Abstract
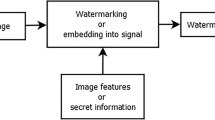
With the recent development in image editing tools the content of digital images can be easily manipulated. Research efforts are being deployed to develop passive and active methods for image authentication. It has been deemed that passive methods are not effective and not yet mature enough to detect even common image manipulations. In contrast, active methods are more efficient, especially when it comes to exposing doctored images where the changes are perfectly performed. In this work, we propose an effective perceptual entanglement-based approach for image authentication. Firstly, the image spatial blocks undergo a local encoding with global entanglement using image spectral matting. Then, the reconstruction residual is utilized for image integrity verification through image disentanglement as an inverse matting process. In our experiments, we demonstrate how a broken spatial and intensity affinity in the image induces higher residual sensitivity, thereby revealing image manipulation. Additionally, our approach is capable of pinpointing the location of tampered pixels as an explanatory authentication decision.







Similar content being viewed by others
Data availability
Availability of data and materials: The datasets analysed during the current study are available from the links http://sipi.usc.edu/database, http://www.ux.uis.no/~tranden/brodatz.html, and https://github.com/ieee8023/covid-chestxray-dataset.
References
Zheng L, Zhang Y, Thing V (2018) A survey on image tampering and its detection in real-world photos. Vis Commun Image Represent 58:380–399
Birajdar GK, Mankar VH (2013) Digital image forgery detection using passive techniques: A survey. Digit Investig. 1(20)
Hu W, Chen W, Huang D (2016) Effective image forgery detection of tampered foreground or background image based on image watermarking and alpha matte. Multimedia Tools and Applications 75:3495–2016
Garg P, Kishore R (2020) Performance comparison of various watermarking techniques. Multimedia Tools Appl 79:25921–25967
Asikuzzaman M, Pickering MR (2018) An overview of digital video watermarking. IEEE Trans Circuits Syst Video Technol 28(9):2131–2153. https://doi.org/10.1109/TCSVT.2017.2712162
Nurul K, Kamsin A, Yee P, Hameedur R (2018) A Review of Text Watermarking: Theory. Methods Appl IEEE Access 6:1–20
Hua G, Huang J, Shi Y, Thing V (2016) Twenty years of digital audio watermarking - a comprehensive review. Signal Process 128:222–242
Kumar C, Singh AK, Kumar PA (2018) Recent survey on image watermarking techniques and its application in e-governance. Multimedia Tools Appl 77:3597–3622
Shih F (2017) Digital Watermarking and Steganography: Fundamentals and Techniques. Taylor and Francis Group CRC Press, Boston
Sridhar P, Sathiya RR (2017) Crypto-watermarking for secure and robust transmission of multispectral images. In: Zaimis E (ed) International Conference on Computation of Power, Energy Information and Commuincation (ICCPEIC), Melmaruvathur, India, pp 153–163. https://doi.org/10.1109/ICCPEIC.2017.8290357
Lei B, Zhao X, Lei H, Ni D, Chen S, Zhou F, Wang T (2017) Multipurpose watermarking scheme via intelligent method and chaotic map. Multimedia Tools Appl 78:27085–27107
Singh L, Singh AK, Singh PK (2020) Secure data hiding techniques: a survey. Multimedia Tools Appl 79:15901–15921
Chandramouli R, Memon N (2001) Analysis of lsb based image steganography techniques. In: Proceedings 2001 International Conference on Image Processing (Cat. No.01CH37205), vol 3. Thessaloniki, Greece, pp 1019–1022. https://doi.org/10.1109/ICIP.2001.958299
Ping WW, Memon N (2001) Secret and public key image watermarking schemes for image authentication and ownership verification. IEEE Trans Image Process 10(10):1593–1601. https://doi.org/10.1109/83.951543
Bender W, Gruhl D, Morimoto N, Lu A (1996) Techniques for data hiding. IBM Syst J 35(3.4):313–336. https://doi.org/10.1147/sj.353.0313
Purna Kumari B, Subramanyam Rallabandi VP (2008) Modified patchwork-based watermarking scheme for satellite imagery. Signal Process 88(4):891–904. https://doi.org/10.1016/j.sigpro.2007.10.009
Pickholtz R, Schilling D, Milstein L (1982) Theory of spread-spectrum communications - a tutorial. IEEE Trans Commun 30(5):855–884. https://doi.org/10.1109/TCOM.1982.1095533
Samcovic A, Turan J (2007) Digital image watermarking by spread spectrum. In: Proceedings of the 11th Conference on 11th WSEAS International Conference on Communications - vol 11. ICCOM’07, pp 29–32. World Scientific and Engineering Academy and Society (WSEAS), Stevens Point, Wisconsin, USA (2007)
Chitra K, Venkatesan VP (2016) Spatial domain watermarking technique: An introspective study. In: Proceedings of the International Conference on Informatics and Analytics. ICIA-16, pp 1–6. Association for Computing Machinery, New York, NY, USA (2016). https://doi.org/10.1145/2980258.2980363
Mun SM, Nam SH, Jang H, Lee HK (2017) A robust blind watermarking using convolutional neural network. arXiv:1704.03248
Zhu J, Kaplan R, Johnson J, Fei-Fei L (2018) Hidden: Hiding data with deep networks. In: Ferrari V, Hebert M, Sminchisescu C, Weiss Y (eds) Computer Vision - ECCV 2018. Springer, Munich, Germany, pp 682–697
Zhong X, Huang P-C, Mastorakis S, Shih FY (2021) An automated and robust image watermarking scheme based on deep neural networks. IEEE Trans Multimedia 23:1951–1961. https://doi.org/10.1109/TMM.2020.3006415
Rafigh M, Moghaddam ME (2010) A robust evolutionary based digital image watermarking technique in dct domain. In: 2010 Seventh International Conference on Computer Graphics, Imaging and Visualization, Sydney, NSW, Australia, pp 105–109. https://doi.org/10.1109/CGIV.2010.24
Vishwakarma VP, Sisaudia V (2018) Gray-scale image watermarking based on de-kelm in dct domain. In: Procedia Computer Science:International Conference on Computational Intelligence and Data Science, vol 132. Gurugram, India, pp 1012–1020. https://doi.org/10.1016/j.procs.2018.05.017
Chang T, Pan I, Huang P (2019) A robust DCT-2DLDA watermark for color images. Multimedia Tools Appl 78:9169–9191. https://doi.org/10.1007/s11042-018-6505-4
Patra JC, Phua JE, Bornand C (2010) A novel DCT domain CRT-based watermarking scheme for image authentication surviving JPEG compression. Digit Signal Proc 20(6):1597–1611. https://doi.org/10.1016/j.dsp.2010.03.010
Tew Y, Wong K (2014) Information hiding in hevc standard using adaptive coding block size decision. In: 2014 IEEE International Conference on Image Processing (ICIP), Paris, France, pp 5502–5506. https://doi.org/10.1109/ICIP.2014.7026113
Bhatnagar G, Jonathan Wu QM, Raman B (2012) Robust gray-scale logo watermarking in wavelet domain. Computers & Electrical Engineering. 38(5), 1164–1176. https://doi.org/10.1016/j.compeleceng.2012.02.002. Special issue on Recent Advances in Security and Privacy in Distributed Communications and Image processing
Lu W, Sun W, Lu H (2012) Novel robust image watermarking based on subsampling and dwt. Multimedia Tools Appl 60(1):31–46. https://doi.org/10.1007/s11042-011-0794-1
Malik S, Kishore RR (2018) Fractional fourier transform and position shuffling based digital image watermarking scheme and its performance analysis. Int J Adv Stud Sci Res 4(1):1–7
Wang J, Du Z (2019) A method of processing color image watermarking based on the Haar wavelet. J Vis Commun Image Represent 64:102627. https://doi.org/10.1016/j.jvcir.2019.102627
Kalra GS, Talwar R, Sadawarti H (2015) Adaptive digital image watermarking for color images in frequency domain. Multimedia Tools Appl 74(17):6849–6869. https://doi.org/10.1007/s11042-014-1932-3
Hamidi M, Haziti ME, Cherifi H, Hassouni ME (2018) Hybrid Blind Robust Image Watermarking Technique Based on DFT-DCT and Arnold Transform. Multimedia Tools Appl 77(20):27181–27214. https://doi.org/10.1007/s11042-018-5913-9
Kang X-B, Zhao F, Lin G-F, Chen YJ (2018) A novel hybrid of dct and svd in dwt domain for robust and invisible blind image watermarking with optimal embedding strength. Multimedia Tools Appl 77(11):13197–13224. https://doi.org/10.1007/s11042-017-4941-1
Li D, Deng L, Bhooshan Gupta B, Wang H, Choi C (2019) A novel cnn based security guaranteed image watermarking generation scenario for smart city applications. Inf Sci 479:432–447. https://doi.org/10.1016/j.ins.2018.02.060
Zheng W, Mo S, Jin X, Qu Y, Deng F, Shuai J, Xie Z, Zheng C, Long S (2018) Robust and high capacity watermarking for image based on dwt-svd and cnn. In: 2018 13th IEEE Conference on Industrial Electronics and Applications (ICIEA), Wuhan, China, pp 1233–1237. https://doi.org/10.1109/ICIEA.2018.8397898
Sengupta S, Jayaram V, Curless B, Seitz SM, Kemelmacher-Shlizerman I (2020) Background matting: The world is your green screen. In: 2020 IEEE/CVF Conference on Computer Vision and Pattern Recognition (CVPR), Seattle, WA, USA, pp 2288–2297. https://doi.org/10.1109/CVPR42600.2020.00236
Su Q (2016) Color Image Watermarking: Algorithms and Technologies. De Gruyter, Berlin, Germany. https://doi.org/10.1515/9783110487732
Levin A, Lischinski D, Weiss Y (2006) A closed form solution to natural image matting. In: 2006 IEEE Computer Society Conference on Computer Vision and Pattern Recognition, vol 1, pp 61–68. IEEE Computer Society, Los Alamitos, CA, USA. https://doi.org/10.1109/CVPR.2006.18
Wang J, Cohen MF (2007) Simultaneous matting and compositing. In: 2007 IEEE Conference on Computer Vision and Pattern Recognition, Minneapolis, MN, USA, pp 1–8. https://doi.org/10.1109/CVPR.2007.383079
Wang J, Cohen MF (2008) Image and video matting: A survey. Foundations and Trends® in Computer Graphics and Vision. 3(2), 97–175. https://doi.org/10.1561/0600000019
He K, Sun J, Tang X (2011) Single Image Haze Removal Using Dark Channel Prior. IEEE Trans Pattern Anal Mach Intell 33(12):2341–2353. https://doi.org/10.1109/TPAMI.2010.168
Dai S, Wu Y (2008) Motion from blur. In: 2008 IEEE Conference on Computer Vision and Pattern Recognition, Anchorage, AK, USA, pp 1–8. https://doi.org/10.1109/CVPR.2008.4587582
Fan J, Shen X, Wu Y (2010) Closed-loop adaptation for robust tracking. In: Daniilidis K, Maragos P, Paragios N (eds) Computer Vision - ECCV 2010. Springer, Berlin, Heidelberg, pp 411–424
Hsu E, Mertens T, Paris S, Avidan S, Durand F (2008) Light mixture estimation for spatially varying white balance. ACM Trans Graph 27(3):1–7. https://doi.org/10.1145/1360612.1360669
Levin A, Lischinski D, Weiss Y (2008) A closed-form solution to natural image matting. IEEE Trans Pattern Anal Mach Intell 30(2):228–242. https://doi.org/10.1109/TPAMI.2007.1177
Xiao D, Deng M, Zhu X (2015) A reversible image authentication scheme based on compressive sensing. Multimedia Tools Appl 74(18):7729–7752. https://doi.org/10.1007/s11042-014-2017-z
Ebert DS, Musgrave FK, Peachey D, Perlin K, Worley S (2002) Texturing and Modeling: A Procedural Approach, 3rd edn. Morgan Kaufmann Publishers Inc., San Francisco, CA, USA
Ansari I, Pant M, Ahn CW (2016) SVD based fragile watermarking scheme for tamper localization and self-recovery. Int J Mach Learn Cybern 7. https://doi.org/10.1007/s13042-015-0455-1
Chen T-H, Huang W-L, Lin Y (2010) Chaos-based image integrity authentication code. In: Proceedings of the 2010 Sixth International Conference on Intelligent Information Hiding and Multimedia Signal Processing. IIH-MSP ’10, pp 13–16. IEEE Computer Society, Darmstadt, Germany. https://doi.org/10.1109/IIHMSP.2010.11
Acknowledgements
We gratefully acknowledge the support of the Computer Research Institute of Montreal (CRIM), the Ministère de l’Économie et de l’Innovation (MEI) of Quebec, and The Natural Sciences and Engineering Research Council of Canada (NSERC).
Funding
The research leading to these results received funding from The Natural Sciences and Engineering Research Council of Canada (NSERC) under Grant Agreement No RGPIN-2020-05171.
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Ethical Approval and Consent to participate
Not Applicable
Conflict of interest/Competing interests
The authors have no relevant financial or non-financial interests to disclose.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Dahmane, M. A perceptual entanglement-based image authentication with tamper localisation. Multimed Tools Appl 83, 38193–38208 (2024). https://doi.org/10.1007/s11042-023-16791-y
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-023-16791-y