Abstract
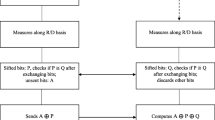
This paper presents a multi-bits transfer quantum protocol based on the three-stage quantum cryptography in which both parties use their own secret keys. In addition, a quantum three-stage protocol emerging with quantum error correction code is proposed. Finally, a cost comparison between the multi-bits transfer quantum protocol and the original three-stage quantum cryptography protocol is analyzed to show that our protocol has better performance.




Similar content being viewed by others
References
Von Neumann, J.: Mathematical foundations of quantum mechanics. Princeton University Press, Princeton (1955)
Feynman, R.P., Leighton, R.B., Sands, M.: Lectures on Physics, vol. III. Quantum mechanics. Addison-Wesley, Reading (1965)
Nielsen, M.A., Chuang, I.L.: Quantum computation and quantum information. Cambridge University Press, Cambridge (2000)
Feynman, R.P.: Simulating physics with computers. Int. J. Theor. Phys. 21, 6 (1982)
Shor, P.W.: Algorithms for quantum computation discrete logarithms and factoring, pp 124–134. IEEE Computer Society Press, Washington (1994)
Grover, L.: Quantum mechanics helps in searching for a needle in a haystack. Phys. Rev. Lett. 79, 325 (1997)
Nguyen, D.M., Kim, S.: Quantum key distribution protocol based on modified generalization of Deutsch-Jozsa algorithm in d-level quantum system. Int. J. Theor. Phys. 58, 1 (2019)
Gaitan, F.: Quantum error correction and fault tolerant quantum computing. CRC Press, Boca Raton (2007)
Shor, P.W.: Scheme for reducing decoherence in quantum computer memory. Phys. Rev. A 52, 2493 (1995)
Steane, A.M.: Error correcting codes in quantum theory. Phys. Rev. Lett. 77, 793 (1996)
Gottesman, D.: Stabilizer codes and quantum error correction. Ph.D. thesis, California Institute of Technology, Pasadena, CA (1997)
Bennett, C.H., Bessette, F., Brassard, G., Salvail, L., Smolin, J.: Experimental quantum cryptography. J Cryptol 5(1), 3–28 (1992)
Cai, Q.Y.: The ping-pong protocol can be attacked without eavesdropping. Phys. Rev. Lett., 91 (2003)
Kak, S.: A three-stage quantum cryptography protocol. Found Phys Lett 19, 293 (2006)
Mandal, S., et al.: Multi-photon implementation of three-stage quantum cryptography protocol. The International Conference on Information Networking (ICOIN) (2013)
Chan, K.W.C., Rifai, M.El., Verma, P.K., Kak, S.C., Chen, Y.: Security analysis of the multi-photon three-stage quantum key distribution. International Journal on Cryptography and Information Security (IJCIS), 5(3/4) (2015)
Parakh. A., van Brandwijk, J.: Correcting rotational errors in three stage QKD. In: 23rd International Conference on Telecommunications (ICT) (2016)
Thapliyal, K., Pathak, A.: Kak’s three-stage protocol of secure quantum communication revisited: hitherto unknown strengths and weaknesses of the protocol. Quantum Inf Process 17, 229 (2018)
Abdullah, A.A., Khalaf, R., Riza, M.: A realizable quantum Three-Pass protocol authentication based on Hill-Cipher algorithm. Math. Probl. Eng., 2015 (2015)
Nguyen, D.M., Kim, S.: Minimal-entanglement entanglement-assisted quantum error correction codes from modified circulant matrices. Symmetry 9(7), 122 (2017)
Nguyen, D.M., Kim, S.: Construction and complement circuit of a quantum stabilizer code with length 7. In: Proceedings of 8th International Conference on Ubiquitous and Future Networks (2016)
Nguyen, D.M., Kim, S.: Quantum stabilizer codes construction from hermitian Self-Orthogonal codes over GF(4). J. Commun. Netw. 20(3), 209–315 (2017)
Devitt, S.J., Munro, W.J., Nemoto, K.: Quantum error correction for beginners. Reports on Progress in Physics. 76(7) (2013)
Acknowledgements
This work was supported by the Research Program through the National Research Foundation of Korea (NRF-2016R1D1A1B03934653, NRF-2019R1A2C1005920).
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Nguyen, D., Kim, S. Multi-Bits Transfer Based on the Quantum Three-Stage Protocol with Quantum Error Correction Codes. Int J Theor Phys 58, 2043–2053 (2019). https://doi.org/10.1007/s10773-019-04098-4
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10773-019-04098-4