Abstract
Blind quantum computation (BQC) enables a client with less quantum computational ability to delegate her quantum computation to a server with strong quantum computational power while preserving the client’s privacy. Generally, many-qubit entangled states are often used to complete BQC tasks. But for a large-scale entangled state, it is difficult to be described since its Hilbert space dimension is increasing exponentially. Furthermore, the number of entangled qubits is limited in experiment of existing works. To tackle this problem, in this paper we propose a universal BQC protocol based on measurement with minor resources, where the trap technology is adopted to verify correctness of the server’s measurement outcomes during computation and testing process. In our model, there are two participants, a client who prepares initial single-qubit states and a server that performs universal quantum computation. The client is almost classical since she does not require any quantum computational power, quantum memory. To realize the client’s universal BQC, we construct an \(m\times n\) latticed state composed of six-qubit cluster states and eight-qubit cluster states, which needs less qubits than the brickwork state. Finally, we analyze and prove the blindness, correctness, universality and verifiability of our proposed BQC protocol.



Similar content being viewed by others
References
Deutsch, D.: Quantum theory, the Church–Turing principle and the universal quantum computer. Proc. R. Soc. Lond. A Math. Phys. Eng. Sci. 400, 97–117 (1985)
Deutsch, D.: Quantum computational networks. Proc. R. Soc. Lond. A Math. Phys. Eng. Sci. 425, 73–90 (1989)
Griffiths, R.B., Niu, C.S.: Semiclassical Fourier transform for quantum computation. Phys. Rev. Lett. 76, 3228–3231 (1996)
Feynman, R.P.: Simulating physics with computers. Int. J Theor. Phys. 21, 467–488 (1982)
Childs, A.M.: Secure assisted quantum computation. Quantum Inf. Comput. 5, 456–466 (2005)
Fisher, K.A.G., Broadbent, A., Shalmet, L.K., Yan, Z., Lavoie, J., Prevedel, R., Jennewein, T., Resch, K.J.: Quantum computing on encrypted data. Nat. Commun. 5, 3074 (2014)
Broadbent, A.: Delegating private quantum computations. Can. J. Phys. 93, 941–946 (2015)
P\(\acute{e}\)rez-Delgado, C.A., Fitzsimons, J.F.: Iterated gate teleportation and blind quantum computation. Phys. Rev. Lett. 114, 220502 (2015)
Kashefi, E., Pappa, A.: Multiparty delegated quantum computing. Cryptography 1(2), 1–20 (2017)
Morimae, T., Fujii, K.: Blind quantum computation protocol in which Alice only makes measurements. Phys. Rev. A 87, 050301 (2013)
Broadbent, A., Fitzsimons, J., Kashefi, E.: Universal blind quantum computation. In: Proceedings of the 50th Annual IEEE Symposium on Foundations of Computer Science, pp. 517–526 (2009)
Morimae, T., Dunjko, V., Kashefi, E.: Ground state blind quantum computation on AKLT states. Quantum Inf. Comput. 15, 200–234 (2015)
Morimae, T., Fujii, K.: Blind topological measurement-based quantum computation. Nat. Commun. 3, 1036 (2012)
Morimae, T.: Continuous-variable blind quantum computation. Phys. Rev. Lett. 109, 230502 (2012)
Barz, S., Kashefi, E., Broadbent, A., Fitzsimons, J.F., Zeilinger, A., Walther, P.: Demonstration of blind quantum computing. Science 335(6066), 303–308 (2012)
Sueki, T., Koshiba, T., Morimae, T.: Ancilla-driven universal blind quantum computation. Phys. Rev. A 87, 060301 (2013)
Dunjko, V., Kashefi, E., Leverrier, A.: Blind quantum computing with weak coherent pulses. Phys. Rev. Lett. 108, 200502 (2012)
Giovannetti, V., Maccone, L., Morimae, T., Rudolph, T.G.: Efficient universal blind quantum computation. Phys. Rev. Lett. 111, 230501 (2013)
Mantri, A., P\(\acute{e}\)rez-Delgado, C.A., Fitzsimons, J.F.: Optimal blind quantum computation. Phys. Rev. Lett. 111, 230502 (2013)
Morimae, T., Fujii, K.: Secure entanglement distillation for double-server blind quantum computation. Phys. Rev. Lett. 111, 020502 (2013)
Li, Q., Chan, W.H., Wu, C., Wen, Z.H.: Triple-server blind quantum computation using entanglement swapping. Phys. Rev. A 89, 040302 (2014)
Huang, H.L., Zhao, Y.W., Li, T., Li, F.G., Du, Y.T., Fu, X.Q., Zhang, S., Wang, X., Bao, W.S.: Homomorphic encryption experiments on ibm’s cloud quantum computing platform. Front. Phys. 12(1), 120305 (2017)
Sheng, Y.B., Zhou, L.: Deterministic entanglement distillation for secure double-server blind quantum computation. Sci. Rep. 5, 7815 (2015)
Takeuchi, Y., Fujii, K., Ikuta, R., Yamamoto, T., Imoto, N.: Blind quantum computation over a collective-noise channel. Phys. Rev. A 93, 052307 (2016)
Morimae, T.: Verification for measurement-only blind quantum computing. Phys. Rev. A 89, 060302 (2014)
Hayashi, M., Morimae, T.: Verifiable measurement-only blind quantum computing with stabilizer testing. Phys. Rev. Lett. 115, 220502 (2015)
Gheorghiu, A., Kashefi, E., Wallden, P.: Robustness and device independence of verifiable blind quantum computing. New J. Phys. 17, 083040 (2015)
Fitzsimons, J.F., Kashefi, E.: Unconditionally verifiable blind quantum computation. Phys. Rev. A 96, 012303 (2017)
Morimae, T.: Measurement-only verifiable blind quantum computing with quantum input verification. Phys. Rev. A 94, 042301 (2016)
Broadbent, A.: How to verify a quantum computation. Theor. Comput. 14(11), 1–37 (2018)
Gheorghiu, A., Kashefi, E., Wallden, P.: Robustness and device independence of verifiable blind quantum computing. New J. Phys. 17, 083040 (2015)
Fitzsimons, J.F.: Private quantum computation: an introduction to blind quantum computing and related protocols. npj Quantum Inf. 3, 1–11 (2017)
Huang, H.L., Zhao, Q., Ma, X.F., Liu, C., Su, Z.E., Wang, X.L., Li, L., Liu, N.L., Sanders, B.C., Lu, C.Y., Pan, J.W.: Experimental blind quantum computing for a classical client. Phys. Rev. Lett. 119, 050503 (2017)
Sun, Z., Yu, J., Wang, P., Xu, L.L.: Symmetrically private information retrieval based on blind quantum computing. Phys. Rev. A 91, 052303 (2015)
Huang, H.L., Bao, W.S., Li, T., Li, F.G., Fu, X.Q., Zhang, S., Zhang, H.L., Wang, X.: Universal blind quantum computation for hybrid system. Quantum Inf. Process. 16, 199 (2017)
Marshall, K., Jacobsen, C.S., Sch\(\ddot{a}\)fermeier, C., Gehring, T., Weedbrook, C., Andersen, U.L.: Continuous-variable quantum computing on encrypted data. Nat. Comm. 7, 13795 (2016)
Horodecki, R., Horodecki, P., Horodecki, M., Horodecki, K.: Quantum entanglement. Rev. Mod. Phys. 81, 865 (2009)
Bandyopadhyay, S., Ghosh, S., Kar, G.: Locc distinguishability of unilaterally transformable quantum states. New J. Phys. 13, 123013 (2011)
Raussendorf, R., Briegel, H.J.: A one-way quantum computer. Phys. Rev. Lett. 86, 5188–5191 (2001)
Lloyd, S.: Universal quantum simulators. Science 273, 1073 (1996)
Monz, T., Schindler, P., Barreiro, J.T., Chwalla, M., Nigg, D., Coish, W.A., Harlander, M., H\(\ddot{a}\)nsel, W., Hennrich, M., Blatt, R.: 14-qubit entanglement: creation and coherence. Phys. Rev. Lett. 106, 130506 (2011)
Friis, N., Marty, O.C., Maier, H.C., Holz\(\ddot{a}\)pfel, M., Jurcevic, P., Plenio, M.B., Huber, M., Roos, C., Blatt, R., Lanyon, B.: Observation of entangled states of a fully controlled 20-qubit system. Phys. Rev. X 8, 021012 (2018)
Song, C., Xu, K., Liu, W.X., Yang, C.P., Zheng, S.B., Deng, H., Xie, Q.W., Huang, K.Q., Guo, Q.J., Zhang, L.B., Zhang, P.F., Xu, D., Zheng, D.N., Zhu, X.B., Wang, H., Chen, Y.A., Lu, C.Y., Han, S.Y., Pan, J.W.: 10-qubit entanglement and parallel logic operations with a superconducting circuit. Phys. Rev. Lett. 119, 180511 (2017)
Wang, X.L., Chen, L.K., Li, W., Huang, H.L., Liu, C., Chen, C., Luo, Y.H., Su, Z.E., Wu, D., Li, Z., Lu, H., Hu, Y., Jiang, X., Peng, C.Z., Li, L., Liu, N.L., Chen, Y.A., Lu, C.Y., Pan, J.W.: Experimental ten-photon entanglement. Phys. Rev. Lett. 117, 210502 (2016)
Danos, V., Kashefi, E., Panangaden, P.: The measurement calculus. J. ACM 54, 1–8 (2007)
Jozsa, R.: An introduction to measurement based quantum computation (2005). arXiv:quant-ph/0508124
Nielsen, M.A., Chuang, I.L.: Quantum Computation and Quantum Information. Cambridge University Press, Cambridge (2000)
McKague, M.: Interactive proofs for bqp via self-tested graph states. Theor. Comput. 12, 1–42 (2016)
Winter, A.: Coding theorem and strong converse for quantum channels. IEEE Trans. Inf. Theory 45, 02481 (1999)
Wilde, M.M.: From Classical to Quantum Shannon Theory. Cambridge University Press, Cambridge (2013)
Hayashi, M., Hajdusek, M.: Self-guaranteed measurement-based blind quantum computation. Phys. Rev. A 97, 052308 (2018)
Acknowledgements
This work was supported by the National Natural Science Foundation of China (Grant No. 62005321).
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendices
Appendix A
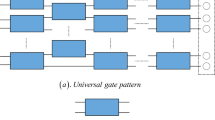
In this part, we show the schematic structures of six-qubit cluster states and eight-qubit cluster states in Figs. 4, 5 and 6. And we also give the form of graph state \(|G\rangle \) in Fig. 7.
In Figs. 4, 5 and 6, a computation starts with the input information in two left qubits, and measurements are performed from left to right. Qubits labeled by \(\alpha _x\), \(\beta _x\), \(\gamma _x\), \(\delta _x\), \(\eta _x\) (\(x=1, 2\)) are measured such that the information for each qubit flows to the right along the lines. In general, each horizontal line represents a single qubit propagation, and each vertical connection represents single qubit interaction.
In Fig. 4, \(\alpha _x\) and \(\beta _x\) are rotation angles in (a). In (b), \(R_z(\alpha _x)\) and \(R_x(\alpha _x)\) are rotations about the Z-axis and X-axis, respectively. \(R_z'(\theta )=HR_z(\theta )\), and it is applicable to Figs. 5 and 6. The lines between qubits represent the controlled-Z which are applied before the computation begins.
In Fig. 5, \(\gamma _x\), \(\delta _x\) and \(\eta _x\) are rotations about the X-axis and Z-axis in (a). Note that extra gates H and \(R_z(-\frac{\pi }{2})\) need to be performed on the above qubit and the below qubit, respectively, to get a gate CNOT. If the cluster state does not contain the final quantum outputs, the operation \(R_z(-\frac{\pi }{2})\) will be naturally corrected by performing projective measurements \(|\pm _{{\eta _t}-\frac{\pi }{2}}\rangle \Leftrightarrow \frac{e^{\frac{i\pi }{4}}}{\sqrt{2}}[|0\rangle \pm e^{i({\eta _t}-\frac{\pi }{2})}|1\rangle ]\).
In Fig. 6, eight-qubits cluster states can also be used to realize single-qubit gates H, S, T, X, Y, Z, I. In this case, Bob needs to perform an undesirable correction operation H on qubits which belong to states \(|LA\rangle \) or traps \(|R_1\rangle \), \(|R_2\rangle \). It is obvious that this increases Bob’s workload and complexity of this protocol. Therefore, we do not use the eight-qubit cluster states to implement gates H, S, T, X, Y, Z, I as far as possible. In the following, we give the structure of graph state \(|G\rangle \) (Fig. 7).
In Fig. 7, the green circles are trap qubits \(|R_1\rangle \) and these traps are randomly attached to the latticed state with a certain rule. In such case, Bob cannot precisely extract the traps from state \(|G\rangle \), so he learns nothing about the true dimension of the latticed state and the positions of the latticed state.
Appendix B
The proofs of correctness of X, Y, CNOT are shown in the following.
Proof
We first give the decompositions of gates X, Y, CNOT in Eq. (3).
where \((R_x(\pi )\otimes I)CZ=e^{\frac{i\pi }{2}}CZ(R_x(\pi )\otimes R_z(\pi ))\) and \((Y\otimes I)CZ=CZ(Y\otimes Z)\). \(\square \)
Figure 8 gives out the simplified process of gate X. For the above qubit, we have \(HR_z(\pi )H R_z(0)=R_x(\pi )\). According to the equation \((R_x(\pi )\otimes I)CZ=e^{\frac{i\pi }{2}}CZ(R_x(\pi )\otimes R_z(\pi ))\), we can move the \(R_x(\pi )\) from the right of the first CZ to the left with auxiliary gate \(R_z(\pi )\) on the below qubit. We set the angles \(\alpha _2=-\pi \), \(\beta _2=0\) and use the equation \((R_z(\theta )\otimes I)CZ=CZ(R_z(\theta )\otimes I)\) to eliminate the influence of \(R_z(\pi )\) to get the circuit (1). Finally, we realize gate X on the above qubit, so does the below qubit.
The simplified process of gate Y can be seen in Fig. 9. By the relationship \(HR_z(\pi )H=R_x(\pi )\) in the above line, we get the circuit (1). Similar to gate X, we get the circuit (2) according to the equations of \((R_x(\pi )\otimes I)CZ=e^{\frac{i\pi }{2}}CZ(R_x(\pi )\otimes R_z(\pi ))\) and \((R_z(\pi )\otimes I)CZ=CZ(R_z(\pi )\otimes I)\). Therefore, we realize gate Y on the above qubit, so does the below qubit.
The simplified process of gate CNOT can be seen in Fig. 10. Through the relationship \(HR_z(0)H\) \(R_z(0)=I\), the above line is I gate, so we get the circuit (1). By the relationship \(HR_z(-\frac{\pi }{2})H=R_x(-\frac{\pi }{2})\) and \(R_z(-\frac{\pi }{2})H=R_x(\frac{\pi }{2})R_z(\frac{\pi }{2})\), we get the circuit (2). Via the relationship \((R_z(\frac{\pi }{2})\otimes R_x(\frac{\pi }{2}))CZ(I\otimes R_x(-\frac{\pi }{2}))CZ=CNOT\), we get the gate CNOT after correcting H and \(R_z(-\frac{\pi }{2})\).\(\square \)
Appendix C
Here, we give a detailed calculation process for the range of \(\epsilon \). Since \(\epsilon \geqslant \frac{2}{3}\cdot \frac{1}{1-q}\geqslant \frac{2}{3}\cdot \frac{1+3\epsilon -6\sqrt{\epsilon }}{1-6\sqrt{\epsilon }}\), we get \(18\epsilon \sqrt{\epsilon }+3\epsilon -12\sqrt{\epsilon }+2\leqslant 0\). Suppose a function \(f(x)=18x\sqrt{x}+3x-12\sqrt{x}+2\), the first-order derivative is \(f'(x)=27\sqrt{x}+3-\frac{6}{\sqrt{x}}\). When \(f'(x)\) equals to 0, the solution is \(x\approx 0.175\), so we obtain \(f(0.175)=-1.1772\). The second-order derivative of f(x) is \(f^{''}(x)=\frac{27}{2\sqrt{x}}+\frac{3}{x\sqrt{x}}\), and we can know \(f^{''}(0.175)>0\). According to the sufficient conditions of extreme value, \(f(0.175)=-1.1772\) is the minimum value. When \(f(x)=0\), we get \(x_1\approx 0.035, x_2\approx 0.384\) calculated by MATLAB. By analyzing the relationship of \(x, f'(x)\) and f(x), we get the conclusion: The function f(x) is decreasing when \(x\in [0,0.175)\), while it is increasing when \(x\in (0.175,1]\). It is easy to get \(x\in [0.035, 0.384]\) when \(f(x)\leqslant 0\). Therefore, the range of \(\epsilon \) is [0.035, 0.384].
Moreover, for \(q\geqslant \frac{3\epsilon }{1+3\epsilon -6\sqrt{\varepsilon }}\), we verify that the range of q is [0, 1]. Suppose a function \(g(y)=\frac{3y}{1+3y-6\sqrt{y}}\), we compute the first-order derivative \(g'(y)=\frac{3-9\sqrt{y}}{(1+3y-6\sqrt{y})^2}\). The function g(y) is increasing if \(g'(y)=\frac{3-9\sqrt{y}}{(1+3y-6\sqrt{y})^2}\geqslant 0\) with \(y\in [0,\frac{1}{9}]\). Otherwise, g(y) is decreasing with \(y> \frac{1}{9}\). Naturally, we obtain \(g(y)_{max}=g(\frac{1}{9})=-\frac{1}{2}\). For \(\epsilon \in [0.035, 0.384]\), it is obvious that \(\frac{1}{9}\in [0.035, 0.384].\) Hence, it is reasonable for \(q\in [0,1].\)
Rights and permissions
About this article
Cite this article
Zhang, X. Measurement-based universal blind quantum computation with minor resources. Quantum Inf Process 21, 14 (2022). https://doi.org/10.1007/s11128-021-03365-w
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11128-021-03365-w