Abstract
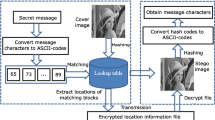
Generally, in watermarking techniques the size of the watermark is very small when compared to the host image. In other words, a little amount of watermark is embedded in the huge quantity of image pixels as the notice of legitimate ownership. Contrary to that idea, this is an attempt in which the capacity of watermarking is improved by embedding huge amount of watermark efficiently in the less quantity of image pixels. The core idea behind the proposed approach is to select watermarkable pixels from the host image based on the census transform and hamming distance followed by the embedding which is done by proposed spectral decompositions, i.e., Hankel, Circulant and Topelitz spectral decomposition. Finally, a reliable watermark extraction scheme is developed which is free from the false-positive detection problem of singular values. The experimental evaluation demonstrates that the proposed scheme is expeditiously able to withstand a variety of extreme attacks and highly suitable for covert communications.



















Similar content being viewed by others
References
Agarwal H, Atrey PK, Raman B (2015) Image watermarking in real oriented wavelet transform domain. Multimedia Tools and Applications 74(23):10883–10921
Barni M, Bartolini F (2004) Watermarking systems engineering: enabling digital assets security and other applications. Marcel Dekker Inc., New York
Bhatnagar G, Raman B (2009a) Robust encryption based watermarking in fractional wavelet domain. Recent advances in multimedia signal processing and communications in the series studies in computational intelligence, vol 231. Springer, pp 375–416
Bhatnagar G, Raman B (2009b) A new reference watermarking scheme based on DWT-SVD. Computer Standards and Interfaces 31(5):1002–1013
Bhatnagar G, Wu QMJ (2013) Biometrics inspired watermarking based on a fractional dual tree complex wavelet transform. Futur Gener Comput Syst 29(1):182–195
Chitla A, Mohan MC (2016) An adaptive quin-tree decomposition (AQTD) technique in image authentication through Lossless Watermarking (LWM). Pattern Recognition and Image Analysis 26(1):69–81
Deng C, Gao X, Li X, Tao D (2009) A local Tchebichef moments-based robust image watermarking. Signal Process 89(8):1531–1539
Flusser J, Zitova B, Suk T (2009) Moments and moment invariants in pattern recognition. Wiley, UK
Gray RM (2006) Toeplitz and circulant matrices: a review. Foundations and Trends in Communications and Information Theory 2(3):155–239
Guo J-M, Liu Y-F (2012) High capacity data hiding for Error-Diffused block truncation coding. IEEE Trans Image Process 21(12):4808–4818
Hsia SC, Jou IC, Hwang SM (2002) A gray level watermarking algorithm using double layer hidden approach. IEICE Trans Fundam E85-A(2):463–471
Hu M (1962) Visual pattern recognition by moment invariants. IRE Transcations on Information Theory IT-8:179–187
Huang HC, Fang WC (2010) Techniques and applications of intelligent multimedia data hiding. Telecommun Syst 44:241–51
Irany BM, Guo XC, Hatzinakos D (2011) A high capacity reversible multiple watermarking scheme for medical images. Proc Int Conf Digital Signal Processing:1–6
Karner H, Schneid J, Ueberhuber CW (2003) Spectral decomposition of real circulant matrices. Linear Algebra Appl 367:301–311
Korus P, Bialas J, Dziech A (2014) A new approach to high-capacity annotation watermarking based on digital fountain codes. Multimedia Tools and Applications 68 (1):59–77
Kundur D, Hatzinakos D (2004) Towards robust logo watermarking using meltiresolution image fusion. IEEE Trans Math 6:185–197
Li L, Pan JS, Yuan X (2001) High-capacity Watermark Embedding Based on Invariant Regions of Visual Saliency. IEICE Transactions on Fundamentals of Electronics, Communications and Computer Sciences E94-A(2):889–893
Li L, Qian J, Pan JS (2011) Characteristic region based watermark embedding with RST invariance and high-capacity. AEU-International Journal of Electronics and Communications 65(5):435–442
Lian S (2008) Multimedia content encryption: techniques and applications. Auerbach Publications, boston
Lin WH, Horng SJ, Kao TW, Fan P, Lee CL, Pan Y (2008) An efficient watermarking method based on significant difference of wavelet coefficient quantization. IEEE Trans Multimed 10(5):746–757
Luk FT, Qiao S (2003) A fast singular value algorithm for Hankel matrices. Fast Algorithms for Structured Matrices: Theory and Applications, Contemporary Mathematics, American Mathematical Society 323:169–177
Pandey P, Kumar S, Singh SK (2014) A robust logo watermarking technique in divisive normalization transform domain. Multimedia Tools and Applications 72:2653–2677
Run R-S, Horng S-J, Lai J-L, Kao T-W, Chen R-J (2012) An improved SVD-based watermarking technique for copyright protection. Expert Syst Appl 39 (1):673–689
Satish K, Jayakar T, Tobin C, Madhavi K, Murali K (2004) Chaos based spread spectrum image steganography. IEEE Trans Consum Electron 50(2):587–590
Singh AK, Dave M, Mohan A (2014) Hybrid technique for robust and imperceptible image watermarking in DWT-DCT-SVD domain. National Academy Science Letters 37(4):351–358
Singh AK, Kumar B, Dave M, Mohan A (2014) Robust and imperceptible dual watermarking for telemedicine applications. Wirel Pers Commun 80(4):1415–1433
Singh AK, Dave M, Mohan A (2015) Robust and secure multiple watermarking in wavelet domain. Journal of Medical Imaging and Health Informatics 5(2):406–414
Singh AK, Dave M, Mohan A (2015) Multilevel encrypted text watermarking on medical images using spread-spectrum in DWT domain. Wireless Personal Communications: An International Journal 83(3):2133–2150
Singh AK, Dave M, Mohan A (2016) Improved Hybrid Technique for Robust and Imperceptible Multiple Watermarking using Medical Images. Multimedia Tools and Applications 75:8381–8401
Song C, Sudirman S, Merabti M (2012) A robust region-adaptive dual image watermarking technique. J Vis Commun Image Represent 23(3):549–568
Strang G (1993). Wellesley-Cambridge Press, Introduction to Linear Algebra
Tang L-L, Huang CT, Pan J-S, Liu C-Y (2015) Dual watermarking algorithm based on the Fractional Fourier Transform. Multimedia Tools and Applications 74 (12):4397–4413
Wang J, Lian S, Wang J (2015) Hybrid additive multi-watermarking and decoding. Multimedia Systems 21(4):345–361
Wu Y (2005) On the security of an SVD-based ownership watermarking. IEEE Transactions on Multimedia 7(4):624–627
Zabih R, Woodfill J (1994) Non-parametric local transforms for computing visual correspondence. Proc European Conf Computer Vision:151–158
Zhang X, Li K (2005) Comments on an SVD-based watermarking scheme for protecting rightful ownership. IEEE Transactions Multimedia 7(3):593–594
Acknowledgments
This work was supported by the Science and Engineering Research Board, DST, India.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Bhatnagar, G. Robust covert communication using high capacity watermarking. Multimed Tools Appl 76, 3783–3807 (2017). https://doi.org/10.1007/s11042-016-3978-x
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-016-3978-x