Abstract
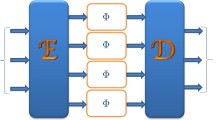
We develop a systematic theory for the construction of quantum codes from classical Reed–Solomon over \({\mathbb {F}}_{p^k}\), where p is prime and \(k \in {\mathbb {Z}}^{+}\). Based on two classical \([n,n-d_m+1,d_m]\) Reed–Solomon codes over \({\mathbb {F}}_{p^k}\), we provide the construction of an \([[n,n+n_e-2(d_m-1),d_m]]\) entanglement-assisted Reed–Solomon code over qudits of dimension \(d=p^k\) that saturates the quantum Singleton bound and needs \(n_e\) entangled qudits, which involves obtaining the explicit form of the stabilizers for the code. Our contributions towards the entanglement-assisted Reed–Solomon code are multi-fold as follows: (a) Based on the parity check matrices of the classical Reed–Solomon codes, the explicit form of the stabilizers of the entanglement-assisted Reed–Solomon code are provided and the rate-optimal code is obtained. (b) Based on the entanglement-assisted Reed–Solomon code, a burst error correcting code for qudits of dimension p that corrects a burst of \(k(t_m-1)\) qudits or less, where \(t_m = \lfloor (d_m-1)/2\rfloor \) is provided. (c) Finally, we provide amenable circuits for encoding and error correction with quantum circuit complexity of \({\mathcal {O}}(n^2)\), useful for practical implementations.











Similar content being viewed by others
Notes
A part of this work was presented as an invited talk at the IEEE Information Theory and Applications workshop at San Diego in February 2019.
The interested reader must note that even though we consider two classical RS codes with the same length and same minimum distance for the construction of EA RS codes, the theory and code construction of the EA RS code obtained from two classical RS codes having the same length but different minimum distances are similar. However, such codes might not always saturate the quantum Singleton bound.
The interested reader should note that though the approaches in [28] and ours are different, the number of entangled qudits required are exactly the same, coincidentally.
We note that \(H_{d_1}\) and \(H_{d_2}\) in Eq. (11) are considered as the generator matrices of \(C_1\) and \(C_2\) in [28], while we consider them as the parity check matrices. As \(C_1\setminus (C_2^{\perp }\cap C_1) = C_1\setminus C_2^{\perp }\) and \(C_2\setminus (C_1^{\perp }\cap C_2) = C_2\setminus C_1^{\perp }\), we obtain \(d' = \mathrm {min}(d_{\mathrm {H}}(C_1\setminus C_2^{\perp }),d_{\mathrm {H}}(C_2\setminus C_1^{\perp }))\).
We note that a zero-rate code has only one basis codeword; hence, it does not have the concept of minimum distance.
We note that the minimum distance of \(C_1\cap C_2^{\perp }\) is obtained as \(n-(d_m-n+v)+1 = 2n-d_m-v+1\) because RS code is an MDS code.
The interested reader should note that in the classical case, the only zero-rate linear code is the all-zero code. However, this is not the case for a quantum code as a single basis codeword of the zero-rate code is a state that is stabilized by all the code stabilizers.
References
Gottesman, D.: Class of quantum error-correcting codes saturating the quantum Hamming bound. Phys. Rev. A 54, 1862–1868 (1996)
Brun, T., Devetak, I., Hsieh, M.: Correcting quantum errors with entanglement. Science 314, 436–439 (2006)
Grassl, M., Geiselmann, W., Beth, T.: Quantum Reed–Solomon codes. In International Symposium on Applied Algebra, Algebraic Algorithms, and Error-Correcting Codes, pp. 231-244 (1999)
Aly, S.A.: Asymmetric quantum BCH codes. In Proceedings of IEEE International Conference on Computer Engineering and Systems (ICCES08), pp. 157–162 (2008)
La Guardia, G. G., Palazzo, R., Lavor, C.: Nonbinary quantum Reed–Solomon codes. Int. J. Pure Applied Math. 65(1) (2010)
La Guardia, G.G.: Asymmetric quantum Reed–Solomon and generalized Reed–Solomon codes. Quant. Inf. Process 11, 591–604 (2012)
Grassl, M., Beth, T., Rötteler, M.: On optimal quantum codes. Int. J. Quantum Inf. 2(1), 55–64 (2004)
Muralidharan, S., Zou, C., Li, L., Jiang, L.: One-way quantum repeaters with quantum Reed-Solomon codes. Phys. Rev. A 97(5) (2018)
Ketkar, A., Klappenecker, A., Kumar, S., Sarvepalli, P. K.: Nonbinary Stabilizer Codes Over Finite Fields. IEEE Trans. Inf. Theory 52(11) (2006)
Fan, J., Chen, H., Xu, J.: Constructions of Q-ary entanglement-assisted quantum MDS codes with minimum distance greater than \(q + 1\). Quantum Info. Comput. 16(5–6), 423–434 (2016)
Guenda, K., Jitman, S., Gulliver, T. A.: Constructions of good entanglement-assisted quantum error correcting codes. Des. Codes Cryptogr. 86(1) (2018)
Hurley, T., Hurley, D., Hurley, B.: Entanglement-assisted quantum error-correcting codes from units. arXiv preprint arXiv:1806.10875 (2018)
Galindo, C., Hernando, F., Ruano, D.: Entanglement-assisted Quantum Error Correcting Codes from RS Codes and BCH Codes with Extension Degree 2. arXiv preprint arXiv:2007.01113 (2020)
Lai, C., Brun, T. A.: Entanglement increases the error-correcting ability of quantum error-correcting codes. Phys. Rev. A 88(1) (2013)
Grassl, M.: Entanglement-Assisted Quantum Communication Beating the Quantum Singleton Bound. arXiv preprint arXiv:2007.01249
Nadkarni, P. J., Garani, S. S.: Non-binary Entanglement-assisted Stabilizer Codes. submitted for publication
Nadkarni, P.J., Garani, S.S.: Entanglement-Assisted Quantum Reed-Solomon Codes. IEEE Information Theory Applications Workshop, San Diego (2019)
Guo, G., Li, R.: New entanglement-assisted quantum MDS codes derived from generalized Reed–Solomon Codes. Int. J. Theor. Phys. 56, 1241–1254 (2020)
Li, Z., Xing, L., Wang, X.: Quantum generalized Reed-Solomon codes: Unified framework for quantum maximum-distance-separable codes. Phys. Rev. A 77(1) (2008)
Li, L., Zhu, S., Liu, L.: Three new classes of entanglement-assisted quantum MDS codes from generalized Reed–Solomon codes. Quant. Inf. Process. 18(366) (2019)
Wilde, M. M., Brun, T. A.: Optimal entanglement formulas for entanglement-assisted quantum coding. Phys. Rev. A 77(6) (2008)
Nadkarni, P.J., Garani, S.S.: Encoding of quantum stabilizer codes over qudits with \(d=p^k\). IEEE Globecom, Abu Dhabi (2018)
Lin, S., Costello, D.J.: Error Control Coding: Fundamentals and applications. Prentice Hall Inc., New Jersy (1983)
Ashikhmin, A., Knill, E.: Nonbinary quantum stabilizer codes. IEEE Trans. Inf. Theory 47(7) (2001)
Calderbank, A.R., Shor, P.W.: Good quantum error-correcting codes exist. Phys. Rev. A 54, (1996)
Calderbank, A.R., Rains, E.M., Shor, P.W., Sloane, N.J.A.: Quantum error correction via codes over GF(4). IEEE Trans. Inf. Theory 44(4), 1369–1387 (1998)
Steane, A. M.: Error correcting codes in quantum theory. Phys. Rev. Lett. 77(5) (1996)
Galindo, C., Hernando, F., Matsumoto, R., Ruano, D.: Entanglement-assisted quantum error-correcting codes over arbitrary finite fields. Quant. Inf. Process 18, 4 (2019)
Wilde, M. M.: Quantum Coding with Entanglement. Univ. of South. Cal., (2008)
Grassl, M., Roetteler, M., Beth, T.: Efficient quantum circuits for non-qubit quantum error-correcting codes. Int. J. Found. Comput. Sci. 14(5) (2003)
Farinholt, J. M.: An ideal characterization of the Clifford operators. J. Phys. A Math.Theor. 47(30) (2014)
Strang, G.: Introduction to Linear Algebra. Cambridge University Press, Cambridge (2016)
Calderbank, A. R., Rains, E. M., Shor, P. W., Sloane, N. J. A.: Quantum error correction via codes over GF(4). IEEE Trans. Inf. Theory 44(4) (1998)
MacWilliams, F.J., Sloane, N.J.A.: The Theory of Error-Correcting Codes. Elsevier, Amsterdam (1988)
Acknowledgements
The Ph. D. work of P. J. Nadkarni is funded by a fellowship from the Ministry of Electronics & Information Technology (MeitY), Government of India (GOI). S. S. Garani acknowledges the Ministry of Human Resource and Development (MHRD), Government of India, for support.
Funding
Funding for this study was obtained from the Ministry of Electronics & Information Technology (MeitY), Government of India (GOI), and the Ministry of Human Resource and Development (MHRD), Government of India.
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest
The authors declare that there are no competing interests.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Supplementary Information
Below is the link to the electronic supplementary material.
Appendices
A Proof of Lemma 1
Proof
When \(\beta =0\), for \(i \in \{0,1,\dots ,k-1\}\), \(\mathrm {Tr}_{p^k/p}(\alpha ^i \beta ) = \mathrm {Tr}_{p^k/p}(0) = 0\).
For some \(\beta \in {\mathbb {F}}_{p^k}\), let \(\mathrm {Tr}_{p^k/p}(\alpha ^i \beta ) = 0\) \(\forall i \in \{0,1,\dots ,k-1\}\). For every \(\kappa \in {\mathbb {F}}_{p^k}\), there exists \(\kappa _0, \dots , \kappa _{k-1} \in {\mathbb {F}}_p\) such that \(\kappa = \underset{i=0}{\overset{k-1}{\sum }} \kappa _i \alpha ^i\) [23]. Since \(\mathrm {Tr}_{p^k/p}(\cdot )\) is an \({\mathbb {F}}_p\)-linear function,
If \(\beta \ne 0\), as by closure property of \({\mathbb {F}}_{p^k}\), \(\{\kappa \beta \}_{\kappa \in {\mathbb {F}}_{p^k}} = \{\kappa '\}_{\kappa '\in {\mathbb {F}}_{p^k}}\), from Eq. (106), \(\mathrm {Tr}_{p^k/p}(\kappa ')=0\) for every \(\kappa '\in {\mathbb {F}}_{p^k}\), which is a contradiction as the trace of all the elements of \({\mathbb {F}}_{p^k}\) cannot be 0. Thus, \(\beta =0\). \(\square \)
B Proof of Theorem 3
Proof
We consider two classical codes \(D_1[n,k_1,d_1]\) and \(D_2[n,k_2,d_2]\) over \({\mathbb {F}}_{p^k}\) with parity check matrices \(H_{d1}\) and \(H_{d2}\), respectively. Based on \(H_{d1}\) and \(H_{d2}\), we construct the matrix \(\mathcal {H_R}\) as in Eq. (11), similar to the check matrix of an entanglement-unassisted CSS code in Eq. (8).
After the extension of \({\mathcal {R}}\) to S, the number of stabilizer generators is \(\rho = k((n-k_1)+(n-k_2)) = k(2n-k_1-k_2)\). Thus, the dimension of the EA CSS code is \(p^{(kn+n_e'-\rho )} = p^{(kn+n_e'-k(2n-k_1-k_2))}6 =p^{(k(k_1+k_2-n)+n_e')}\) .
Similar to the qubit case [29], the distance of the EA stabilizer code depends only on the matrix \(\mathcal {H_R}\) as the added subqudits are assumed to be error-free at the receiver end. Similar to the minimum distance of the CSS codes in Theorem 1, we obtain the minimum distance \(d'\) of the EA CSS code to be \(d' \ge \mathrm {min}(d_1,d_2)\).
\(\textit{Computation of }\underline{\varvec{n_e'}}\):
From Eq. (9), the number of entangled subqudits needed for the EA CSS code is \( n_e' = \mathrm {rank}\left( {\mathcal {T}}\left( {\mathcal {H}}_{\mathrm {X}}{\mathcal {H}}_{\mathrm {Z}}^{\mathrm {T}}\right) \right) \), where \( {\mathcal {H}}_{\mathrm {X}} = [(H_{d1})^{\mathrm {T}}~\alpha (H_{d1})^{\mathrm {T}}\dots \alpha ^{(k-1)}(H_{d1})^{\mathrm {T}}]^{\mathrm {T}}\) and \( {\mathcal {H}}_{\mathrm {Z}}= [(H_{d2})^{\mathrm {T}}\) \(~\alpha (H_{d2})^{\mathrm {T}}\dots \alpha ^{(k-1)}(H_{d2})^{\mathrm {T}}]^{\mathrm {T}}\). We first compute \({\mathcal {H}}_{\mathrm {X}}{\mathcal {H}}_{\mathrm {Z}}^{\mathrm {T}}\) as follows:
where \(Q=H_{d1}H_{d2}^{\mathrm {T}}\).
We note that the matrix \(H_{d1}H_{d2}^{\mathrm {T}}\) need not be a full-rank matrix. Let \(Q'\) be a submatrix of Q such that the rows of \(Q'\) are a set of maximally linearly independent rows of Q. Then, \(Q'\) is a full-rank matrix and \(\mathrm {rank}(Q)=\mathrm {rank}(Q')\). Let the size of \(Q'\) be \(r\times c\). We note that the number of columns of \(Q'\) and Q are the same.
We note that every element in \({\mathbb {F}}_{p^k}\) can be written as an \({\mathbb {F}}_p\)-linear combination of 1, \(\alpha \), \(\dots \), \(\alpha ^{k-1}\). From the definition of \(Q'\), the rows of Q can be obtained from the linear combination of the rows of \(Q'\). Thus, the rows of Q, \(\alpha Q\), \(\dots \), \(\alpha ^{(k-1)}Q\) can be obtained from the \({\mathbb {F}}_p\)-linear combination of the rows of \(Q'\), \(\alpha Q'\), \(\dots \), \(\alpha ^{(k-1)}Q'\).
In Eq. (107), considering only those rows of \({\mathcal {H}}_{\mathrm {X}}\!{\mathcal {H}}_{\mathrm {Z}}^{\mathrm {T}}\) that have the rows of \(Q'\) in the blocks instead of Q, we obtain the matrix
From Eqs. (107) and (108), we note that the rows of \( {\mathcal {H}}_{\mathrm {X}}\!{\mathcal {H}}_{\mathrm {Z}}^{\mathrm {T}}\) can also be obtained from the \({\mathbb {F}}_p\)-linear combination of the rows of P as the rows of Q, \(\alpha Q\), \(\dots \), \(\alpha ^{(k-1)}Q\) can be obtained from the \({\mathbb {F}}_p\)-linear combination of the rows of \(Q'\), \(\alpha Q'\), \(\dots \), \(\alpha ^{(k-1)}Q'\).
Let \(q_{ij}\) be the \((i,j)^{\mathrm {th}}\) element of \(Q'\), where \(i\in \{1,\dots ,r\}\) and \(j\in \{1,\dots ,c\}\). We next prove that the matrix \({\mathcal {T}}(P)\) is a full-rank matrix.
If the matrix \({\mathcal {T}}(P)\) is not a full-rank matrix, there exists a non-trivial linear combination of the rows of \({\mathcal {T}}(P)\) that sum up to zero. For \(l,m\in \{0,\dots ,k-1\}\), the \((i,j)^{\mathrm {th}}\) elements in the \(l^{\mathrm {th}}\) and \(m^{\mathrm {th}}\) column subblock of P are \(\alpha ^{(l+m)}q_{ij}\). Thus, there exists \(g_{il}\in {\mathbb {F}}_{p}\), where \(i\in \{1,\dots ,r\}\) and \(l\in \{0,\dots ,k-1\}\), such that
for all \(m\in \{0,\dots ,k-1\}\) and \(j\in \{1,\dots ,c\}\). As the field trace is \({\mathbb {F}}_{p}\)-linear, from Eq. (109), for all \(m\in \{0,1,\dots ,k-1\}\) and \(j\in \{1,\dots ,c\}\), we have
As the rows of \(Q'\) are linearly independent, only the trivial linear combinations of \(\{q_{ij}\}_{i=1}^{r}\) is zero. Thus, from Eq. (110), we obtain
We note that \(f(x) = \overset{k-1}{\underset{l=0}{\sum }} x^{l}g_{il}\) is a polynomial of degree less than k with coefficients from \({\mathbb {F}}_p\). Thus, \(f(\alpha ) = \overset{k-1}{\underset{l=0}{\sum }} \alpha ^{l}g_{il}\) cannot be equal to zero unless all \(g_{il}\)s are zero as \(\alpha \) is the primitive element and its minimal polynomial is the primitive polynomial of the field having degree k. Thus, each coefficient of f(x) is zero. Thus, from Eq. (111), we obtain
From Eqs. (109) and (112), only the trivial linear combination of the rows of \({\mathcal {T}}(P)\) results in the all-zero vector. Thus, \({\mathcal {T}}(P)\) is a full-rank matrix.
As \(\mathrm {rank}(Q') = \mathrm {rank}(Q)\) and \(Q'\) is a full-rank matrix, the number of rows r of \(Q'\) is \(\mathrm {rank}(Q)\). Thus, the number of rows of \({\mathcal {T}}(P)\) is \(k~\mathrm {rank}(Q)\). As \({\mathcal {T}}(P)\) is a full-rank matrix, the rank of \({\mathcal {T}}(P)\) is \(k~\mathrm {rank}(Q) =k~\mathrm {rank}(H_{d1}H_{d2}^{\mathrm {T}})\).
We note that the rank of the matrix does not change if linearly dependent rows are added to the matrix. Thus, as all the rows of \({\mathcal {H}}_{\mathrm {X}}{\mathcal {H}}_{\mathrm {Z}}^{\mathrm {T}}\) can be obtained from the \({\mathbb {F}}_p\)-linear combination of the rows of P, \(\mathrm {rank}({\mathcal {T}}({\mathcal {H}}_{\mathrm {X}}{\mathcal {H}}_{\mathrm {Z}}^{\mathrm {T}})) = \mathrm {rank}({\mathcal {T}}(P)) = k~\mathrm {rank}(H_{d1}H_{d2}^{\mathrm {T}})\). Thus, from Eq. (9), we obtain \( n_e' = k~\mathrm {rank}(H_{d1}H_{d2}^{\mathrm {T}}).\) \(\square \)
C Proof of Proposition 1
We will first state two results in Lemmas 5 and 6 necessary to prove Proposition 1.
Lemma 5
The generator matrix of an \([n,n-d_m+1,d_m]\) classical RS code C with parity check matrix \(H_b\) is obtained from \(H_{n-b+1}\) based on Eq. (12), by replacing \(d_m\) with \(n-d_m+2\).
Proof
As the dimension of the code C is \(n-d_m+1\), the generator matrix has \(n-d_m+1\) linearly independent rows. Let A be the matrix obtained from \(H_{n-b+1}\) based on Eq. (12), by replacing \(d_m\) with \(n-d_m+2\). The \((i,j)^{\mathrm {th}}\) element of A is \(\alpha ^{(n-b+i)(j-1)}\), where \(i \in \{1,\dots ,n-d_m+1\}\) and \(j \in \{1,\dots ,n\}\). As the set of rows of A is a subset of the rows of a Vandermonde matrix, A is a full-rank matrix with \(n-d_m+1\) linearly independent rows.
We next show that the rowspace of A is equal to the nullspace of \(H_b\). As the \((i,j)^{\mathrm {th}}\) element of \(H_b\) and A are \(\alpha ^{(i+b-1)(j-1)}\) and \(\alpha ^{(n-b+i)(j-1)}\), respectively, we obtain
where \(i \in \{1,\dots ,d_m-1\}\) and \(j \in \{1,\dots ,n-d_m+1\}\). As \(n+1\le n+i+j-1 \le 2n-1\), we obtain \((n+i+j-1)~\mathrm {mod}~n \ne 0\). Thus, from Eqs. (17) and (113), we obtain \((H_bA^{\mathrm {T}})_{i,j} =0 ~\forall \) \(i \in \{1,\dots ,d_m-1\}\) and \(j \in \{1,\dots ,n-d_m+1\}\). Thus, the rowspace of A lies in the null space of \(H_b\). As the rank of \(H_b\) is \(d_m-1\), by the rank-nullity theorem [32], its null space has a dimension of \(n-d_m+1\). As the rank of A is \(n-d_m+1\) and \(H_bA^{\mathrm {T}}=0\), the rowspace of A is equal to the nullspace of \(H_b\) and A is the generator matrix of the RS code C. \(\square \)
Lemma 6
An EA RS code with minimum distance \(d'\) constructed from two classical codes \(C_1\) and \(C_2\) is a non-degenerate code if every element in \(C_1\cap C_2^{\perp }\) and \(C_2\cap C_1^{\perp }\) has a weight of at least \(d'\).
Proof
A stabilizer code is a non-degenerate code if there does not exist two correctable errors \(E_a\) and \(E_b\) such that \(E_aE_b^{\dagger }\) is a stabilizer [1]. A stabilizer code is a non-degenerate code if the weight of each stabilizer is at least the minimum distance \(d'\) of the code [33]. For an EA RS code, as the errors \(E_a\) and \(E_b\) operate only on the first n transmitter end qudits, the operation of \(E_aE_b^{\dagger }\) on the receiver end qudits is the identity operation. Thus, for non-degeneracy, we only consider those stabilizers that are obtained by extending the elements of \({\mathcal {R}}\) with identity operators (field isomorphic equivalent is \(\varvec{0}\)) in Theorem 5.
In Theorem 5, only the elements of \({\mathcal {R}}\) that commute with all elements of \({\mathcal {R}}\) have been extended with identity operators. These elements of \({\mathcal {R}}\) correspond to the indices of the rows of \(H_{b1}\) and \(H_{b2}\) in sets \(N_{\mathrm {OX}}\) and \(N_{\mathrm {OZ}}\), respectively. We note that \(H_{b1}\) and \(H_{b2}\) generate \(C_1^{\perp }\) and \(C_{2}^{\perp }\) and their nullspaces are \(C_1\) and \(C_2\), respectively. As \(N_{\mathrm {OX}}\) and \(N_{\mathrm {OZ}}\) correspond to the rows of \(H_{b1}\) and \(H_{b2}\) that are orthogonal to all rows of \(H_{b2}\) and \(H_{b1}\), respectively, we consider the vectors in \(C_1\cap C_2^{\perp }\) and \(C_2\cap C_1^{\perp }\) to determine whether the code is non-degenerate.
The elements in \({\mathcal {R}}\) corresponding to the vectors in \(C_1\cap C_2^{\perp }\) and \(C_2\cap C_1^{\perp }\) have the same weight as the vectors. As these elements in \({\mathcal {R}}\) are extended by identity operators, the weight of their corresponding stabilizers is equal to the weight of the corresponding vectors in \(C_1\cap C_2^{\perp }\) or \(C_2\cap C_1^{\perp }\). From the definition of a non-degenerate code, we obtain an EA RS code to be a non-degenerate code if every element in \(C_1\cap C_2^{\perp }\) and \(C_2\cap C_1^{\perp }\) has a weight of at least \(d'\).
Proposition 1
The EA RS code satisfies the following properties:
-
a.
The EA RS code is a non-degenerate code.
-
b.
The minimum distance of the EA RS code is \(d_m\).
-
c.
The EA RS code saturates the quantum Singleton bound.
Proof
As the EA RS code is an \(((n,p^{(k(n-2d_m+2+n_e))},d'\ge d_m))_{p^k}\) code, the minimum distance \(d'\) of the code is atleast \(d_m\), i.e., \(d' \ge d_m\). We can write the code \(((n,p^{(k(n-2d_m+2+n_e))},d'\) \(\ge d_m))_{p^k}\) as an \([[n,n-2d_m+2+n_e,d']]_{p^k}\) code. The minimum distance \(d'\) of an EA CSS codeFootnote 5 obtained from \(C_1\) and \(C_2\) is \(\mathrm {min}(d_{\mathrm {H}}(C_1\setminus C_2^{\perp }),d_{\mathrm {H}}(C_2\setminus C_1^{\perp }))\), where \(d_{\mathrm {H}}\) is the minimum hamming weight of the vectors in the set [28].
We consider the following two cases:
Case A: \(\mathbf {2(d_m-1) < n}\)
As the minimum distance of both \(C_1\) and \(C_2\) is \(d_m\), the codewords in \(C_1\) and \(C_2\) have a weight of at least \(d_m\). Thus, the vectors in \(C_1\setminus C_2^{\perp }\) and \(C_2\setminus C_1^{\perp }\) also have a weight of at least \(d_m\). As the dual of an \([n,n-d_m+1,d_m]\) RS code is an \([n,d_m-1,n-d_m+2]\) RS code, the minimum distance of both \(C_1^{\perp }\) and \(C_2^{\perp }\) is \(n-d_m+2\) [34]. Thus, the codewords in \(C_1^{\perp }\) and \(C_2^{\perp }\) have weight of at least \(n-d_m+2\). As \(2(d_m-1) < n\), we obtain \(d_m < n-d_m+2\). Thus, all codewords in \(C_1\) and \(C_2\) of weight \(d_m\) belong to \(C_1\setminus C_2^{\perp }\) and \(C_2\setminus C_1^{\perp }\), respectively. Thus, the minimum distance \(d'\) of the EA RS code is \(\mathrm {min}(d_{\mathrm {H}}(C_1\setminus C_2^{\perp }),d_{\mathrm {H}}(C_2\setminus C_1^{\perp })) = d_m\).
As the minimum distance of \(C_1^{\perp }\) and \(C_2^{\perp }\) is \(n-d_m+2 > d_m\), the weight of elements in \(C_1\cap C_2^{\perp }\) and \(C_2\cap C_1^{\perp }\) have a weight of at least \(n-d_m+2\) and greater than \(d_m\). From Lemma 6, the EA RS code is a non-degenerate code as all elements in \(C_1\cap C_2^{\perp }\) and \(C_2\cap C_1^{\perp }\) have weight of at least \(d'=d_m\). The quantum Singleton bound for an \([[n,l,d']]_{p^k}\) non-degenerate EA stabilizer code is \(2(d'-1) \le n+n_e-l\) [16]. Thus, the \([[n,n-2d_m+2+n_e,d_m]]_{p^k}\) non-degenerate EA RS code saturates the quantum Singleton bound.
Case B: \(\mathbf {2(d_m-1)\ge n}\)
As the minimum distance to \(C_1\) and \(C_2\) are both \(d_m\), the vectors in \(C_1\setminus C_2^{\perp }\) and \(C_2\setminus C_1^{\perp }\) have a weight of at least \(d_m\). The codewords in the \([n,d_m-1,n-d_m+2]\) RS codes \(C_1^{\perp }\) and \(C_2^{\perp }\) have a weight of at least \(n-d_m+2\). As \(C_1\), \(C_2\), \(C_1^{\perp }\), and \(C_2^{\perp }\) are RS codes of length n, their codewords are generated by the rows of the Vandermonde matrix. The codewords of \(C_1^{\perp }\) and \(C_2^{\perp }\) are generated by the matrices \(H_{b1}\) and \(H_{b2}\). From Lemma 5, the codewords of \(C_1\) and \(C_2\) are generated by the matrices obtained from \(H_{n-b_1+1}\) and \(H_{n-b_2+1}\), by replacing \(d_m\) with \(n-d_m+2\).
We first show that there exists at least one vector in \(C_1\setminus C_2^{\perp }\) and \(C_2\setminus C_1^{\perp }\) with weight \(d_m\). We prove the result for \(C_1\setminus C_2^{\perp }\). The proof is similar for \(C_2\setminus C_1^{\perp }\). In Table 1, three exhaustive cases have been provided for the EA RS code based on the relation between the parameters \(b_1\), \(b_2\), \(d_m\), and n. As \(2(d_m-1) \ge n\), we do not consider Case 1 from Table 1. As Case 3 from Table 1 results in a zero-rate codeFootnote 6, we only consider Cases 2(a) and 2(b). We show that every vector in \(C_1\cap C_2^{\perp }\) has weight greater than \(d_m\); hence, there exists a vector of weight \(d_m\) in \(C_1\setminus C_2^{\perp }\). We note that all rows of the generator matrix \(A=[\alpha ^{(n-b_1+i)(z-1)}]\) of \(C_1\) and all rows of the generator matrix \(H_{b2}\) of \(C_2^{\perp }\) are rows of the \((n\times n)\)-Vandermonde matrix. The rows of the Vandermonde matrix that generate \(C_1\cap C_2^{\perp }\) are the rows common to both A and \(H_{b2}\). As \(A=[\alpha ^{(n-b_1+i)(z-1)}]\) and \(H_{b2}=[\alpha ^{(b_2-1+j)(z-1)}]\), the rows are equal if \(n-b_1+i = b_2-1+j\), where \(i \in \{1,\dots ,n-d_m+1\}\) and \(j \in \{1,\dots ,d_m-1\}\). Thus, as \(v=(b_1+b_2-2)~\mathrm {mod}~n\), we obtain
For Case 2(a) in Table 1, as \(n-v < d_m \Rightarrow n-v \le d_m-1\) and \(j \in \{1,\dots ,d_m-1\}\), from Eq. (114), we obtain the range of j for the rows common to both A and \(H_{b2}\) to be \(j\in \{n-v,\dots ,d_m-1\}\). The set \(\{n-v,\dots ,d_m-1\}\) corresponds to \((d_m-1)-(n-v)+1 = d_m-(n-v)\) rows. Thus, the dimension of \(C_1\cap C_2^{\perp }\) is \(d_m-n+v\). As the rows of the Vandermonde matrix generate \(C_1\cap C_2^{\perp }\), it is an \([n,d_m-n+v,2n-d_m-v+1]\) RS codeFootnote 7. As \(2(d_m-1)+v < 2n\) for Case 2(a) of Table 1, we obtain \(2(d_m-1)+v \le 2n-1 \Rightarrow 2n-d_m-v+1 \ge d_m\). When \(2n-d_m-v+1 = d_m\), from Theorem 4, \(n_e = n-v-1\) and the EA RS code obtained is a zero-rate code as \(n+n_e-2(d_m-1)=0\). As this code has only one basis codewordFootnote 8, there is no concept of minimum distance. When \(2n-d_m-v+1 > d_m\), there is no vector of weight \(d_m\) in \(C_1\cap C_2^{\perp }\) as the minimum distance of \(C_1\cap C_2^{\perp }\) is \(2n-d_m-v+1\). As the minimum distance of \(C_1\) is \(d_m\), there exists at least one vector in \(C_1\) of weight \(d_m\). Thus, there exists at least one vector of weight \(d_m\) in \(C_1\setminus C_2^{\perp }\) and the minimum distance of the EA RS code is \(d_m\).
For Case 2(b), as \(n-v\ge d_m\) and \(j \in \{1,\dots ,d_m-1\}\), from Eq. (114), we obtain the range of j for the rows common to both A and \(H_{b2}\) to be \(j\in \{1,\dots ,n-v-d_m\}\) (as the row indices are modulo n) that corresponds to \(n-v-d_m\) rows. Similar to Case 2(a), we obtain \(C_1\cap C_2^{\perp }\) to be an \([n,n-v-d_m,v+d_m+1]\) RS code. As \(v+1 >0\), we obtain the minimum distance \(v+d_m+1\) of \(C_1\cap C_2^{\perp }\) to be greater than \(d_m\), i.e., \(v+d_m+1> d_m\); hence, \(C_1\cap C_2^{\perp }\) does not contain any vector of weight \(d_m\). As \(C_1\) has minimum distance of \(d_m\), there exists a vector of weight \(d_m\) in \(C_1\setminus C_2^{\perp }\); hence the minimum distance of the EA RS code is \(d_m\).
For both Cases 2(a) and 2(b), the minimum distance of \(C_1\cap C_2^{\perp }\) is greater than the minimum distance \(d'=d_m\) of the EA RS code. From Lemma 6, we obtain the EA RS code to be a non-degenerate code. We note that the \([[n,n-2d_m+2+n_e,d_m]]_{p^k}\) non-degenerate EA RS code saturates the quantum Singleton bound. [16]. \(\square \)
D Summation of powers of \(\varvec{\omega }\) containing \(\varvec{\mathrm {Tr}_{p^k/p}}\) operator
Lemma 7
For \(\gamma \in {\mathbb {F}}_{p^k}\), \(\underset{\theta \in {\mathbb {F}}_{p^k}}{\sum }\omega ^{\mathrm {Tr}_{p^k/p}(\gamma \theta )} = \delta _{\gamma ,0}p^k\).
Proof
We consider the two cases of \(\gamma \ne 0\) and \(\gamma =0\) separately to prove our claim.
Case 1: \(\varvec{\gamma \ne 0}.\)
Every \(\theta \in {\mathbb {F}}_{p^k}\) can be written as \(\theta = \underset{i=0}{\overset{k-1}{\sum }}\theta _i\alpha ^i\), where \(\theta _0, \theta _1, \dots , \theta _{k-1} \in {\mathbb {F}}_p\). Let \(m = \mathrm {Tr}_{p^k/p}(\gamma \theta ) \in {\mathbb {F}}_p\).
Case (a): \(\varvec{m=0}\)
If \(m=0\), then for every \(f \in {\mathbb {F}}_p\),
as \(\mathrm {Tr}_{p^k/p}(\cdot )\) is an \({\mathbb {F}}_p\)-linear function and \(f \in {\mathbb {F}}_p\).
We consider the set \(M_0 = \{\theta \in {\mathbb {F}}_{p^k} : \mathrm {Tr}_{p^k/p}(\gamma \theta )=0\}\). To obtain the cardinality of the set \(M_0\), we note that
as \(\mathrm {Tr}_{p^k/p}(\cdot )\) is an \({\mathbb {F}}_p\)-linear function and \(\theta _i \in {\mathbb {F}}_p\), where \(i\in \{0,\dots , k-1\}\). From Eq. (115), we obtain
As every \(\theta = \underset{i=0}{\overset{k-1}{\sum }}\theta _i\alpha ^i \in M_0\) satisfies Eq. (116), the cardinality \(|M_0|\) is equal to the size of the space orthogonal to the space generated by \([\mathrm {Tr}_{p^k/p}(\gamma )~\dots \mathrm {Tr}_{p^k/p}(\gamma \alpha ^{k-1})]^{\mathrm {T}}\). The dimension of the space generated by \([\mathrm {Tr}_{p^k/p}(\gamma )~\dots \mathrm {Tr}_{p^k/p}(\gamma \alpha ^{k-1})]^{\mathrm {T}}\) is 1. The dimension of the space \({\mathbb {F}}_{p}^{k}\), to which \([\theta _0~\dots ~\theta _{k-1}]^{\mathrm {T}}\) belongs, is k. Thus, the dimension of the orthogonal space is \((k-1)\) and
as the elements of the vector \([\theta _0~\dots ~\theta _{k-1}]\) belong to \({\mathbb {F}}_{p}\).
Case (b): \(\varvec{m\ne 0}\)
If \(m \ne 0\), then, for \(f\in {\mathbb {F}}_p\backslash \{0\}\), we obtain \(\mathrm {Tr}_{p^k/p}(\gamma (f\theta )) = f\mathrm {Tr}_{p^k/p}(\gamma \theta )\), and
where \(l= fm \in {\mathbb {F}}_p\backslash \{0\}\), because, by the closure property of \({\mathbb {F}}_p\), \(\{fm\}_{f\in {\mathbb {F}}_p\backslash \{0\}} = \{f\}_{f\in {\mathbb {F}}_p\backslash \{0\}}\) as \(m\!\ne \! 0\) and \(f,\!m\! \in \!{\mathbb {F}}_p\); hence, the summation of \(\omega ^{fm}\) over f is equal to the summation of \(\omega ^l\) over l.
As the sum of all the \(p^{\mathrm {th}}\) roots of unity is 0, we obtain
For every \(\theta \in {\mathbb {F}}_{p^k} \setminus M_0\), we can combine \((p-1)\) elements to form the set \({\mathcal {B}}_{\theta } :=\{f\theta \}_{f=1}^{p-1}\). For some \(j\in {\mathbb {F}}_{p} \setminus \{0\}\), let us consider \(\theta ' = j\theta \). Then, the set \({\mathcal {B}}_{\theta '}\) is
As \(f,j\in {\mathbb {F}}_p \backslash \{0\}\), by closure property of \({\mathbb {F}}_p\), \(\{fj\}_{f=1}^{p-1} = \{f\}_{f=1}^{p-1}\). From Eq. (120), by considering \(\{fj\}_{f=1}^{p-1} = \{f\}_{f=1}^{p-1}\), we obtain
From Eq. (121), the set \({\mathcal {B}}_{\theta '}\) considered for any element \(\theta ' = f\theta \) in the set \({\mathcal {B}}_{\theta }\) will produce the same set \({\mathcal {B}}_{\theta }\).
Let K be the set of \(\theta \)s for which \({\mathcal {B}}_{\theta }\)s are distinct. If \(\theta \) satisfies \(\mathrm {Tr}_{p^k/p}(\gamma \theta )\ne 0\), then it belongs to one of these K sets. For each \(\theta \in K\), from Eq. (119), we have
The size of each \({\mathcal {B}}_{\theta }\) is \(p-1\) as \({\mathcal {B}}_{\theta } = \{f\theta \}_{f=1}^{p-1}\). Using Eq. (117), the number of distinct sets \({\mathcal {B}}_{\theta }\), where \(\theta \in {\mathbb {F}}_{p^k} \setminus M_0\), is equal to
From Case (a) and Case (b) in this proof, we obtain
where the first part of the summation corresponds to the elements of \(M_0\) and the second part of the summation corresponds to the \(p^{k-1}\) sets \(B_{\theta }\) for \(\theta \in K\).
Substituting Eqs. (122) and (123) in Eq. (124), and as \(\mathrm {Tr}_{p^k/p}(\gamma \theta ) = 0\) for \(\theta \in M_0\), we obtain
Case 2: \(\varvec{\gamma = 0.}\)
From Eqs. (125) and (126),\( \underset{\theta \in {\mathbb {F}}_{p^k}}{\sum }\!\!\!\omega ^{\mathrm {Tr}_{p^k/p}(\gamma \theta )} \!=\! \delta _{\gamma ,0}p^k\!\!.\) \(\square \)
Proofs of relations (R1)–(R10)
In this appendix, we provide a few relations with proofs that have been used in the main body of this paper. For \(\beta \in {\mathbb {F}}_{p^k}\), the following relations hold true:
- (R1):
-
\(\varvec{\mathrm {Q}(\mathrm {FFFT})\mathrm {X}_i^{(p^k)}(\beta )(\mathrm {Q}(\mathrm {FFFT}))}^{\varvec{-1}}\varvec{=}\underset{\varvec{j=0}}{\overset{\varvec{n-1}}{\varvec{\otimes }}}\varvec{\mathrm {X}}^{\varvec{(p^k)}}\varvec{(\beta \alpha }^{\varvec{j(i-1)}}\varvec{),}~\varvec{\forall }~\varvec{i\in }\{\varvec{1,}\dots ,\varvec{n}\}\) .
Proof
For \(i\in \{1,\dots ,n\}\) and \(\beta \in {\mathbb {F}}_{p^k}\), we have
as \(\mathrm {FFFT}(\cdot )\) is a linear function .
Let \(\varvec{\theta _2'} = \mathrm {FFFT}(\varvec{\theta _2})\), then \(\varvec{\theta _2} = \mathrm {FFFT}^{-1}(\varvec{\theta _2'})\). As \(\mathrm {FFFT}\) is an invertible function, for every \(\varvec{\theta _2} \in {\mathbb {F}}_{p^k}^n\) we obtain a unique \(\varvec{\theta _2'} = \mathrm {FFFT}(\varvec{\theta _2}) \in {\mathbb {F}}_{p^k}\). Thus, the set \(\{\varvec{\theta _2'} = \mathrm {FFFT}(\varvec{\theta _2})\}_{\varvec{\theta _2}\in {\mathbb {F}}_{p^k}^{n}}\) contains \(p^{kn}\) unique elements in \({\mathbb {F}}_{p^k}^{n}\) as the set \(\{\varvec{\theta _2}\}_{\varvec{\theta _2}\in {\mathbb {F}}_{p^k}^{n}}\) contains \(p^{kn}\) elements. As the field \({\mathbb {F}}_{p^k}^n\) has only \(p^{kn}\) elements, the set \(\{\varvec{\theta _2'} = \mathrm {FFFT}(\varvec{\theta _2})\}_{\varvec{\theta _2}\in {\mathbb {F}}_{p^k}^{n}}\) contains all the elements of \({\mathbb {F}}_{p^k}^{n}\).
By substituting \(\varvec{\theta _2'}\) in Eq. (127), the summation over \(\varvec{\theta _2}\) taking all the values of \({\mathbb {F}}_{p^k}^n\) transforms into a summation over \(\varvec{\theta _2'}\) taking all the values of \({\mathbb {F}}_{p^k}^n\). We will use this idea throughout the paper to transform summations when we change summation variables.
From Eq. (2), \(\mathrm {FFFT}(\beta {\mathbf {e}}_i^{\mathrm {T}}) = [\beta ~\beta \alpha ^{(i-1)}~\dots ~\beta \alpha ^{(n-1)(i-1)}]\). Substituting \(\varvec{\theta _2'} = \mathrm {FFFT}(\varvec{\theta _2})\) and \(\mathrm {FFFT}(\beta {\mathbf {e}}_i^{\mathrm {T}}) = [\beta ~\beta \alpha ^{(i-1)}~\dots ~\beta \alpha ^{(n-1)(i-1)}]\) in Eq. (127), we obtain
By using the completeness relation of quantum mechanics, \(\underset{\varvec{\theta _2'}\in {\mathbb {F}}_{p^k}^{n}}{\sum }\!\!\!\! \vert \varvec{\theta _2'}\rangle \!\langle \varvec{\theta _2'}\vert = \mathrm {I}_{p^k}^{\otimes n}\), and we obtain
\(\square \)
- (R2) :
-
\(\varvec{\mathrm {Q}(\mathrm {FFFT})\mathrm {Z}_i^{(p^k)}(\beta )(\mathrm {Q}(\mathrm {FFFT}))}^{\varvec{-1}}\!\varvec{=}\!\!\underset{\varvec{j=0}}{\overset{\varvec{n-1}}{\varvec{\otimes }}}\varvec{\mathrm {Z}}^{\varvec{(p^k)}}\varvec{((p\!\!-\!1)\beta \alpha }^{\varvec{j(n-i+1)}}\varvec{),}~\varvec{\forall }\varvec{i\in }\!\{\varvec{1,}\dots ,\varvec{n}\}\).
Proof
For \(i\in \{1,\dots ,n\}\), \(\beta \in {\mathbb {F}}_{p^k}\) ,and \(\varvec{\theta _2}\in {\mathbb {F}}_{p^k}^n\), we note that
where \(\omega ^{\mathrm {Tr}_{p^k/p}(\varvec{\theta _2}\beta {\mathbf {e}}_i^{\mathrm {T}})}\) is obtained as the operator \(\mathrm {Z}_i^{(p^k)}\!(\beta )\) performs \(\mathrm {Z}^{(p^k)}\!(\beta )\) on the \(i^{\mathrm {th}}\) qudit.
For \(i\in \{1,\dots ,n\}\), we consider
Substituting Eq. (129) in Eq. (130), we obtain
Let \(\varvec{\theta _2'} = \mathrm {FFFT}(\varvec{\theta _2})\). Let \(\varvec{\theta _2'}=[t_0~t_1~\dots ~t_{n-1}]\). From Eq. (41), we have
Let \(l = (m+1)\), then l ranges from 1 to n as m ranges from 0 to \(n-1\). Substituting \(l=(m+1)\) in Eq. (132), we obtain
Substituting \(\varvec{\theta _2'} = \mathrm {FFFT}(\varvec{\theta _2})\) and Eq. (133) in Eq. (131), we obtain
By using the completeness relation, \(\underset{\varvec{\theta _2'}\in {\mathbb {F}}_{p^k}^{n}}{\sum }\!\!\!\! \vert \varvec{\theta _2'}\rangle \langle \varvec{\theta _2'}\vert = \mathrm {I}_{p^k}^{\otimes n}\). Thus, from Eq. (134),
\(\square \)
- (R3) :
-
\(\varvec{\mathrm {Q(FFFT)}}\left( \underset{\varvec{j=0}}{\overset{\varvec{n-1}}{\varvec{\otimes }}}\varvec{\mathrm {X}}^{\varvec{(p^k)}}\varvec{(\beta \alpha }^{\varvec{ij}})\right) \varvec{(\mathrm {Q(FFFT))}}^{\varvec{-1}} =\varvec{\mathrm {X}}_{\varvec{(n-i+1)}}^{\varvec{(p^k)}}\varvec{((p-1)\beta ),}~\varvec{\forall }~\varvec{i\in }\{\varvec{1,}\dots ,\varvec{n}\}\).
Proof
For \(i\in \{1,\dots , n\}\) and \(\beta \in {\mathbb {F}}_{p^k}\), we have
From Eq. (135), the operator \(\underset{j=0}{\overset{n-1}{\otimes }}\mathrm {X}^{(p^k)}(\beta \alpha ^{ij})\) performs the operation \(\mathrm {X}^{(p^k)}(\beta \alpha ^{ij})\) on the \((j+1)^{\mathrm {th}}\) qudit, for all \(j\in \{0,\dots ,n-1\}\). For \(s\in \{1,\dots , n\}\) and \(\gamma \in {\mathbb {F}}_{p^k}\), the operator \(\mathrm {X}^{(p^k)}_s(\gamma )\) performs \(\mathrm {X}^{(p^k)}(\gamma )\) on the \(s^{\mathrm {th}}\) qudit. Thus, from Eq. (135), \(\underset{j=0}{\overset{n-1}{\otimes }}\mathrm {X}^{(p^k)}(\beta \alpha ^{ij}) = \overset{n-1}{\underset{j=0}{\prod }} \mathrm {X}^{(p^k)}_{(j+1)}(\beta \alpha ^{ij})\) and we obtain
As \(\alpha ^n = \alpha ^{p^k-1} = 1\), we note that
as \(\alpha ^{n}=1\) and the roots of unity sum to 0. Thus, from Eq. (137), we have
Substituting Eq. (138) in Eq. (136), we obtain
because \(n=p^k-1=p-1 ~(\text {in }{\mathbb {F}}_{p^k})\), and in the tensor product \(\underset{g=1}{\overset{n}{\otimes }}\mathrm {X}^{(p^k)}\left( \beta n\delta _{g,n-i+1}\right) \), only the \((n-i+1)^{\mathrm {st}}\) element is non-identity (\(\because g= (n-i+1)\)), while the rest become identity (\(\because g\ne (n-i+1) \Rightarrow \mathrm {X}^{(p^k)}(0)=\mathrm {I}_{p^k}\)). We note that \(i \in \{1,\dots ,n\} \Rightarrow (n-i+1)\in \{1,\dots ,n\}\). \(\square \)
- (R4) :
-
\(\varvec{\mathrm {Q(FFFT)}}\left( \underset{\varvec{j{=}0}}{\overset{\varvec{n{-}1}}{\varvec{\otimes }}}\varvec{\mathrm {Z}}^{\varvec{(p^k)}}\varvec{(\beta \alpha }^{\varvec{ij}})\right) \varvec{(\mathrm {Q(FFFT))}}^{\varvec{-1}} {=}\varvec{\mathrm {Z}}_{\varvec{(i+1)}}^{\varvec{(p^k)}}\varvec{(\beta ),}~\varvec{\forall }~\varvec{i\in }\{\varvec{0,}{\dots },\varvec{n-1}\}\).
Proof
For \(i\in \{0,\dots , n-1\}\) and \(\beta \in {\mathbb {F}}_{p^k}\), we have
From Eq. (139), the operator \(\underset{j=0}{\overset{n-1}{\otimes }}\mathrm {Z}^{(p^k)}(\beta \alpha ^{ij})\) performs the operation \(\mathrm {Z}^{(p^k)}(\beta \alpha ^{ij})\) on the \((j+1)^{\mathrm {th}}\) qudit, for all \(j\in \{0,\dots ,n-1\}\). For \(s\in \{1,\dots , n\}\) and \(\gamma \in {\mathbb {F}}_{p^k}\), the operator \(\mathrm {Z}^{(p^k)}_s(\gamma )\) performs \(\mathrm {Z}^{(p^k)}(\gamma )\) on the \(s^{\mathrm {th}}\) qudit. Thus, from Eq. (135), \(\underset{j=0}{\overset{n-1}{\otimes }}\mathrm {Z}^{(p^k)}(\beta \alpha ^{ij}) = \overset{n-1}{\underset{j=0}{\prod }} \mathrm {Z}^{(p^k)}_{(j+1)}(\beta \alpha ^{ij})\) and we obtain
Similar to Eq. (137), we obtain
Thus, from Eq. (141), we have
as \(g\in \{1,\dots ,n\}\) and \((n+g) \equiv g\) in the range 1 to n.
Substituting Eq. (142) in Eq. (140), we obtain
because \((p-1)n=(p-1)(p^k-1)=(p-1)(p-1) = 1 ~(\text {in }{\mathbb {F}}_{p^k})\), and in the tensor product \(\underset{g=1}{\overset{n}{\otimes }}\mathrm {Z}^{(p^k)}\left( (p-1)\beta n\delta _{g,i+1}\right) \), only the \((i+1)^{\mathrm {st}}\) element is non-identity (\(\because g= (i+1)\)), while the rest become identity (\(\because g\ne (i+1) \Rightarrow \mathrm {Z}^{(p^k)}(0)=\mathrm {I}_{p^k}\)). We note that as \(i \in \{0,\dots ,n-1\}\), we obtain \((i+1)\in \{1,\dots ,n\}\). \(\square \)
- (R5) :
-
\(\varvec{\mathrm {X}}^{\varvec{(p^k)}}\varvec{(\beta )}\varvec{\vert \epsilon \rangle = \vert \epsilon \rangle ,}\!\mathbf{ where }\varvec{\vert \epsilon \rangle =\mathrm {DFT}}^{\varvec{-1}}\varvec{\vert 0\rangle }\)
Proof
From Eq. (77),
For \(\beta \in {\mathbb {F}}_{p^k}\), we analyse the action of \(\mathrm {X}^{(p^k)}(\beta )\) on \(\vert \epsilon \rangle \) from Eq. (143) as follows:
Performing the change of variable from \(\theta _1\) to \(\theta _1' = \theta _1+\beta \) in Eq. (144) and using Eq. (143), we obtain
\(\square \)
- (R6) :
-
\(\varvec{\mathrm {Z}}^{\varvec{(p^k)}}\varvec{(\beta )}\varvec{\vert 0\rangle = \vert 0\rangle .}\)
Proof
For \(\beta \!\in \! {\mathbb {F}}_{p^k}\), \(\mathrm {Z}^{(p^k)}(\beta )\!\vert 0\rangle \!\!=\!\omega ^{\mathrm {Tr}_{p^k/p}(\beta .0)}\vert 0\rangle \!=\!\! \vert 0\rangle \). \(\square \)
- (R7) :
-
\(\varvec{(\mathrm {X}^{(p^k)}((p-1)\beta ) \otimes \mathrm {X}^{(p^k)}(\beta ))\vert \eta \rangle = \vert \eta \rangle }\).
Proof
For \(\beta \in {\mathbb {F}}_{p^k}\), from Eq. (78), we have
- (R8) :
-
\(\varvec{(\mathrm {Z}^{(p^k)}(\beta )\otimes \mathrm {Z}^{(p^k)}(\beta ))\vert \eta \rangle = \vert \eta \rangle }\)
Proof
For \(\beta \in {\mathbb {F}}_{p^k}\), from Eq. (78), we have
\(\square \)
- (R9) :
-
\(\varvec{\mathrm {DFT}_{\varvec{p^k}}~\mathrm {X}}^{\varvec{(p^k)}}\varvec{(\beta )}\varvec{\mathrm {DFT}}_{\varvec{p^k}}^{\varvec{-1}} \varvec{=\mathrm {Z}}^{\varvec{(p^k)}}\varvec{(\beta )}\)
Proof
For \(\beta \in {\mathbb {F}}_{p^k}\), from Eq. (75), we have
because \(\underset{\theta _1\in {\mathbb {F}}_{p^k}}{\sum } \vert \theta _1\rangle \langle \theta _1\vert = \mathrm {I}_{p^k}\) by completeness relation. \(\square \)
- (R10) :
-
\(\varvec{\mathrm {DFT}_{p^k}~\mathrm {Z}}^{\varvec{(p^k)}}\varvec{(\beta )}\varvec{\mathrm {DFT}}_{p^k}^{\varvec{-1}} \varvec{=\mathrm {X}}^{\varvec{(p^k)}}\varvec{(-\beta )}\)
Proof
For \(\beta \in {\mathbb {F}}_{p^k}\), from Eq. (75), we have
because \(\underset{\theta _4\in {\mathbb {F}}_{p^k}}{\sum }\vert \theta _4\rangle \!\langle \theta _4\vert = \mathrm {I}_{p^k}\) by completeness relation. \(\square \)
F Computing the elements of set \(P_{\mathrm {O}}\)
In this appendix, we show that the set \(P_{\mathrm {O}}\) is based on the ranges provided in Table 2.
We recall that the position index sets are
From Eqs. (145) and (146), when elements s and t belong to \(P_{\mathrm {X}}\) and \(P_{\mathrm {Z}}\), respectively, s and t satisfy the following inequalities:
Thus, the general form of \(s \in P_{\mathrm {X}}\) and \(t \in P_{\mathrm {Z}}\) is
The value of s and t in Eqs. (148) and (149) are considered modulo n and belong to the range 1 to n.
We next consider an element r that belongs to \(P_{\mathrm {O}}\) from Eq. (147). As \(P_{\mathrm {O}} = P_{\mathrm {X}} \cap P_{\mathrm {Z}}\), the element r belongs to both \(P_{\mathrm {X}}\) and \(P_{\mathrm {Z}}\). Thus, from Eqs. (148) and (149), for some \(i,j \in \{1,\dots , (d_m-1)\}\), we obtain
As the general form of the elements of \(P_\mathrm {X}\) and \(P_\mathrm {Z}\) in Eqs. (148) and (149) is considered modulo n, \(r = (n-(b_1-2+i))\) and \(r = (b_2+j)\) are also considered modulo n. From Eq. (18), as \(v=(b_1+b_2-2)~\mathrm {mod}~n\), Eq. (151) is same as the condition \((v+i+j)~\mathrm {mod}~n=0\) obtained in Sect. 4 to find the value of \(n_e\). Thus, i and j in Eq. (151) belong to the ranges in Table 2 that was obtained using the condition \((v+i+j)~\mathrm {mod}~n=0\). From Table 2, let the range of i be from \(i_l\) to \(i_m\), then, from Eq. (150), we obtain \(P_{\mathrm {O}} = \{n-(b_1-2+i)\}_{i=i_l}^{i_m}\). We note that the elements in the set \(P_{\mathrm {O}}\) are modulo n and range from 1 to n. The set \(P_O\) for various cases in Table 1 is provided in Supplementary material.
G Proof of Lemma 4
Proof
Let \(L_{i,j}\) be the \((i,j)^{\mathrm {th}}\) element of the lower triangular matrix L. For \(i\in \{1,\dots ,n\}\), let \(L_i\) be the matrix obtained by replacing \(i^{\mathrm {th}}\) row of an identity matrix with \(i^{\mathrm {th}}\) row of L.
We consider the matrix \(F=L_s\) and \(G=L_t\), where \(s,t\in \{1,\dots ,n\}\) and \(s\ne t\). Let \(F_{i,j}\) and \(G_{i,j}\) be the \((i,j)^{\mathrm {th}}\) elements of F and G, respectively. Based on the definition of \(L_s\) and \(L_t\), and from Eq. (152), we have
From Eq. (153), the value of the \((i,j)^{\mathrm {th}}\) element of FG is
We consider three cases, where we consider the \(s^{\mathrm {th}}\) row, \(t^{\mathrm {th}}\) row, and the rest of the rows, respectively.
Case 1: \(\varvec{i=s}\)
From Eq. (155), we obtain
Thus, the \(s^{\mathrm {th}}\) row of FG is equal to the \(s^{\mathrm {th}}\) row of L.
Case 2: \(\varvec{i=t}\)
From Eq. (155), we obtain
Thus, the \(t^{\mathrm {th}}\) row of FG is equal to the \(t^{\mathrm {th}}\) row of L.
Case 3: \(\varvec{i\ne s}\) and \(\varvec{i \ne t}\)
From Eq. (155), we obtain
Thus, the \(i^{\mathrm {th}}\) row of FG, where \(i\ne s\) and \(i \ne t\), is equal to the \(i^{\mathrm {th}}\) row of the identity matrix \(\mathrm {I}_{n}\).
Thus, the matrix \(L_sL_t = FG\) is the matrix obtained by replacing the \(s^{\mathrm {th}}\) and \(t^{\mathrm {th}}\) row of the identity matrix with the \(s^{\mathrm {th}}\) and \(t^{\mathrm {th}}\) row of L. Thus, \(L_1L_2\dots L_n\) is the matrix obtained by replacing the \(1^{\mathrm {st}}\), \(2^{\mathrm {nd}}\), \(\dots \), \(n^{\mathrm {th}}\) row of the identity matrix by the \(1^{\mathrm {st}}\), \(2^{\mathrm {nd}}\), \(\dots \), \(n^{\mathrm {th}}\) row of L, respectively, which is equal to L. \(\square \)
Rights and permissions
About this article
Cite this article
Nadkarni, P.J., Garani, S.S. Entanglement-assisted Reed–Solomon codes over qudits: theory and architecture. Quantum Inf Process 20, 129 (2021). https://doi.org/10.1007/s11128-021-03028-w
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11128-021-03028-w