle also leads to the smooth pasting condition usually imposed in American option pricing; for reference, see (Shreve, 2004).
This is a well-known result; see Durrett (2010, Chapter 4) for instance.
See the proof of Corollary 3.2 in Appendix B.
The distribution of \(Z_k^{(m)}\) is actually not dependent on m. The superscript (m) merely indicates a different set of random variables. Without ambiguity, we drop the superscript for the random walk \(W_n\) to simplify the notation.
In the sense that only the first moment of the overshoot needs estimating.
Recall that \(\varphi _1\) and \(\varphi _2\) in Corollary 3.1 are not always positive.
References
Ahmadian, D., & Ballestra, L. V. (2015). A numerical method to price discrete double barrier options under a constant elasticity of variance model with jump diffusion. International Journal of Computer Mathematics, 92(11), 2310–2328. https://doi.org/10.1080/00207160.2014.986114.
Ahmadian, D., Ballestra, L. V., & Karimi, N. (2021). An extremely efficient numerical method for pricing options in the Black-Scholes model with jumps. Mathematical Method in the Applied Sciences, 44(2), 1843–1862. https://doi.org/10.1002/mma.6882.
Bernard, C., Le Courtois, O., & Quittard-Pinon, F. (2008). Pricing derivatives with barriers in a stochastic interest rate environment. Journal of Economic Dynamics and Control, 32(9), 2903–2938. https://doi.org/10.1016/j.jedc.2007.11.004.
Boyarchenkoy, M., & Levendorskiĭ, S. (2012). Valuation of continuously monitored double barrier options and related securities. Mathematical Finance, 22(3), 419–444. https://doi.org/10.1111/j.1467-9965.2010.00469.x.
Broadie, M., Glasserman, P., & Kou, S. G. (1997). A continuity correction for discrete barrier options. Mathematical Finance, 7(4), 325–349. https://doi.org/10.1111/1467-9965.00035.
Broadie, M., Glasserman, P., & Kou, S. G. (1999). Connecting discrete and continuous path-dependent options. Finance and Stochastics, 3(1), 55–82. https://doi.org/10.1007/s007800050052.
Cai, N., Chen, N., & Wan, X. (2009). Pricing double-barrier options under a flexible jump diffusion model. Operations Research Letters, 37(3), 163–167. https://doi.org/10.1016/j.orl.2009.02.006.
Cai, N., & Kou, S. (2011). Option pricing under a mixed-exponential jump diffusion model. Management Science, 57(11), 2067–2081. https://doi.org/10.1287/mnsc.1110.1393.
Cai, N., & Kou, S. (2012). Pricing Asian options under a hyper-exponential jump diffusion model. Operations Research, 60(1), 64–77. https://doi.org/10.1287/opre.1110.1006.
Chernoff, H. (1965). Sequential tests for the mean of a normal distribution IV (Discrete case). Annals of Mathematical Statistics, 36(1), 55–68. https://doi.org/10.1214/aoms/1177700270.
Dia, E. H. A., & Lamberton, D. (2011). Connecting discrete and continuous lookback or hindsight options in exponential Lévy models. Advances in Applied Probability, 43(4), 1136–1165. https://doi.org/10.1239/aap/1324045702.
Durrett, R. (2010). Probability: Theory and Examples (4th ed.). Cambridge University Press.
Fuh, C. D., Luo, S. F., & Yen, J. F. (2013). Pricing discrete path-dependent options under a double exponential jump-diffusion model. Journal of Banking and Finance, 37(8), 2702–2713. https://doi.org/10.1016/j.jbankfin.2013.03.023.
Geman, H., & Yor, M. (1996). Pricing and hedging double-barrier options: A probabilistic approach. Mathematical Finance, 6(4), 365–378. https://doi.org/10.1111/j.1467-9965.1996.tb00122.x.
Gobet, E., & Menozzi, S. (2010). Stopped diffusion processes: Boundary corrections and overshoot. Stochastic Processes and their Applications, 120(2), 130–162. https://doi.org/10.1016/j.spa.2009.09.014.
Golbabai, A., Ballestra, L. V., & Ahmadian, D. (2014). A highly accurate finite element method to price discrete double barrier options. Computational Economics, 44(2), 153–173. https://doi.org/10.1007/s10614-013-9388-5.
Hörfelt, P. (2003). Extension of the corrected barrier approximation by Broadie, Glasserman, and Kou. Finance and Stochastics, 7(2), 231–243. https://doi.org/10.1007/s007800200077.
Jun, D. (2013). Continuity correction for discrete barrier options with two barriers. Journal of Computational and Applied Mathematics, 237(1), 520–528. https://doi.org/10.1016/j.cam.2012.06.021.
Keener, R. (2013). Improving Brownian approximations for boundary crossing problems. Bernoulli, 19(1), 137–153. https://doi.org/10.3150/11-BEJ396.
Kou, S. G. (2008). Disrete barrier and lookback options. In J. Birge & V. Linetsky (Eds.), Handbooks in Operations Research and Management Science: Financial Engineering (Vol. 15, pp. 343–373). North-Holland.
Kunitomo, N., & Ikeda, M. (1992). Pricing options with curved boundaries. Mathematical Finance, 2(4), 275–298. https://doi.org/10.1111/j.1467-9965.1992.tb00033.x.
Lai, T. L., Yao, Y. C., & AitSahlia, F. (2007). Corrected random walk approximations to free boundary problems in optimal stopping. Advances in Applied Probability, 39(3), 753–775. https://doi.org/10.1239/aap/1189518637.
Li, A. (1999). The pricing of double barrier options and their variations. In P. P. Boyle, G. Pennacchi, & P. Ritchken (Eds.), Advances in Futures and Options Research (pp. 17–41). Emerald Publishing.
Lian, G., Zhu, S. P., Elliott, R. J., & Cui, Z. (2017). Semi-analytical valuation for discrete barrier options under time-dependent Lévy processes. Journal of Banking and Finance, 75, 167–183. https://doi.org/10.1016/j.jbankfin.2016.11.012.
Lorden, G. (1970). On excess over the boundary. Annals of Mathematical Statistics, 41(2), 520–527. https://doi.org/10.1214/aoms/1177697092.
Merton, R. C. (1974). On the pricing of corporate debt: The risk structure of interest rates. Journal of Finance, 29(2), 449–470. https://doi.org/10.1111/j.1540-6261.1974.tb03058.x.
Milev, M., & Tagliani, A. (2010). Numerical valuation of discrete double barrier options. Journal of Computational and Applied Mathematics, 233(10), 2468–2480. https://doi.org/10.1016/j.cam.2009.10.029.
Pelsser, A. (2000). Pricing double barrier options using Laplace transforms. Finance and Stochastics, 4(1), 95–104. https://doi.org/10.1007/s007800050005.
Shepp, L., & Shiryaev, A. N. (1993). The Russian options: Reduced regret. Annals of Applied Probability, 3(3), 631–640. https://doi.org/10.1214/aoap/1177005355.
Shreve, S. E. (2004). Stochastic Calculus for Finance II: Continuous-Time Models. Springer-Verlag.
Siegmund, D. (1979). Corrected diffusion approximations in certain random walk problems. Advances in Applied Probability, 11(4), 701–719. https://doi.org/10.2307/1426855.
Siegmund, D. (1985). Sequential Analysis: Tests and Confidence Intervals. Spring-Verlag.
Acknowledgements
We would like to thank the Editor and two anonymous referees for their insightful comments and suggestions that help to improve the quality of the paper. All remaining errors are our responsibility.
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Sheng-Feng Luo: This research has been financially supported by Grants NSTC 105-2410-H-033-010 and NSTC 108-2410-H-033-013 of National Science and Technology Council, Taiwan.
Hsin-Chieh Wong: This research has been financially supported by Grant NSTC 111-2118-M-305-004-MY2 of National Science and Technology Council, Taiwan.
Appendices
A Auxiliary lemmas
In this part, we will introduce four lemmas that help to establish our final correction result. The first lemma estimates the expected increment in (3.1):
Lemma A.1
As \(m\rightarrow \infty\),
for \(a<x<b\).
Proof
Given \(a<x<b\), first note from (2.12) that u(t, x) is \(C^\infty\) in x; hence, on \(\left\{ x+V_{m,1}\in (a,b)\right\}\), we have
for some \(x^*\) lying between x and \(x+V_{m,1}\), whereas on \(\{x+V_{m,1}\notin (a,b)\}\), \(\bar{v}(t,x)\) is twice differentiable with respect to x but is only \(C^1\) thanks to (2.23), which then leads to
in which \(x^{**}\) likewise lies between x and \(x+V_{m,1}\).
Next, with our function forms of f and u (see (2.8) and (2.12)) and under the parameter constraint (2.9), straightforward (although tedious) analyses show (i) \(u_x\), \(u_{xx}\), \(u_{xxx}\), and \(u_{xxxx}\) are all uniformly bounded in \(x\in (a,b)\); and (ii) on \(\{x+V_{m,1}\notin (a,b)\}\), \(|\bar{v}_{xx}(t+\varDelta t,x^{**})-u_{xx}(t+\varDelta t, x)|\) can be bounded by an exponential form as \(e^{l(V_{m,1})}=1+l(V_{m,1})+O(V_{m,1}^2)\) for some linear function l. Thus, combining (A.1) and (A.2), we further obtain
Now, since also
the estimation of \(\bar{v}\) becomes
Then, since \(u(t,x)=e^{-\alpha \,t}\,\nu (x)\) for some one-variable function \(\nu\), we can also take Taylor’s expansions of u and its partial derivatives, with respect to t, which gives
and
Since u satisfies (2.10),
(A.4) can be rewritten as
Therefore, plugging (A.5) and (A.6) into (A.3), we get
Finally, it is easy to check that
and hence for all \(x\in (a,b)\),
Moreover, note that \(1_{\left\{ x+V_{m,1}\ge b\right\} }+1_{\left\{ x+V_{m,1}\le a\right\} }\) indeed stands for the indicator of \(\big \{V_{m,1}\ge b-x\big \}\bigcup \big \{V_{m,1}\le a-x\big \}\), and this union of events simply implies \(V_{m,1}^2\ge \min \left\{ (b-x)^2,(a-x)^2\right\}\). As a result,
Since also
we can further conclude
with the help of (A.7). The proof is hence completed. \(\square\)
The second lemma estimates the sum of those \(e_m\)’s related to (3.2):
Lemma A.2
Recall the definitions of \(W_k\), \(a_m(k)\), and \(b_m(k)\) in (3.4); we have
as \(m\rightarrow \infty\).
Before directly proving the lemma just mentioned, we here list two facts that will be repeatedly used in the proof. First, for any \(d>0\), define
Recall \(\hat{\tau }_m\) and \(\check{\tau }_m\) as defined in (3.5). According to the criterion provided by Keener (2013, p. 140), either \(\hat{\tau }_m\varDelta t\) or \(\check{\tau }_m\varDelta t\), \(m\ge 1\), are uniformly integrable. Since both \(\tau _m\le \hat{\tau }_m\) and \(\tau _m\le \check{\tau }_m\) almost surely, so are \(\tau _m\varDelta t\). Since \(a_m(t)\) and \(b_m(t)\) also have a bounded first derivative with respect to t, we have both
by analogy with Keener (2013, Lemma 2.2) and thanks to the symmetry of normality.
Second, for \(0<x_k<\delta\),
which implies
Proof of of Lemma A.2
First note from (2.26) and (3.3) that \(a_m(k)<W_k<b_m(k)\) for \(k<\tau _m\). Let
so that \(c_m(k)=a_m(k)+d^*=b_m(k)-d^*\) is the middle point of \(a_m(k)\) and \(b_m(k)\). Thus, on \(\left\{ c_m(k)<W_k<b_m(k)\right\}\),
and
in which we have applied (A.9) with \(\delta =d^*\) and \(n=\tau _m\). Similarly, on \(\left\{ a_m(k)<W_k<c_m(k)\right\}\), we have
Thus, with the help of (A.8), we can conclude
Finally, to complete the proof, we will show
To see (A.10), first observe that \(E(\tau _{m})\le \min \left\{ E(\hat{\tau }_m),\;E(\check{\tau }_m)\right\} .\) Under the presumption (2.6), we either have \(E(\hat{\tau }_m)<\infty\) or \(E(\check{\tau }_m)<\infty\), depending on the sign of \(\mu _m\). Suppose \(\mu _m>0\); then, the famous Wald’s identity gives
where the overshoot \(\hat{R}_m(b)\) is defined in (3.6). Denoting by \(\tau _{m}^{+}\) the associated first ladder height, we further have
according to Lorden (Lorden (1970), Theorem 3). Also, it has been known from Siegmund (1979) that the moments of \(W_{m,\tau _{m}^{+}}\) are continuous in \(\mu _m\in [0,\mu ^*]\) for sufficiently small \(\mu ^*\), and \(E(W_{m,\tau _{m}^{+}})\) is bounded away from zero. These facts together account for the uniform boundedness of \(E(\hat{R}_m(b))\) with respect to m. In other words, together with (2.27) and (2.28), (A.11) leads to
or (A.10) exactly. If \(\mu _m<0\) instead, apply the same analysis to \(E(\check{\tau }_m)\) and \(E[\check{R}_m(a)]\), leading to the same conclusion. This concludes the proof. \(\square\)
We now turn to study the asymptotic behavior of the overshoots in (2.28). Recall \(W_n\) in (3.4); for \(x\ge 0\), let
where \(\tau _{+}\) is the first ladder time, defined by \(\tau _{+}=\inf \left\{ n\in {\mathbb {N}}:\,W_n>0\right\} .\) Then, \(H(\cdot )\) is a qualified distribution function and admits a mean of
Here \(\zeta (\cdot )\) is the Riemann zeta function, and \(\rho \approx 0.5826\) (see Chernoff 1965). In addition, if \(\tau _B(y)\) is the first passage time that a standard Brownian motion hits the boundary of level \(y\in {\mathbb {R}}\), it is known that
The next lemma states the limits of the overshoots’ conditional first moments:
Lemma A.3
Recall the definitions in (2.16), (2.28), and (A.13). We have
and
as \(m\rightarrow \infty\).
Proof
Recall the one-boundary overshoots defined in (3.6). Then, for \(x\ge 0\),
Note that the event considered in \(P_2\) above implies \(\tau _m<\hat{\tau }_m\); thus
Now, let us first deal with \(P_1\). We will use the tilting technique as in Siegmund (1979). To begin with, note that the distribution of \(Z_{m,1}\), say F(z), in (2.27) belongs to an exponential family. Specifically, we have
where \(F_{u}(.)\) is the normal distribution function with mean u and variance 1, and \(\psi (y)=y^2/2\) is the cumulant function of the standard normal distribution. Then, if \(\mu _m>0\), \(P(\hat{\tau }_m<\infty )=1\) according to the law of large numbers and hence
where we further appeal to Wald’s likelihood ratio identity for the second equality and \(E_0\) denotes the expectation taken under which each \(Z_{m,k}\) has zero mean. Next, note that
as \(m\rightarrow \infty\), according to Siegmund (1979) for instance. Here “\(\Rightarrow\)” denotes convergence in distribution. Also, \(\mu _mb_m=\gamma \,b\) is actually a constant, with \(\gamma\) defined in (2.5). These facts, plus the asymptotic independence by Siegmund (1979, Lemma 3), yield
in which H(x) is given by (A.12) and we have utilized the fact (A.14) for the last equality. On the other hand, when \(\mu _m<0\), we use the same technique to get
as \(m\rightarrow \infty\). Here \(\bar{E}\) stands for the conjugate expectation taken under which each \(Z_{m,k}\) has a mean of \(-\mu _m>0\) and hence \(\bar{P}(\hat{\tau }_m<\infty )=1\). By analogy,
Thus, in this case we also see
Next, for \(P_2\), borrowing the result for \(P_1\) to achieve
where in the penultimate equation we have taken advantage of the property of weak convergence between \(X_{m,n}\) and \(X_t\). Therefore, combining the two outcomes for \(P_1\) and \(P_2\), we arrive at
Finally, by Fatou’s lemma,
The result for \(R_m(a)\) can be obtained similarly by symmetry. \(\square\)
The last lemma states one type of asymptotic independence between \(\tau _m\) and \(R_m\):
Lemma A.4
As \(m\rightarrow \infty\),
and
Proof
Again, only the details for the first result related to the upper boundary b will be provided. The proof with regard to the lower boundary a is quite similar and hence omitted for the sake of space.
First note that (2.26) can be rewritten as
Thus consider
and define
Then, for \(x\in (a_m-b_m,0)\),
Therefore, on \(\left\{ W_{m,k}\in (a_m,b_m)\right\}\),
which implies
for any \({\mathcal {F}}_k^{(m)}\)-measurable function \(l_k\).
Now, note that
Since
as \(m\rightarrow \infty\) by weak convergence, what remains is to also show
To see (A.16), let us start with the following decomposition, which mimics the idea of telescoping behind (3.2):
Then, for the second part,
by Lemma A.3 directly.
As in the first part, we apply (A.15) to obtain
Next, according to (2.21), it is easy to see there exists a constant K uniformly for all k such that
Thereby,
Finally, by the same argument leading to (A.17), we have
and hence
by (A.10) and Lemma A.3 again. (A.16) thus follows, concluding the proof. \(\square\)
B Corollary proofs
Proof of Corollary 3.1
First of all, from (2.21), we get
Also, the boundary condition \(f(t,b)=u(t,b)\) of (2.11) implies
and hence
Recall from (2.15) that \(\phi (\alpha )=E\left[ \exp (-\alpha \,\tau _{\infty })\right]\); so we have
By analogy, we have
Then, according to Theorem 3.2,
On the other hand, recalling (2.14), we have
by Theorem 3.1. Thus, combining (B.1) and (B.2), we get
Next, apply the approximation \(1+t=e^{t}+o(t)\) (for small t) to both quantities in the curly brackets above, which then leads to the final result. \(\square\)
Proof of Corollary 3.2
Starting directly with the definition and by Fubini’s theorem,
Since \(\theta\) is confined to be larger than 0, the inner integral with respect to k can be carried out, which gives
Now, by Fubini’s theorem again and by the law of iterated expectations,
Then, by the Markovian property of the log-return process \(X_t\), the last equation becomes
with the help of (2.2). Since \(r+\alpha -G(\theta +1)>0\) by presumption, the dt-integral can be worked out, which finally leads to
Ultimately, to get the desired result, we apply (3.8) to the previous equality. \(\square\)
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made. The images or other third party material in this article are included in the article's Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article's Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Luo, SF., Wong, HC. Continuity correction: on the pricing of discrete double barrier options. Rev Deriv Res 26, 51–90 (2023). https://doi.org/10.1007/s11147-022-09193-z
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11147-022-09193-z