Abstract
We study lattice trees (LTs) and animals (LAs) on the nearest-neighbor lattice \({\mathbb {Z}}^d\) in high dimensions. We prove that LTs and LAs display mean-field behavior above dimension \(16\) and \(17\), respectively. Such results have previously been obtained by Hara and Slade in sufficiently high dimensions. The dimension above which their results apply was not yet specified. We rely on the non-backtracking lace expansion (NoBLE) method that we have recently developed. The NoBLE makes use of an alternative lace expansion for LAs and LTs that perturbs around non-backtracking random walk rather than around simple random walk, leading to smaller corrections. The NoBLE method then provides a careful computational analysis that improves the dimension above which the result applies. Universality arguments predict that the upper critical dimension, above which our results apply, is equal to \(d_c=8\) for both models, as is known for sufficiently spread-out models by the results of Hara and Slade mentioned earlier. The main ingredients in this paper are (a) a derivation of a non-backtracking lace expansion for the LT and LA two-point functions; (b) bounds on the non-backtracking lace-expansion coefficients, thus showing that our general NoBLE methodology can be applied; and (c) sharp numerical bounds on the coefficients. Our proof is complemented by a computer-assisted numerical analysis that verifies that the necessary bounds used in the NoBLE are satisfied.
Similar content being viewed by others
Avoid common mistakes on your manuscript.
1 Introduction
1.1 Motivation
Lattice trees (LTs) and lattice animals (LAs) are models for branched polymers, where excluded volume creates a self-avoidance interaction between different pieces (vertices or bonds), while the branching nature corresponds to polymers whose building blocks can have covalent bonds to more than two other building blocks. They are the branching equivalents of self-avoiding walks (see [33] for a detailed introduction, and a brief introduction to LTs and LAs as well). The study of LTs and LAs in low dimensions is quite hard and few results exist. Exceptions are the beautiful relation between LTs in dimension d and a hard-core lattice gas in dimension \(d+2\), as predicted by Parisi and Sourlas [38] and shown for a continuum model by Brydges and Imbrie [5] (see also [31] for a simple and elegant proof). As a result, also LTs and LAs in other dimensions have been investigated.
Like many statistical physics models, LTs and LAs are expected to have a so-called upper critical dimension, above which their behavior should be similar to a simpler model having less intricate interactions. For LTs and LAs, the upper critical dimension is believed to be \(d_c=8\), while this simpler model is branching random walk (BRW). BRW has gained enormous popularity in the probability community, and its critical behavior can be proved rigorously. See for example Perkins [39] for super-process limits of BRWs.
The main tool to prove that LTs and LAs show mean-field behavior is the so-called lace expansion, a perturbation expansion that compares LTs and LAs to BRWs. Many results have so far been proved for LTs, including the identification of some of their critical exponents by Hara and Slade [20] (which also applies to LAs), scaling limits of lattice trees of a given number of vertices by Derbez and Slade [7, 8], and the structure of lattice trees that are conditioned to have long paths in them by Holmes [27] (see also [24] for a recent tightness result). Almost all of these results apply to the technically simpler setting of spread-out LTs and LAs. In this paper, our goal is to study nearest-neighbor LTs and LAs above the upper critical dimension \(d_c=8\). Nearest-neighbor models are the simplest models to formulate, which makes them quite popular.
The lace expansion was first used by Brydges and Spencer in 1985 [6] to prove mean-field behavior for weakly self-avoiding walk. Since then, it has been applied (strictly) self-avoiding walks (SAW), percolation, and lattice trees and animals [17, 18, 21, 42]. It has become one of the key tools (and often the only tool available) to prove mean-field behavior of statistical mechanical models above the upper critical dimension of these models. More recent extensions include oriented percolation [26, 36, 37], the contact process [25, 40], and the Ising model [41].
The lace expansion is a perturbative method in nature, and therefore, applications of the lace expansion typically necessitate a small parameter. This small parameter tends to be the inverse of the degree of the underlying base graph. This is the reason why it is often convenient to work with so-called spread-out models, where long- but finite-range connections over a (large) distance L are possible, as then the degree of the base graph can be made large independently of the dimension. Thus, results can often be proved to hold, for L sufficiently large, all the way down to the critical dimension of the corresponding model. The simplest, and most often studied, version of these models is, however, the nearest-neighbor model. For the nearest-neighbor model, the degree of a vertex is 2d. Taking 2d large in order to obtain a small perturbation parameter then necessitates to take d large in order to prove mean-field results. This leads to suboptimal results in terms of the dimension above which the results hold. A seminal exception is SAW, where Hara and Slade [19] have proved that \(d\ge 5\) is sufficient for their perturbation analysis to hold, using a computer-assisted method and a detailed analysis of the perturbation terms arising through the lace expansion. For SAW, mean-field results are expected to be false in dimension \(d=4\). See the work using the renormalization group to identify the logarithmic corrections to mean-field behavior by Bauerschmidt, Brydges and Slade in [1, 2] and the references therein.
In this paper, we apply lace-expansion methodology to nearest-neighbor LTs and LAs. Hara and Slade [18] derived a lace expansion for LTs and LAs, and used it to prove mean-field behavior for sufficiently spread-out LTs and LAs in the optimal \(d>8\), while their results also apply to the nearest-neighbor setting in sufficiently high dimensions. Which dimension suffices was not answered by Hara and Slade, and we revisit this question. We derive a so-called non-backtracking lace expansion (NoBLE) and build upon the techniques of [21] to prove mean-field behavior for LTs in \(d\ge 16\) and for LAs for \(d\ge 17\). This extends our recent work deriving general conditions under which such a NoBLE can be applied [12], and its application to percolation for \(d>10\) [13].
The main differences of the NoBLE to the classical lace expansion method are that (i) we perturb around non-backtracking random walk, rather than around simple random walk, so that the lace-expansion coefficients are significantly smaller than in the classical lace expansion as used by Hara and Slade; (ii) our bounds on the lace-expansion coefficients are matrix-based, so as to profit maximally from the fact that loops present in the lace-expansion coefficients consist of at least four bonds in the NoBLE; and (iii) we use and provide Mathematica notebooks that implement the bounds, and that can be downloaded from the first author’s website or from the supplementary material page of the publisher. We prove that the LT and LA two-point functions satisfy a so-called infra-red bound that describes its singularity for small Fourier variables. Such an infrared bound immediately implies the finiteness of the so-called square diagram, and thus implies the existence of certain critical exponents, that take on mean-field values.
Our proof is computer-assisted, and relies on two key ingredients, that were also used to analyze percolation in high-dimensions in [13]:
-
(I)
Rigorous upper bounds on various simple random walk integrals, as first proved by Hara and Slade in [21]. This part of the analysis is unchanged compared to the Hara-Slade proof for SAWs. The crucial reason why we can use these integrals is that the non-backtracking random walk Green’s function can be explicitly described in terms of the simple random walk Green’s function. Our analysis requires us to compute 140 such integrals, corresponding to convolutions of random walk Green’s functions with itself at various points in \(\mathbb {Z}^d\). We further need to compute the number of simple random walks of lengths up to 10 ending at various points in \(\mathbb {Z}^d\), as well as the number of related self-avoiding walks and bond-self-avoiding walks. These bounds are performed in one Mathematica notebook;
-
(II)
Two additional Mathematica notebooks. The first implements the computations in our general approach to the non-backtracking lace expansion (NoBLE) in [12], and the second computes the rigorous bounds on the lace-expansion coefficients provided in the present paper, both for LTs as well as for LAs. These notebooks do nothing else than implement the bounds proved here and in [12], and rely on nothing but (many) multiplications, additions, as well as diagonalisations of two five-by-five matrices. These computations could be performed by hand, but the use of the notebooks tremendously simplifies them.
Let us remark that in dimensions \(d\ge 100\), say, we require only the values of 5 integrals, and no computations concerning the number of random walks ending at various points. The additional computations are used to obtain a sharper bound on the perturbations. We next introduce the nearest-neighbor LTs and LAs that we investigate, and state our main results. Our methods initially apply to any specific dimension, but we also derive bounds that are monotone in the dimension and can be applied to all \(d\ge 30\) at once. Thus, we can check the necessary dimensions up to \(d=29\) one by one, and then analyse \(d\ge 30\) in one go.
1.2 The Model
A nearest-neighbor lattice tree on \({\mathbb {Z}}^d\) is a finite connected set of nearest-neighbor bonds that contains no closed loops (or cycles). A nearest-neighbor lattice animal on \({\mathbb {Z}}^d\) is a finite connected set of nearest-neighbor bonds, which may or may not contain closed loops. Although a tree T and an animal A are defined as a set of bonds, for \(x\in {\mathbb {Z}}^d\), we write \(x\in T\) and \(x\in A\), respectively, to denote that x is an element of a bond of T and A, respectively. The number of bonds in T and A are denoted by |T| and |A|, respectively. We define \(t^{\scriptscriptstyle (a)}_n(x)\) and \(t^{\scriptscriptstyle (t)}_n(x)\) to be the number of LAs and LTs, respectively, that consist of exactly n bonds and contain the origin and \(x\in {\mathbb {Z}}^d\). We study LAs and LTs using the one-point function \(g_z\) and the two-point function \({\bar{G}}_z\), that are defined by
where we sum over animals A and trees T respectively, and we choose z such that the above sums make sense. In what follows, we drop the superscripts (a) and (t) when we speak about both models simultaneously, but sums over A and T, respectively, always refer to sums over LAs and LTs, respectively. Only when we discuss specific statements for LAs or LTs separately, the superscripts will be shown. We define the susceptibility of LAs and LTs by
and similarly for LTs where the sum is over T instead, and denote the radii of convergence of these sums by \(z_c=z_c(d)\). As for SAW, \(1/z_c\) describes the exponential growth of the number of LTs/LAs as n grows.
We use the notation \({\bar{G}}_z\) for the two-point function, and use a normalized two-point function \(G_z(x)={\bar{G}}_z(x)/g_z\) for our analysis. We give the reason for this in Sect. 3.2. Intuitively, this is due to the fact that it is convenient to have that \(G_z(0)=1,\) which is true for the normal two-point functions of SAW and percolation, but not for those of LTs and LAs. Since \({\bar{G}}_z(0)=g_z\) by definition, we thus prefer to work with \(G_z(x)={\bar{G}}_z(x)/g_z\) instead. Dealing properly with such one-point functions is a major ingredient of our proof.
Fourier Transforms. Our analysis makes heavy use of Fourier analysis. Unless specified otherwise, k always denotes an arbitrary element from the Fourier dual of the discrete lattice, which is the torus \((-\pi ,\pi ]^d\). The Fourier transform of a function \(f:\mathbb {Z}^d\rightarrow {\mathbb {C}}\) is defined by
For two summable functions \(f,g:{\mathbb {Z}}^d\rightarrow \mathbb {R}\), we let \(f\star g\) denote their convolution, i.e.,
We note that the Fourier transform of \(f\star g\) is given by the product of \({{\hat{f}}}\) and \({{\hat{g}}}\). In particular, let \(D(x)=\mathbbm {1}_{\{|x|=1\}}/(2d)\) be the nearest-neighbor random walk transition probability, so that
Critical Exponents. It is believed that the asymptotic behavior of lattice trees and lattice animals can be described by a small number of critical exponents. These critical exponents describe the growth of \(t_n\) as \(n\rightarrow \infty \) and \({\bar{G}}_z\) as z approaches its radius of convergence \(z_c\). Further, they describe the typical length-scale of a lattice tree/animal, as characterized by the average radius of gyration \(R_n\) and the correlation length of order two \(\xi _2\), that are defined by
and
where \(|x|=(\sum _{i=1}^d x_i^2)^{1/2}\) denotes the Euclidean norm of \(x\in {\mathbb {Z}}^d\) and the sum over A in (1.8) is replaced by one over T for LTs.
It is believed that there exist critical exponents \(\gamma ,\eta ,\nu \) such that
as \(|x|\rightarrow \infty \) and \(k\rightarrow 0\). These exponents are believed to be universal, in the sense that they do not depend on the detailed structure of the lattice. In particular, it is believed that the values of \(\gamma ,\eta \) and \(\nu \) are the same in the nearest-neighbor setting that we consider here, and in the spread-out setting. The symbol \(\sim \) in (1.9)–(1.10) can have several meanings, and we shall always mean that the critical exponent exists in the bounded-ratio sense, meaning that there exist \(0<c_1<c_2<\infty \) such that, uniformly for \(z\in (0,z_c)\),
For (1.10), the uniformity is with respect to x and k, respectively, instead.
As for SAWs, it is believed that the critical exponents \(\gamma , \nu , \eta \) are related by the Fisher relation \(\gamma =(2-\eta )\nu \) and it has been proven in [4] that \(\gamma \ge 1/2\) in all dimensions. Further, it is believed that there exists an upper critical dimension \(d_c\) such that the critical exponents of LT/LA in \(d>d_c\) take their mean-field values, which are \(\gamma =1/2, \nu =1/4, \eta =0\). These values correspond to the mean-field model of LTs and LAs, studied in [3]. It is conjectured in [32] that the upper critical dimensions of LTs and LAs are \(d_c=8\). In [29], site LAs and LTs are simulated and the conjectured values of the critical exponents are consistent with these simulations (see [29] or [30] for the precise definition of site LAs and LTs). These computations are only done for site LTs, but as the critical exponents are expected to be universal, the values should be the same as for the bond trees/animals discussed here. This conjecture is supported by rigorous work in [22], where it is shown that if the “square diagram” is finite at the critical point, as is believed for \(d>8\), then the critical exponent \(\gamma \) is at most 1/2. Hara and Slade [18] proved that mean-field behavior holds for LTs and LAs in the spread-out setting with L sufficiently large and \(d>8\), or for nearest-neighbor LTs and LAs in sufficiently high dimensions.
The main aim of this paper is to put an exact value to what ‘sufficiently large’ means
The authors have learnt through private communication with Takashi Hara that Hara and Slade expected the classical lace expansion to only be successful in dimensions much larger than \(d_c=8\), however, we do not know of a precise numerical value above which their arguments work. The difficulty of the problem for lattice trees and animals can be appreciated by noting that mean-field behavior is tied to the finiteness of the square diagram, and already the SRW square diagram is quite large even for dimension \(d=50\), as it takes the value 1.1118..., while we would need that it is almost one. Indeed, the maximal open square \(\sup _{x\in \mathbb {Z}^d\setminus \{0\}} (\bar{G}_{z}\star \bar{G}_{z}\star \bar{G}_{z}\star \bar{G}_{z})(x)\) is a good indication of the error in the lace-expansion approximation. Since \(\bar{G}_{z}\) is approximately \({\mathrm {e}}\) times the SRW two-point function, the corresponding bound in dimension \(d=50\) is roughly \({\mathrm {e}}^4\times 0.1118\approx 2.2456\), which is far from small. This is explained in more detail in Sect. 4.1, where we explain the key steps to obtain a small perturbation.
1.3 Results
The main result of this paper is the following infrared bound:
Theorem 1.1
(Infrared bound) For nearest-neighbor lattice trees and lattice animals in dimensions \(d\ge 16\) and \(d\ge 17\), respectively, there exist constants \(\bar{A}_1(d)\) and \(\bar{A}_2(d)\) such that
uniformly for \(z\le z_c(d)\).
Note that Theorem 1.1 implies that \(\eta \ge 0\) in the Fourier-space asymptotics in (1.10), as \([1-{\hat{D}}(k)]\approx |k|^2\) for small k. We prove Theorem 1.1 first for \({\hat{G}}_z(k)\) as this is the central quantity in the NoBLE analysis. The analysis used for the proof for \({\hat{G}}_z(k)\) creates bounds on the amplitudes \(A_1(d)\) and \(A_2(d)\) replacing \(\bar{A}_1(d)\) and \(\bar{A}_2(d)\). Since \(\bar{G}_z(x)=g_z G_z(x)\), these bounds, together with an upper bound on \(g_z\), imply upper bounds on \(\hat{\bar{G}}_z(x),\) \(\bar{A}_1(d)\) and \(\bar{A}_2(d)\).
Our methods require a detailed analysis of both the critical value as well as the amplitudes \(A_1(d)\) and \(A_2(d)\). As a result, we obtain the following numerical bounds:
Theorem 1.2
(Bounds on the critical value and amplitude) For nearest-neighbor lattice trees, the bounds in Table 1 hold. For nearest-neighbor lattice animals, the bounds in Table 2 hold.
These upper bounds are a by-product of our analysis and we explain in Sect. 2.5 how they are computed using the Mathematica notebooks available at [9] and as supplementary material to this paper on the publisher’s website. We are able to improve the numerical bounds in Theorem 1.2, with reasonable efforts, but yielding an insignificant improvement. These efforts, however, would not reduce the minimal dimensions above which our results apply. It would, probably, be possible to improve these optimal dimensions slightly, but the effort required for this would be enormous. In particular, we do not expect that our results can be improved to all \(d>d_c=8\) without using substantially new ingredients and insights that are way beyond our proof.
Let \(\square (z)=(\bar{G}_{z}\star \bar{G}_{z}\star \bar{G}_{z}\star \bar{G}_{z})(0)\) denote the square diagram. We say that the square condition holds when \(\square (z_c)<\infty \). Since
the infrared bound in Theorem 1.1 (which is uniform in \(z<z_c\)) immediately implies that the square condition holds, and by [22] thus also that \(\gamma =1/2\) and \(\nu =1/4\):
Corollary 1.3
(Square condition and critical exponents) For nearest-neighbor lattice trees and lattice animals in dimensions \(d\ge 16\) and \(d\ge 17\), respectively, the square condition holds, i.e., \(\square (z_c)<\infty \). As a result, the susceptibility and radius of gyration critical exponents \(\gamma \) and \(\nu \) exist in the bounded-ratio sense and take on the mean-field values \(\gamma =1/2\) and \(\nu =1/4\).
We next move to some further extensions of our results, starting with sharp asymptotics of the Fourier transform of the critical two-point function \(\hat{\bar{G}}_{z_c}(k)\) for k small, which implies that \(\eta =0\) in the Fourier-space asymptotics in (1.10):
Theorem 1.4
(Two-point function k-space asymptotics) For nearest-neighbor LTs and LAs in dimensions \(d\ge 16\) and \(d\ge 17\), respectively, there exists a constant \(\bar{A}(d)\) such that, as \(|k|\rightarrow 0\),
We next investigate the asymptotics in x-space of \(\bar{G}_{z_c}(x)\) for x large, using the results of Hara in [15]. This result also implies that \(\eta =0\) in the x-space asymptotics in (1.10):
Theorem 1.5
(Two-point function x-space asymptotics) For nearest-neighbor LTs and LAs in dimensions \(d\ge 27\), and with the constant \(\bar{A}(d)\) as in Theorem 1.4, as \(|x|\rightarrow \infty \),
The restriction \(d\ge 27\) originates as a condition in [15], where it is used to start a recursion in [15, Proof of (1.47), assuming Lemmas 1.8 and 1.9]. It is unclear to us whether this restriction can be avoided. We can, however, prove the convergence of the classical lace expansions for \(d\ge 16\) for LTs and \(d\ge 17\) for LAs. Whether this is enough to obtain the x-space asymptotics in Theorem 1.5 is an open problem. To resolve this, one would need an alternative method to start the recursion to prove [15, (1.47)]. We elaborate on this somewhat counterintuitive issue in Sect. 7.3.
In Sect. 2, we give an overview of the proof of Theorem 1.1. We next discuss relations to the literature.
1.4 Relations to the Literature and Discussion
Critical Exponents. For spread-out lattice trees and animals, as well as for nearest-neighbor lattice trees in sufficiently high (unspecified) dimensions, the statements that \(\gamma =1/2\) and \(\nu =1/4\) have been improved to fixed n, as in [20, Theorem 1.1]. This means that there exist constants \(A_\gamma , A_\nu \) such that
Here, the critical exponent \(\gamma -1\) is sometimes called \(\theta \). Such results are proved by using Tauberian Theorems on \(\chi (z)=\sum _{n\ge 0} \sum _{x\in {\mathbb {Z}}^d} t_n(x)z^n\) and \(\sum _{n\ge 0}\sum _{x\in {\mathbb {Z}}^d} |x|^2 t_n(x) z^n\), where \(z\in {\mathbb {C}}\) with \(|z|<z_c\). This requires careful Taylor expansions of these generating functions, with explicit control over the error terms. Possibly our results could be extended in this direction as well, but this would require a more detailed and extensive study of the analytic properties of \(\chi (z)\) and \({\hat{G}}_z(k)\), which we refrain from.
Other interesting critical exponents exist. For example, the correlation length \(\xi (z)\) is defined as
It is predicted that \(\xi (z)\) scales similarly as \(\xi _2(z)\), so that, in particular,
corresponding to \(\nu =1/4\) also for this correlation length.
Relations to Super-Processes. There has been a considerable effort to identify super-process limits of lattice trees and lattice animals, with a focus on lattice trees. Derbez and Slade [7, 8] show that the scaling limits of lattice trees of a fixed size scale to a finite measure called integrated super-Brownian excursion (ISE). For such a scaling limit, a lattice tree of size n is seen as a random counting measure \(X_n\), where \(X_n(E)\) is the number of vertices of a random lattice tree that are in \(E\subseteq \mathbb {R}^d\). When rescaling space by \(n^{1/4}\) (which is related to \(\nu =1/4\) in Corollary 1.3), and rescaling mass by 1/n (so that the total mass becomes 1), this random measure converges to ISE. Holmes and collaborators, instead, consider the super-Brownian motion limits of lattice trees, proving convergence in finite-dimensional distributions [23, 27] (see also [28]) and tightness [24], in the context of spread-out lattice trees above 8 dimensions. The key advantage to working with spread-out models is that the square diagram can be made small in any dimension \(d>8\) by making the models more spread-out. Extensions of such results to nearest-neighbor lattice trees, as well as to lattice animals, where the small parameter is essentially the inverse dimension, are of great interest.
Convergent Classical Lace Expansion. In the above extensions, or in other ones not discussed here, it may be very useful that the classical lace expansion for LTs and LAs as derived by Hara and Slade in [18] is convergent, as a result of our methods, as explained in detail and in the context of the proof of Theorem 1.5 in Sect. 7.3. Thus, it is not necessary to adapt such proofs to the NoBLE setting.
Asymptotics of \(z_c\) and \(g_{z_c}\). The asymptotic values of \(z_c\) and \(g_{z_c}={\bar{G}}_{z_c}(0)\) when d is large are shown in [35] to be given by
where the factor \(\mathbbm {1}^{a}\) is 1 for LAs and 0 for LTs. The rigorous bounds on the error terms were derived using the lace expansion. These asymptotic expansions have also been studied extensively in the physics literature, where results were obtained up to the order of \(1/(2d)^6\), but with non-rigorous estimates on the error term. We refer the reader to [35] for an overview of such results and a discussion of the 1/d expansions of the critical value \(z_c\) of SAW, percolation, LT, and LA.
2 Overview of the Proof
In this section, we give a brief overview of how we derive our main results. This overview is similar in spirit to that in [13, Sect. 2], where nearest-neighbor percolation was investigated. We repeat part of this discussion, as it provides the key ideas in our proof.
2.1 Philosophy of the Proof
We reduce the proof of Theorem 1.1 to three key ingredients that we call cornerstones, and a computer-assisted proof. These ingredients involve
-
(a)
the derivation of the non-backtracking lace expansion (NoBLE) in Cornerstone 2.1;
-
(b)
the diagrammatic bounds on the NoBLE coefficients in Cornerstone 2.2;
-
(c)
the analysis presented in [12] to obtain the infrared bound in Theorem 1.1 for all \(z\le z_c\), as stated in Cornerstone 2.3; and
-
(d)
a computer-assisted proof to verify the numerical conditions arising in the analysis in [12].
The philosophy behind the proof of these parts is discussed in Sects. 2.2, 2.3 and 2.5, respectively. In Sects. 3 and 5 we prove parts (a) and (b), respectively. In Sect. 2.4, we explain how we obtain part (c) using the analysis of [12]. The computer-assisted proof of part (d) is performed in [9] using the results of this paper. For the analysis in the generalized setting [12] we state assumptions, which we verify in Sect. 3.4 and in Sect. 5.3. Part (d) is explained in detail in Sect. 2.5, where we describe how the necessary computations are performed in several Mathematica notebooks. The mathematics behind the notebooks is explained in [12].
Let us now explain how our main results are proved. The notebooks contain a routine that verifies whether the numerical assumption on the expansions are satisfied and thereby whether the analysis of [12] yields the infrared bounds for a given dimension. The results in [12], combined with a successful verification using the notebooks, thus prove Cornerstone 2.3, which in turn implies Theorem 1.1. See also Fig. 1 for a visual description of the proof of Theorem 1.1.
Theorem 1.2 will follow from the numerical bounds derived in the proof. The proofs of Corollary 1.3, Theorems 1.4 and 1.5 are completed in Sect. 7.3, using the results of Hara [15]. We further rely on an improvement of the analysis there by Hara that we learned about in private communication [16], which yields an improved numerical condition for the convergence of the classical-lace expansion coefficients, allowing us to conclude the x-space asymptotics in Theorem 1.5 for \(d\ge 27\). We close this section with a discussion of our method and results.
In the following, we explain the philosophy behind the non-backtracking lace expansion (NoBLE), and we start by describing simple random walk and non-backtracking walk:
Simple Random Walk. An n-step nearest-neighbor simple random walk (SRW) on \({\mathbb {Z}}^d\) is an ordered \((n+1)\)-tuple \(\omega =(\omega _0,\omega _1,\omega _2,\ldots , \omega _n)\), with \(\omega _i\in {\mathbb {Z}}^d\) and \(|\omega _i-\omega _{i+1}|_1=1\), where \(|x|_1=\sum _{i=1}^d |x_i|\). Unless stated otherwise, we take \(\omega _0=(0,0,\ldots ,0)\) to be the origin in \({\mathbb {Z}}^d\). Then, for \(n\ge 1\),
with D being defined before (1.6) and \(f^{\star n}\) denoting the n-fold convolution of a function f. The SRW two-point function is defined by
for \(|z|<1/(2d)\), in x-space and k-space, respectively. The SRW susceptibility is given by

for \(|z|<z_c\), with critical point \(z_c=1/(2d)\).
Notations. Before introducing non-backtracking random walk, we introduce some notation that will be used throughout this paper. We exclusively use the Greek letters \(\iota \) and \(\kappa \) for values in \(\{-d,-d+1,\ldots ,-1,1,2,\ldots ,d\}\) and denote the unit vector in direction \(\iota \) by \({e}_{\iota }\in {\mathbb {Z}}^d\), e.g. \(({e}_{\iota })_i=\text {sign}(\iota ) \delta _{|\iota |,i}\). We use \({{\mathbb {C}}}^{2d}\)-valued and \({{\mathbb {C}}}^{2d}\times {{\mathbb {C}}}^{2d}\)-valued quantities. For a clear distinction between scalar-, vector- and matrix-valued quantities, we always write \({{\mathbb {C}}}^{2d}\)-valued functions with a vector arrow (e.g. \( \mathbf {v}\)) and matrix-valued functions with bold capital letters (e.g. \(\mathbf{M}\)). We do not use \(\{1,2,\ldots ,2d\}\) as the index set for the elements of a vector or a matrix, but use \(\{-d,-d+1,\ldots ,-1,1,2,\ldots ,d\}\) instead. We denote the identity matrix by \(\mathbf{I}\in {{\mathbb {C}}}^{2d\times 2d}\) and the all-one vector by \( {\mathbf {1}} =(1,1,\ldots ,1)^T\in {{\mathbb {C}}}^{2d}\). Moreover, we define the matrices \(\mathbf{J},{{\hat{\mathbf{D}}}}(k)\in {{\mathbb {C}}}^{2d\times 2d}\) by
where \(k\in [-\pi ,\pi ]^d\) and for negative index \(\iota \in \{-d,-d+1,\ldots ,-1\}\), we write \(k_\iota =-k_{|\iota |}\). Now we can introduce non-backtracking random walk and its Green’s function.
Non-backtracking Walk. If an n-step SRW \(\omega \) satisfies \(\omega _i\not =\omega _{i+2}\) for all \(i=0,1,2,\ldots ,n-2\), then we call \(\omega \) a non-backtracking walk (NBW). The NBW two-point function \(B_z\) is defined, for \(|z|<1/(2d-1)\), by
As derived in [12, Sect. 1.2.2], this two-point function satisfies
The critical NBW and SRW two-point functions are thus related by
This link allows us to compute values for the NBW two-point function in x- and k-space, using the SRW two-point function. A detailed analysis of the NBW including a proof that the NBW, when properly rescaled, converges to Brownian motion can be found in [11].
2.2 Part (a): Non-backtracking Lace Expansion (NoBLE)
In this section, we explain the shape of the Non-Backtracking Lace Expansion (NoBLE), which is a perturbative expansion of the two-point function. For this, we state an equation like (2.5) for the two-point function \(G_z(x)\). This expansion is derived in Sect. 3.1.
Next to the usual two-point function \(G_z\), see (1.2), we use a slight adaptation \(G_z^\iota \), with \(\iota \in \{\pm 1,\pm 2,\ldots , \pm d\}\) being a distinct direction. We postpone the definition of \(G_z^\iota \) to Sect. 3.1, see (3.4). Intuitively, \(G_z^\iota \) considers only LTs and LAs that do not contain \(e_\iota \), but for technical reasons, the precise definition is somewhat more involved. Our analysis relies on two expansion identities relating \(G_z(x)\) and \(G_z^\iota (x)\) that are highlighted in the following cornerstone:
Cornerstone 2.1
(Non-backtracking lace expansion) For every \(x\in \mathbb {Z}^d\), \(\iota ,\kappa \in \{\pm 1,\pm 2, \ldots , \pm d\}\), the following recursion relations hold:
where
Explicit formulas for the above lace-expansion coefficients are given in Sect. 3.2.
Equations (2.7) and (2.8) are similar in spirit to the equations satisfied by the NBW two-point function, where \(G_z(x)\) is replaced by \(B_z(x)\) and \(G^\iota _z(x)\) by \(B^\iota _z(x)\), which is the Green’s function of all NBWs for which the first step is unequal to \(e_{\iota }\) (recall [12]). For this, the similar equation to (2.7) is obtained by conditioning on the first step, while (2.8) is obtained by splitting depending on whether the first step equals \(e_{\iota }\) or not. Equations (2.7) and (2.8) reduce to the equations for NBW when we set \(\Psi ^{\kappa }_z=\Xi _{z}=\Pi _{z}^{\iota ,\kappa }\equiv 0\), and replace \(\mu _z\) by \((2d-1)z\) and \({\bar{\mu }}_z\) by 2dz. [Even though \({\bar{\mu }}_z= zg_z\) does not appear in (2.7) and (2.8), it is a crucial ingredient in much of our proof, which explains why we define it here.] Thus, we can think of (2.7) and (2.8) as a perturbations around NBW, and of \(\Psi ^{\kappa }_z=\Xi _{z}=\Pi _{z}^{\iota ,\kappa }\) as the perturbation coefficients, of which we hope to prove that they are ‘small’ in an appropriate sense.
Of course, the precise formulas for the lace-expansion coefficients are crucial for our analysis to succeed. However, at this stage, we refrain from stating their forms explicitly, and refer to Sect. 3.2 instead where they are derived while performing the NoBLE. As such, Cornerstone 2.1 cannot be seen as a formal result at this point, since, for example, the convergence of the sums arising in it cannot yet be guaranteed.
Applying the Fourier transforms to (2.7) and (2.8) and some simple rearrangements, see [12, Sect.1.3], we derive that
with
Equation (2.12) is the NoBLE equation, and is the workhorse behind our proof. The goal of the NoBLE is now to show that (2.12) is indeed a perturbation of (2.5). This amounts to proving that \(\hat{\Xi }_{z}(k)\),\(\mathbf {\hat{\Xi }}(k)\), \(\mathbf {\hat{\Psi }}_z(k)\) and \(\hat{\varvec{\Pi }}(k)\) are small, which will only be true in sufficiently high dimensions.
We continue by discussing how to bound the NoBLE coefficients.
2.3 Part (b): Bounds on the NoBLE
The content of the second key step in the NoBLE analysis is that the NoBLE coefficients can be bounded by combinations of simple diagrams. Simple diagrams are combinations of two-point functions, like the following examples:
The important property that our proof crucially relies on is stated in the following cornerstone:
Cornerstone 2.2
(Diagrammatic bound on the NoBLE coefficients) For each \(N\ge 0\), the NoBLE coefficients \( \Pi ^{{\scriptscriptstyle ( \text { N})},\iota ,\kappa }(y),\) \(\Xi ^{{\scriptscriptstyle ( \text { N})}}(x),\) \(\Psi ^{{\scriptscriptstyle ( \text { N})},\kappa }(y)\) and \(\Xi ^{{\scriptscriptstyle ( \text { N})},\iota }(x)\) can be bounded by a finite combination of sums and products of simple diagrams.
The explicit form of the bounds in Cornerstone 2.2 is given in Lemmas 5.1–5.5 below. In Sect. 5.3 we summarize the bounds as required for the analysis in [12]. As the complete proof of the bounds on the NoBLE coefficients is highly elaborate, we only sketch the proof. Since Cornerstone 2.2 is not explicit in what simple diagrams bound the NoBLE lace-expansion coefficients, it only becomes a formal result after these bounds are obtained below. In this paper, we only informally define the diagrams that we use to bound the coefficients. A complete definition and additional details can be found in the extended version [14].
Matrix-Valued Bounds. The lace-expansion coefficients arising in the NoBLE describe contributions created by multiple mutually intersecting paths, in the LTs and LAs. We will informally call such path-intersections loops, and this notion will be made precise below. In the NoBLE, these loops require at least 4 bonds by design, as direct reversals are excluded by the way that we set up the NoBLE expansion. These lace-expansion coefficients can be bounded in terms of certain Feynman diagrams, of which the lines correspond to various two-point functions, and these lines are required to have various intersections. We will refer to the two-point functions arising in these bounds informally as ‘lines’.
The diagrams turn out to have the general property that lines can be part of at most two loops. To optimally use the information that loops contain at least 4 bonds, we distinguish five cases for the length and function of paths used by two loops. Then, we bound the contribution of each loop of the lace-expansion diagram one-by-one, using the information on the lines shared with the previous and next loop. We explain this in detail in Sect. 4. This procedure naturally gives rise to a bound on the NoBLE coefficients in terms of matrix products, as formalized in Lemma 5.4. For example, our proof yields that
for \(N\ge 3\), see (5.36), for certain vectors \(\mathbf {P}, \, \mathbf {E}^\mathrm{{open}}\) and 5 by 5 matrices \(\mathbf{A}\). We will give an interpretation of the elements in these vectors and matrices in Sect. 5.1. For our analysis, we require a bound on this when summed over N. To compute this bound numerically, we perform an eigenvector decomposition of \(\mathbf {P}\), in terms of the eigenvectors \((\mathbf \mathrm{v}_i)_{i=1}^5\) of \(\mathbf{A}\) with corresponding eigenvalues \((\lambda _i)_{i=1}^5\). In this decomposition, we write \(\mathbf {P}=\sum _{i=1}^5 \mathbf \mathrm{v}_i,\) so that the eigenvectors used are not normalizedFootnote 1. Then,
The sum of this over N is computed using the geometric sum, see [12, Sect. 5.4] for more details.
The order of this bound is to a large extent given by the largest eigenvalue of \(\mathbf{A}\). For example, for LTs in \(d=16\),
with largest eigenvalue \(\lambda _1=0.103089\). In the classical lace expansion, the corresponding Nth lace-expansion diagram bound also decays exponentially in N, where the base of the exponent is a non-trivial square. We can bound the non-trivial square, as it arises in the classical lace expansion, by 2.53461. Revisiting the classical lace expansion and then using all our improvements, which we explain in Sect. 4.1, we can improve the base of the exponent to a value of 0.130586.
Using our matrix-valued bounds, we can reduce the base of the exponent by a further \(30\%\). The gain in various explicit contributions is usually even larger.
2.4 Part (c): The NoBLE Analysis
At the center of our analysis are the so-called bootstrap functions, which we next discuss.
Bootstrap Functions. For the bootstrap, we define the following functions:
where \(c_\mu >1\) and \(c_{n,l,S}>0\) are some well-chosen constants and \({\mathcal {S}}\) is some finite set of indices. Let us now discuss the choice of these functions, and explain their use.
The functions \(f_1\) and \(f_3\) can be seen as combinations of multiple functions. We group these functions together as they play a similar role and are analyzed in the same way. We do not expect that the values of the bounds on the individual functions that constitute \(f_1\) and \(f_3\) are comparable. This is the reason that we introduce the constants \(c_\mu \) and \(c_{n,l,S}\).
The choice of point-sets \(S\in {\mathcal {S}}\) improves the numerical accuracy of our method considerably. For example, we obtain much better estimates for \(x=0\) (leading to a closed diagram), than for \(x\ne 0\). For x being a neighbor of the origin, we can further use symmetry to improve our bounds significantly. To obtain the infrared bound as stated in Theorem 1.1, we use the following set \({\mathcal {S}}\):
with \({\mathcal {X}}=\{x\in {\mathbb {Z}}^d:|x|>1\}\). This turns out to be sufficient for our main results.
We apply a forbidden region or bootstrap argument that is based on three claims:
-
(i)
\(z\mapsto f_i(z)\) is continuous for all \(z\in [z_{I}, z_c)\) and \(i=1,2,3\) and for some \(z_{I}\in (0,z_c)\);
-
(ii)
\(f_i(z_{I})\le \gamma _i\) holds for \(i=1,2,3\); and
-
(iii)
if \(f_i(z)\le \Gamma _i\) holds for \(i=1,2,3\), then, in fact, also \(f_i(z)\le \gamma _i\) holds for every \(i=1,2,3\), where \(\gamma _i<\Gamma _i\) for every \(i=1,2,3\).
Together, these three claims imply that \(f_i(z_{I})\le \gamma _i\) holds for every \(i=1,2,3\) and all \(z\in [z_{I}, z_c)\). This in turn implies the statement of Theorem 1.1 for all \(z\in [z_{I}, z_c)\).
The continuity in Claim (i) is proven in [12] under some assumption that we explain and prove below. The proofs of the initialization of the bootstrap in Claim (ii) as well as the improvement of the bounds in Claim (iii) use the following relations that are also sketched in Figs. 2 and 3:
-
(1)
simple diagrams can be bounded by a combination of two-point functions, see [12, Sect. 4];
-
(2)
the NoBLE coefficients can be bounded by a combination of simple diagrams, that, in turn, can be bounded using the bounds on the two-point functions that we obtain from the bootstrap assumption, see Sect. 5.2;
-
(3)
bounds on the NoBLE coefficients imply bounds on the two-point function, see [12, Sect. 2], which allows us to improve upon the bounds that we assumed.
Thus, whenever we have numerical bounds on simple diagrams, or on NoBLE coefficients, or on the two-point function, we can also conclude bounds on the other two quantities.
We choose \(z_{I}\) such that \(G_{z_I}(x)\le B_{1/(2d-1)}(x)\) holds pointwise in x. Then, using this and the fact that we can compute \(B_{1/(2d-1)}(x)\) numerically, we verify the initialization of the bootstrap in Claim (ii) (i.e., \(f_i(z_I)\le \gamma _i\) for \(i=1,2,3\)) numerically, see Fig. 2.
The proof of Claim (iii) is the most elaborate step of our analysis. Its structure is shown in Fig. 3. We start from the assumption that \(f_i(z)\le \Gamma _i\) holds for every \(i=1,2,3\). The function \(f_1\) gives a bound on \(zg_z\) and \(zg_z^\iota \). The function \(f_2\) allows us to bound the two-point function in Fourier space by \({{\hat{B}}}_{1/(2d-1)}(k)\), which we can integrate numerically to obtain numerical bounds on simple diagrams. Further, \(f_2\) allows us to conclude the infra-red bound in Theorem 1.1. These, in turn, imply bounds on the NoBLE coefficients, which we use to improve our bounds on the bootstrap functions.
In the case that the computed bounds are small enough, we can conclude that \(f_i(z)\le \gamma _i\) holds for \(i=1,2,3\), and thereby that the improvement of the bounds in Claim (iii) holds. Whether we can indeed prove that Claim (iii) holds depends on the dimension we are in, the quality of the bounds and the analysis used to conclude bounds for the bootstrap function. In high-enough dimensions (e.g. \(d\ge 1000\)) the perturbation is rather small so that it is relatively easy to prove Claim (iii). Proving the claim in lower dimensions is only possible when the bounds on the lace-expansion coefficients and the analysis are sufficiently sharp and hence sophisticated. It is here that it pays off to apply the NoBLE compared to the classical lace expansion. The third key step in the proof of Theorem 1.1 is highlighted in the following cornerstone:
Cornerstone 2.3
(Successful application of NoBLE analysis) For nearest-neighbor LTs and LAs, in \(d\ge 16\) and \(d\ge 17\), the NoBLE analysis of [12] applies and proves the infrared bound in Theorem 1.1. In particular, there exist constants \(\Gamma _1,\Gamma _2,\Gamma _3\) and \(\gamma _1,\gamma _2,\gamma _3\) such that \(f_i(z_I)\le \gamma _i\) for \(i=1,2,3\) and, for every \(z\in [z_I,z_c)\), the bounds \(f_i(z)\le \Gamma _i\) for \(i=1,2,3\) imply that \(f_i(z)\le \gamma _i\) for \(i=1,2,3\).Footnote 2
As shown in Fig. 3, Cornerstone 2.3 is proved using the results of Cornerstones 2.1–2.2, the analysis of [12] and the computer-assisted proof performed in the Mathematica notebook that can be found on [9] as well as on the publisher’s website for supplementary material. To apply the general NoBLE analysis of [12], we need to prove that the assumptions formulated in [12] hold. All but one of these assumptions are proven in Sect. 3.4. The one remaining assumption, involving the bounds on the NoBLE coefficients, is addressed in Sect. 5.
2.5 Part (d): Numerical Analysis
In this section, we explain how the numerical computations are performed using Mathematica notebooks that are available from the first author’s homepage [9] as well as on the publisher’s website for supplementary material.
Simple-Random-Walk Computations. The procedure starts by evaluating the notebook SRW. The file computes the value of the SRW, and thereby the NBW, two-point function for various locations in \({\mathbb {Z}}^d\). This computation uses pre-computed values of the number of SRWs paths and SRW integrals based on numerical integration of certain Bessel functions. These computations rely on ideas from [21, Appendix B], and are explained in detail in [12, Sect. 5]. The SRW integrals provide rigorous numerical upper bounds on various convolutions of SRW Green’s functions with themselves, evaluated at various \(x\in \mathbb {Z}^d\). We rely on 140 of such integrals.
Running these programs takes several hours. For this reason, once computed, the results are saved in two files, SRWCountData.nb and SRWIntegralsData.nb and are loaded automatically when the notebook is evaluated a second time for the same dimension. Alternatively, these two files can also be downloaded directly, and put in one’s own home directory.Footnote 3
Implementation of the NoBLE Analysis for LT and LA. After having computed all the simple-random-walk ingredients, we evaluate the notebook General, that implements the bounds of the NoBLE analysis [12]. After this, we are ready to perform the NoBLE analysis for LTs and LAs, respectively, by evaluating the notebook LA and LT, respectively. In these notebooks, we implement all the bounds proven in this paper. The computations in General, LA and LT merely implement the bounds proven in this paper and in [12], and rely on many multiplications and additions, as well as the diagonalization of two 5-by-5 matrices. These computations could in principle be done by hand (even though we prefer a computer to do them).
Output of Mathematica Notebooks. After having evaluated the Mathematica notebooks, we can verify whether the analysis has worked with the chosen constants \(\Gamma _1,\Gamma _2, \Gamma _3\). Figure 5 shows the key output of the LA notebook. Let us explain this output in more detail. The green dots mean that the bootstrap has been successful for the parameters as chosen. When evaluating the notebook, it is possible that some red dots appear, and this means that these improvements were not successful. The first 3 dots in the first table are the verifications that \(f_i(z_I)\le \gamma _i\) for \(i=1,2,3\). The next three dots show that the improvement has been successful for any \(z\in (z_I,z_c)\). The values for \(\Gamma _1, \Gamma _2,\Gamma _3\) are indicated in the second row. For example, \(\Gamma _1=1.10225007\) means that we have assumed that \(f_1(z)=(2d-1)zg_z\le 1.10225007\). Using this assumption we have concluded that \(f_1(z)\le 1.102250067\) from the improvement step (which relies on the NoBLE analysis), so that we can choose \(\gamma _1=1.02250069\) for our analysis in Cornerstone 2.3. Since this is true for all \(z\in (z_I,z_c)\), we obtain that \((2d-1)z_cg_{z_c}\le 1.0225007\). This explains the value in the table of Theorem 1.2. The stated upper bound on \(g_{z_c}\) follows from \(g_{z_c}\le {\mathrm {e}}\Gamma _1\), which we obtain by combining \(f_1(z)<\Gamma _1\) with \(z_c>(2d-1)^{-1}{\mathrm {e}}^{-1}\), which is proven in Sect. 3.4.
Similarly, \(\Gamma _2=1.335307\) implies that
which, in turn, implies that
Using these computations, we have computed the bounds stated in Theorem 1.2. Anyone interested in obtaining improved bounds on \(g_{z_c}\), \(g_{z_c}z_c\) or \(A_2\) for other values of d can play with the notebooks to optimize them. The second and third table in Fig. 4 provides details on the improvement of \(f_3(z)\), which, as indicated in (2.17) and (2.18), consists of several contributions, over which the maximum is taken. The assumed bounds correspond to the constants \(c_{n,l,S}\), with \(S\in {{\mathcal {S}}}\) in (2.18). The notebooks LT and LA also includes a routine that optimizes the choices of \(\Gamma _i\) and \(c_{n,l,S}\). This makes it possible to efficiently find values for which the analysis works (when these exist)
2.6 Structure of the NoBLE Proof and Related Results
Summary of the Proof of the Infrared Bound in Theorem 1.1. We have already seen how delicately the four parts of the proof described in Sect. 2.1 are intertwined. The expansion in part (a) provides a characterization of \({{\hat{G}}}_z(k)\) as a perturbation of \({{\hat{B}}}_{1/(2d-1)}(k)\) involving the NoBLE coefficients. The analysis in part (c) allows us to compute bounds on \({{\hat{G}}}_z(k)\), when numerical bounds on the coefficients are available. To obtain such bounds we need to derive diagrammatic bounds, as formulated in part (b), that bound the NoBLE coefficients by simple diagrams. However, we rely on bounds on \(G_z\) to bound such simple diagrams numerically. Thus, we appear to obtain a circular reasoning. We next explain how this argument can be completed, and the circle can be broken.
We use a so-called bootstrap argument to complete the argument and avoid the apparent circularity of our proof, see Figs. 2 and 3. The bootstrap argument allows us to obtain a bound on \({{\hat{G}}}_z(k)\) for all \(z\in [z_I, z_c)\). To apply the bootstrap argument, we need to show that \(f_i(z_I)\le \gamma _i\), as well as the fact that \(f_i(z)\le \Gamma _i\) implies that \(f_i(z)\le \gamma _i\), for appropriately chosen \(\gamma _i\) and \(\Gamma _i\), and for all \(z\in (z_I, z_c)\). The verification whether \(f_i(z_I)\le \gamma _i\) holds for \(i=1,2,3\), as well as whether we can conclude from \(f_i(z)\le \Gamma _i\) for \(i=1,2,3\) that also \(f_i(z)\le \gamma _i\) holds for \(i=1,2,3\), both require a computer-assisted proof as indicated in Sect. 2.5. Starting from \(G_{z_I}(x)\le B_{1/(2d-1)}(x)\), \(f_i(z)\le \Gamma _i\) for \(i=1,2,3\) and explicit computations of \(B_{1/(2d-1)}(x)\), we obtain numerical bounds on simple diagrams. These are then used to obtain numerical bounds on the NoBLE coefficients, which we in turn use to verify whether we can actually conclude from \(f_i(z)\le \Gamma _i\) for \(i=1,2,3\) that \(f_i(z)\le \gamma _i\) for \(i=1,2,3\) holds.
Combining these steps yields the required results for \(z\in [z_I, z_c)\). We obtain the statement also for \(z=z_c\) by using that \({{\hat{G}}}_z(k)/{{\hat{B}}}_{1/(2d-1)}(k)\) and the NoBLE-coefficients are continuous and uniformly bounded for \(z\in [z_I, z_c)\), as well as left-continuous in x-space at \(z_c\).
Extension to all \(d\ge 20\). Theorems 1.1 and 1.2 prove the infrared bound, as well as estimates on amplitudes and critical values, for \(d=16, \ldots , 20\) for lattice trees, and for \(d=17, \ldots , 20\) for lattice animals. The Mathematica notebooks, and the numerical estimates that these rely upon, are designed to prove our results for any specific dimension. We successfully execute them for d up to 29.
To prove that the statements hold for all higher dimensions \(d\ge 30\), without spending eternity checking the condition one dimension at time, we further modify our numerical verifications so that they only use quantities that are monotone decreasing in the dimension. It results in bounds on the NoBLE coefficients and related quantities that hold uniformly in all \(d\ge 30\), implying that the bootstrap succeeds in all these dimensions in one go. This numerical verification is performed in the Mathematica notebook LAmonotone for LA. This analysis also immediately applies to LTs, as all LT quantities are bounded by their LA analogues.
The idea behind these uniform bounds, used in the improvement of the bootstrap bounds, is the following:
-
(a)
The SRW quantities that we rely upon, such as the Green’s function at various points in \(\mathbb {Z}^d\) and contributions of short paths, are monotone decreasing in d.
-
(b)
Simple diagram are bounded using the bootstrap assumption \(f_i(z)\le \Gamma _i\) and these SRW quantities. Using the same \(\Gamma _i\) for all \(d\ge 30\), the bounds on simple diagrams are monotone decreasing in d as well.
-
(c)
Our NoBLE coefficients are bounded using simple diagrams, which implies that these bounds are also monotone decreasing in d.
-
(d)
Our bounds on the NoBLE coefficients decrease in d, so that the bounds on the coefficients appearing in the analysis of [12] are monotone decreasing as well. In the end, this guarantees that the improvement of the bootstrap bounds succeeds for all \(d\ge 30\) at once.
In Appendix B, we explain how we modify our numerical verifications, show that the SRW quantities that we rely upon are monotone decreasing in d, and discuss the additional steps needed to make the analysis work for all \(d\ge 30\).
Organization of this Paper. The remainder of this paper is organised as follows. In Sect. 3, we perform the NoBLE, and thus show that the statement in Cornerstone 2.1 is indeed true. There, we also give explicit formulas for the NoBLE coefficients. In Sect. 4, we explain how diagrammatic bounds on the NoBLE coefficients can be obtained. These diagrammatic bounds are phrased in terms of various building blocks that are informally defined in Sect. 5.1. In Sect. 6, we explain how such diagrammatic bounds are proved. In Sect. 7, we prove our main results. In Appendix A, we prove that \(z_I\ge (2d-1)^{-1}{\mathrm {e}}^{-1}\), and in Appendix B, we use monotonicity arguments to extend the results to all dimensions \(d\ge 30\).
3 The Non-backtracking Lace Expansion
3.1 Derivation of the Expansion
In this section we derive the NoBLE for LTs and LAs using an algebraic expansion. The basic idea is similar to the classical lace expansion applied to SAWs derived first in [6], and is an adaptation of the classical lace expansion for LTs and LAs derived in [20].
Let us consider a LT that contains 0, x. As a LT does not contain any loops there exists a unique path connecting 0 and x. We call this path the backbone. A LA containing 0, x can contain loops. Therefore, a connection between 0 and x is not necessarily unique. The analogue to the backbone for LAs is formed by the pivotal bonds, which are defined as follows:
Definition 3.1
(Double connections and pivotal bonds) Let A be a LA that contains \(x,y\in {\mathbb {Z}}^d\). We say that x and y are doubly connected in A if there exist two edge-disjoint paths \(p_1,p_2\subset A\) connecting x and y. By convention, we say that \(x\in A\) is doubly connected to itself. We call a bond \(b\in A\) pivotal for x and y if the removal of b would disconnect A into two disjoint animals, one containing x and the other y.
Let us consider a LA containing x and y as given in Fig. 6. Then, x and y are either doubly connected or there exists at least one pivotal bond b. If there are multiple pivotal bonds, then they have a natural order for the connection from x to y, because every self-avoiding path from x to y has to use the pivotal bonds \((b_i)_{i\ge 1}\) in the same order.
The removal of the bonds \((b_i)_{i\ge 1}\) disconnects the animal into mutually non-intersecting pieces, which we denote in Fig. 6 by \((S_i)_{i\ge 1}\). We will consider bonds to be directed, and write \(b=(x,y)\) for the bond directed from x to y. For a directed bond \(b=(x,y)\), we write \(\bar{b}=y\) and \({\underline{b}}=x\) for the two ends of the bond. The pieces \((S_i)_{i\ge 1}\) form double connections between the end of one pivotal bond \({\bar{b}}_i\) to the beginning of the following pivotal bond \({\underline{b}}_{i+1}\). We call these doubly connected pieces \((S_i)_{i\ge 1}\) sausages, and the sequence of pivotal bonds \((b_i)_{i\ge 1}\) the backbone of the animal. For LTs double connections are not possible, so that \(\bar{b}_i=\underline{b}_{i+1}\).
So far, we follow the classical lace expansion as in [20]. Now we start to deviate, and we wish to do so in a way that is closer to the NBW. In order to do this, we define the rib-walk for LTs, and the sausage-walk for LAs, respectively, to characterize the combination of a backbone and a set of ribs/sausages, that are non-backtracking. Using these walks we derive the NoBLE for LTs and LAs, the steps of the classical lace expansion, by expanding a graph-based description of the avoidance constraints of the sausages and of the backbone.
Definition 3.2
(Ribs and rib-walks for LTs)
-
(i)
We call a LT S that contains \(x\in {\mathbb {Z}}^d\) a rib for x and define that the empty set is also a rib for all \(x\in {\mathbb {Z}}^d\) (recall that a LT is a collection of bonds).
-
(ii)
For \(x,y\in {\mathbb {Z}}^d\) and \(n\ge 1\), we call a collection of n oriented nearest-neighbor bonds \((b_i)_{i=1}^n\) and \(n+1\) ribs \((S_i)_{i=0}^n\) an n-step rib-walk from x to y, if \(S_0\) is a rib for \({\underline{b}}_1=x\), \(S_n\) is a rib for \({\bar{b}}_n=y\), and, for \(i=1,\ldots ,n-1\), the LT \(S_i\) is a rib for \({\bar{b}}_i={\underline{b}}_{i-1}\). We call \((b_i)_{i=1}^n\) the backbone of the rib-walk.
-
(iii)
For a rib-walk \(\omega =((b_i)_{i=1}^n, (S_i)_{i=0}^n)\), we define \(|\omega |\) to be the number of bonds in the backbone. We denote the ith bond of the backbone by \(b^{\omega }_i\) and the ith rib of \(\omega \) by \(S^{\omega }_i\).
-
(iv)
We say that any LT containing the origin is a zero-step rib-walk to the origin.
-
(v)
We call a rib-walk \(\omega \) non-backtracking if
 and \({\bar{b}}^\omega _{i+1}\ne {\underline{b}}^\omega _{i}\) for all i.
and \({\bar{b}}^\omega _{i+1}\ne {\underline{b}}^\omega _{i}\) for all i. -
(vi)
We define
 as the set of all rib-walks from the origin 0 to x and
as the set of all rib-walks from the origin 0 to x and  to be the set of all rib-walks \(\omega \) from 0 to x such that
to be the set of all rib-walks \(\omega \) from 0 to x such that  and \({\bar{b}}^\omega _1\ne {e}_{\iota }\). We write
and \({\bar{b}}^\omega _1\ne {e}_{\iota }\). We write  for the set of all sausage-walks such that
for the set of all sausage-walks such that  and \({\bar{b}}^\omega _1\ne {e}_{\iota }\) and with arbitrary start and end point.
and \({\bar{b}}^\omega _1\ne {e}_{\iota }\) and with arbitrary start and end point.
We point out that a bond could be part of multiple ribs, so that there is no bijection between rib-walks and LTs containing 0 and x. This bijection is however possible if we restrict to self-avoiding rib-walks. The non-backtracking condition is part of this necessary self-avoidance constraint. It rules a specific notion of immediate reversals out. Thus, we can think of a LT as a non-backtracking rib-walk with extra mutual avoidance constraints between the ribs.
We continue by defining similar quantities for LAs, to set the stage for an expansion that can treat LTs and LAs at the same time:
Definition 3.3
(Sausages and sausage-walks for LAs)
-
(i)
We call a LA S a sausage for \((x,y)\in {\mathbb {Z}}^d\times {\mathbb {Z}}^d\), if x and y are doubly connected in S. Further, we define that the empty set is a sausage for every (x, x) with \(x\in {\mathbb {Z}}^d\).
-
(ii)
For \(x,y\in {\mathbb {Z}}^d\) and \(n\ge 1\) we call a collection of n oriented nearest-neighbor bonds \((b_i)_{i=1}^n\) and \(n+1\) sausages \((S_i)_{i=0}^n\) an n-step sausage-walk from x to y, when \(S_0\) is a sausage for \((x,{\underline{b}}_1)\), \(S_n\) is a sausage for \(({\bar{b}}_n,y)\) and \(S_i\) is a sausage for \(({\bar{b}}_i,{\underline{b}}_{i+1})\) for \(i=1,\ldots ,n-1\).
-
(iii)
For a sausage-walk \(\omega =((b_i)_{i=1}^n, (S_i)_{i=0}^n)\) we define \(|\omega |\) to be the number of steps of \(\omega \). We denote the ith bond of the backbone by \(b^{\omega }_i\) and the ith sausage of \(\omega \) by \(S^{\omega }_i\). We call \((b_i^\omega )_{i=1}^n=(b_i)_{i=1}^n\) the backbone of the sausage-walk.
-
(iv)
For \(x\in {\mathbb {Z}}^d\) we define any sausage for (0, x) to be a zero-step sausage-walk from the origin to x.
-
(v)
We call a sausage-walk non-backtracking, if
 and \({\bar{b}}^\omega _i\ne {\underline{b}}^\omega _{i-1}\) for all i.
and \({\bar{b}}^\omega _i\ne {\underline{b}}^\omega _{i-1}\) for all i. -
(vi)
We define
 as the set of all sausage-walks from the origin 0 to x and
as the set of all sausage-walks from the origin 0 to x and  to be the set of all sausage-walks \(\omega \) from 0 to x such that
to be the set of all sausage-walks \(\omega \) from 0 to x such that  and \({\bar{b}}_1^\omega \ne {e}_{\iota }\). We write
and \({\bar{b}}_1^\omega \ne {e}_{\iota }\). We write  for the set of all sausage-walks such that
for the set of all sausage-walks such that  and \({\bar{b}}_1^\omega \ne {e}_{\iota }\), with arbitrary start and end point.
and \({\bar{b}}_1^\omega \ne {e}_{\iota }\), with arbitrary start and end point.
Similarly to Definition 3.2, a key point in Definition 3.3 is that a sausage-walk does not necessarily lead to a LA. For a rib-/sausage-walk \(\omega \), we define
where \(-{\mathcal {U}}_{s,t}(\omega )\) is the indicator that the ribs/sausages \(S_s^\omega \) and \(S_t^\omega \) intersect at some point in \({\mathbb {Z}}^d\). Then, \(K[0,|\omega |]\) is the indicator that all ribs/sausages of the walk are self-avoiding. Thus, if \(K[0,|\omega |](\omega )=1\), then the union of the oriented bonds and all ribs/sausages of \(\omega \) is a disjoint union and the resulting object is a LT/LA. The pair interaction in (3.1) thus gives a convenient description of when rib-/sausage-walks lead to a LT/LA, and this representation allows us to expand out this pair interaction in a convenient way.
To capture the contribution of the ribs/sausages we define
and remark that \(Z[a,b](\omega )=Z[a,c](\omega )Z[c+1,b](\omega )\) for \(c\in [a,b)\). We often drop the argument \(\omega \) for \({\mathcal {U}}_{st}, K[a,b]\) and Z[a, b] when this can cause no confusion. Further, we drop the superscript A and T for \({\mathcal {W}}\) when we consider both models simultaneously. We can now write the two-point function as
In the NoBLE, we use an adaptation of the two-point function given by
We expand \({\bar{G}}^{\kappa }\) using the same set of graphs and laces as used by Hara and Slade in [18]:
Definition 3.4
(Graphs and connected graphs) Let \(a,b\in \mathbb {N}\) with \(a<b\). For \(s,t\in [a,b]\cap \mathbb {N}\) with \(s<t\), the edge between s and t is the tuple (s, t). We abbreviate st to denote (s, t). We call a set of edges a graph. We call a graph connected, if for all \(c\in [a,b]\) there exists an edge \(st\in \Gamma \) such that \(s\le c\le t\). Let \({\mathcal {B}}[a,b]\) be the set of all graphs on [a, b] and \({\mathcal {G}}[a,b]\) the set of all connected graphs on [a, b].
Definition 3.5
(Laces and compatible edges) We call a graph minimally connected or a lace if the removal of any edge would disconnect the graph and define \({\mathcal {L}}[a,b]\) to be the set of all minimally-connected graphs on [a, b]. We define the function \(\mathrm{L}:{\mathcal {G}}[a,b] \mapsto {\mathcal {L}}[a,b]\) in a constructive manner as follows: For \(\Gamma \in {\mathcal {G}}[a,b]\), we let
This procedure ends after a finite number of steps N. We denote the resulting lace \(L=\{s_1t_1,s_2t_2,\ldots ,s_Nt_N\}\) by \(\mathrm{L}(\Gamma )\). We call an edge \(st\not \in L\) compatible to a lace L if \(\mathrm{L}(L\cup \{st\})=L\). We denote by \({\mathcal {C}}(L)\) the set of all edges that are compatible with L.
We define, for \(a>b\),
Further, we see that
and \(K[a,a]=J[a,a]=1\). The key observation in the lace expansion is that, for \(a<b\), we can write
see e.g. [18, Lemma 3.4]. We apply (3.7) to (3.3) with \(a=0\) and \(b=|\omega |>0\) to obtain
Here, the second term also contains the case where \(|\omega |=0\) and \(x=0\). We define the contribution of (3.9) to be \({\bar{\Xi }}_z(x)\), i.e.,
To further rewrite (3.8), we cut the non-backtracking rib-/sausage-walk at the ith bond of the backbone, \(b_i=(y,y-{e}_{\kappa })\), into a walk \(\omega ^1\in {\mathcal {W}}\) from 0 to y (which could correspond to a one-point function for \(|\omega ^1|=0\)), and a second walk \(\omega ^2\in \bigcup _{\kappa }{\mathcal {W}}^{\kappa }\) from \(y-{e}_{\kappa }\) to x. This leads to

where


In this way, we have obtained a recurrence relation for the two-point function given by
which is the first step towards (2.7). For (2.8), we instead consider
As \(\omega \in {\mathcal {W}}(x)\setminus {\mathcal {W}}^{\iota }(x)\) we know that \({e}_{\iota }\in S_0^\omega \) or \({\bar{b}}_1={e}_{\iota }\). For convenience, we define
and remark that the non-backtracking condition of the rib-/sausage-walk excludes that \({e}_{\iota }\in S_0^\omega \) and \({\bar{b}}_1={e}_{\iota }\) occur for the same walk. Therefore,
The contribution of \(J[0,|\omega |]\) gives rise to

Again, this term incorporates the contribution when \(|\omega |=0\). The dominant contribution of \(J[0,i]K[i+1,|\omega |]\) in (3.19) is given by \(|\omega |\ge 1, i=0\) and \(b^{\omega }_0=(0,{e}_{\iota })\), for which we see that
where \(g^{\iota }_z={\bar{G}}^{\iota }_z(0)\). We extract this contribution explicitly, and split the remainder at \(b_i=(y,y-{e}_{\kappa })\), as in (3.11), which leads to

We define

and see that the sums over \(\omega ^1\) and \(\omega ^2\) in (3.19) factorize, to conclude that

This completes the derivation of the expansion for LT and LA for \({\bar{G}}_{z}(x)\). To obtain (2.7) and (2.8), we need to divide (3.14) and (3.22) by \(g_z\), as we will explain in more detail in the next section. \(\square \)
3.2 Definitions Used in the Generalized Analysis
In this section we complete the expansion as stated in Cornerstone 2.1 and used in the general analysis of [12]. For the analysis, we use the normalized two-point functions LT and LA defined as
This has the advantage that the analysis and bounds on the lace-expansion coefficients are naturally divided into two parts. The one-point functions \(g_z\) and \(g_z^\iota \) and their influence, see (1.20), are controlled using the bootstrap function \(f_1\), see (2.15). The spatial dependence of the two-point functions is controlled using the bootstrap function \(f_2\), see (2.16).
To improve the numerical accuracy of our method, we extract some dominant contributions of the lace-expansion coefficients to be used explicitly within the analysis. These explicit terms are defined in Sect. 3.3. Before that we now complete the formal statement and proof of Cornerstone 2.1 by identifying the lace-expansion coefficients arising in it.
The NoBLE coefficients can be written into an alternating series of non-negative functions. The series arise in a natural way by the negative signs of the \({{\mathcal {U}}}_{st}\) terms in the expansion for LTs and LAs, see (3.5) as well as [10, Chap. 2], as we now explain in more detail:
Definition 3.6
(Laces for with fixed number of edges) For \(n\ge 1\) and \(N\ge 1\), let \({\mathcal {L}}^{{\scriptscriptstyle ( \text { N})}}[0,n]\subseteq {\mathcal {L}}[0,n]\) be the set of all laces \(L\subseteq {\mathcal {L}}[0,n]\) that consist of exactly N edges.
Define
A sausage/rib-walk \(\omega \) for which the indicator \(J^{\scriptscriptstyle ( \text { N})}\) equals one has N intersecting sausages/ribs. These intersections are characterized by the lace L in (3.24). This gives a convenient interpretation of the NoBLE coefficients that allows for sharp bounds. For \(N\ge 0\) and \(x\in {\mathbb {Z}}^d\), we define




to be the restrictions of the NoBLE coefficients to laces of fixed size, with the convention that \(J^{\scriptscriptstyle ( \text { 0})}[0,|\omega |]=\delta _{0,|\omega |}\).
The dominant contributions of these coefficients are given by

We use these terms explicitly in our analysis. We perform the NoBLE analysis using the following coefficients:
where we explicitly subtract the dominant contributions, of which most of them are also present for the NBW. The situation simplifies considerably for LTs, due to the absence of double connections, so that
while, using (3.16), as well as (3.20)–(3.21),

For LAs, several further contributions due to \(x\ne 0\), which require a double connection, arise. Using the above notation we obtain (2.7)–(2.8) by dividing the equations (3.14) and (3.22) by \(g_z\). Thereby, we have completed the formal statement and proof of Cornerstone 2.1, and have identified the NoBLE coefficients appearing in it. \(\square \)
3.3 Split for the Coefficients
In this section, we define further terms that we extract from the NoBLE coefficients to be used in the analysis of [12]. By extracting these terms we reduce the size of the perturbation, which ultimately improves the numerical accuracy of our analysis. We first give the definitions for LAs, and then explain how terms simplify for LTs.
Definition of the Explicit Terms for \(N=0\). For a LA A and \(x,y\in {\mathbb {Z}}^d\), we denote by \(x {\mathop {\Longleftrightarrow }\limits ^{A}} y\) the event that x and y are doubly connected via bonds in A. By \(d_A(x,y)\) we denote the intrinsic distance of x, y in A, meaning the length of the shortest connection of x and y using bonds in A. For \(N=0\), we define



and



For \(N=1\), the terms are more involved and are given by



All sausage-walks contributing to these sums have the following in common: (a) The first step of the backbone \({\underline{b}}^\omega _0\) starts at the origin. (b) The sausages \(S_0\) and \(S_{|\omega |}\) intersect either at 0 or at x. (c) At least one bond is explicitly present. Most of the times this bond is (0, x), forced by \(d_A(0,x)=1\).
We define the remainder terms arising through this split by
This completes the necessary split for LAs.
Lattice Trees. We use the same definitions for LTs, where we sum over LTs T instead of LAs A. However, for LTs the terms simplify considerably, as double connections are not possible. This is especially true for \(N=0\), for which, for all \(x\in {\mathbb {Z}}^d\) (recall (3.34)),

Further, the split actually captures the complete contribution of \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }_z\), since

This completes the derivation of the split of the coefficients as used in [12, Sect. 4].
3.4 Assumptions on the Model
In this section, we verify most of the assumptions necessary to apply the analysis of [12]. We start by proving the assumptions that are independent of the NoBLE: [12, Assumptions 2.2, 2.3 and 2.4].
3.4.1 Assumption on the Two-Point Function
We begin with [12, Assumption 2.4] as it will help us prove [12, Assumptions 2.2].
[12, Assumption 2.4]: For \(z\in [0,z_c)\), the functions \( z\mapsto {\bar{\mu }}_z\) and \(z\mapsto \mu _z\) are continuous.
To verify this assumption, we choose \({\bar{\mu }}_z=zg_z\) and \(\mu _z=zg_z^\iota \), with

By Abel’s Theorem, the one-point function is continuous within the radius of convergence of these power series, which is at most \(z_c\), see (1.3) and the text thereafter. Thus, also \(z\mapsto {\bar{\mu }}_z\) and \(z\mapsto \mu _z\) are continuous.
[12, Assumption 2.2]:There exists a \(z_I\in [0,z_c)\) such that (recall (2.2))
for all \(x\in {\mathbb {Z}}^d\) and \(z\in [0,z_I]\).
To prove this statement for LTs and LAs we adapt an argument used in [18, Proof of Lemma 3.1]. We know that each LT/LA containing 0 and x contains a path of bonds that connects 0 and x. Each point of the path is connected to at most one rib/sausage. The weight of all possible rib/sausages \(z^{|S_i|}\) (see (3.2)) can be bounded by \(g_z\), as each rib/sausage \(S_i\) is itself a LT/LA. For \(x\ne 0\) we can improve this by bounding the weight by \(g^{\iota }_z\) instead. This is possible as each rib/sausage needs to avoid at least the next/previous step of the path from 0 to x. From this, we conclude for \(x\ne 0\) that

where \({\mathcal {W}}^{{\scriptscriptstyle \text { NBW}}}(x)\) is the set of all NBWs (see the text above (2.5)) starting at 0 and ending at x, and \(|\omega |\) is the number of steps of the NBW \(\omega \). The inequality (3.54) then follows for all z for which \(zg^{\iota }_z\le (2d-1)^{-1}\) and \(x\ne 0\). We define
This is well-defined as \(\mu _z=zg_{z}^\iota \) is continuous and non-decreasing in z with \(zg_{z}^\iota =0\) when \(z=0\). To complete the proof of [12, Assumption 2.2], we still need to prove that \(z_I<z_c\). For this we note that \(g_z-g_z^\iota ={\bar{G}}_z({e}_{1})\) and use (3.54) to obtain

From this we conclude that
\(z_I\le z_c\) as otherwise
\(\chi (z_c)=\infty \), while
 on the right-hand side is finite. To exclude that
\(z_I=z_c\), we see that (3.54) also holds when we replace
\(g^{\iota }_z\) with
on the right-hand side is finite. To exclude that
\(z_I=z_c\), we see that (3.54) also holds when we replace
\(g^{\iota }_z\) with
for all ribs/sausages except those at 0 and x. We define \(z'\) as the value z such that \(z'g'_{z'}=(2d-1)^{-1}\), and conclude as in (3.56) that \(z_c \ge z'>z_I\). Recalling \({\bar{G}}_z(x)=g_z G_z(x)\) and \(g^{\iota }_z<g_z\) we conclude (3.54) from (3.53). This concludes the proof of [12, Assumption 2.4].
Additionally, we prove the lower bound \(z_I\ge (2d-1)^{-1}{\mathrm {e}}^{-1}\). As this uses ideas not used elsewhere, we move the proof to Appendix A (see Lemma A.1).
Growth of the two-point function. [12, Assumption 2.3]: We need to show that for every \(x\in {\mathbb {Z}}^d\), the two-point functions \(z\mapsto G_z(x)\) and \(z\mapsto G^\iota _z(x)\) are non-decreasing and differentiable in \(z\in (0,z_c)\). Further, we need to show that for all \(\varepsilon >0\), there exists a constant \(c_{\varepsilon }\ge 0\) such that for all \(z\in (0,z_c-\varepsilon )\) and \(x\in {\mathbb {Z}}^d\setminus \{0\}\),
Finally, we need to show that for each \(z\in (0,z_c)\), there exists a constant \(K(z)<\infty \) such that \(\sum _{x\in {\mathbb {Z}}^d} |x|^2 G_{z}(x)<K(z)\). We will do this now.
As a generating function of a non-negative sequence (see (1.2)), the two-point function is clearly non-decreasing in the parameter z as well as differentiable in z for \(z\in (0,z_c)\). Next, we first prove the bound on the derivative in (3.58) for LTs. We know that a LT T with |T| edges contains \(|T|+1\) vertices. We use this property to compute for \(x\ne 0\)
As a LT \(T\ni x,y\) contains no loops, the path from x to y is unique. We denote this path by \(b^T(x,y)\). By u we denote the last vertex that the paths from 0 to x and from 0 to y have in common. For \(u\ne x\) we split the walk at u into three individual trees and bound the contributions of these individual trees by two-point functions. Doing this, we have to take into account that in (3.59) the tree T is only weighted by \(z^{|T|-1}\), so that we have to choose one bond of the tree that does not carry the weight z. We choose the first step of the path from u to x to be this bond. For \(u=x\) there exists no first step. In this case, we choose the last step of the path from 0 to x to be the bond without weight z. Using that \({\bar{G}}_{z}(0)\ge 1\), we obtain the bound
For the normalized two-point function, we conclude
as required. To conclude such an inequality for LAs, we note that an animal with |A| bonds contains at least |A|/d vertices and as for the LT compute that
As the last step we prove that for all \(z< z_c\) there exists \(K(z)<\infty \) such that \(\sum _{x\in {\mathbb {Z}}^d} |x|^2 G_{z}(x)<K(z)\). In [20, (1.1)], it is proved that the connectivity constants \(\lambda =1/z_c\) can be used to prove that
Let \(|x|_\infty :=\max _{i=1}^d |x_i|\) be the supremum norm and compute
From this we conclude that \({\bar{G}}_z(x)\) decays exponentially for all \(z<z_c\), i.e., there exist \(c,m(z)\in (0,\infty )\) such that
We use this bound to conclude that
which proves the desired statement. \(\square \)
3.4.2 Assumptions on the NoBLE-Coefficients
In this section, we verify the assumptions on the NoBLE coefficients formulated in [12, Assumptions 4.1, 4.2 and 4.4].
Symmetry of the model. [12, Definition 2.5] We denote by \({\mathcal {P}}_d\) the set of all permutations of \(\{1,2,\ldots , d\}\). For \(\nu \in {\mathcal {P}}_d\), \(\delta \in \{-1,1\}^d\) and \(x\in {\mathbb {Z}}^d\), we define \(p(x;\nu ,\delta )\in {\mathbb {Z}}^d\) to be the vector with entries \((p(x;\nu ,\delta ))_j=\delta _j x_{\nu _j}\). We say that a function \(f:{\mathbb {Z}}^d\mapsto \mathbb {R}\) is totally rotationally symmetric (TRS) when \(f(x)=f(p(x;\nu ,\delta ))\) for all \(\nu \in {\mathcal {P}}_d\) and \(\delta \in \{-1,1\}^d\).
Total rotational symmetry is natural on \({\mathbb {Z}}^d\), e.g. the two-point function \(G_z\) as well as the NBW and SRW two-point functions have this symmetry. We next argue that the NoBLE coefficients have similar symmetries.
[12, Assumption 4.1]. Let \(\iota ,\kappa \in \{\pm 1,\pm 2,\ldots ,\pm d\}\). The following symmetries hold for all \(x\in {\mathbb {Z}}^d\), \(z\le z_c\), \(N\in \mathbb {N}\) and \(\iota ,\kappa \):
For all \(N\in \mathbb {N}\), the coefficients
as well as the remainder terms of the split

are totally rotationally symmetric functions of \(x\in {\mathbb {Z}}^d\). Further, the dimensions are exchangeable, i.e., for all \(\iota ,\kappa \),
By the definition of the NoBLE coefficients in Sect. 3.1, it is easy to see that (3.67), (3.68) and (3.71) hold. The TRS stated in (3.69), (3.70) might be less obvious. The definition of \(\Xi ^{\scriptscriptstyle ( \text { N})}_z\) does not include constraints on specific directions, so it is not difficult to see that \(x\mapsto \Xi ^{\scriptscriptstyle ( \text { N})}_z(x)\) is TRS for all \(N\ge 0\). The other three NoBLE coefficients are not TRS as their definition includes constraints on one or two specific directions. For example, the coefficient \(\Psi ^{{\scriptscriptstyle ( \text { N})},\kappa }_z(x)\) includes the constraint that \(x-{e}_{\kappa }\) is not in the last rib/sausage. When we sum over \(\kappa \), though, the directional constraint is averaged out and thus \(\sum _{\kappa }\Psi ^{{\scriptscriptstyle ( \text { N})},\kappa }_z(x)\) is TRS. For the same reason, the sums over \(\iota \) and \(\iota ,\kappa \) in (3.69), as well as the stated remainder terms, are TRS. The arguments given above hold provided that the coefficients are well-defined, which is definitely the case for all \(z<z_c\).
[12, Assumption 4.1] states that the symmetry properties also hold for \(z=z_c\), where it is not even obvious that these objects are well-defined. We verify the left-continuity in [12, Assumption 4.4] below, from which the symmetries will follow also for \(z=z_c\). Further, inspection of the proof in [12] shows that the symmetries are only used for \(z<z_c\). \(\square \)
Relation between coefficients. [12, Assumption 4.2] For all \(x\in {\mathbb {Z}}^d\), \(z\le z_c\), \(N\in \mathbb {N}\) and \(\iota ,\kappa \in \{\pm 1,\pm 2,\ldots ,\pm d\}\), the following bounds hold:
We first compare \({\bar{\Xi }}^{{\scriptscriptstyle ( \text { N})}}\) and \({\bar{\Psi }}^{{\scriptscriptstyle ( \text { N})},\kappa }\), in (3.25), (3.27) and see that they differ by the additional condition  , so that \({\bar{\Xi }}^{{\scriptscriptstyle ( \text { N})}}(x)\le {\bar{\Psi }}^{{\scriptscriptstyle ( \text { N})},\kappa }(x)\). Considering the normalisation (3.33), we see that \(\Xi ^{{\scriptscriptstyle ( \text { N})}}\) was normalised using \(g_z\), while \(\Psi ^{{\scriptscriptstyle ( \text { N})},\kappa }\) was normalised using \(g^{\iota }_z\). As \({\bar{\mu }}_z/\mu _z=g_z/g^{\iota }_z\) we conclude that the left inequality in (3.72) holds.
, so that \({\bar{\Xi }}^{{\scriptscriptstyle ( \text { N})}}(x)\le {\bar{\Psi }}^{{\scriptscriptstyle ( \text { N})},\kappa }(x)\). Considering the normalisation (3.33), we see that \(\Xi ^{{\scriptscriptstyle ( \text { N})}}\) was normalised using \(g_z\), while \(\Psi ^{{\scriptscriptstyle ( \text { N})},\kappa }\) was normalised using \(g^{\iota }_z\). As \({\bar{\mu }}_z/\mu _z=g_z/g^{\iota }_z\) we conclude that the left inequality in (3.72) holds.
Regarding \(\Xi ^{{\scriptscriptstyle ( \text { N})},\iota }\) and \(\Pi ^{{\scriptscriptstyle ( \text { N})},\iota ,\kappa }\), defined in (3.26) and (3.28), note that \(\Pi ^{{\scriptscriptstyle ( \text { N})},\iota ,\kappa }\) contains the extra factor \(\mathbbm {1}_{\iota }(\omega )=\mathbbm {1}^{\Pi }_{\iota }(\omega ,x,\kappa )\) for \(N\ge 1\), as well as an additional factor z. Further, we do not normalize \(\Pi ^{{\scriptscriptstyle ( \text { N})},\iota ,\kappa }\), while \(\Xi ^{{\scriptscriptstyle ( \text { N})},\iota }\) is normalized with a factor \(1/g_z\), creating the stated factor \({\bar{\mu }}_z=zg_z\), which proves the bound for \(N\ge 1\). To obtain the equation also for \(N=0\), we review (3.21) and see that \(\mathbbm {1}_{\iota }(\omega )\) and \(\mathbbm {1}^{\Pi }_{\iota }(\omega ,x,\kappa )\) only differ when \(x\ne 0\), which is not possible for LTs, as double connections are not present. For LAs, we see that

and conclude the desired relation for \(x\ne {e}_{\iota }+{e}_{\kappa }\), with \(\iota \ne -\kappa \). For the remaining case \(x={e}_{\iota }+{e}_{\kappa }\) with \(|\iota |\ne |\kappa |\), we compute

by symmetry in \(\iota , \kappa \). To verify that this is positive for all \(d\ge 30\), we use the highly helpful rearrangement

so that

While it is to be expected that this quantity is indeed positive, we could not find a direct injection between the different classes of LAs with the same number of bonds. Thus, we have to resort to a numerical verification of the inequality, using numerical upper and lower bounds. We add this extra numerical verification in the LA Mathematica notebook (see [9, Improvement of Bounds, Technical condition]), alongside three other numerical conditions that need to be verified for the analysis of [12], like \({{\hat{G}}}_z(k)\ge 0\) for all k.
Alternatively, this condition could be dropped, at the expense of having to prove separate bounds for \(\Pi ^{{\scriptscriptstyle ( \text { 0})},\iota ,\kappa }(x)\), rather than relying on this simple relation to bound \(\Pi ^{{\scriptscriptstyle ( \text { 0})},\iota ,\kappa }(x)\) in terms of \( \Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }(x)\). We refrain from following this route. \(\square \)
Growth at the critical point. [12, Assumption 4.4] The functions \(z\mapsto {\hat{\Xi }}_z(k),z\mapsto {\hat{\Xi }}^{\iota }_z(k),z\mapsto {\hat{\Psi }}^{\kappa }_z(k),z\mapsto {\hat{\Pi }}^{\iota ,\kappa }_z(k)\) are continuous for \(z\in (0,z_c)\). Further, let \(\Gamma _1,\Gamma _2,\Gamma _3\ge 0\) be such that \(f_i(z)\le \Gamma _i\) and assume that [12, Assumption 4.3] holds. Then, the functions \(z\mapsto \Xi _z(x),z\mapsto \Xi ^{\iota }_z(x),z\mapsto \Psi ^{\kappa }_z(x),z\mapsto \Pi ^{\iota ,\kappa }_z(x)\) are all left-continuous in \(z_c\) with a finite limit when \(z\nearrow z_c\) for all \(x\in {\mathbb {Z}}^d\). Further, for technical reasons, we assume that \(z_c<\tfrac{1}{2}{}\).
The two-point function \(G_z\) is defined as a power series that is clearly continuous in z within its radius of convergence \(z_c\). Since \(G^\iota _z\le G_z\), it has a radius of convergence that is at least \(z_c\). The coefficients \(\Xi ^{{\scriptscriptstyle ( \text { N})}}_z,\Xi ^{{{\scriptscriptstyle ( \text { N})}},\iota }_z,\Psi ^{{{\scriptscriptstyle ( \text { N})}},\iota }_z\) and \(\Pi ^{{{\scriptscriptstyle ( \text { N})}},\iota ,\kappa }_z\) are also power series and can be bounded in terms of many two-point functions. Since \(\sum _{x\in {\mathbb {Z}}^d} G_z(x)<\infty \) for all \(z<z_c\), also the radii of convergence of these coefficients are at least \(z_c\). [We believe that \(G^\iota _z\) and the NoBLE coefficients have the same radii of convergence as \(G_z\), but that is irrelevant here.] Assuming that the bootstrap functions are uniformly bounded, all stated functions are uniformly bounded as well, which implies that they are left-continuous at \(z_c\) by Abel’s theorem.
To prove that \(z_c<\tfrac{1}{2}{}\) consider a simple random walk that only takes steps in the positive direction. After n steps there are \(d^n\) possible trajectories, each being also a LT, so that \(t_n(0)\ge d^n\). As \(z_c\) is defined as the radius of convergence of \(\chi \) (see (1.3)), and
we know that \(z_c\le 1/d<\tfrac{1}{2}{}\).
4 An Overview to the NoBLE Diagrammatic Bounds
In this section we discuss how we bound the NoBLE coefficients. We explain the concepts that we use to obtain sharp numerical bounds on these diagrams, each of which forms a numerical improvement on the bounds on classical lace-expansion coefficients. We make the bounds explicit by giving numerical values for \({\bar{\Xi }}^{{\scriptscriptstyle ( \text { 1})}}\) for LTs, in the particular case of \(d=18\). While the choice of \(d=18\) is somewhat arbitrary, the numerical improvements show the importance of each of the four improvements. Then, we follow that up with the technical definitions of these concepts. We end this section with a discussion of how we bound double connections for LAs, as these are quite central in our bounds for LAs.
4.1 Basic Bounds and Their Improvements
We explain here how we obtain sharp numerical bounds on
by using four central ideas that we explain one at a time. We restrict ourselves here to LTs in dimension \(d=18\), as these give rise to the simplest diagrams, which already display all the main characteristics of our bounds.
We compare the improvement that we obtain in our bounds by providing numerical bounds for the initial point \(z=z_I\) resulting from the numerical analysis performed in our Mathematica notebooks. Our proof is based upon the fact that the values of various quantities at \(z_I\) and at \(z_c\) are actually quite close. Thus, even though \(z_c>z_I\), such bounds should give us a clear idea of how large such bounds are, and what the effect of certain specific improvements is.
We recall (3.54) and combine it with the bound \(g^\iota _{z_I}\le {\mathrm {e}}\), see (A.6), to conclude, for \(z_I=(2d-1)^{-1}{\mathrm {e}}^{-1}\),
where \({\mathrm {e}}\) is the Euler number and B(x) is the critical two-point function of the NBW, see (2.5). This bound is independent of the lace expansion and we can compute its value numerically. While this bound does not hold at the critical point \(z_c\), its value is a good enough approximation to compare the bounds discussed in this section. All stated numerical results are computed for dimension \(d=18\), and are aimed to convey the numerical improvements in the bounds.
Plain–Vanilla Bound. We focus on \({\bar{\Xi }}^{{\scriptscriptstyle ( \text { 1})}}_z\) and start with the simplest possible approach, which relies on the bounds as they have been stated up to now in the literature. The coefficient \({\bar{\Xi }}^{{\scriptscriptstyle ( \text { 1})}}_z\) involves three points: 0, x and a point where \(S^{\omega }_0\) and \(S^{\omega }_{|\omega |}\) intersect, which we denote by w. Bounding the connections between each of the points by individual independent LTs we obtain
which, combined with (4.2), implies
This is of course a very bad bound that does not allow us to successfully apply the lace-expansion method, so we improve it using the four ideas explained below.
First Improvement: Extracting Trivial Lines. A simple way to improve this bound is to consider four cases depending on which lines are trivial: first \(x=0\), then \(w=x\ne 0\) and \(w=0\ne x\), and finally the remaining cases. In the case \(x=0\), we extract the contribution of the first rib \(g_z^\iota \) and the first bond of the backbone with all its possible directions 2dz, and bound the remaining rib-walk, that goes back to the origin, by \({\bar{G}}_z({e}_{1})\). Thus, the case \(x=0\) is bounded by \(2d zg_z^\iota (D\star {\bar{G}}_z)(0)\).
For \(w=x\ne 0\) and \(w=0\ne x\), 2 non-trivial two-point functions are required. For  , instead, all three connections are non-trivial. We bound the non-trivial connections by \({\bar{G}}_{z_I}(x) \le {\mathrm {e}}B(x)\le \tfrac{2d{\mathrm {e}}}{2d-1}(D\star B)(x)\) for \(x\ne 0\) and conclude that
, instead, all three connections are non-trivial. We bound the non-trivial connections by \({\bar{G}}_{z_I}(x) \le {\mathrm {e}}B(x)\le \tfrac{2d{\mathrm {e}}}{2d-1}(D\star B)(x)\) for \(x\ne 0\) and conclude that
This is an enormous improvement compared to (4.4). The simple idea of extracting trivial lines, by splitting between different cases, is a basic technique that is used for all coefficients in Sect. 6.
Second Improvement: Improved Counting of One-Point Functions by Rib Allocation. We observe that we extract a single one-point function at every line in an intersection point. This gives rise to the three factors of \({\mathrm {e}}\) in (4.5). However, when the different lines come from the same rib, there in fact is only one one-point function, so that we are overcounting one one-point function (leading to a factor \({\mathrm {e}}\)) every time we split a rib. Thus, for the diagram in (4.4), we would need only one factor \({\mathrm {e}}\) instead of three. Let us explain one way to obtain a bound without overcounting.
In (4.3), the terms \({\bar{G}}_z(w)\) and \({\bar{G}}_z(w-x)\) bound the ribs \(S^{\omega }_0\) and \(S^{\omega }_{|\omega |}\), which, being ribs, are just LTs. The indicator \(J^{\scriptscriptstyle ( \text { 1})}[0,|\omega |]\) in (4.1) guarantees that only those \(\omega \) contribute for which all in-between ribs do not intersect, so that the rib-walk between \({\overline{b}}_1^\omega =u\) and \({\overline{b}}^{\omega }_{|\omega |}=v\) also describes a LT and can be bounded by \({\bar{G}}_z(v-u)\). Explicitly extracting the case that \(|\omega |=1\), for which \({\overline{b}}_1^\omega ={\overline{b}}^{\omega }_{|\omega |}\), so that there are no in-between ribs, we obtain
where z and \(z^2\) correspond to the weight of the first and last bond of the original backbone.Note that \(g_{z_I} z_I\) is roughly 1/(2d) and \(g_{z_I}\approx {\mathrm {e}}\), so that \(z_I\approx 1/(2d{\mathrm {e}})\) (see e.g., Theorem 1.2 or Lemma A.1 in the appendix). In turn, this implies that \(2d z_I{\bar{G}}_{z_I}\approx B\) rather than \({\mathrm {e}}B\). Considering the four cases for 0, x, w, used in the first improvement, we thus obtain
The improvement of (4.5) to (4.7) is mostly realized by the proper handling of the weights of the one-point function \(g^{\iota }_z\approx {\mathrm {e}}\) at the origin and at x, which are bounded twice in (4.5), leading to two unnecessary factors of \({\mathrm {e}}\) in some of the contributions.
Remark 4.1
(Rib-weight allocation) In general, the diagram of \(\Xi ^{{\scriptscriptstyle ( \text { N})}}_z\) has \(4N-1\) connections for LTs. Allocating the one-point functions properly will save us approximately a factor \({\mathrm {e}}^{4N-2}\) for all N. This allocation of rib weights is a central technical problem, especially as we require various different allocations for the weights when we bound the coefficient with spatial weight \(|x|^2\). Using splitting arguments of such spatial terms, that are standard in lace-expansion analyses, we split the weight along a path connecting 0 and x, e.g. using \(|x|^2\le N\sum _{i=1}^N |x_i|^2\), where the \((x_i)_{i=1}^N\) are the displacements along the bottom lines of the diagram, so that \(x=\sum _{i=1}^N x_i\). For each of these partial weights \(|x_i|^2\), we want to bound the corresponding connection by \({\bar{G}}_z\), as \(f_3\) only provides us with a bound on \(|x_i|^2 {\bar{G}}_z(x_i)\). This imposes severe restrictions on our rib-weight allocation, and we need to be really careful in such arguments. We discuss this in more detail in Sect. 4.2, see also Remark 4.5.
Third Improvement: Using the Non-backtracking Nature of the Diagram. Now, we use the non-backtracking property of the rib-walk for the first time. This property implies that any loop needs at least 4 bonds, as direct reversals are prohibited and loops on the lattice require an even number of bonds. For example, the self-loop of the rib-walk back to \(x=0\) will take at least 4 steps and can thus instead be bounded by
Further, we can omit the case \(w\in \{0,x\}\) for the case that \(b_1^\omega =(0,x)\), see property (v) of Definition 3.2. Going through 8 different combinations of how the 4 steps can be distributed, we obtain
The improvement from (4.7) to (4.9) demonstrates the power of the NoBLE and its non-backtracking property. To use this property for more involved diagrams, we will split depending on the lengths of lines shared by two loops. This splitting into a total of five cases of lengths of shared lines will create matrix-based bounds. This will become apparent in Sect. 5.1.
Fourth Improvement: Using Repulsiveness in Diagrams. We can actually improve this bound even further. For this we have to understand that the paths connecting 0, x and w do not intersect, so that the loop is actually a self-avoiding polygon. We call such a polygon a repulsive diagram. For this to work, we have to choose the point \(w_1\) as a first intersection point and bound it by a repulsive diagram. We formally define both italic phrases in the next two sections. Using these repulsive diagrams, we improve the bound (4.9) to
This is explained in more detail in Sect. 4.3.
Summary. By the above four improvements combined, we have now improved our estimate on this simple diagram \(\sum _{x\in {\mathbb {Z}}^d}{\bar{\Xi }}^{{\scriptscriptstyle ( \text { 1})}}_{z_I}(x)\) by a factor that is close to 1000. Since we need all the numerical precision that we can get our hands upon, so as to be able to apply our methods in the lowest possible dimensions, such estimates are crucial to the success of our method.
Extension to Lattice Animals. Lattice animals (LAs) allow for double connections. Despite this additional difficulty, for \({\underline{b}}_0=0\) and \({\overline{b}}_{|\omega |}=x\), we can use the same bounds as explained in (4.3)–(4.10) based on exactly the same arguments. For \({\underline{b}}_0\ne 0\) we need to bound the sausage, which connects the points \(0,{\underline{b}}_0\), as well as the first intersection point \(w_1\). We explain this in Sect. 4.2, where we also define the required notions. In Sect. 4.4, we discuss how we use a symmetry argument to improve the bound for the important case \(w_1\in \{0,{\underline{b}}_0\}\) of a double connection.
4.2 Allocation of One-Point Functions
In the preceding section, we disassembled the rib-walk into up to three pieces: the initial rib, the final rib and the walk in between, and have argued that rib-weight allocation is a crucial ingredient to the success of our method. In the following, we also need to split individual ribs/sausages. Below we give a rigorous description of the split of a rib/LT and explain how we ensure that we do not overcount one-point functions by an optimal rib-weight allocation.
After this, we explain the allocation of one-point functions for the more involved diagrams. In the process we define the concept of first intersection point of two sausages, that will allow us to choose bond-disjoint paths connecting the corner points of the loops. In the next section we use this choice of bond-disjoint paths to define repulsive diagrams.
Splitting the Weight of a Rib: Planted Animals/Trees. Our aim is to bound the contribution \(z^{|T|}\) of LTs that contain the vertices \(0,x,v\in {\mathbb {Z}}^d\) efficiently. We identify the last vertex u that the path \(0\leftrightarrow x\) and the path \(0\leftrightarrow v\) have in common, split the tree into three trees and ignore the avoidance constraints between them to obtain
which corresponds to the plain-vanilla bound of the last section. Thus, it also counts three ribs at u, whereas there really only is one.
To avoid this, we define an adapted version of the two-point function that only counts the trivial first rib/sausage \(A^\omega _0=\varnothing \), i.e.,
Using this two-point function, we obtain the bound
which is approximately \({\mathrm {e}}^2\) smaller than (4.11).
Planted Animals. For LTs, the point u at which we split the tree is unique, which is not the case for LA. We define the concepts of backbone, connecting planted animal and first point of intersection, to provide a rigorous way to split the sausage for LAs. We only give the definition for LAs and sausage-walks, as each LT is also a LA and each rib-walk is also a sausage-walk. See Fig. 7 for an example of connecting planted animals.
Before defining these notions, we discuss the lexicographic order on paths, which is a way to identify paths uniquely. We say that \(x\in {\mathbb {Z}}^d\) has a lower lexicographic order than \(y\in {\mathbb {Z}}^d\), if there exists an \(i\in \{1,2,\ldots ,d \}\) with \(x_i<y_i\) and \(x_j=y_j\) for \(j=1,2,\ldots , i-1\). A bond b is defined as a tuple of two vertices \(b=({\underline{b}},{\overline{b}})\), so that we can view b also to be a vector in \(\mathbb {Z}^{2d}\) and use the same order relations as for vertices. A path \((b_1,b_2,\ldots ,b_n)\) has a lower lexicographic order than the path \((t_1,t_2,\ldots ,t_m)\), if either there exists a \(i\in \{1,2,\ldots , \min (n,m)\}\), such that \(b_i\) has a lower order than \(t_i\) and \(b_j=t_j\) for \(j=1,2,\ldots , i-1\) or if \(n<m\) and \(b_i=t_i\) for \(i=1,2,\ldots , n\).
Definition 4.2
(Backbone) Let A be a lattice animal containing \(x,y\in {\mathbb {Z}}^d\), with \(x\ne y\). A path from x to y in A is a sequence of bonds \((b_i)_{i=1}^N\) such that \(b_i\in A, {\overline{b}}_i\ne {\overline{b}}_j\) for all \(i\ne j\), and \({\underline{b}}_1=x,{\overline{b}}_i={\underline{b}}_{i+1},{\overline{b}}_N=y\) for \(i=1,\ldots ,N-1\). We define \(b^A(x,y)\) to be the path from x to y in A with the lowest lexicographic order. For \(x=y\in A\), we define \(b^A(x,y)=\varnothing \).
Definition 4.3
(Connecting planted animal) Let A be a lattice animal containing \(x,y\in {\mathbb {Z}}^d\), with \(x\ne y\), and let p be a path from x to y in A. We write \(A\setminus p\) for the collection of bonds obtained by removing the bonds in p from those in A. Let S be the subset of \(A\setminus p{}\) of all bonds for which at least one vertex of the bond is connected to x via bonds in \(A\setminus p{}\). We call \(B^A(x,y;p)=A\setminus S\) the connecting planted animal from x to y along p.
Unless stated otherwise, we consider the path p to be the backbone \(p=b^A(x,y)\) and omit p from the notation. For a sausage-/rib-walk \(\omega \), we define \(B^\omega _i(x,y)=B^{A^\omega _i}(x,y)\).
We next define the notion of a first intersection point. We do this in a more general setting, encoded by a lace L, where some of the LAs are forced to intersect each other, while others are not. This will make sure that we can use this definition for all NoBLE lace-expansion coefficients:
Definition 4.4
(First intersection point) For a sausage-walk \(\omega \), a lace \(L=\{s_1t_1,s_2t_2,\) \(\ldots ,\) \(s_Mt_M\}\) and \(i\le M\), we define \(W_i(\omega )\) to be the set of vertices w that are contained in both \(A^\omega _{s_i}\) and \(A^\omega _{t_i}\), such that \(b^{A^\omega _{s_i}}({\overline{b}}^\omega _{s_i},w)\) and \(A^\omega _{t_i}({\overline{b}}^\omega _{t_i},w)\) only intersect at w. If \(W_i(\omega )\) is non-empty, then we define \(w_i(\omega )\) to be the smallest in the set \(W_i(\omega )\). We call \(w_i(\omega )\) the first intersection point of \(A^\omega _{s_i}\) and \(A^\omega _{t_i}\).
Note that if the end of the \(s_i\)th pivotal bond \({\overline{b}}^\omega _{s_i}\) is in \(S^\omega _{t_i}\), then \(W_i(\omega )=\{{\overline{b}}^\omega _{s_i}\}\). We illustrate the concept of a first intersection point in Fig. 8.
Two examples of the set of first intersection points \(W_N(\omega )=\{w_a,w_b,w_c\}\). In the picture the \(s_N\)th and \(t_N\)th sausage of the sausage-walk \(\omega \) intersect. We choose the point \(w_N(\omega )\) to be the unique smallest representative of \(W_N(\omega )\) in the lexicographic order
Non-trivial sausages. If we wish to extend the analysis to LAs, then we need to deal with non-trivial sausages. A lattice animal A is called a non-trivial sausage if it contains three vertices 0, x, w (with \(x\ne 0\)), such that 0 and x are doubly connected in A, as shown in the first image of Fig. 9. We now show how we bound these sausages. In Sect. 4.4, we explain how we obtain improved bounds for the special case \(w\in \{0,x\}\), which is a major contribution for LAs.
We define the point u to be a point that every path from 0 to w and x to w shares. By construction, the points 0, u, x are pairwise doubly connected, so that there exist four bond-disjoint paths: \(p_1(u,w), p_2(u,x), p_3(0,u)\) and \(p_4(0,x)\) connecting the indicated points in A. We bound the contribution of such LAs by
We obtain this bound by decomposing each LA A into four parts as shown in Fig. 9. Using the pictured decomposition, we know that \(A_4\) is an animal containing x, the sum of which we bound by \({\bar{G}}_z(x)\). Further, \(A_1\) and \(A_3\), respectively, only include one bond that contains u and 0, respectively. Thus, we bound their sums using the modified two-point function \({\tilde{G}}_z\). The animal \(A_2\) is the interesting case as u and x are only connected by one bond each. If \(u\ne x\), then we bound its contribution by the step involved by \(2d z D(\cdot )\) and the remainder by \({\tilde{G}}_z\), creating the bound \(2dz(D\star {\tilde{G}}_z)(x-u)\). If \(u=x\) then \(A_2=\varnothing \) and \(A_3\) only has one bond at the origin and one at x, so we bound the sum over \(A_3\) by \(2dz(D\star {\tilde{G}}_z)(x)\).
The way that we split a LA to obtain the bound (4.14)
There are multiple ways to split such animals, and depending on the situation we might want to use a different combination of where to attribute the rib weights. To give an example, we can create animals as discussed above in which each line is bounded by \({\tilde{G}}_z\). For this, we modify the split shown in Fig. 9 as follows:
-
(i.)
Let \(R_3=B^{R_2}(x,0; p_4(x,0))\), and \(R_4=R_2\setminus R_3\).
-
(ii.)
Let \({\bar{A}}_3=B^{R_2}(0,u; p_3(0,u))\), and \({\bar{A}}_4=R_3\setminus {\bar{A}}_3\).
-
(iii.)
Let \({\bar{A}}_2=R_4\cup A_2\).
The split into \(A_1,{\bar{A}}_2,{\bar{A}}_3\) and \({\bar{A}}_4\) is very much like the one shown in Fig. 9, the only difference being that every bond incident to x that is not part of the path \(p_4(x,0)\) is now part of \({\bar{A}}_2\) instead of \({\bar{A}}_4\). This gives rise to the bound
Which of the different bounds is chosen depends on the precise nature of the bound that we are deriving. In fact, optimizing over such decisions is numerically an important ingredient of our method.
Bound on the Sausage-Walk in \(\Xi ^{{\scriptscriptstyle ( \text { 1})}}_z(x)\). Here we continue our bound on \(\Xi ^{{\scriptscriptstyle ( \text { 1})}}_z(x)\) started in Sect. 4.1, now specializing to LAs with a non-trivial first sausage. We have bounded the case \({\underline{b}}_1=0\) by splitting the sausage-walk into three parts:
-
(a)
The first sausage \(S^\omega _0\) that connects 0 and \(w_1(\omega )\), whose sum is bounded by \({\bar{G}}_z(w)\);
-
(b)
The last sausage \(S^\omega _{|\omega |}\) that connects x and \(w_1(\omega )\), whose sum is bounded by \({\bar{G}}_z(w-x)\);
-
(c)
The remaining sausage-walk without the first and last sausage, whose sum is bounded by \(2dz(D\star {\tilde{G}}_z)(x)\).
For \({\underline{b}}_1\ne 0\), which is not possible for LTs, we need to split the first sausage \(S^\omega _0\). The first sausage contains \(0,{\underline{b}}_1\) and \(w_1(\omega )\) and doubly connects 0 and \({\underline{b}}_1\). Thus, \(S^\omega _0\) is a non-trivial sausage as discussed in the previous paragraph. Combining these bounds we arrive at
where the second term is absent for LTs.
The Allocation of One-Point Functions. As can be seen above, we have some choice in how we split the sausages. This becomes quite complex when more lines are involved. Let us discuss the example \(\Xi ^{{\scriptscriptstyle ( \text { 2})}}_z\), which is the simplest diagram of the more involved ones.
In the following, we define how we split the diagram of \(\Xi ^{{\scriptscriptstyle ( \text { 2})}}_z(x)\) for \(s_2<t_1\), as shown in Fig. 10. Consider \(\omega \) and a lace L that contributes to \(\Xi ^{{\scriptscriptstyle ( \text { 2})}}_z(x)\). We know that \(S^\omega _{0},S^\omega _{t_1}\) and \(S^\omega _{s_2},S^\omega _{|\omega |}\) intersect, at their first intersection points \(w_1(\omega )\) and \(w_2(\omega )\) (recall Definition 4.4).
Let u be the last common point of the paths \(0\longleftrightarrow w_1(\omega )\) and \({\underline{b}}_1\longleftrightarrow w_1(\omega )\) in \(S_0^\omega \). Let y be the last point that the paths \({\overline{b}}_1\longleftrightarrow w_2(\omega )\) and \({\underline{b}}_{t_1+1}\longleftrightarrow w_1(\omega )\) in \(\omega \) share.
For \({\underline{b}}_1=0\), we have that \(u=0\) and define \(I_{S1}:=B^{S_0^{\omega }}_0(0,w_1)\) and \(I_{S2}=I_{S3}=I_{S4}=\varnothing \).
For \({\underline{b}}_1\ne 0\), the first sausage is non-trivial. We use the split that created (4.15), which formally corresponds to
Then, we split the three branches from the backbone, that create two intersections at \(w_1\) and \(w_2\), namely \(II_S:=B^ \omega _{t_1}(y,w_2)\), \(III_S:=B^\omega _{s_2}({\underline{b}}_{s_2+1},w_1)\) and \(IV_S:=B^\omega _{|\omega |}(x,w_2)\). The trimmed sausage-walks then create \(II_B\), \(III_B\), \(IV_B\). By this construction, all ten paths connecting the labeled points are bond-disjoint and each piece is a LA.
All pieces with sub-index S are planted animals, whose sums can be bounded by \({\tilde{G}}_z\). For the backbone lines \(II_B,III_B,IV_B\), we have to decide where to bound the sausages at the labeled points. We can bound two of the pieces using \({\tilde{G}}_z\), taking into account only the weight of either the first or final sausage. The third piece has to be bounded using \({\bar{G}}_z\), which bounds the sausages on both ends. Thus, we bound only one connection by \({\bar{G}}_z\), rather than all four, which is a major improvement. Using a slightly different split of the sausage-walk, we are actually free to choose any line to be bounded by \({\bar{G}}_z\). This will be useful when dealing with weighted diagrams, as we discuss in detail in Sect. 6.2.
For the case \(t_1=s_2\), as shown in the right diagram of Fig. 10, we need to split the sausage \(S^\omega _{t_1}\). For this we define y to the be point that all connections in \(S^\omega _{t_1}\) from \({\underline{b}}_{t_1+1}\) to \(w_1\) and from \({\underline{b}}_{t_1+1}\) to \(w_2\) share and define
The rest is split in the same way as described for the case \(s_2<t_1\).
Remark 4.5
(One-point function allocation) In Fig. 10, we have ten connections, nine of which can be bounded by \({\tilde{G}}_z\), and one by \({\bar{G}}_z\). In general, the diagram of \(\Xi ^{{\scriptscriptstyle ( \text { N})}}_z\) has \(4N+2\) connections, and only one of them needs to be bounded by \({\bar{G}}_z\). This means that by bounding each line by \({\bar{G}}_z\) instead of \({\tilde{G}}_z\), as done previously in literature, any bound on \({\hat{\Xi }}^{{\scriptscriptstyle ( \text { N})}}_z\) is unnecessarily a factor \({\mathrm {e}}^{4N+1}\) too large, at least for \({\underline{b}}_1\ne 0\). For \({\underline{b}}_1=0\) three lines are trivial (\(I_{S2}=I_{S3}=I_{S4}=\varnothing \)), so that this unnecessary factor is still \({\mathrm {e}}^{4N-2}\). We can and will choose which of the lines is bounded by \({\bar{G}}_z\) in a way that sensitively depends on the precise structure of a diagram. In Sect. 6.2, we explain in detail how we do this for the lace-expansion coefficients with the spatial weight \(|x|^2\), for which it is the most relevant. For bounds without the spatial weights, we usually use the split shown in Fig. 11. There, we use the bound \({\bar{G}}_z(x)\le g^{\iota }_z{\tilde{G}}_z(x)\) for \(x\ne 0\) for the single \({\bar{G}}_z\) factor, which simply extracts one one-point function \(g^{\iota }_z\), after which all connections of the diagram are given by \({\tilde{G}}_z\).
4.3 Repulsive Diagrams
In this section, we define the basic diagrams used to bound the NoBLE coefficients. The ribs/sausages of the NoBLE coefficients have numerous avoidance constraints. We incorporate some of these in our diagrams to improve our numerical bounds. Here we explain how this can be done using so-called repulsive diagrams.
Picture of a possible \(\Xi ^{{\scriptscriptstyle ( \text { 4})}}_z\) diagram. The backbone is marked by a thicker line and the ribs of \(x_i\) have different colors. Arrow tips indicate that the one-point function is allocated at this endpoint. Thus, all lines except for one are \({\tilde{G}}\)’s. Only one line has two arrow tips, which corresponds to a factor \(\bar{G}\). This line can be located anywhere in the diagram. In the above one-point function allocation, the line between 0 and \(x_1\) corresponds to a factor \(\bar{G}\). The numbers are labels for the corresponding two-point functions
To motivate the precise definition of these diagrams, we review the avoidance structure of the first square (1, 2, 3, 4) in Fig. 11. In the diagrams the vertices \(x_i\) denote points on the backbone, the vertices \(w_i\) denote the ith first intersection point (recall Definition 4.4), and \(u_i\) the vertices where we have to split a sausage/rib. Like the split of \(\Xi ^{{\scriptscriptstyle ( \text { N})}}_z\) given above, the split given in Fig. 11 has the following interpretation:
- \(\rhd \):
-
Line 2 is the connected planted animal \(B^{\omega }_0(0,w_1)\);
- \(\rhd \):
-
Line 3 is the connected planted animal \(B^{\omega }_{t_1}(x_1,w_1)\);
- \(\rhd \):
-
Line 4 is the connected planted animal \(B^{\omega }_{t_1}(w_1,u_1)\);
- \(\rhd \):
-
Line 1 is the backbone \(b^\omega (0,x_1)\), together with the sausages \((A^\omega _{i})_{i=1}^{t_1-1}\) and the (trimmed) animal \(A^{\omega }_{t_1}\setminus (B^{\omega }_{t_1}(x_1,w_1)\cup B^{\omega }_{t_1}(w_1,u_1))\).
These lines obey the following avoidance constraints:
- \(\rhd \):
-
Relation between lines 1 and 2: By the definition of \(J[0,|\omega |]\), the sausage \(A_{t_1}^\omega \) is the first sausage to intersect with the sausage \(A_0^\omega \). Thus, lines 2 and 1 only have the origin as starting point in common and are otherwise vertex-disjoint;
- \(\rhd \):
-
Relation between lines 1 and 3, 4: The connections 3 and 4 are all in \(A_{t_1}^\omega \). The indicator \(J[0,|\omega |]\) ensures that \(A_{t_1}^\omega \) does not intersect any of the intermediate sausages \((A_i^\omega )_{i=1}^{t_1-1}\). Further, 1 bounds the part of \(A_{t_1}^\omega \) that has not been split off as planted animal into 3, indicated by the tip of the arrow in Fig. 11. Thus, 1 is bond-disjoint from 3 and 4;
- \(\rhd \):
-
Relation between lines 3 and 4: Both are part of the sausage \(A_{t_1}^\omega \) and are thus bond-disjoint;
- \(\rhd \):
-
Relation between lines 2 and 3, 4: We know that \(A_{0}^\omega \) and \(A_{t_1}^\omega \) intersect in at least one point. We choose \(w_1=w_1(\omega )\) to be the first intersection point, as defined in Definition 4.4. By this choice the backbones \(b^{A^\omega _0}(0,w_1)\) and \(b^{A^\omega _{t_1}}(x_1,w_1)\) only intersect at \(w_1\).
We define repulsive diagrams to bound such diagrams. As seen for lines 2 and 3, 4, the constraint that the pieces are bond-disjoint is too strong. For this reason, we denote by repulsiveness of a diagram that we can find bond-disjoint paths connecting the corner points of the diagram.
In the following, we define the skeleton of a diagram that encodes the avoidance constraints of the backbone lines, the lengths of the backbone lines and the information whether the start or the end points of a connection is the root of a planted animal. This is formalized as follows:
Definition 4.6
(Mutually avoiding skeleton) Let \(x_0=0\in {\mathbb {Z}}^d\) and \(n\in \{1,2,3,4\}\). For each \(i\in \{1,\ldots ,n\}\), let \(x_i\in {\mathbb {Z}}^d, l_i\in \mathbb {N}\), the index \(j_i\in \{l_i,{\underline{l}}_i\}\), \(s_i\in \{+,-\}\), and let \(\omega ^i\) be a sausage-walk from \(x_{i-1}\) to \(x_i\). We define \(S^{s_1,\ldots ,s_n}_{j_1,\ldots ,j_n}(\omega ^1,\ldots ,\omega ^n)\) to be the indicator that the following holds:
-
(1)
There exists a sequence of paths \((p^i)_{i=1}^n\) such that \(p^i\) is a path from \(x_{i-1}\) to \(x_i\) and \(p^i\) uses only edges in \(\omega ^i\), each path \(p^i\) describes a self-avoiding walk and all paths are pairwise bond-disjoint;
-
(2)
For each \(i\in \{1,\ldots ,n\}\), we can choose \(p^i\) in item (1) such that \(|p^i|\ge l_i\) when \(j_i=l_i\), while \(|p^i|=l_i\) when \(j_i={\underline{l}}_i\);
-
(3)
For each \(i\in \{1,\ldots ,n\}\), the sausages of the walk \((A^{\omega ^i}_j)_{j=0}^{|\omega ^i|}\) do not intersect, so that \(\omega ^i\) describes a LA.
-
(4)
For each \(i\in \{1,\ldots ,n\}\), if \(s_i=+\) then \(A^{\omega ^i}_{0}=\varnothing \), while \(A^{\omega ^i}_{|\omega ^i|}=\varnothing \) when \(s_i=-\).
The skeleton is then the collection \(\{(s_1,\ldots ,s_n), (j_1,\ldots ,j_n), (\omega ^1,\ldots ,\omega ^n)\}\).
We next use this skeleton to define the repulsive bubble, triangle and square diagrams as follows:
Definition 4.7
(Repulsive diagrams) For \(i=1,2,3,4\), let \(x_i\in {\mathbb {Z}}^d,\ l_i\in \mathbb {N},\ j_i\in \{l_i,{\underline{l}}_i\}\), and let \(x_0=0\). We define
Further, for \(i\in \{1,\ldots ,n\}\) and \(x\in {\mathbb {Z}}^d\), we define
Each line of these repulsive diagrams in (4.17), (4.18) and (4.19) are planted animals and can therefore be bounded using the modified two-point functions \({\tilde{G}}_{z}\). The double connection in (4.20) is special, and we will treat this separately in Sect. 4.4 below.
To use the constraints on the lengths of connections arising from loops consisting of at least 4 bonds in the NoBLE, we further define, for \(l\in {\mathbb {N}} \) and \(j\in \{l,{\underline{l}}\}\),
and note that \({\tilde{G}}_{0,z}(x)={\tilde{G}}_{z}(x)\). Using \({\tilde{G}}_{j,z}\), we can obviously bound the repulsive diagrams by ignoring the self-avoidance constraints as
However, as demonstrated by the fourth improvement in Sect. 4.1, the use of repulsiveness improves our numerical bounds drastically, so we do not rely on the numerically worse bounds as in (4.22).
4.4 Bounds on Double Connections
The bound on contributions in which two points are doubly connected, that is, connected by two-bond disjoint paths, is of central interest for LAs. This is especially relevant since a large contribution to the NoBLE lace-expansion coefficients for LAs is given by
Using our notation we bound this \(\mathscr {D}_0(x)\), defined in (4.20).
Let us briefly discuss a numerical aspect of our bounds. Using the ideas described in the previous section, we obtain
We now explain how we can improve this bound by a factor close to 2. This is possible as the two paths that created the double connection are interchangeable, so that (4.24) bounds each possible animal twice.
For the technical derivation of this improvement, we consider yet another split of the LA A given as follows:
-
(i)
Let \(p_1=(b^1_1,b^1_2,\ldots ,b^1_{n})\) and \(p_2(0,x)=(b^2_1,b^2_2,\ldots ,b^2_{m})\) be two bond-disjoint paths between 0 and x in A, that we choose in some unique way for each A, e.g. \(p_1\) is the smallest path in the lexicographic order such that there exists such a bond-disjoint \(p_2\), and then \(p_2\) is the smallest of these bond-disjoint paths, so that \(p_1\) is smaller in lexicographic order than \(p_2\) as we will assume from now on.
-
(ii)
Let \(A_1=B^{A}(0,b^1_{n};p_1)\).
Then,
By symmetry, we could also have performed the split of the animal A according to the path \(p_2\), instead.
We next improve upon this bound. Since the paths \(p_1\) and \(p_2\) are bond-disjoint, we conclude that \({\overline{b}}^1_1={e}_{\iota }\ne {\overline{b}}^2_1={e}_{\kappa }\), with \(\iota <\kappa \) since \(p_1\) is smaller than \(p_2\) in the lexicographic order. Remove the bonds in the paths \(p_1\) and \(p_2\) from A. That divides the LA into at most \(n+m+2\) disjoint LAs containing the vertices of \(p_1\) and \(p_2\). Thus, we now define \(A_0\) to be the LA containing 0, \(A_1=B^{A'}(b^1_1,x;p_1)\setminus A_0\), where \(A'\) is the LA obtained from \(A_2\) by removing \(p_2\) and keeping the parts that do not contain vertices in \(p_2\). Then, by definition of \(B^{A'}(b^1_1,x;p_1)\), \(A_1\) is disjoint from \(p_2\), and the sausage at \({\overline{b}}_1^1\) is trivial in \(A_1\). Finally, define \(A_2=A\setminus (A_0\cup A_1)\) (which contains the bonds in \(p_2\)). Note that, by construction, the sausage of x in \(A_2\) is trivial, so that \(A_2\) is a planted LA, while also the sausage at 0 is trivial. Then,
as the bound (4.25) does not assume anything on the order of the paths. Here, in the first inequality, \(z^2\) corresponds to the weight of the bonds \(b_1^1, b_1^2\), the factor \(g^{\iota }_z\) comes from the LA \(A_0\), the factor \({\tilde{G}}_{z}\) from the LA \(A_1\), and the factor \({\bar{G}}_{z}\) from the LA \(A_2\). Using the same arguments we obtain the factor \(\tfrac{1}{2}{}\) for all other terms in (4.24). In our final numerical bounds, we will drastically improve upon this bound by using the repulsive nature of the two paths \(p_1, p_2\).
5 The Diagrammatic Bounds
In the preceding section we have explained the technical details of our method of bounding LT/LA diagrams. In this section we first combine the repulsive diagrams (4.17)–(4.19), to larger diagrams that we call building blocks. Then, we combine these building blocks to obtain bounds on the NoBLE coefficients. We close this section with an overview of where to find all bounds required for the analysis, as stated in [12, Assumption 4.3].
In Sect. 6 we prove the bounds for \(N=0\) and sketch how the remaining bounds are proven in the example of \(N=1,2\). The rigorous proof of these bounds is tedious and is based on techniques that are relatively standard in lace-expansion analyses. For this reason we omit many details.
5.1 Building Blocks
In this section we combine simple diagrams, defined in (4.17)–(4.19), to larger diagrams, that we call building blocks. These building blocks are designed to encode the following information:
- \(\rhd \):
-
the repulsiveness of the paths involved;
- \(\rhd \):
-
the lengths of lines shared by two loops;
- \(\rhd \):
-
the role of the lines shared by two loops, meaning whether it is part of the backbone or not, and, if so, how the backbone is connected to the line in question.
We encode the repulsiveness by defining the blocks using the repulsive diagram (4.17)–(4.19). In the following we discuss the other two features.
Aim: Encoding Backbone-Paths. In Fig. 11, we have shown an example of the diagram contributing to \(\Xi ^{\scriptscriptstyle ( \text { 4})}_z\). However, the form shown in Fig. 11 is only one of eight possible patterns that the backbone can form. These patterns arise by the different cases for the underlying lace, i.e. whether \(s_{i+1}=t_i\) or \(s_{i+1}<t_i\) for \(i=1,2,3\). In Fig. 12 we show all the possible backbone patterns for the \(\Xi ^{{\scriptscriptstyle ( \text { 4})}}\)-diagrams. One function of the building block will be to encode all possible patterns at once, so as to encode the roles that the shared lines play compared to the backbone.
Picture of all possible \(\Xi ^{{\scriptscriptstyle ( \text { 4})}}_z\) diagrams. The backbone is marked by a thick line and the four first intersection points are marked as dots. The leftmost diagram on the second row corresponds to the diagram shown in Fig. 11
Aim: Encoding of the Line Lengths. When creating a bound on the NoBLE coefficients we want to make full use of all the avoidance constraints of a sausage-walk, as well as the fact that any closed loop consists of at least four bonds. To be able to do this, we consider different cases for the lengths of paths that are shared by two squares. Here, the length of a path is given by the number of bonds it uses.
Our Solution. We use the indices \(l,m\in \{-2,-1,0,1,2\}\) to encode the information of the length and role of a shared line. We explain their meaning in the example of the diagram given in Fig. 13.
As indicated in Figs. 11, 12 and 13, we always draw the diagrams in such a way that the origin is on the left side and the first piece of the sausage-walk from \({\underline{b}}_0\) to \({\underline{b}}_{s_2}\) is the lower line of the first square. A positive index \(m_i\) indicates that the backbone ends on the upper part of a piece of the diagram. Interactions between neighboring squares will be particularly important, in which case there will be two indices, for example in the open square building block \(A^{m_{i-1},m_i}\) defined below (and which should not be confused with walks sausages denoted by \(A^{\omega ^i}_j\)). In this case, \(m_{i-1}>0\) indicates that the backbone in the \((i-1)\)st square starts on the upper part of the diagram, while \(m_i>0\) indicates that the backbone ends on the upper part of a piece of the diagram. Further, by \(|m_i|=1\), we denote that the vertical line consists of exactly one bond and \(|m_i|=2\) denotes that the vertical line consists of at least two bonds. If \(m_i=0\), then the vertical line is trivial, i.e., it consists of no bonds. In the case that \(m_i=0\), we draw the following piece of the backbone on the lower part of the following square.
Informal Definition of Building Blocks. In this section, we informally define the diagrams, also called building blocks, that we use to bound the NoBLE coefficients. The precise properties of the building blocks originate from the properties of the NoBLE coefficients, as we will see when we bound the coefficients in Sect. 6. The list below consists of 9 basic building blocks:
-
(i.)
Open square \(A^{l,m}\). We use this building block to bound the intermediate pieces of the diagrams appearing in the NoBLE coefficients. It consists of an open square, with 4 of the 5 vertices fixed and one being summed over.

We label the vertices in the diagram \(A^{l,m}\) such that u is the starting vertex and x is the ending vertex of the backbone. The indices l, m identify the lengths of the connections between u, v and x, y, respectively, i.e., the number of bonds in these connections. For example: If \(m=0\) then \(x=y\). If \(|m|=1\) then x and y are direct neighbors and are directly connected. The case where \(|m|=2\) summarizes all the other cases. A positive index l, m indicates that the backbone starts/ends at the top. This means that if \(lm\ge 0\), then the connection from x to y is not part of the backbone. The horizontal parts of the backbones (i.e., the paths from u to x or from u to y) are always non-trivial, in that they use at least one bond. If the backbone \(b^A(u,x)\) consists of only one bond, then we know that
 . Closing the diagram, by including any path from u to v of length l, always creates a diagram with at least four bonds.
. Closing the diagram, by including any path from u to v of length l, always creates a diagram with at least four bonds. -
(ii.)
Double open triangle \({\bar{A}}^{l,m}\).

This diagram follows the same rules as the open square \(A^{l,m}\), the difference being that the connection from x to y does not contribute (i.e., that line is absent indicating that it is used in another building block). We only draw the example with \(l,m>0\). The role of l and m in \({\bar{A}}^{l,m}\) is the same as in \(A^{l,m}\).
-
(iii.)
Weighted open triangle \(C^{l,m}\), as indicated in Fig. 14.
-
(iv.)
Closed fundamental block \(P^{{\scriptscriptstyle ( \text { 1})},m}.\)
This diagram is used to bound the first square of \(\Xi ^{{\scriptscriptstyle ( \text { N})}}_z\) and for \(m>0\) has the shape given in Fig. 15.
Each triangle, square and pentagon consists of at least four bonds. The first diagram characterizes the case where the first step of the backbone starts at the origin, i.e., \({\underline{b}}_1^\omega =0\). In the following, we use \(u=\bar{b}_1^\omega \) to denote the first step of the backbone. Note that only \({\underline{b}}_1^\omega = 0\) contributes for LT. If the backbone between u and x consists of only one step, then
 . The pieces of the backbone \(b^A(u,x)\), \(b^A(0,y)\) and \(b^A(x,y)\), respectively, are non-trivial. Note that the left diagram is the same diagram as \(A^{0,m}(0,0,x,y)\).
. The pieces of the backbone \(b^A(u,x)\), \(b^A(0,y)\) and \(b^A(x,y)\), respectively, are non-trivial. Note that the left diagram is the same diagram as \(A^{0,m}(0,0,x,y)\). -
(v.)
Open fundamental block \({\bar{P}}^{{\scriptscriptstyle ( \text { 1})},m}.\) This diagram corresponds to the closed fundamental block \(P^{{\scriptscriptstyle ( \text { 1})},m}\), in which the connection from x to y does not contribute (but we keep information about its length using the index m).
-
(vi.)
Weighted fundamental block \(\Delta ^{\text {start},m}\). This diagram corresponds to the open fundamental block \({\bar{P}}^{{\scriptscriptstyle ( \text { 1})},m}\), where the lower connection is weighted by its displacement, i.e., \(|x|^2\) for \(m\le 0\) and \(|y|^2\) for \(m\ge 0\).
-
(vii.)
Weighted terminal block \(\Delta ^{\text{ end },m}\). This diagram is defined by \(\Delta ^{\text{ end },m}(u,v,x)=C^{m,0}(u,v,x,x)\) and is used to bound the last square of \(\Xi ^{{\scriptscriptstyle ( \text { N})}}_z\) and \(\Xi ^{{\scriptscriptstyle ( \text { N})},\iota }_z\).
-
(viii.)
Iota-fundamental block \(P^{{\scriptscriptstyle ( \text { 1})},\iota ,m}.\) This diagram is used to bound the first square of \(\Xi ^{{\scriptscriptstyle ( \text { N})},\iota }_z\) and has the following structure for \(m<0\):

This diagram is similar to \(P^{{\scriptscriptstyle ( \text { 1})},m}\). The sausage-walks that we bound with this diagram have the property that either \({e}_{\iota }\) is part of the first sausage or that \({\underline{b}}_1^\omega \) ends in \({e}_{\iota }\). If \({e}_{\iota }\) is in the first sausage, then we extend the idea of (4.15). We identify the last point v that the double connection 0 to \({\underline{b}}_1\) and a connection 0 to w share. Then, we identify the last common point u of the connection 0 to \({e}_{\iota }\) to the rest. This point u could be on all possible connections 0 to \({\underline{b}}_1\), 0 to v, \({\underline{b}}_1\) to v as well as v to w, as indicated in the figure above.
-
(ix.)
Weighted iota-fundamental block
 . These diagrams have the same shape as \(P^{{\scriptscriptstyle ( \text { 1})},\iota ,m}\), but the connection from x to y does not contribute. Further,
. These diagrams have the same shape as \(P^{{\scriptscriptstyle ( \text { 1})},\iota ,m}\), but the connection from x to y does not contribute. Further,  is weighted by a factor \(|x|^2\) and
is weighted by a factor \(|x|^2\) and  by a factor \(|x-{e}_{\iota }|^2\) for \(m\le 0\).
by a factor \(|x-{e}_{\iota }|^2\) for \(m\le 0\).
In this version we omit the detailed definition of these diagrams, as they do not yield additional insight and are rather lengthly. Their definition is given in the appendix of the extended version [14].
Elements of the Bounds. Here we define the quantities that we use to state the bounds on the NoBLE coefficients. In the following, we define the vectors \(\mathbf {P},\mathbf {P}^{\iota },\mathbf {E},\mathbf {\Delta }^\mathrm{{start}},\mathbf {\Delta }^\mathrm{{end}},\mathbf {\Delta }^{\iota }\in \mathbb {R}^{5}\) and the matrices \({{{\bar{\mathbf{A}}}}},\mathbf{A},\mathbf{C}\in \mathbb {R}^{5\times 5}\) by their entries. For convenience, we use \(\{-2,-1,0,1,2\}\) as indices for the entries of the vectors and matrices. Let
and
Using the bootstrap assumption \(f_i(z)<\Gamma _i\) we can compute explicit numerical bound for each of these quantities. We use these quantities to formulate the bounds on the NoBLE coefficients.
5.2 The Bounds
Now we state our bounds on the NoBLE coefficients. For this, we use the notation \(\mathbbm {1}^{a}\), as used in (1.19), where \(\mathbbm {1}^{a}\) is 1 in bounds for LAs and 0 in bounds for LTs. We have to be especially careful in our bounds for \(N=0\) and \(N=1\), which turn out to be the major contributions to the NoBLE coefficients. Therefore, we distinguish between the bounds for \(N=0\), \(N=1\) and \(N\ge 2\). We start by formulating the bounds on \(\Xi ^{{\scriptscriptstyle ( \text { 0})}}\) and \(\Psi ^{{\scriptscriptstyle ( \text { 0})},\kappa }\):
Lemma 5.1
(Bounds on \(\Xi ^{{\scriptscriptstyle ( \text { 0})}}\) and \(\Psi ^{{\scriptscriptstyle ( \text { 0})},\kappa }\)) Let \(0\le z<z_c\). Then,
and
Further,
We continue by formulating the bounds on \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }\) and \(\Pi ^{{\scriptscriptstyle ( \text { 0})},\iota ,\kappa }\). To state the bound on \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }\) and the remainder of the split  and
and  , we use the abbreviations \(\alpha _{n,m}\), \(\beta _{n}\) and \(\gamma _{n}\), that will only be used in this lemma, and which, for \(n,m\in \{0,1,2\}\), are given by
, we use the abbreviations \(\alpha _{n,m}\), \(\beta _{n}\) and \(\gamma _{n}\), that will only be used in this lemma, and which, for \(n,m\in \{0,1,2\}\), are given by
Then the bounds on \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }\) and \(\Pi ^{{\scriptscriptstyle ( \text { 0})},\iota ,\kappa }\) read as follows:
Lemma 5.2
(Bounds on \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }\) and \(\Pi ^{{\scriptscriptstyle ( \text { 0})},\iota ,\kappa }\)) Let \(0\le z< z_c\). Then,
The remainder terms of the split are bounded in a similar way as
The explicit terms of the splits are bounded by
The terms in the split of \(\Pi ^{{\scriptscriptstyle ( \text { 0})},\iota ,\kappa }_z\) satisfy
We continue with the bounds for \(N=1\):
Lemma 5.3
(Bounds on the coefficients for \(N=1\)) Let \(0\le z< z_c\). Then,
and
Further, \(\Xi ^{{\scriptscriptstyle ( \text { 1})},\iota }_z\) satisfies
We continue with the bounds for \(N\ge 2\):
Proposition 5.4
(Bounds on the NoBLE coefficients for \(N\ge 2\)) Let \(0\le z<z_c\) and \(N\ge 2\). Then,
Having stated our main bounds on the NoBLE coefficients, we next state some additional bounds that improve the numerical accuracy of our method:
Lemma 5.5
(Bounds on differences) Let \(0\le z<z_c\). Then,
and
Further,
5.3 Summary of the Bounds
In this section, we give an overview of where to find the bounds stated in [12, Assumption 4.3]. We emphasize that, next to the diagrammatic bounds proven in this document, [12, Assumption 4.3] also requires a method to conclude numerical bounds. In [12, Sect. 5], we describe this method. In [9], we provide the source code that computes the numerical bounds. This source code allows us to apply the analysis of [12] to obtain our mean-field results. We give a summary of where to find most bounds in Table 3.
In the following, we discuss some bounds that are not stated in Table 3. These are also required for the analysis, but are in general very easy to obtain. We start by bounding \({\bar{\mu }}_z/\mu _z\), as formulated in [12, first inequality in (4.30) in Assumption 4.3],
Regarding \(\beta _{\scriptscriptstyle \mu }\), we remark that by the definition of \(z_I\) in (3.55), for each \(z>z_I\),
as formulated in [12, second inequality in (4.30) in Assumption 4.3]. [12, Assumption 4.3] also states lower bonds on \(\Psi ^{\scriptscriptstyle ( \text { 0})}\) and \(\Pi ^{\scriptscriptstyle ( \text { 0})}\), which we could obtain using simple combinatorics. We numerically found that the benefit of these extra bounds is minimal, so that we simply use the trivial lower bounds \(\underline{\beta }_{\scriptscriptstyle \Psi }^{\scriptscriptstyle ( \text { 0})} = \underline{\beta }_{\scriptscriptstyle \sum \Pi }^{\scriptscriptstyle ( \text { 1})}=\underline{\beta }_{ \scriptscriptstyle \sum \Pi _\alpha }^{\scriptscriptstyle ( \text { 0})}=0\) for these coefficients, which are by definition non-negative.
Further, we assume that the geometric series bounding our NoBLE coefficients converge, which follows if their base is smaller than one as formulated in [12, (4.34) in Assumption 4.3], i.e.,
For example, this shows that the matrix inverse in (2.12) is well defined. Finally, the inequalities \({\underline{\beta }}_{\scriptscriptstyle \alpha ,F}-\underline{\beta }_{\scriptscriptstyle \Delta R,F}>0\) and \({\underline{\beta }}_{\scriptscriptstyle c,\Phi }-\beta _{\scriptscriptstyle |\alpha ,\Phi |}-\beta _{{\scriptscriptstyle R,\Phi }}>0\) guarantee that the numerator and denominator of \({\hat{G}}_z(k)\) in (2.12) are non-negative, see [12, one-but-last sentence of Assumption 2.7]. These are numerical conditions that are verified explicitly in the Mathematica notebooks. These conditions are relatively weak, in the sense that, empirically, we observe that the bootstrap analysis, which in particular includes an improvement of bounds, is much more likely to fail.
6 Proof of the Bounds on the NoBLE Coefficients
In this section, we explain how the bounds stated in the preceding section are proven. In Sect. 4, we have already explained the basic idea of the bounds. We start by proving the bounds on the relatively simple coefficients arising for \(N=0\) and \(N=1\). Then, we explain how the coefficients for general \(N\ge 2\) are bounded. After this, we discuss bounds on the difference of coefficients.
6.1 Proof of Bounds for \(N=0\)
Here we prove Lemmas 5.1 and 5.2. For \(N=0\), the coefficients arise from LAs in which 0 and x are doubly connected, see (3.24). In Sect. 4.4 we have explained how to bound the contribution of such LAs, so we add here only the missing details.
Proof of Lemma 5.1
In Sect. 4.4 we have already proven the bound on \(\Xi ^{{\scriptscriptstyle ( \text { 0})}}_{z}\). From \(\Xi ^{{\scriptscriptstyle ( \text { 0})}}_{{\scriptscriptstyle R},z}\), we have extracted the contributions in which 0 and x are connected by a direct bond, see (3.36). Considering this, the bounds (5.6) and (5.9) follow directly. The only difference between \(\Xi ^{{\scriptscriptstyle ( \text { 0})}}_{{\scriptscriptstyle R},z}\) and \(\Psi ^{{\scriptscriptstyle ( \text { 0})},\kappa }_{{\scriptscriptstyle R, II},z}\) is that  for \(\Psi ^{{\scriptscriptstyle ( \text { 0})},\kappa }_{{\scriptscriptstyle R, II},z}\). Since each double connection requires at least two neighbors of x to be part of A, the spatial symmetry of the LAs implies that
for \(\Psi ^{{\scriptscriptstyle ( \text { 0})},\kappa }_{{\scriptscriptstyle R, II},z}\). Since each double connection requires at least two neighbors of x to be part of A, the spatial symmetry of the LAs implies that
which implies (5.7) and (5.10).
The coefficient \(\Psi ^{{\scriptscriptstyle ( \text { 0})},\kappa }_{{\scriptscriptstyle R, I},z}(x)\) was created by extracting the shortest contributions with \(x={e}_{\kappa }\) and x’s that are neighbors of \({e}_{\kappa }\). The contribution of the remaining \((2d-1)\) neighbors of the origin is bounded using \(\mathscr {B}_{{\underline{1}},3}({e}_{1},0)\). For all other x, i.e., those with \(|x|>1\), we use \(\Psi ^{{\scriptscriptstyle ( \text { 0})},\kappa }_{{\scriptscriptstyle R, II},z}(x)\le \Psi ^{{\scriptscriptstyle ( \text { 0})},\kappa }_{{\scriptscriptstyle R, I},z}(x)\) to conclude the bounds stated in (5.11).
In (5.12), we bound the contribution due to all neighbors of the origin by the first term. The contribution due to all other x are bounded by the second term. Regarding the neighbors \(x={e}_{\iota }\) of the origin, with \(\iota \in \{\pm 1,\ldots ,\pm d\}\), we note that
Summing over \(\iota \) yields the stated factor 4d. For the other x, we know that any path to x contains at least two bonds. To be able to use a symmetry argument, we ignore that we have extracted terms and as well as the condition  , to obtain the simple bound
, to obtain the simple bound
Then, we use that \(|x-{e}_{\kappa }|^2=(|x|^2 -2x_\kappa +1)\) and that the term involving \(-2x_\kappa \) sums to zero by symmetry, to obtain
which is the second term in (5.12). This proves (5.12), and completes the proof of Lemma 5.1. \(\square \)
Proof of Lemma 5.2
By definition,
For LTs, this simplifies to
For LAs we recall that we have bounded such animals already between (4.14) and (4.15).
We improve these bounds by using repulsive diagrams (recall Sect. 4.3) and by considering four cases for the point u, where u is the summand appearing in (4.14), thus yielding the bound \(\alpha _{1,1}\) (see (5.13)). Let us explain the four cases for u:
(a) For \(u=0\), the diagram is given by a double connection from 0 to x and a simple path from 0 to \({e}_{\iota }\) that we bound by
The first term is given explicitly in (5.16) and the second term corresponds to the first term of \(\alpha _{1,1}\).
(b) For \(u={e}_{\iota }\), the point \({e}_{\iota }\) is on the double connection between 0 and x. For \(x={e}_{\iota }\), we have a simple double connection to \({e}_{\iota }\), otherwise a repulsive triangle, as stated in the second and third term of \(\alpha _{1,1}\).
(c) In the contributions in which  we find a double connection between 0 and x, bounded by \(\mathscr {D}_{1}(x,0)\), and a connection from x to \({e}_{\iota }\), bounded by \({\tilde{G}}_{m,z}(x-{e}_{\iota })\). We improve this bound slightly using the parity of the lattice: If 0 and x are directly connected, then the length of the connection between x to \({e}_{\iota }\) is at least 2.
we find a double connection between 0 and x, bounded by \(\mathscr {D}_{1}(x,0)\), and a connection from x to \({e}_{\iota }\), bounded by \({\tilde{G}}_{m,z}(x-{e}_{\iota })\). We improve this bound slightly using the parity of the lattice: If 0 and x are directly connected, then the length of the connection between x to \({e}_{\iota }\) is at least 2.
(d) In the remaining contributions, we have that \(u\ne \{0,x,{e}_{\iota }\}\), so that these LAs can be bounded by
which corresponds to the last term of \(\alpha _{1,1}\). This completes the proof of (5.16).
The diagrams with the additional weights \(|x|^2\) and \(|x-{e}_{\iota }|^2\) are bounded in a similar manner. As the numerical bounds, using the bootstrap function \(f_3\), require a \(G_z\) to carry the spatial weight, we express the bounds using two-point functions instead of repulsive diagrams. For the weight \(|x-{e}_{\iota }|^2\), two additional steps are made: Firstly, for \(u=0\ne x\) we first split the weights using symmetry, as shown in (6.4), and then bound the two arising terms. This leads to the first line of \(\gamma _1\) in (5.15). Secondly, for \(u\ne \{0,{e}_{\iota },x\}\), we use that \(|x-{e}_{\iota }|^2\le 2(|x|^2+1)\), see [12, (2.24)], and bound the arising terms individually. This completes the proofs of (5.17) and (5.18).
For the bounds on \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }_{{\scriptscriptstyle R, I},z}\) and \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }_{{\scriptscriptstyle R, II},z}\) stated in (5.19)–(5.20), we review which terms have been extracted from \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }_z(x)\) to yield \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }_{{\scriptscriptstyle R, I},z}\) and \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }_{{\scriptscriptstyle R, II},z}\). For \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }_{{\scriptscriptstyle R, II},z}(x)\), the LAs in which x is directly connected to the origin have been removed. For this reason, in \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }_{{\scriptscriptstyle R, II},z}\) all paths from 0 to x have a length of at least 2 instead of 1. This is expressed by the subscripts n of \(\alpha _{n,m}\) and \(\beta _{n}\). To obtain \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }_{{\scriptscriptstyle R, I},z}(x)\) from \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }_z(x)\), we have extracted all LAs in which x is directly connected to \({e}_{\iota }\). This means that in \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }_{{\scriptscriptstyle R, I},z}(x)\), the path from \({e}_{\iota }\) to x in contributing LAs have length at least 2. The bounds (5.19) and (5.20) are created by repeating the consideration of cases for u, as given above for the bound on \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }_z(x)\), while keeping these additional restrictions.
We continue with the bounds on \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }_{\alpha ,{\scriptscriptstyle I},z}\) and \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }_{\alpha ,{\scriptscriptstyle II},z}\) in (5.21)–(5.23). Note that for LTs, most of these terms are zero due to the lack of double connections, so we restrict to LAs. Recall (3.34), as well as (3.50)–(3.51).
By their definitions in (3.39) and (3.40),
which proves (5.21). To obtain the bound in (5.22), we again use (3.39), and remark that, for \(x\ne 0\) with \(|x-{e}_{\iota }|^2=1\), we can write \(x={e}_{\kappa }+{e}_{\iota }\) with \(\kappa \ne -\iota \) to get
Thus, \({e}_{\kappa }+{e}_{\iota }\) and \({e}_{\iota }\) are directly connected in the LA. We distinguish between the case where \({e}_{\iota }\) is on the double connection or not to obtain
Summing over all neighbors \({e}_{\kappa }+{e}_{\iota }\) of \({e}_{\iota }\), and also using that the contribution of \(\kappa =-\iota \) is \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }_{\alpha ,{\scriptscriptstyle I},z}(0)=G_z({e}_{\iota })\), proves (5.22).
For \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }_{\alpha ,{\scriptscriptstyle II},z}({e}_{\kappa })\), we recall (3.40), and consider \(\kappa \ne \iota \), distinguish between the cases where \({e}_{\iota }\) is part of the double connection from 0 to \({e}_{\kappa }\) or not. For this, let u be the first point that any path between 0 and \({e}_{\iota }\), and the path between \({e}_{\kappa }\) and \({e}_{\iota }\), share. We split between \(u=0, {e}_{\kappa },{e}_{\iota }\) and \(u\not \in \{0,{e}_{\kappa }, {e}_{\iota }\}\), to obtain
Summing this over all neighbors \({e}_{\kappa }\) of the origin, and using that the contribution for \(\kappa =\iota \) can be bounded by \(\frac{\mathbbm {1}^{a}}{g_z}\mathscr {D}_{1}({e}_{\iota })\), proves (5.23).
For the bounds on \(\Pi ^{{\scriptscriptstyle ( \text { 0})},\iota ,\kappa }_{z}, \Pi ^{{\scriptscriptstyle ( \text { 0})},\iota ,\kappa }_{\alpha ,z}\) and \(\Pi ^{{\scriptscriptstyle ( \text { 0})},\iota ,\kappa }_{{\scriptscriptstyle R},z}\) stated in (5.24)–(5.26), it is useful to write out the definition of \(\Pi ^{{\scriptscriptstyle ( \text { 0})},\iota ,\kappa }_{z}\) in (3.28), and simplify it for the special case \(N=0\). This leads to

Using the split \(\Pi ^{{\scriptscriptstyle ( \text { 0})},\iota ,\kappa }_{\alpha ,z}\) (see (3.41)), we extract from this the contributions where \(x={e}_{\iota }\), as well as those with \(x={e}_{\iota }+{e}_{\kappa }\) in which the edge \(({e}_{\iota },{e}_{\iota }+{e}_{\kappa })\) is in the LA. For \(x={e}_{\iota }\), we see that

as the LAs contain a simple double connection to a neighbor of the origin. Summing this over \(\kappa \) proves (5.24). The bounds (5.25) and (5.26) basically follow from the fact that \(\Pi ^{{\scriptscriptstyle ( \text { 0})},\iota ,\kappa }_z(x)\le zg_z\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }_z(x)\), see (3.72). To understand (5.25) we compare the bound with (5.16). When summing over \(\iota \) for \(x=0\), \(\iota =-\kappa \) does not contribute explaining the factor \((2d-1)\). Further, we have extracted the case that \(x={e}_{\iota }\), thus we can use \(\alpha _{1,1}\) instead of \(\alpha _{1,0}\) for this bound.
For (5.26), we need to redistribute the weights. We write

since \(\Pi ^{{\scriptscriptstyle ( \text { 0})},\iota ,\kappa }_z(x)\le zg_z\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }_z(x)\). The first contribution is bounded by \(2(2d)^2zg_z G_z({e}_{\iota })\). We use (5.18) for the \(|x-{e}_{\iota }|^2\) contribution. We further use (5.16) (without the term created by \(x\in \{0,{e}_{\iota }\}\)) to obtain a bound \((2d)^2zg_z\alpha _{1,1}\) on the contribution due to \(+1\). Finally, \(\sum _{\iota } \Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }_z(x)\) is symmetric, so that the \(x_\kappa \) contribution vanishes, while the \(\delta _{\iota ,\kappa }\) contribution gives  , which can be taken together with the \(+1\) contribution using (5.16). \(\square \)
, which can be taken together with the \(+1\) contribution using (5.16). \(\square \)
6.2 Proof of Bounds for \(N=1\)
In this section we explain how we prove the bounds stated in Lemma 5.3. We explain in detail how we obtain the bounds on \(\Xi ^{{\scriptscriptstyle ( \text { 1})}}_{z}\), stated in (5.27) and (5.31), and then discuss how to modify the statements to derive the bounds on the other coefficients.
The first step to obtain the bounds are the following x-space bounds:
Lemma 6.1
(Pointwise bounds) For all \(x\in {\mathbb {Z}}^d\), \(\iota \) and \(0\le z\le z_c\),
We define \(P^{{\scriptscriptstyle ( \text { N})},0}\) in Table 4. The formal definition of \(P^{{\scriptscriptstyle ( \text { 1})},\iota ,0}\) is provided in Appendix C.2.2 of the extended version [14].
Proof
The coefficients that we consider here are defined by sausage-walks for which only the first and last sausage intersect. In Sect. 4.1, we have discussed how to bound \(\Xi ^{{\scriptscriptstyle ( \text { 1})}}_z(x)\) for LTs and later obtained the bound (4.16) for LAs. Using that all connections are repulsive, we can improve (4.16) to
As discussed in the third improvement in Sect. 4.1, each loop in this diagram consists of at least four bonds, and we have that  . All this is implied by the non-backtracking condition in the NoBLE. We make use of this by considering some special cases for b and u, as summarized in Table 4, which improves the bound to obtain (5.27):
. All this is implied by the non-backtracking condition in the NoBLE. We make use of this by considering some special cases for b and u, as summarized in Table 4, which improves the bound to obtain (5.27):
Bounds on \(\Xi ^{{\scriptscriptstyle ( \text { 1})},\iota }\). For \(\Xi ^{{\scriptscriptstyle ( \text { 1})},\iota }\), we know that either \({\overline{b}}_1={e}_{\iota }\) or \({e}_{\iota }\in A_0^\omega \) as enforced by the indicator \(\mathbbm {1}_\iota (\omega )\) defined in (3.16). To create a bound we consider 16 possible forms of the diagram and then bound each of them separately. Then, we define \(P^{{\scriptscriptstyle ( \text { 1})},\iota ,0}_{z}(x,x)\), as well as \(\Delta ^{\iota ,{\scriptscriptstyle I},0}\) and \(\Delta ^{\iota ,{\scriptscriptstyle II},0}\), as the sum of these 16 individual diagrams. The necessary derivation and definitions are only given in the extended version of this article.
This completes the proof of Lemma 6.1. \(\square \)
We continue with the proof of Lemma 5.3:
Proof of Lemma 5.3. The bounds in (5.27) and (5.33) follow by summing the pointwise bounds in Lemma 6.1 over x.
Weighted Diagrams for \(\Xi _z^{{\scriptscriptstyle ( \text { 1})}}(x)\). Now we derive a bound for the weighted diagram \(|x|^2\Xi _z^{{\scriptscriptstyle ( \text { 1})}}(x)\). Below (4.16), we have argued that we can split the sausage-walk such that (only) one line is bounded by \({\bar{G}}_z\). Multiplying such a bound with \(|x|^2\) we obtain
For the second term, which is not present for LTs, we have the problem that there is no single line connecting 0 and x to which we can allocate the weight \(|x|^2\). This is problematic as the bootstrap function \(f_3\) only allows us to bound \(|x|^2{\bar{G}}_z(x)\). For this reason, we go back to an earlier step in the bounding procedure. We first apply \(|x|^2\le 2 |{\underline{b}}_1|^2+2 |x-{\underline{b}}_1|^2\) when still summing over the sausage-walks. Only then we split the sausages and choose which line is bounded by \({\bar{G}}_z\). This yields the bound
This term can be bounded using our bootstrap functions. We improve this bound using three ideas, that we now explain. To improve the term in (6.20), we consider the cases \(w=0\), \(w=x\) and \(w\not \in \{0,x\}\) to obtain the bound
To improve (6.22) we use a total of five special cases for u, w and \({\underline{b}}_1\) and will omit the details here.
The third idea is to use symmetry, of which we provide an example when \(u={\underline{b}}_1\) and \(x=y+u\). In this case, we split the weight using \(|u+y|^2=|y|^2+|u|^2+2\sum _{i=1}^d u_iy_i\) and conclude a bound of the form
Here, the mixed weights \(u_iy_i\) cancel since the bubble to u, as well as the triangle to y, are symmetric in each coordinate. This saves us a factor 2, for \(u={\underline{b}}_1\) when compared to (6.22). The building block \((\mathbf {\Delta }^\mathrm{{start}})_0\) is defined as the sum of these terms. This proves (5.31).
Bounds on \(\Xi ^{{\scriptscriptstyle ( \text { 1})}}_{{\scriptscriptstyle R},z},\Psi ^{{\scriptscriptstyle ( \text { 1})}}_{{\scriptscriptstyle R, I},z},\Psi ^{{\scriptscriptstyle ( \text { 1})}}_{{\scriptscriptstyle R, I},z}\). These coefficients have been obtained by extracting some explicit contributions from \(\Xi ^{{\scriptscriptstyle ( \text { 1})}}_{z}\) resulting in very similar bounds as for \(\Xi ^{{\scriptscriptstyle ( \text { 1})}}_{{\scriptscriptstyle R},z}\). The diagrammatic representation of these coefficients are all similar to \(P^{{\scriptscriptstyle ( \text { 1})},0}_{z}\) depicted in Fig. 15. In all cases we have extracted contributions to the left square of Fig. 15, which is bounded by \(A^{0,0}\). We derive the bounds in (5.28), (5.29) and (5.30) by removing the contribution \(A^{0,0}\), and then add the parts of this square that are actually required.
For \(\Xi ^{{\scriptscriptstyle ( \text { 1})}}_{{\scriptscriptstyle R},z}\) and \(\Psi ^{{\scriptscriptstyle ( \text { 1})}}_{{\scriptscriptstyle R, II},z}\), we have extracted the case \(x=0\), as well as all contributions in which 0 and x are directly connection via a bond, see (3.42). For this reason, all connections from 0 to x consist of at least 2 steps, which is reflected in (5.28) and (5.30).
For \(\Psi ^{{\scriptscriptstyle ( \text { 1})}}_{{\scriptscriptstyle R, I},z}\), we have only extracted the contribution of \(x=0\) and \(x={e}_{\kappa }\). Thus, when comparing (5.29) and (5.30), we see that we have to add to (5.29) also the contribution of points \(x\ne {e}_{\kappa }\) that can be reached within one step.
Regarding the weighted bounds stated in (5.31)–(5.32), it (numerically) turns out that we cannot benefit from the fact that we have extracted terms. For this reason we simply note that \(\Xi ^{{\scriptscriptstyle ( \text { 1})}}_{{\scriptscriptstyle R},z}(x)\le \Xi ^{{\scriptscriptstyle ( \text { 1})}}_{z}(x)\) and \(\max \{\Psi ^{{\scriptscriptstyle ( \text { 1})}}_{{\scriptscriptstyle R, I},z}(x),\Psi ^{{\scriptscriptstyle ( \text { 1})}}_{{\scriptscriptstyle R, II},z}(x)\}\le \Xi ^{{\scriptscriptstyle ( \text { 1})}}_{z}(x)\), and apply the original bounds for these terms.
Weighted Bounds on \(\Xi ^{{\scriptscriptstyle ( \text { 1})}, \iota }_{z}\). The bounds on the weighted diagrams of \(\Xi ^{{\scriptscriptstyle ( \text { 1})}, \iota }_{z}\) in (5.34)–(5.35) follow by carefully analysing the weighted version of \(P^{{\scriptscriptstyle ( \text { 1})},\iota ,0}_{z}(x,x)\), which appear as sums of 32 individual diagrams. The necessary derivation and definitions are only given in the extended version of this article.
The above bounds sketch the proof of Lemma 5.3. \(\square \)
6.3 Proof of Bounds for \(N\ge 2\)
In this section we will explain how we bound the NoBLE coefficients with \(N\ge 2\) and thereby complete the proof of Proposition 5.4.
Decomposition of spatial Weights. We bound the diagram for \(N\ge 2\) by splitting the diagram into individual pieces, as seen in Fig. 16. When a spatial weight \(|x|^2\) is present, we need to distribute it along the connections of the diagram, as already seen in the case of \(\Xi ^{{\scriptscriptstyle ( \text { 1})}}\) in (6.21)–(6.22). For this, we define \((x_i)_i\) as displayed in Fig. 17 and use
After applying (6.24) we bound each term of the sum with its partial spatial weight \(|x_i|^2\) individually. This will be done in (6.35) below. As the partial spatial weight depends on the sausage/rib-walk and lace, writing \(|x_i|^2\Xi ^{{\scriptscriptstyle ( \text { N})}}_{z}(x)\) is not meaningful. To fix this technicality, for \(N\ge 2\) and \(i=1,\ldots ,N\), we define
with \(|x_i(\omega ,L)|^2\) as shown in Fig. 17 in the example where \(N=4\). We define \(\Xi ^{{\scriptscriptstyle ( \text { N})},\iota }_z(x,\Delta _i)\) accordingly with the additional indicator \(\mathbbm {1}_{\iota }(\omega )\) (compare (3.25) and (3.26)). It is possible to give the formal definition of \(x_i(\omega ,L)\) using the lace \(L={s_1t_1,\ldots , s_Nt_N}\), the backbone \((b^\omega _j)_{j=1}^{|\omega |}\), and the sausages that are being split \(S_{s_i}^\omega \), \(S_{t_i}^\omega \). As this would not be very informative, we omit this and just refer to Fig. 17 instead. Figure 17 allows for a straightforward adaptation for all \(N\ge 3\). Then we obtain, using (6.24),
Construction of the Bounding Diagram. We combine the building blocks, see Sect. 5.1, to construct the bounds on the NoBLE coefficients: We recursively define
for \(N\ge 2\) and \(m\in \{-2,-1,\ldots ,2\}\). The formal definition of \(P^{{\scriptscriptstyle ( \text { 1})},m}\) and \(P^{{\scriptscriptstyle ( \text { 1})},\iota ,m}\) are only provided in Appendix C of the extended version [14]. Here we only give the definition of \(P^{{\scriptscriptstyle ( \text { N})},0}\) in Fig. 4 as an example.
Using these constructs, we bound the coefficients as follows:
Lemma 6.2
(Pointwise bounds) For all \(x\in {\mathbb {Z}}^d\), \(\iota \) and \(0\le z\le z_c\), and \(N\ge 2\),
Further, for \(N,M\ge 1\),
The same bounds hold for \(\Xi ^{{\scriptscriptstyle ( \text { N})},\iota }\), when \(P^{{\scriptscriptstyle ( \text { N-1})},l}\) and \(\Delta ^{\mathrm{start},l} \) are replaced by \(P^{{\scriptscriptstyle ( \text { N-1})},\iota ,l}\) and \(\Delta ^{\iota ,{\scriptscriptstyle I},l} \) or \(\Delta ^{\iota ,{\scriptscriptstyle II},l}\), respectively.
Combining all these bounds we are able to bound the weighted diagrams. First, we split the weight \(|x|^2\) using (6.24), as formulated in (6.26). Then, we use the bounds in Lemma 6.2 to obtain

which implies the bound stated in (5.37).
Let us highlight once more how crucial the order is in which we create our bounds: First, we group each combination \((\omega ,L)\) according to the length and role of shared lines as given by \((l_i)_{i=1}^{N-1}\). Secondly, we identify the first intersection points at which we split the sausage/rib-walks. Thirdly, we use (6.24) to distribute the weight along the bottom lines, as shown in Fig. 17. In the fourth step, we apply, depending on the weight \(|x_i|^2\), one of the bounds of Lemma 6.2. Then we also allocate the one-point functions such that the spatial weight is along a line corresponding to a two-point function \(G_z\).
Proof of Lemma 6.2
We divide the proof depending on whether \(N=2\) and \(N\ge 3\).
Proof for \(N=2\). As we have already discussed how to bound the non-trivial sausage for \(\Xi ^{\scriptscriptstyle ( \text { 1})}_z\), occurring for \({\underline{b}}_1\ne 0\), we will restrict to \({\underline{b}}_1= 0\) in our discussion for \(\Xi ^{\scriptscriptstyle ( \text { 2})}_z \). We have to consider the coefficients as shown in Fig. 18: For a sausage-walk \(\omega \) and a lace \(L=\{0t_1,s_2|\omega |\}\) to which \(\omega \) contributes we define the first intersection points \(w_1=w_1(\omega ),\ w_2=w_2(\omega )\) and \(y={\overline{b}}^\omega _{s_2}\). If \(s_2<t_1\), then we define \(u=\omega _{s_1}\) and \(l=\max \{d_\omega (u,y),2\}\). For \(s_2=t_1\) we identify the last point u that the paths \(b^{S^\omega _{s_2}}({\underline{b}}^\omega _{s_2+1}, v)\) and \(b^{S^\omega _{s_2}}({\underline{b}}^\omega _{s_2+1}, w)\) have in common and define \(l=-\max \{d_{A^\omega _{s_2}}({\underline{b}}^\omega _{s_2+1},u),2\}\).
By definition of a sausage-walk (Definition 3.3), using the non-backtracking condition, and the selection of the first intersection points \(w_1,w_2\), we know that each square is repulsive and consists of at least four bonds. Especially, if \(t_1=1\), so that \(S^\omega _{0}\) and \(S^\omega _{1}\) intersect, then the non-backtracking condition states that this intersection cannot occur at the backbone bond, i.e.,  . For the same reason we know that
. For the same reason we know that  in the cases of \(|\omega |-s_2=1\) and \({\overline{b}}_{|\omega |}^\omega =x\). This last observations look like a minute special case, but it is numerically a major contribution.
in the cases of \(|\omega |-s_2=1\) and \({\overline{b}}_{|\omega |}^\omega =x\). This last observations look like a minute special case, but it is numerically a major contribution.
To obtain (6.31), we let the line from u to y contribute to the left square. When we add the weight \(|x-y|^2\), we obtain (6.32). When considering the weight \(|y|^2\), we choose the split of the diagram such that the line from u to y contributes to the right square instead. This creates the bound (6.33). To prove (6.31)–(6.33), we have to go through all cases for l and check that all possible sausage-walks are captured by the bounds on the right-hand sides. These tedious arguments follow the same steps as in the proof of the bounds on the coefficients for \(N=1\) in the previous section, and we omit the details. The bound on \(\Xi ^{{\scriptscriptstyle ( \text { 2})},\iota }_z\) is obtained in the same way, using the initial piece \(P^{{\scriptscriptstyle ( \text { 1})},\iota ,m}_{z}\), sketched in Sect. 5.1.
Proof for \(N\ge 3\). The bounds for \(N\ge 3\) are proven following the same procedure as described for \(N=2\). For each sausage-walk \(\omega \) and lace L, we identify the points at which we split \(\omega \), these are \({\underline{b}}_{s_i}\), \({\underline{b}}_{t_i}\), as well as the first intersection points \(w_i(\omega )\). Whenever \(s_i=t_{i-1}\), we also identify the point at which we split the sausage \(S_{s_i}^\omega \), see Figs. 10 and 11. Then, we define the lengths of the shared lines of neighboring loops \(l_i\) accordingly. For a bound on the weighted diagrams, we then split the weight using (6.24), leading to a sum of weighted diagrams as in (6.26), and for each of these summands, we derive a bound as in (6.32)–(6.34) depending on which line is weighted.
We now give some insight into how these bounds can be proven. As all these arguments do not offer any further insight, we omit their formal proof and refer the interested reader to [10, Sect. 4.3.5], where more details are given. It involves defining skeletons that encode (i) the length of the pieces of shared lines of neighboring loops; (ii) the location of the backbone; and (iii) the partial displacements \((x_i)_{i=1}^{N}\). Then, we classify all pairs of rib-/sausage-walks and laces \((\omega ,L)\) uniquely according to their skeleton and prove the bound using induction on N. The proof strategy uses ideas already presented above and techniques described in the standard reference [43].
Bound on \(\Xi ^{{\scriptscriptstyle ( \text { N})},\iota }_z\). The coefficients \(\Xi ^{{\scriptscriptstyle ( \text { N})}}_z\) and \(\Xi ^{{\scriptscriptstyle ( \text { N})},\iota }_z\) differ only by the first sausage, as informally explained in the foundation block \(P^{{\scriptscriptstyle ( \text { 1})},m}\) and \(P^{{\scriptscriptstyle ( \text { 1})},\iota ,m}\). Thus, also the bounds differ only in the first block. The block \(P^{{\scriptscriptstyle ( \text { 1})},\iota ,m}\) can have very many forms and the bounds on its weighted versions \(\Delta ^{\iota ,{\scriptscriptstyle I},m}\) and \(\Delta ^{\iota ,{\scriptscriptstyle II},m}\) have to be performed with utmost care, as they are numerically important. In the extended version of this article [14], we provide the complete definitions of \(P^{{\scriptscriptstyle ( \text { 1})},\iota ,m}\), \(\Delta ^{\iota ,{\scriptscriptstyle I},m}\) and \(\Delta ^{\iota ,{\scriptscriptstyle II},m}\) that list all possible cases/forms and their corresponding bounds. See [14, Appendices C.2.2–C.2.4]. As this takes 19 pages we omit these definitions here. In this version we have only added the sketch of \(P^{{\scriptscriptstyle ( \text { 1})},\iota ,m}\) in Sect. 5.1. \(\square \)
Decomposition Using Matrices. In the recursive definitions of \(P^{{\scriptscriptstyle ( \text { N})},m}\), \(P^{{\scriptscriptstyle ( \text { N})},\iota ,m}\), \(Q^{{\scriptscriptstyle ( \text { N})},m}\) in (6.27)–(6.28), as well as in the bounds of Lemma 6.2, we sum over the lengths of lines that are shared by two loops. We do this as it allows us to make use of the fact that any loop consists of at least four bonds. We convert this sum over line lengths into a product of matrices to obtain the bounds stated in Proposition 5.4. Here we explain how we do this. We start with the definition of \(P^{{\scriptscriptstyle ( \text { N})},m}\) in (6.27) and obtain
where we recall (5.4). Using this recursion, we can prove by induction and using (5.1), that
Combining this with (6.31), we obtain the bound on \(\Xi ^{{\scriptscriptstyle ( \text { N})}}_{z}\), as stated in (5.36), by bounding
The bound on \(\Xi ^{{\scriptscriptstyle ( \text { N})},\iota }_{z}\) is obtained in the same way, where \(P^{{\scriptscriptstyle ( \text { N})},l}_{z}\) is replaced with \(P^{{\scriptscriptstyle ( \text { N})},\iota ,l}_{z}\).
Using translation invariance for \({Q}_z^{{\scriptscriptstyle ( \text { M})},m}\), recall (6.29)–(6.30) for its definition, we obtain
Combining (6.36) and (6.38) with (6.35), we obtain
which proves (5.37). The bounds on \(\Xi ^{{\scriptscriptstyle ( \text { N})},\iota }_z\) are proven in the same way, using other initial diagrams.
Let us briefly mention a numerical aspect here. For \(|m|=1\), we only count u, v that are neighbors. By spatial symmetry,

where the sum over e indicates a sum over all neighbors of the origin. This means that the step of taking the supremum over \(v\in {\mathbb {Z}}^d\), while disassembling \(P_z^{{\scriptscriptstyle ( \text { N})},m}\) and \({Q}_z^{{\scriptscriptstyle ( \text { M})},m}\) in (6.36) and (6.38), actually holds with an equality for \(|m|\le 1\). We also apply this method to \(P^{{\scriptscriptstyle ( \text { N})},\iota ,m}_{z}\), when we simply sum over \(\iota \), to obtain

6.4 Bounds on Differences: Proof of Lemma 5.5
Now we turn to the bounds stated in Lemma 5.5. By definition \(\Xi ^{\scriptscriptstyle ( \text { 0})}_{\alpha ,z}(0)=0\), see (3.36). Further, we recall that, now by (3.42),
For \(x=0\), the sausage-walk needs to return to the origin. Note that the indicator \(J^{{\scriptscriptstyle ( \text { 1})}}[0,|\omega |]\) enforces an intersection between the zeroth and the last sausage, which in fact is implied also by the fact that \(\omega \in {\mathcal {W}}(0)\) and \({\underline{b}}^\omega _0=0\). However, \(J^{{\scriptscriptstyle ( \text { 1})}}[0,|\omega |]\) also forces the other sausages to avoid each other. Thus, the sausage-walk, without the initial sausage and \(b^\omega _0\), form a lattice animal and can be bounded by \({\bar{G}}_{3,z}({\overline{b}}^\omega _0)\). We bound the zeroth sausage by the factor \(zg^{\iota }_z\), resulting in the bound

which, together with \(\Xi ^{\scriptscriptstyle ( \text { 0})}_{\alpha ,z}(0)=0\), shows the bounds in (5.40) for \(x=0\), as well as (5.41). Using the same reasoning, we obtain

which, together with \(\Xi ^{\scriptscriptstyle ( \text { 1})}_{\alpha ,z}({e}_{1})\ge 0\), implies (5.42).
To prove (5.40) for \(x={e}_{1}\), we now show that \(\Xi ^{\scriptscriptstyle ( \text { 0})}_{\alpha ,z}({e}_{1})<\Xi ^{\scriptscriptstyle ( \text { 1})}_{\alpha ,z}({e}_{1})\). We do this by arguing that each LA contributing to \(\Xi ^{\scriptscriptstyle ( \text { 0})}_{\alpha ,z}({e}_{1})\) can be decomposed into a unique contribution to \(\Xi ^{\scriptscriptstyle ( \text { 1})}_{\alpha ,z}({e}_{1})\). For any LA that contributes to \(\Xi ^{\scriptscriptstyle ( \text { 0})}_{\alpha ,z}({e}_{1})\), choose one of the connections between 0 and \({e}_{1}\) to be the backbone, and allocate the rest of the LA to be sausages of the walk in any unique way you want (as long as it is unique, the map will yield an injection). As there is a double connection in the original LA, the first and last sausages in the created sausage-walks intersect, and thus provide a contribution to \(\Xi ^{\scriptscriptstyle ( \text { 1})}_{\alpha ,z}({e}_{1})\). The bounds (5.45)–(5.46) are obtained in a similar way.
In \(\Psi ^{{\scriptscriptstyle ( \text { 0})},1}_{\alpha ,{\scriptscriptstyle I},z}({e}_{1}+{e}_{\iota })\) and \(\Psi ^{{\scriptscriptstyle ( \text { 1})},1}_{\alpha ,{\scriptscriptstyle I},z}({e}_{1}+{e}_{\iota })\), the origin and \({e}_{1}+{e}_{\iota }\) are connected using two disjoint paths, each consisting of two bonds. Thus,
Combining these two bounds yields (5.43) and (5.44). \(\square \)
7 Proof of Main Results: Critical Exponents \(\nu , \gamma \) and \(\eta \)
In this section, we prove our main results. We start by noting that Theorem 1.1 immediately follows from the fact that \(f_2(z)\le \gamma _2\) uniformly in \(z\in [z_I,z_c)\). The bound for \(z=z_c\) follows from [12, Assumption 4.4], which was verified in Sect. 3.4.2. This implies Theorem 1.1. Similarly, Theorem 1.2 follows from the numerical estimates and the facts that \(f_i(z)\le \gamma _i\) uniformly in \(z\in [z_I,z_c]\) for \(i=1,2\). We prove Corollary 1.3 in Sect. 7.1, Theorem 1.4 in Sect. 7.2, and Theorem 1.5 in Sect. 7.3.
7.1 Proof of \(\gamma =1/2\) and \(\nu =1/4\) in Corollary 1.3
The finiteness of the square diagram follows from the infrared bound in Theorem 1.1, together with the Fourier inversion theorem, which together imply that
The finiteness of the integral is valid for \(d>8\), under the infrared bound which holds for \(d\ge 16\) and \(d\ge 17\) for lattice trees and lattice animals, respectively, by Theorem 1.1. The fact that \(\gamma =1/2\) follows directly from the finiteness of the square diagram, as proved in [4, 22, 44].
In the following, we will show that \(\nu =1/4\). The critical exponent \(\nu \) governs the explosion for \(z\nearrow z_c\) of \(\xi _2(z)\) defined in (1.8). For this we rely on notation and techniques used in the accompanying paper [14]. Indeed, we write, using (2.12),
with
By the completion of the bootstrap argument, we know that all the above NoBLE coefficients are well defined for all \(z\le z_c\).
In [14, Sect. 3.3.1], we define the continuous Laplace operator \(\bigtriangleup \): For a differentiable function g and \(s\in \{1,2,\ldots ,d\}\), let \(\partial _s g(k)=\frac{\partial }{\partial k_s} g(k)\) and \(\bigtriangleup g(k)=\sum _{s=1}^d\partial _s^2 g(k)\). For the Laplace operator \(\bigtriangleup \), we note that
and compute, now restricting to \(z<z_c\),
By the symmetry inherited from the symmetry of lattice trees and lattice animals, we know that all first order derivatives are zero at \(k=0\), so that all elements in the second line are zero. Thus, we conclude that
Starting from \(\xi _2(z)\), defined in (1.8), and (7.5), we conclude that
Our numerical estimates imply numerical lower and upper bounds of these factors in dimensions above \(16\) and \(17\) for lattice trees and lattice animals, respectively, uniformly in \(z<z_c\). In [14, Appendix D] we give a detailed description on how to bound such factors using the bounds on the coefficients summarized in Sect. 5.3. In particular, we obtain that, since \(\sum _{x\in {\mathbb {Z}}^d} |x|^2F_z(x)\) and \(\sum _{x\in {\mathbb {Z}}^d} |x|^2\Phi _z(x)\) are power-series with radius of convergence \(z_c\), by Abel’s theorem,
and these sums are absolutely convergent. We thus conclude that
The fact that \(\nu =1/4\) now follows from the fact that \(\gamma =1/2\). \(\square \)
7.2 Proof of \(\eta =0\) in k-Space in Theorem 1.4
By Abel’s theorem, and the fact that \(1-{{\hat{F}}}_{z_c}(k)>0\) for \(k\ne 0\) (which follows from Theorem 1.1),
Note that \(1-{{\hat{F}}}_{z_c}(0)=0\) (which follows from the finiteness of \({\hat{\Phi }}_{z_c}(0)\) and the fact that \(\chi (z)\) blows up as \(z\nearrow z_c\)). Since \(\bigtriangleup {{\hat{F}}}_z(k)|_{k=0}\) is well-defined, we thus immediately conclude that
so that Theorem 1.4 follows with
\(\square \)
7.3 Proof of \(\eta =0\) in x-Space in Theorem 1.5
The proof of Theorem 1.5 follows by using the x-space asymptotics proved by Takashi Hara in [15]. See in particular [15, Proposition 1.3]. For ease of reference, we also mention some useful bounds that follow from our analysis of LAs in dimension \(d=17\). We only give the bounds for LAs, as these bounds also bound the corresponding lace-expansion coefficients for LTs. While we only prove Theorem 1.5 for \(d\ge 27\), these bounds suggest that the classical lace expansion converges for \(d\ge 17\) by our numerical estimates, which is interesting in its own right. This also exemplifies that the restriction that Theorem 1.5 only applies to \(d\ge 27\) does not originate in the current paper, but rather in [15].
Using the bound on \(f_2(z_c)\) directly, with \(\bar{A}_2(17)=3.78,\) we obtain the rough bounds
In the following, we improve these rough bounds using the ideas explained in detail in Sect. 4.1.
For this, we explain how to modify the bounds on the lace-expansion coefficients for the classical expansion, by allocating one-point functions efficiently, and repulsiveness of the corresponding diagrams. We emphasize that we apply all these bounds to the coefficients of the classical lace expansion, not to the NoBLE, to make them compatible with the classical lace expansion that [15] is based upon. Allocating the one-point functions properly, and avoiding overcounting them as described in Sect. 4.2, we obtain
Next, we use repulsiveness as defined in Sect. 4.3. Recall that repulsiveness implies that all paths of the square that actually connect the five (for open squares) or four (for closed squares) boundary points are mutually bond-disjoint. We can bound the squares arising as bounds on intermediate diagrams in the coefficients of the classical lace expansion by
We further obtain bounds on the (open and closed) weighted triangles \(\bar{T}^{\scriptscriptstyle (2,0)}=\sup _{y}T^{\scriptscriptstyle (2,0)}(y)\), as required for [15], given by
In communication with Takashi Hara early 2019, we learned that finiteness of the diagrams in (7.17), together with the maximum of the diagrams in (7.16) being strictly smaller than \(\tfrac{1}{2}\), suffices for the x-space bounds in Theorem 1.5 to hold. The reason for the latter is that the base of the geometric convergence of the classical lace-expansion coefficients is at most twice the maximum of the squares in (7.16). When this number is strictly smaller than one, the classical lace expansion converges, which is needed to apply [15]. These bounds also hold in any \(d\ge 17\), using a numerical check in dimensions 17–29, and the monotonicity arguments in Appendix B for \(d\ge 30\). The fact that we only obtain Theorem 1.5 for \(d>27\) is due to a technical restriction in the proof in [15], that we explain in some more detail now.
The proof in [15], see in particular [15, Lemma 1.7], requires an initial bound of the form \(G_z(x)\le (|x|+1)^{-\alpha }\), and uses this to obtain a bound on the (classical) lace expansion coefficient \(\Pi _z(x)\) in x-space. However, since the precise bound in [15, Lemma 1.7] is not optimal in the case of lattice trees and animals (see the remark below [15, Lemma 1.7]), this requires a slightly stronger bound, as formulated in [15, (1.47)]. In the proof of [15, (1.47)], a recursion is being used that relies on the fact that an x-space bound on \(\Pi _z(x)\) implies one on \(G_z(x)\), which in turn again implies one on \(\Pi _z(x)\). The ingredients to this recursion can be found in [15, Lemmas 1.8 and 1.9], which handle each of these two steps. In order to get started, we need to rely on an initial bound, and the only initial bound that is available is the bound that \(\sum _{x\in {\mathbb {Z}}^d}|x|^2 |\Pi _z(x)|<\infty \). Applying this bound, the recursion yields the desired result provided that \(d>26\). In order to improve upon this, one would need to improve the estimates formulated in [15, Lemmas 1.7–1.9], which we do not know how to do.
The fact that the constant A(d) in Theorem 1.5 equals the one in Theorem 1.4 follows directly from the proof in [15]. \(\square \)
Change history
13 January 2022
A Correction to this paper has been published: https://doi.org/10.1007/s10955-021-02853-8
Notes
We do account for the possibility that \(\mathbf{A}\) is not diagonalizable.
In the application of the NoBLE to nearest-neighbor percolation in [13], we erroneously wrote \(p<p_c\) instead, but also there we need that \(p\in [p_I,p_c)\).
In Mathematica, the command $InitialDirectory will tell you what this directory is.
References
Bauerschmidt, R., Brydges, D., Slade, G.: Critical two-point function of the 4-dimensional weakly self-avoiding walk. Commun. Math. Phys. 338(1), 169–193 (2015)
Bauerschmidt, R., Brydges, D., Slade, G.: Logarithmic correction for the susceptibility of the 4-dimensional weakly self-avoiding walk: a renormalisation group analysis. Commun. Math. Phys. 337(2), 817–877 (2015)
Borgs, C., Chayes, J., van der Hofstad, R., Slade, G.: Mean-field lattice trees. Ann. Comb. 3(2–4), 205–221 (1999). (On combinatorics and statistical mechanics)
Bovier, A., Fröhlich, J., Glaus, U.: Branched polymers and dimensional reduction. In: Phénoménes critiques. systémes aléatoires, théories de jauge, Part I, II (Les Houches, 1984), pp. 725–893. North-Holland, Amsterdam (1986)
Brydges, D., Imbrie, J.: Branched polymers and dimensional reduction. Ann. Math. 158(3), 1019–1039 (2003)
Brydges, D.C., Spencer, T.: Self-avoiding walk in 5 or more dimensions. Commun. Math. Phys. 97, 125–148 (1985)
Derbez, E., Slade, G.: Lattice trees and super-Brownian motion. Can. Math. Bull. 40, 19–38 (1997)
Derbez, E., Slade, G.: The scaling limit of lattice trees in high dimensions. Commun. Math. Phys. 193, 69–104 (1998)
Fitzner, R.: www.fitzner.nl/noble/
Fitzner, R.: Non-backtracking lace expansion. PhD. thesis, TU Eindhoven (2013)
Fitzner, R., van der Hofstad, R.: Non-backtracking random walk. J. Stat. Phys. 150(2), 264–284 (2013)
Fitzner, R., van der Hofstad, R.: Generalized approach to the non-backtracking lace expansion. Probab. Theory Relat. Fields 169(3–4), 1041–1119 (2017)
Fitzner, R., van der Hofstad, R.: Mean-field behavior for nearest-neighbor percolation in \(d>10\). Electron. J. Probab. 22, 65 (2017)
Fitzner, R., van der Hofstad, R.: NoBLE for lattice trees and lattice animals. Extended version (2019). arXiv:1905.02785
Hara, T.: Decay of correlations in nearest-neighbor self-avoiding walk, percolation, lattice trees and animals. Ann. Probab. 36(2), 530–593 (2008)
Hara, T.: Private communication (2015)
Hara, T., Slade, G.: Mean-field critical behaviour for percolation in high dimensions. Commun. Math. Phys. 128, 333–391 (1990)
Hara, T., Slade, G.: On the upper critical dimension of lattice trees and lattice animals. J. Stat. Phys. 59, 1469–1510 (1990)
Hara, T., Slade, G.: The lace expansion for self-avoiding walk in five or more dimensions. Rev. Math. Phys. 4, 235–327 (1992)
Hara, T., Slade, G.: The number and size of branched polymers in high dimensions. J. Stat. Phys. 67, 1009–1038 (1992)
Hara, T., Slade, G.: Self-avoiding walk in five or more dimensions. I. The critical behaviour. Commun. Math. Phys. 147, 101–136 (1992)
Hara, T., Tasaki, H.: Critical behavior in a system of branched polymers. Prog. Theor. Phys. Suppl. 92, 14–25 (1987)
van der Hofstad, R., Holmes, M.: The survival probability and \(r\)-point functions in high dimensions. Ann. Math. 178(2), 665–685 (2013)
van der Hofstad, R., Holmes, M., Perkins, E.: A criterion for convergence to super-Brownian motion on path space. Ann. Probab. 45(1), 278–376 (2017)
van der Hofstad, R., Sakai, A.: Gaussian scaling for the critical spread-out contact process above the upper critical dimension. Electron. J. Probab. 9, 710–769 (2004)
van der Hofstad, R., Slade, G.: A generalised inductive approach to the lace expansion. Probab. Theory Relat. Fields 122(3), 389–430 (2002)
Holmes, M.: Convergence of lattice trees to super-Brownian motion above the critical dimension. Electron. J. Probab. 13(23), 671–755 (2008)
Holmes, M., Perkins, E.: Weak convergence of measure-valued processes and \(r\)-point functions. Ann. Probab. 35(5), 1769–1782 (2007)
Hsu, H., Nadler, W., Grassberger, P.: Simulations of lattice animals and trees. J. Phys. A 38(4), 775–806 (2005)
Jensen, I.: Enumerations of lattice animals and trees. J. Stat. Phys. 102(3–4), 865–881 (2001)
Kenyon, R., Winkler, P.: Branched polymers. Am. Math. Mon. 116(7), 612–628 (2009)
Lubensky, T.C., Isaacson, J.: Statistics of lattice animals and dilute branched polymers. Phys. Rev. A 20(5), 2130–2146 (1979)
Madras, N., Slade, G.: The Self-avoiding Walk. Birkhäuser, Boston (1993)
Mejía Miranda, Y., Slade, G.: The growth constants of lattice trees and lattice animals in high dimensions. Electron. Commun. Probab. 16, 129–136 (2011)
Mejía Miranda, Y., Slade, G.: Expansion in high dimension for the growth constants of lattice trees and lattice animals. Comb. Probab. Comput. 22(4), 527–565 (2013)
Nguyen, B.G., Yang, W.-S.: Triangle condition for oriented percolation in high dimensions. Ann. Probab. 21, 1809–1844 (1993)
Nguyen, B.G., Yang, W.-S.: Gaussian limit for critical oriented percolation in high dimensions. J. Stat. Phys. 78(3), 841–876 (1995)
Parisi, G., Sourlas, N.: Critical behavior of branched polymers and the Lee-Yang edge singularity. Phys. Rev. Lett. 46(14), 871–874 (1981)
Perkins, E.: Dawson-Watanabe superprocesses and measure-valued diffusions. In: Lectures on Probability Theory and Statistics (Saint-Flour, 1999), vol. 1781 of Lecture Notes in Mathematics, pp. 125–324. Springer, Berlin (2002)
Sakai, A.: Mean-field critical behavior for the contact process. J. Stat. Phys. 104(1–2), 111–143 (2001)
Sakai, A.: Lace expansion for the Ising model. Commun. Math. Phys. 272(2), 283–344 (2007)
Slade, G.: The diffusion of self-avoiding random walk in high dimensions. Commun. Math. Phys. 110, 661–683 (1987)
Slade, G.: The Lace Expansion and Its Applications. Lecture Notes in Mathematics, vol. 1879. Springer, Berlin (2006)
Tasaki, H.: Stochastic geometric methods in statistical physics and field theories. University of Tokio (1986) (PhD. thesis)
Acknowledgements
This work was supported in part by the Netherlands Organisation for Scientific Research (NWO) through VICI Grant 639.033.806 and the Gravitation Networks Grant 024.002.003. We thank David Brydges, Takashi Hara and Gordon Slade for their constant encouragement, as well as for several stimulating discussions. This work builds upon the work by Takashi Hara and Gordon Slade, originally used for self-avoiding walk and percolation. We are indebted to Takashi for his help in the proof of Theorem 1.5, which relies on an improved version of this analysis in [15] that Takashi shared with us in 2015. Early 2019, Takashi significantly helped us once more by clarifying the requirements for [15] to apply for LTs and LAs (see Sect. 7.3). The work of RF was partially performed while being employed by the Institute for Complex Molecular Systems at Eindhoven University of Technology.
Open Access
This article is distributed under the terms of the Creative Commons Attribution 4.0 International License (http://creativecommons.org/licenses/by/4.0/), which permits unrestricted use, distribution, and reproduction in any medium, provided you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons license, and indicate if changes were made.
Author information
Authors and Affiliations
Corresponding author
Additional information
Communicated by Hal Tasaki.
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
The original online version of this article was revised: the notation for vectors, which should consistent and it is updated in the article.
Supplementary Information
Below is the link to the electronic supplementary material.
Appendices
A Lower Bound on the Initial Point
In this section, we prove that \(z_I\ge (2d-1)^{-1}{\mathrm {e}}^{-1}\) by proving upper bounds on \(g_{z_I}\) and \(g^\iota _{z_I}\):
Lemma A.1
(Lower bound on \(z_I\)) Let \(z_I\) satisfy
Then, \(z_I\ge (2d-1)^{-1}{\mathrm {e}}^{-1}\).
To prove Lemma A.1, we use a similar argument as in [18, Proof of Lemma 3.1]. Unfortunately, one step in [18, Proof of Lemma 3.1] is not correct as claimed. We correct the argument by using Lemma A.2 below. We explain the issue with and its origin [18, Proof of Lemma 3.1] in the proof of Lemma A.2. We have also recently learned that Mejía Miranda and Slade in [34, Lemma 2] prove a slightly weaker correction. Both proofs are adaptations of the proof of [3, (3.6)].
The proof of Lemma A.1 relies on the following lemma, that we prove thereafter, and which is of independent interest:
Lemma A.2
(Upper bound on the number of n-bond LAs) The number of n-bond LAs that contain the origin is bounded above by
Let us first use Lemma A.2 to prove Lemma A.1:
Proof of Lemma A.1
We use Lemma A.2 to show that \(z_I\ge (2d-1)^{-1}{\mathrm {e}}^{-1}\). For this, we bound \(g_z\) using (A.2) as
We note that
since the summand in (A.4) equals the probability that the total progeny of a branching process with Poisson offspring distribution with parameter one equals n, and the sum of these probabilities equals 1, since the tree is a.s. finite. We obtain for \(z \le ((2d-1){\mathrm {e}})^{-1}\) that
Since \(g^{\iota }_z\le g_z\) this is also a bound for \(g^{\iota }_z\).
We can improve this bound on \(g^{\iota }_z\) by using the condition that \({e}_{\iota }\) is not part of the tree/animal. A non-trivial LT/LA contains at least one edge connecting the origin to a neighboring point. Therefore, at least 1 out of 2d LTs/LAs counted in \(g_z\) does not contribute to \(g^{\iota }_z\). We conclude that, for \(z \le ((2d-1){\mathrm {e}})^{-1}\),
and thus, for all \(z\le z_I\),
as well as, by the definition of \(z_I\) in (3.55),
This implies that \(z_I\ge (2d-1)^{-1}{\mathrm {e}}^{-1}\). \(\square \)
We complete this section by proving Lemma A.2:
Proof of Lemma A.2
The proof of [18, Lemma 3.1] uses a similar bound as stated in (A.2) in Lemma A.2, but contains an error that originates from a related computation in [4]. Namely it is used that there are \((n+1)^{n}/(n+1)!\) abstract unlabeled rooted trees with n edges. However, while Cayley’s theorem states that there are \((n+1)^{n}\) labeled rooted trees, the removal of the labels does not create a factor \(1/(n+1)!\) as stated. Indeed, there are less than \((n+1)!\) ways to label an abstract tree, e.g., for a tree with two edges there are only 3 different ways to label the tree as the only difference is the label of the vertex that is part of two edges.
To prove the bound stated in (A.2) we first use the techniques of [3, Sects. 2 and 5] to show the lemma only for LTs. Then, we adapt the arguments to LAs.
We begin by defining a non-backtracking branching random walk with Poisson offspring distribution. Abstract trees are the family trees of a critical branching process with Poisson offspring distribution. In more detail, we begin with a single individual having \(\xi \) offspring, where \(\xi \) is a Poisson random variable of mean 1, i.e., \(\mathbb {P}(\xi =m)=({\mathrm {e}}m!)^{-1}\). Each of the offspring then independently has offspring of its own with the same critical Poisson distribution. We denote by \(|{\mathcal {T}}|\) the number of bonds of the tree \({\mathcal {T}}\). For an abstract rooted tree \({\mathcal {T}}\), with the ith individual having \(\xi _i\) offspring, this associates to \({\mathcal {T}}\) the weight

We define an embedding \(\varphi \) of \({\mathcal {T}}\) into \({\mathbb {Z}}^d\) to be a mapping of the vertices of \({\mathcal {T}}\) into \({\mathbb {Z}}^d\), such that the root is mapped to the origin and adjacent vertices in the tree are mapped to nearest-neighbors in \({\mathbb {Z}}^d\). Further, we restrict to embeddings in which the children are not mapped to the location of the grandparents, which corresponds to a non-backtracking condition. We define the pair \(({\mathcal {T}},\varphi )\) to be a non-backtracking branching random walk with Poisson offspring distribution (Poisson-NBBRW). Given an abstract tree \({\mathcal {T}}\) with n bonds, there are \(2d (2d-1)^{n-1}\) possible embeddings \(\varphi \) of \({\mathcal {T}}\). The Poisson-NBBRW measure is given by

for all \({\mathcal {T}}\) and \(\varphi \). We define \(\mathbb {I}^{\scriptscriptstyle (t)}({\mathcal {T}},\varphi )\) to be the indicator that the embedding \(\varphi \) of \({\mathcal {T}}\) is a LT, i.e., \(\varphi :{\mathcal {T}}\mapsto {\mathbb {Z}}^d\) is injective. For a LT T, we write \(T=\varphi ({\mathcal {T}})\) if the embedding \(\varphi \) of \({\mathcal {T}}\) equals T. For abstract trees with n bonds, we define the measure

with normalization

We prove that the number of n-bond LTs that contain the origin is given by

which is equivalent to

To do that, we show that, for each n-bond LT T,

which implies that the measure \({{\mathbb {Q}}}^{\scriptscriptstyle (t)}_n\) corresponds to the uniform measure on all n-bond LTs and thus implies (A.14), and thus (A.13).
From (A.10) we conclude that, for all T with \(|T|=n\),

We continue by proving that, for any LT T,

Let \(d_0\) be the degree of 0 in T, and given non-zero \(x\in T\), let \(d_x\) be the degree of x in T minus 1. The set \(\{d_x:x\in T\}\) must be equal to the set of \(\xi _i\) for any \({\mathcal {T}}\) that can be mapped to T. Defining \(\nu (T)=\#\{({\mathcal {T}},\varphi ):\varphi ({\mathcal {T}})=T\}\), (A.17) is therefore equivalent to

We prove (A.18) by induction on the number N of generations of T. By this, we mean the length of the longest self-avoiding path in T, starting from the origin. The identity (A.18) clearly holds for \(N=0\). Our induction hypothesis is that (A.18) holds if there are \(N-1\) or fewer generations. Suppose T has N generations, let \(T_1,\ldots ,T_{d_0}\) denote the LTs resulting from deleting from T all bonds incident on the origin. We regard each \(T_a\) as rooted at the neighbor of the origin in the corresponding deleted bond. It suffices to show that \(\nu (T)=b_0!\prod _{a=1}^{d_0}\nu (T_a)\), since each \(T_a\) has fewer than N generations. To prove this, we note that each \(({\mathcal {T}},\varphi )\) with \(\varphi ({\mathcal {T}})=T\) induces a Poisson-NBBRW \(({\mathcal {T}}_a,\varphi _a)\) such that \(\varphi _a({\mathcal {T}}_a)=T_a\). This correspondence is \(d_0!\) to 1, since \(({\mathcal {T}},\varphi )\) is determined by the set of \(({\mathcal {T}}_a,\varphi _a)\), up to permutations of the branches of \({\mathcal {T}}\) at its root. This proves \(\nu (T)=d_0!\prod _{a=1}^{d_0}\nu (T_a)\), which extends (A.18) to LTs of N generations by the induction hypothesis. The claim in (A.18) for all N follows by induction.
We finally complete the proof of the lemma for LTs. We rearrange (A.13) and use (A.10) to obtain

Since there are \(2d (2d-1)^{n-1}\) embeddings \(\varphi \), we then know that

The probability distribution of the total number of bonds of a Poisson branching process is given by \(\mathbb {P}(|{\mathcal {T}}|=n)={\mathrm {e}}^{-(n+1)} (n+1)^{n}/(n+1)!\) (as this is the number of vertices, also called the total progeny, minus 1). We insert this into (A.20) and obtain the claimed bound for LTs.
The claim for LAs is obtained using similar ideas, but requires some adaptations as LAs can contain loops. The main difficulty is to obtain a relation similar to (A.18).
We now define \(\mathbb {I}^{\scriptscriptstyle (a)}({\mathcal {T}},\varphi )\) to be the indicator for the event that
-
(1)
no two bonds of the abstract tree \({\mathcal {T}}\) are mapped to the same bond in \({\mathbb {Z}}^d\) by \(\varphi \);
-
(2)
for all \(i\in {\mathcal {T}}\) either \(\xi _i=0\) or the following two conditions hold:
-
(a)
there exist no \(j\in {\mathcal {T}}\setminus \{i\}\), such that \(\varphi (i)=\varphi (j), \xi _j>0\) and \(\mathrm{height}(j)=\mathrm{height}(i)\),
-
(b)
there exist no \(j\in {\mathcal {T}}\setminus \{i\}\), such that \(\varphi (i)=\varphi (j)\) and \(\mathrm{height}(j)<\mathrm{height}(i)\),
where the height of a point \(a\in {\mathcal {T}}\) is the intrinsic distance of a to the root in \({\mathcal {T}}\).
-
(a)
For a Poisson-NBBRW \(({\mathcal {T}}_a,\varphi _a)\) (1) guarantees that each bond is only used once by the process and (2) is the condition that whenever a point is visited by multiple individuals then only the first of them can have offspring. Thus, (1) and (2) together imply that the image \(\varphi ({\mathcal {T}})\) is a LA. Here, for a LA A, we write \(A=\varphi ({\mathcal {T}})\) if the embedding \(\varphi \) of \({\mathcal {T}}\) equals A.
Now we proceed as for LTs by defining

where

We next prove that the number of n-bond LAs containing the origin is given by

This is analogous to the proof for LT in (A.13), which the exception of the proof that

We now explain how to adapt the argument so as to obtain (A.24). To prove this we define \(d_x\) such that it corresponds to the number of offspring of the Poisson branching process. In contrast to the LT case, for LAs it can happen that \(\varphi \) maps multiple individuals of \({\mathcal {T}}\) to x. Therefore, it is not obvious how to choose \(d_x\) such that \((\xi _i)_i\) and \((d_x)_x\) are equivalent.
For a LA A, and two vertices \(x,y\in A\), we define \(d_{A}(x,y)\) to be the intrinsic distance between x and y, and call the distance \(d_A(0,x)\) the age of x. For \(N\in \mathbb {N}\), we call the set of all vertices with age N the generation N. We define an exploration process, that we use to define \((d_x)_x\), as follows:
-
(1)
We define \(d_0\) to be the degree of 0 in A;
-
(2)
We define S to be the set of all vertices directly connected to the origin in A;
-
(3)
We define \(B\subset A\) to be the subset of all bonds in A that do not contain the origin;
-
(4)
Let N be the age of the youngest vertex in S;
-
(5)
For the unique x in the Nth generation with the lowest lexicographic order:
-
(i)
we define \(d_x\) to be the degree of x in B;
-
(ii)
we update S by adding the endpoints of the bonds in B adjacent to x, and give these endpoints an age that is equal to the age of x plus one;
-
(iii)
we remove x from S and the bonds that contain x from B.
-
(i)
-
(6)
If S is non-empty, then we repeat the procedure starting in 4) with the updated sets S and B.
This procedure terminates when \(d_x\) has been defined for all vertices of A.
Similarly to the LT case, we define \(\nu (A)=\#\{({\mathcal {T}},\varphi ):\varphi ({\mathcal {T}})=A, \mathbb {I}^{\scriptscriptstyle (a)}({\mathcal {T}},\varphi )=1\}\) and now show that
which implies (A.24).
We again prove (A.25) by induction on the number N of generations of A. The number of generations corresponds to the age of the oldest particle in A. The identity (A.18) clearly holds for \(N=0\). Our induction hypothesis is that (A.18) holds if there are \(N-1\) or fewer generations.
For a LT, the removal of the \(d_0\) bonds adjacent to the origin splits the tree into \(d_0\) unique, non-intersecting subtrees \(T_1,\ldots ,T_{d_0}\). Due to possible double connections in a LA, the removal of the bonds adjacent to the origin does not automatically split the animal into \(d_0\) uniquely defined sub-animals \(A_a\). We will now create a unique split of the animal A, that is consistent with the exploration process that we have used to define \((d_x)_x\).
For this, we first remove a certain set of bonds to create a LT \(T\subseteq A\). Then we split the T into \(d_0\) subtrees as done above. In the last step we add each of the removed bonds to the subtrees to create a unique decomposition \(A_1,\ldots ,A_{d_0}\). This procedure is visualized in Fig. 19. In what follows, we explain how the set of bonds that is removed is being chosen. We fix a LA A.
The first picture shows how we orient the bonds of A to create \(\mathbf {A}\). In the second picture we see the LT that is created by the removal of the bonds. The coordinates of the vertices that we compare in step (2) of the algorithm below are indicated. The last picture shows the result of the partition of \(\mathbf {A}\setminus \{0\}\), which is the oriented graph obtained by removing the vertex 0 and all edges incident to it from \(\mathbf {A}\)
-
(1)
We orient all bonds of A away from the origin in the intrinsic distance, see Fig. 19, and denote by \(\mathbf {A}\) the created LA of oriented bonds. Thus, the oriented bonds \(b=(x,y)\) are such that the age of y equals that of x plus one (equal ages cannot happen due to the bipartite structure of the hypercubic lattice \(\mathbb {Z}^d\));
-
(2)
For all \(x\in {\mathbb {Z}}^d\) which have multiple ingoing bonds we remove all ingoing bonds from \(\mathbf {A}\) with the exception of the ingoing bond \((b_i=({\underline{b}}_i,{\overline{b}}_i=x))_i\) that contains the starting point \({\underline{b}}_i\) with the lowest lexicographic order;
-
(3)
We denote the resulting LA by \(\mathbf {T}\) and the set of all removed oriented bonds by \(\mathbf {S}\);
-
(4)
We know that \(\mathbf {A}=\mathbf {T}\cup \mathbf {S}\) and that in fact \(\mathbf {T}\) is a LT since step (3) leaves at most one ingoing bond for every x (and precisely one for all vertices except for 0). Further, we see that \(\mathbf {T}\) contains the same set of vertices as A, so that \(\mathbf {T}\) can also be considered a spanning tree of the graph A;
-
(5)
We delete from \(\mathbf {T}\) all bonds incident to the origin and denote the created LTs by \(\mathbf {T}_1,\ldots ,\mathbf {T}_{d_0}\);
-
(6)
For \(i=1,\ldots , d_0\), we define
$$\begin{aligned} \mathbf {A}_i=\mathbf {T}_i\cup \{ b\in \mathbf {S} \mid {\underline{b}}\in \mathbf {T}_i\}, \end{aligned}$$(A.26)and \(A_i\) to be the LA obtained by removing the orientation of the bonds of \(\mathbf {A}_i\).
We regard \(A_{i}\) as rooted at the unique vertex in it that was directly connected to the origin in A. We see that for all \(i=1,\ldots ,d_0\) and \(x\in A_i\), the number \(d_x\) corresponds to the number of outgoing edges of x in \(A_i\). We note that for all bonds \(b\in \mathbf {S}\cup \mathbf {A}_i\), the end-vertex \({\overline{b}}\) has no outgoing bonds. This is related to the condition (2) of the definition of \(\mathbb {I}^{\scriptscriptstyle (a)}({\mathcal {T}},\varphi )\).
It suffices to show that \(\nu (A)=d_0!\prod _{a=1}^{d_0}\nu (A_{a})\), since each \(A_{i}\) has at most \(N-1\) generations. We note that each \(({\mathcal {T}},\varphi )\) with \(\varphi ({\mathcal {T}})=A\) induces a Poisson-NBBRW \(({\mathcal {T}}_{a},\varphi _{a})\) such that \(\varphi _a({\mathcal {T}}_{a})=A_{a}\). This correspondence is \(d_0!\) to 1, since \(({\mathcal {T}},\varphi )\) is determined by the set of \(({\mathcal {T}}_{a},\varphi _{a})\), up to permutations of the branches of \({\mathcal {T}}\) at its root. This proves that indeed \(\nu (A)=d_0!\prod _{a=1}^{d_0}\nu (A_{a})\). The completion of the proof of (A.23) for LAs is now identical to that for LTs.
Knowing that (A.23) holds, we repeat the steps between (A.20) and (A.19) for LAs, and obtain the claimed bound on \(t^{\scriptscriptstyle (a)}_n(0)\), which completes the proof of Lemma A.2. \(\square \)
B Extension to All Dimensions \(d\ge 30\)
In this section we prove that when a modified version of our analysis is applied successfully in some dimension \(d'\), which we choose to be \(d'=30\), then this analysis will also succeed in any dimension \(d\ge d'\). For this, we need to modify the analysis somewhat, so that the bounds that apply in dimension \(d'\) will be guaranteed to apply to any dimension \(d\ge d'\). The basic ideas, that also guide the structure of this appendix, are the following:
-
(1)
In Appendix B.1 we prove that all SRW integrals that are used in our bounds for \(d\ge d'\) are monotone decreasing in d.
-
(2)
In Appendix B.2 we prove that the contributions of short explicit paths within our bounds are all monotone decreasing in d.
-
(3)
In Appendix B.3 we argue that the first two observations imply that the bounds on all simple diagrams are monotone decreasing in d. This will imply that all bounds on the coefficients \(\beta _{\bullet }\), as summarized in Sect. 5.3 but now applied to our slightly modified analysis, are monotone decreasing in d.
-
(4)
In Appendix B.4 we show that, since our bounds on the coefficients are all monotone in the dimension d, all bounds on the coefficients arising in the rewrite used in the general analysis [12], are also monotone.
-
(5)
In Appendix B.5 we describe how the above steps imply that whenever the bootstrap succeeds with a given set of parameters \((\gamma _i,\Gamma _i)_{i=1}^3\) in \(d=d'\), then it also succeeds in all dimension \(d\ge d'\). This in turn implies our results in all \(d\ge d'\).
We emphasize that the bounds derived here are slightly worse than the ones used for a specific dimension. This is due to the fact that we do not know that all SRW integrals that we rely upon in the bounds for explicit dimensions are monotone decreasing. Thus, we need to rely on the subset of SRW integrals that we can prove to be monotone decreasing.
We implement these bounds, which are provably monotone in d, using the notebook LAmonotone. Before starting this, let us clarify the notion of monotonicity in d:
Definition B.1
(Monotonicity in dimension) Let \(g^{\scriptscriptstyle (d)}:\mathbb {Z}^d\rightarrow \mathbb {R}\) be a family of functions. We say that \(g^{\scriptscriptstyle (d)}(x^{\scriptscriptstyle (d)})\) is monotone in d when \(g^{\scriptscriptstyle (d+1)}((x^{\scriptscriptstyle (d)},0))\le g^{\scriptscriptstyle (d)}(x^{\scriptscriptstyle (d)})\), where \((x^{\scriptscriptstyle (d)},0)=(x_1, \ldots , x_d,0)\) is \(x^{\scriptscriptstyle (d)}\) appended with an extra coordinate that takes the value zero.
Prominent examples of such monotone families are the critical SRW Green’s function in d dimensions \(C_{1/(2d)}^{\scriptscriptstyle (d)}\), for which we investigate its monotonicity for \(x^{\scriptscriptstyle (d)}\) equal to the origin, as well as some points close to the origin, which we investigate next.
1.1 B.1 SRW Integrals
We start by showing that all the bounds on the SRW integrals \((I_{n,m},K_{n,m},T_{n,m},U_{n})\) and \({\mathcal {J}}_{n,l}(x)\) that we use in our analysis can be uniformly bounded in d, using bounds that are monotone decreasing in d. We emphasize that we do not claim that all integrals, such as \(U_n\), are monotone decreasing in d, only that the bounds that we rely upon are. The reason for this distinction is that the only monotonicity that we can actually prove is given by the two lemmas below:
Lemma B.2
(Monotonicity of SRW Green’s function in d) Let \(|x|_{\scriptscriptstyle \infty }\) be the supremum norm of \(x\in \mathbb {Z}^d\). Then, for every \(n\ge 1\) and \(x^{\scriptscriptstyle (d)}\in \mathbb {Z}^d\) with \(|x^{\scriptscriptstyle (d)}|_{\scriptscriptstyle \infty }\le 2\),

where \(x^{\scriptscriptstyle (d+1)}_i=x^{\scriptscriptstyle (d)}_i\) for \(i\in \{1,\ldots ,d\}\), while \(x^{\scriptscriptstyle (d+1)}_{d+1}=0\).
Lemma B.3
(Monotonicity of SRW Green’s function in x) For any positive integer \(n\ge 1\), the function \(x\mapsto I_{n,0}(x)\) is monotone decreasing in each \(|x|_\mu \) with \(\mu =1,2,\ldots , d\).
Lemma B.3 is [19, Lemma B.3] and follows from the monotonicity of Bessel functions, see (B.3). Lemma B.2 is already proven for all x with \(|x^{\scriptscriptstyle (d)}|_{\scriptscriptstyle \infty }\le 1\), in the proof of [19, Lemma C.1]. For this reason we copy parts of the proof almost verbatim from [19, Lemma C.1]. For \(|x^{\scriptscriptstyle (d)}|_{\scriptscriptstyle \infty }=2\), we only need to add some additional ideas.
Proof
Equation [19, (B.2)], states, after a rescaling of the t variable, that

where

Let \(\ell _1\) be the number of coordinates equal to \(\pm 1\) in \(x^{\scriptscriptstyle (d)}\), and \(\ell _2\) the number of coordinates equal to \(\pm 2\) in \(x^{\scriptscriptstyle (d)}\). Then,

Denoting the \(L_p(-\pi ,\pi )\) norm of \(g_s(\theta ):=\exp (-s(1-\cos \theta ))\) by \(\Vert g_s\Vert _p\), we obtain by (B.3) that \(f_0(s/d)^d=\Vert g_s\Vert _{1/d}\), which is monotone decreasing in d for fixed s. This already yields the statement for \(x^{\scriptscriptstyle (d)}=0\).
As shown by Hara and Slade [19, Proof of Lemma C.1], the factor \(f_1(s/d)/f_0(s/d)\) is monotone decreasing in d, for fixed s, because \(z\mapsto f_1(z)/f_0(z)\) is monotone increasing in \(z>0\). This can be seen from a direct calculation of its derivative, which gives

where

This proves the statement for all \(x^{\scriptscriptstyle (d)}\) with \(|x^{\scriptscriptstyle (d)}|_{\scriptscriptstyle \infty }=1\), and starts the point where we extend [19, Lemma C.1].
For even N, we use the periodicity of \(\cos (\theta )\) and \(\cos (N\theta )\), as well as \(\cos (N\theta )=\cos (N(\theta +\pi ))\) and (B.3), to see that

For odd N, the same can be derived where \(\cosh \) is replaced by \(\sinh \), as \(\cos (N\theta )=-\cos (N(\theta +\pi ))\) for odd N, but we will not rely on this fact.
Using a uniform random variable U on \([-\pi /2,\pi /2]\), we can rewrite the above as

Using the random variable X with density \(f_{\scriptscriptstyle X}(z)=\cosh (zx)/\int _0^\pi \cosh (zy)dy\), we can simplify
Then, we note that \(\cos (2x)=2\cos (x)^2-1\), so
Finally, let \(Y=\cos (X)\), which is non-negative as \(X\in [-\pi /2,\pi /2]\), to conclude

Since both \(y\mapsto \tanh (zy) y\) as well as \(y\mapsto y^2\) are increasing on [0, 1], the above covariance is non-negative. Here we use that \(\mathrm {Cov}(f(Y),g(Y))\ge 0\) when both f and g are increasing on the support of Y, with strict inequality when both are not constant. \(\square \)
In what follows, every bound on SRW-integrals that we use is concluded from the monotonicity in d of \(I_{n,0}(x)\) of Lemma B.2, as well as the monotonicity in \(|x_\mu |\) of \(I_{n,0}(x)\) in Lemma B.3. In this way all these bounds will inherit their monotonicity from these \(I_{n,0}(x)\). To compute these other bounds, we use that

and apply this bound iteratively starting from \(m=1\) until \(m=10\) to create our bounds.
As we know that \(I_{n,m}(x)\) is monotone in d only for \(m=0\) and appropriate values of x, it is a priori not clear that these bounds are also monotone decreasing in d. For this reason, let us create a bound that is monotone decreasing by construction. For \(x\in {\mathbb {Z}}^d\), let

Thus, \({\underline{x}}\) is the point that is closest to x and is still covered by Lemma B.2. By Lemma B.3, we know that \(I_{n,0}(x)\le I_{n,0}({\underline{x}})\), which allows us to use monotone bounds.
Let us now explain how we use the above ideas to derive monotone bounds on \(I_{n,m}(x)\) for every n, m, x. We define \({\bar{I}}_{n,0}(x):= I_{n,0}({\underline{x}})\) and, for \(m\ge 1\), define \({\bar{I}}_{n,m}(x)\) recursively by

To finalize the bounds we need to show that

which we will do by induction on m.
For \(m=0\), the inequality (B.12) holds by definition and Lemma B.3. For \(m\ge 1\), we note that
where the inequality follows from (B.12) for \(m-1\). This advances the induction, and thus proves (B.12). It also concludes our construction of bounds that are monotone in d, as \({\bar{I}}_{n,m}\) is monotone in the sense of Definition B.1.
Using these monotone bounds on \(I_{n,m}(x)\) we conclude bounds on \(L_n(x)\), as given in [12, (5.17)], e.g.,
which again, by the monotonicity in the coordinates of \(I_{n,0}(x)\), creates a bound on \(L_n(x)\) that is monotone decreasing in d as well. Using the same idea and the methods in [12, Sect. 5.2], we can construct bounds on \(K_{n,m}(x)\), \(T_{n,m}(x)\), \(V_{n,m}\), \(T_{n,m}(x)\), \( {\mathcal {J}}_{n,l}(x)\). These bounds inherit their monotonicity in d from that of \({\bar{I}}_{n,m}(x)\). Note that we also remove all terms that are subtracted, e.g. \(2I_{n,l}(2{e}_{1})\) in [12, (5.25)], and use only points x covered by Lemma B.2, by exploiting the monotonicity of \(\bar{I}_{n,m}(x)\) in x. All this can be found in the second section of the (very readable) LAMonotone Mathematica notebook, which can be downloaded from [9] in its original form, as well as in pdf-format, or, alternatively, from the publisher’s website for supplementary material.
1.2 B.2 Monotonicity of Small-Step Paths
A cornerstone of our numerical bounding procedure is to extract explicit short contributions from our diagrams, for which we can use the repulsiveness of connections involved. For this step we require that
\(c_n(x)/(2d-1)^n\) is monotone decreasing in d, where \(c_n\) is the size of a collection of paths, such as simple random walk, non-backtracking walks, self-avoiding walk, or bond-self-avoiding walk paths, of n steps, starting at the origin and ending at \(x\in \mathbb {Z}^d\). Our argument applies to each of these collections.
Lemma B.4
(Monotonicity of small-step paths) Fix n and x. Let \(c_n(x)\) be the number of n-step paths from 0 to x of the above types and \(\mathrm {dim}(x)\) be the dimensionality of x, i.e.,
Then, \(d\mapsto c_n(x)/(2d-1)^n\) is monotonically decreasing in d for \(2d\ge \max \{2\mathrm {dim}(x)+n-|x|_1, 2n-2\}\).
Proof
We define the dimension of a path be the maximal dimension of the points it traverses, and let
This \(c_n^{\scriptscriptstyle (d)}\) has the following properties, which hold for any type of nearest-neighbor paths:
-
(i)
\(c_n^{\scriptscriptstyle (d)}(x)\equiv 0\) when \(n<|x|_1\), as there are simply not enough steps n to reach x;
-
(ii)
\(c_n^{\scriptscriptstyle (d)}(x)\equiv 0\) when \(d< \mathrm {dim}(x)\), as the point x lives in larger dimension than d;
-
(iii)
\(c_n^{\scriptscriptstyle (d)}(x)\equiv 0\) when \(n-|x|_1\) is odd, by parity of the lattice;
-
(iv)
\(c_n^{\scriptscriptstyle (d)}(x)\equiv 0\) when \(d>\mathrm {dim}(x)+\tfrac{n-|x|_1}{2}\), as a path can simply not use all the required dimensions d and still reach x in n steps.
By grouping the paths from 0 to x according to the number of dimensions \(d'\) used, regarding the properties above, we obtain

The binomial coefficient represents the free choices for the additional dimensions \(d'\), not imposed by x itself, that the path uses. We then write
where

Our restriction to \(2d\ge 2\mathrm {dim}(x)+n-|x|_1\) ensures that each summand contributes, which allows us to conclude the required monotonicity of \(d\mapsto c_n(x)/(2d-1)^n\) by showing that \(d\mapsto f_n(d',d+1)\) is monotonically decreasing for every \(d'\) fixed. For this, we need to show that
is smaller than one. The first fraction is monotone increasing in \(\mathrm {dim}(x)\) and \(d'\). We use that \(d'\le \tfrac{n-|x|_1}{2}\), \(\mathrm {dim}(x)\le |x|_1\) and then \(n\ge |x|_1\ge 0\) to obtain
where the final inequality follows since \(n\le d+1\). For the second fraction we note that \((1+y)^n\le 1+yn+y^2n(n-1)/2\) for all \(n\le y\) and \(y>-1\), so that
Combining both bounds, we obtain
We finally note that, since \(n\le d\),
when \(d\ge 1\). \(\square \)
1.3 B.3 Monotonicity of Bounds on the NoBLE Coefficients
We bound simple and repulsive diagrams using the bootstrap assumption, SRW-integrals and by extracting short explicit contributions. This is explained in detail in [12, Sect. 5.3.1]. For example,
where \(p_n\) is the number of n-step bond-self-avoiding paths from 0 to x, i.e., paths that do not use the same bond twice. For dimension \(d=16,\ldots , 29\), we use \(M=10\). For our analysis in \(d\ge 30\), we extract only 7 steps, so that \(M=8\).
To obtain numerical values for these bounds, we use
and use the following bound that can be numerically computed:
By Lemma B.4 the first term is monotone decreasing in d. Further, we bound \(K_{n,8}(x)\) using bounds that are monotone in d (recall Sect. 1), which means that our bound on \(\mathscr {T}_{1,1,0}(x)\) is monotone decreasing in d.
We use the same kind of bounds for all simple and repulsive diagrams. As we bound all NoBLE coefficients using these diagrams (recall Sect. 5.2), the bounds that we rely upon inherit this monotonicity. Having made this point we should add that in three bounds in Lemma 5.2 we see a factor of \((2d-2)/2d\), which is not monotone decreasing. We resolve this non-monotonicity issue by simply replacing \((2d-2)/2d\) by 1 in our bounds/implementation for \(d\ge 30\).
Unfortunately our verification of the technical condition \(\Pi ^{{\scriptscriptstyle ( \text { 0})},\iota ,\kappa }(x)\le zg_z \Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }(x)\) is numerical. We have already proved this for all \(x\ne {e}_{\iota }+{e}_{\kappa }\). Even though the contribution for \(x={e}_{\iota }+{e}_{\kappa }\) is quite small (recall (3.75)), we did not manage to find a proof that is uniform in the dimension for \(x={e}_{\iota }+{e}_{\kappa }\). This causes problems in the application of the general analysis in [12]. To bypass this, we use a bound that applies to \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }\) and \(\Pi ^{{\scriptscriptstyle ( \text { 0})},\iota ,\kappa }\) at the same time, and replace the bounds \(\beta _{\scriptscriptstyle \Xi ^\iota }^{\scriptscriptstyle ( \text { 0})}, \beta _{{\scriptscriptstyle \Delta \Xi ^\iota },0}^{\scriptscriptstyle ( \text { 0})}, \beta _{{\scriptscriptstyle \Delta \Xi ^\iota },\iota }^{\scriptscriptstyle ( \text { 0})}\) that are currently used to bound \(\Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }\) only, by a bound that applies also to \(\Pi ^{{\scriptscriptstyle ( \text { 0})},\iota ,\kappa }\). Numerically, this makes no difference, as our crude numerical bound already applies to both these terms at the same time. This problem has repercussions in the proof of (5.25) and (5.26), where the bound \(\Pi ^{{\scriptscriptstyle ( \text { 0})},\iota ,\kappa }(x)\le zg_z \Xi ^{{\scriptscriptstyle ( \text { 0})},\iota }(x)\) was used, and we rely on the above strategy instead. However, the problem does not arise in (5.24), since it does not involve \(x={e}_{\iota }+{e}_{\kappa }\). This problem does not arise in (5.26) either, since it is zero when \(x={e}_{\iota }+{e}_{\kappa }\) (recall also ((6.16))).
In conclusion, all bounds that are used in the general analysis of [12], as summarized in Sect. 5.3, are monotone decreasing in d.
1.4 B.4 Monotonicity of Bounds on the General Analysis Coefficients
In this section we discuss the analysis of the generalized NoBLE analysis as explained in [12]. Our aim is to show that the monotonicity of the bounds on the coefficients implies that if a bootstrap argument, as described in Cornerstone 2.3, is successful in the given dimension \(d'=30\), then the bootstrap will be successful in every larger dimension \(d\ge d'\). For this, we fix the assumed bounds \(\Gamma _i, c_{n,l,S}\) and use them uniformly for all \(d\ge 30\). We next explain how we can see that the success of the bootstrap argument for \(d=30\) implies that for \(d\ge 30\), splitting between the various bootstrap function \(f_i(z)\) for \(i=1,2,3\):
Monotonicity of Success for the Initialization and Improvement of \(f_1\). We start with the bootstrap function
In (A.7) we have already seen the bound on \(f_1(z_I)\), which is clearly monotone decreasing in d. This deals with the initialization.
For \(z\in (z_I,z_c)\), the bounds on \(f_1(z)\) as given in [12, (3.5)] can be bounded uniformly in d as follows. In our argument, we write \(\beta _\bullet (d)\) for the parameter \(\beta _\bullet \) in dimension d. Note that the analysis in the previous section implies the monotonicity of \(d\mapsto \beta _\bullet (d)\) for all \(\beta _\bullet (d)\) discussed in Sect. 5.3. This leads to
For \(\beta _{\scriptscriptstyle \mu }(d)\), which bounds \(g_z/g_z^{\iota }\), we note that
This implies that
We bound \(G_z({e}_{\iota })\) in terms of simple diagrams, see Appendix B.3. This creates a bound that is monotone decreasing. Thus, our bound on \(\beta _{\scriptscriptstyle \mu }(d)\) is decreasing in d as well.
Bounds on the Rewrite. We bound \(f_2\) and \(f_3\) using a rewrite as this made the analysis much clearer. To proceed we next show that all coefficients of the rewrite are monotone decreasing in d. This is done by checking each bound on the rewrite, as given in [12, Appendix D], one bound at a time.
For most bounds it is obvious that they are monotone in d, as they only use the bounds on the coefficients \(\beta _{\bullet }\) (which we showed are monotone already in the previous section). For this reason we only comment on three issues, for which it is not obvious that the bounds are monotone decreasing.
Regarding the bounds on [12, (D.4)] and [12, (D.5)], we note that we have defined \(\underline{\beta }_{\scriptscriptstyle \Psi }^{\scriptscriptstyle ( \text { 0})} = \underline{\beta }_{\scriptscriptstyle \sum \Pi }^{\scriptscriptstyle ( \text { 1})}=0\), so that the last terms in these lines are not a concern regarding monotonicity.
In the bounds on the remainder terms in [12, Steps 2–5 in Appendix D], the following terms appear:
We next derive bounds on these terms that are uniform in d.
The function \(\tfrac{x}{1-x^2}\) is monotone increasing on the interval [0, 1], and \(\mu \le \tfrac{\Gamma _1}{2d-1}\le \tfrac{\Gamma _1}{59}\) for \(d\ge 30\), so that
The term \(\alpha _{{\scriptscriptstyle F},z}\approx 1\), which plays a central role in the NoBLE rewrite and is defined in [12, (4.18)], is bounded from above and below. We require an upper bound that is decreasing and a lower bound that is increasing in d. The upper bound, stated in [12, (D.2)],
is clearly monotone, as we have chosen \(\underline{\beta }_{ \scriptscriptstyle \sum \Pi _{\alpha }}^{\scriptscriptstyle ( \text { 0})}=0\) and bound the other two terms using repulsive diagrams, see (5.43), (5.46). As \(\alpha _{{\scriptscriptstyle F},z}\) arises in the dominator of \({{\hat{G}}}_z(k)\), see [12, (1.37)], we require a monotone increasing lower bound on \(\alpha _{{\scriptscriptstyle F},z}\), to obtain then a bound on \({{\hat{G}}}_z(k)\) that is monotone decreasing. We use the lower bound in [12, (D.2)] that reads
The term in the brackets is bounded by
This sum of bounds in \(\zeta (d)\) is clearly decreasing in d, so that \(1-\zeta (d)\ge 1-\zeta (30)\). Let us remark that we have implicitly assumed that \(\zeta (d)<1\), which a relatively weak condition that we have verified numerically. The initial factor \(\tfrac{2d \mu }{1-\mu ^2}\) is monotone increasing in \(\mu \) and we know that
for all \(z\ge z_I\), by definition of \(z_I\). This means that
so that
Due to the factor \(\tfrac{2d-1}{2d-2}\) this is decreasing in d and not increasing as required for the lower bounds on \(\alpha _{{\scriptscriptstyle F},z}\). We can circumvent by simply using the uniform bound \(\tfrac{2d-1}{2d-2}\le \tfrac{59}{58}\), which we use in the implementation.
Monotonicity of Success for the Initialization and Improvement of \(f_2\). The bootstrap function \(f_2\), defined in (2.16), bounds \({{\hat{G}}}_z(k)\). The bounds for the initialization follow the same bounds as for the improvement, so we only discuss the improvement here.
From [12, (3.9)] and the bounds on \(\alpha _{{\scriptscriptstyle F},z}\) that we have derived above, we obtain
The definition (2.16) states
which creates a bound that holds uniformly for all \(d\ge 30\).
Monotonicity of Success for the Initialization and Improvement of \(f_3\). The bound on \(f_3\) is derived in multiple steps, so that we have to check the monotonicity of multiple expressions. All of these are quite similar and the required monotonicity always follows from the monotonicity of the NoBLE coefficients of the rewrite and the SRW integrals.
The bounds for the initialization of the bootstrap argument for \(f_3\) at \(z_I\) is given in [12, (3.30)–(3.31)]. To guarantee that we use a monotone bound we omit from \({\mathcal {J}}_{n,l}(x)\), as defined in [12, (3.30)], the term \(-\tfrac{1}{d} I_{n+3,l}(x)\) and use the spatial monotonicity of \(I_{n+3,l}(x)\) in \(|x_\mu |\) to ensure that we only use values for \(I_{n+3,l}(x+2{e}_{\iota })\) for which \(|x+2{e}_{\iota }|_{\infty }\le 2\). This results in a uniform bound on \(f_3(z_I)\).
The bound on \(f_3(z)\) for \(z\in (z_I,z_c)\) that is used in the improvement step of the bootstrap argument is stated in [12, (3.87)] and consists of many individual terms derived in the lines [12, (3.60)–(3.85)]. All these terms consist of simple products of bounds on the terms of the rewrite and SRW integrals, which, as argued before, are monotone decreasing in d.
To remove any doubt about monotonicity, we redefine some bounding coefficients whose definition included a factor \(\tfrac{2d-2}{2d-1}\):
This results in a bound in which each individual piece is monotone decreasing in d, so that the bound on \(f_3\) holds uniformly in \(d\ge 30\).
1.5 B.5 Conclusion for all \(d\ge 30\)
Our aim was that to show that our results, as stated in Theorem 1.1, Corollary 1.3, Theorem 1.4 and Theorem 1.5, hold for all \(d\ge d'=30\).
The proof of these results is described in Sect. 2. Regarding the proof we note that Cornerstones 2.1 and 2.2 hold regardless of the dimension, even for \(d\le 16\). Our restriction to \(d\ge 16\) for LT and \(d\ge 17\) for LA, respectively, is only necessary as Cornerstone 2.3 does not hold in smaller dimensions.
In Appendix B.4 we conclude a bound on the bootstrap functions that holds uniformly for \(d\ge d'\). Using our numerical verification in LAmonotone, we check that Cornerstone 2.3 holds using (only) our monotone bounds. In other words in \(d'=30\) our bootstrap was successful. As the bounds on the bootstrap function are uniform in d we know that Cornerstone 2.3 therefore also holds for \(d'\ge d\). For this reason, our analysis succeeds in all \(d\ge d'=30\). \(\square \)
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Fitzner, R., van der Hofstad, R. NoBLE for Lattice Trees and Lattice Animals. J Stat Phys 185, 13 (2021). https://doi.org/10.1007/s10955-021-02816-z
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s10955-021-02816-z


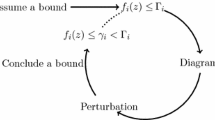

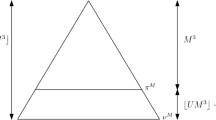






 and
and  as the set of all rib-walks from the origin 0 to x and
as the set of all rib-walks from the origin 0 to x and  to be the set of all rib-walks
to be the set of all rib-walks  and
and  for the set of all sausage-walks such that
for the set of all sausage-walks such that  and
and  and
and  as the set of all sausage-walks from the origin 0 to x and
as the set of all sausage-walks from the origin 0 to x and  to be the set of all sausage-walks
to be the set of all sausage-walks  and
and  for the set of all sausage-walks such that
for the set of all sausage-walks such that  and
and 







 . Closing the diagram, by including any path from u to v of length l, always creates a diagram with at least four bonds.
. Closing the diagram, by including any path from u to v of length l, always creates a diagram with at least four bonds.
 . The pieces of the backbone
. The pieces of the backbone 
 . These diagrams have the same shape as
. These diagrams have the same shape as  is weighted by a factor
is weighted by a factor  by a factor
by a factor 




