Abstract
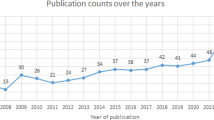
The study of security and computer privacy has become a significant focus in security and privacy research. To reflect a website's, service's, or app's privacy policies, they're frequently used as a beginning step for researchers investigating the reliability of stated data regulations, user comprehension of policy, or user control methods. It's challenging to collect information about privacy practices from Internet resources like websites and mobile applications for analysis because of the wide variations in the structure, presentation, and content. Most computer privacy studies attempt to test new methods for detecting, classifying, and analyzing computer privacy content. However, numerous papers have been published to promote research activities, and no trace of any bibliometric analysis work on computer privacy demonstrates research trends. By conducting a thorough analysis of computer privacy studies, it searches the Scopus database, which contains over 2000 papers published between 1976 and 2020. Using the bibliometric analysis technique, this study examines research activity in Europe, South America, and other continents. This work investigated the number of papers published, citations, research area, keywords, institutions, topics, and researchers in detail. An overview of the research efforts is followed by listing the words into a classification of computer privacy analysis tools, emphasizing the significance of a computer privacy research study. According to the investigation findings, there are numerous significant implications of research efforts in Europe compared to other continents. Finally, we summarize the review findings for each part by highlighting potential future research directions.




Similar content being viewed by others
References
Pimple, K.D.: Emerging pervasive information and communication technologies (PICT): ethical challenges, opportunities and safeguards (2014)
Torra, V.: Random dictatorship for privacy-preserving social choice. Int. J. Inf. Secur. 19(5), 537–545 (2020). https://doi.org/10.1007/S10207-019-00474-7
Ware, W.: Records, computers and the rights of citizens. Educ. Res. 2(11), 18–19 (1973). https://doi.org/10.3102/0013189x002011018
Utz, C., Degeling, M., Fahl, S., Schaub, F., Holz, T.: (Un)informed consent: studying GDPR consent notices in the field. In: Proceedings of the ACM Conference on Computer and Communications Security, pp. 973–990, (2019). https://doi.org/10.1145/3319535.3354212
Reidenberg, J.R., Russell, N.C., Callen, A., Qasir, S., Norton, T.: Privacy harms and the effectiveness of the notice and choice framework. SSRN Electron. J. (2018). https://doi.org/10.2139/ssrn.2418247
Hölzl, M., Roland, M., Mir, O., Mayrhofer, R.: Disposable dynamic accumulators: toward practical privacy-preserving mobile eIDs with scalable revocation. Int. J. Inf. Secur. 19(4), 401–417 (2020). https://doi.org/10.1007/S10207-019-00458-7
Obar, J.A., Oeldorf-Hirsch, A.: The biggest lie on the Internet: ignoring the privacy policies and terms of service policies of social networking services. Inf. Commun. Soc. 23(1), 128–147 (2020). https://doi.org/10.1080/1369118X.2018.1486870
Bennett, C.J., Parsons, C.: Privacy and surveillance: the multidisciplinary literature on the capture, use, and disclosure of personal information in cyberspace. Oxford Handb. Internet Stud. (2016). https://doi.org/10.1093/oxfordhb/9780199589074.013.0023
Jeff Smith, H., Dinev, T., Xu, H.: Information privacy research: an interdisciplinary review. MIS Q. Manag. Inf. Syst. 35(4), 989–1015 (2011). https://doi.org/10.2307/41409970
Chan, Y., Greenaway, K.: Theoretical explanations for firms’ information privacy behaviors. J. Assoc. Inf. Syst. 6(6), 171–198 (2005). https://doi.org/10.17705/1jais.00068
Awad, N.F., Krishnan, M.S.: The personalization privacy paradox: an empirical evaluation of information transparency and the willingness to be profiled online for personalization. MIS Q. Manag. Inf. Syst. 30(1), 13–28 (2006). https://doi.org/10.2307/25148715
Earp, J.B., Baumer, D.: Innovative web use to learn about consumer behavior and online privacy. Commun. ACM 46(4), 81–83 (2003). https://doi.org/10.1145/641205.641209
Paine, C., Reips, U.D., Stieger, S., Joinson, A., Buchanan, T.: Internet users’ perceptions of ‘privacy concerns’ and ‘privacy actions.’ Int. J. Hum. Comput. Stud. 65(6), 526–536 (2007). https://doi.org/10.1016/j.ijhcs.2006.12.001
Ang, P.H.: The role of self-regulation of privacy and the internet. J. Interact. Advert. 1(2), 1–9 (2001). https://doi.org/10.1080/15252019.2001.10722046
Helles, R., Lomborg, S.: Regulatory response? Tracking the influence of technological developments on privacy regulation in Denmark from 2000 to 2011. Policy Internet 5(3), 289–303 (2013). https://doi.org/10.1002/1944-2866.POI334
Strauss, J., Rogerson, K.S.: Policies for online privacy in the United States and the European Union. Telemat. Inform. 19(2), 173–192 (2002). https://doi.org/10.1016/S0736-5853(01)00012-0
Uchidiuno, J., Manweiler, J., Weisz, J.D.: Privacy and fear in the drone era: preserving privacy expectations through technology. In: Conference on human factors in computing systems - proceedings, vol 2018. https://doi.org/10.1145/3170427.3188457
Jensen, C., Potts, C.: Privacy policies as decision-making tools: an evaluation of online privacy notices. Conf. Hum. Factors Comput. Syst. Proc. 6(1), 471–478 (2004)
Tsai, J.Y., Egelman, S., Cranor, L., Acquisti, A.: The effect of online privacy information on purchasing behavior: an experimental study. Inf. Syst. Res. 22(2), 254–268 (2011). https://doi.org/10.1287/isre.1090.0260
Culnan, M.J., Armstrong, P.K.: Information privacy concerns, procedural fairness, and impersonal trust: an empirical investigation. Organ. Sci. 10(1), 104–115 (1999). https://doi.org/10.1287/orsc.10.1.104
Gerlach, J., Widjaja, T., Buxmann, P.: Handle with care: how online social network providers’ privacy policies impact users’ information sharing behavior. J. Strateg. Inf. Syst. 24(1), 33–43 (2015). https://doi.org/10.1016/j.jsis.2014.09.001
Mollick, J.S., Mykytyn, P.P.: An empirical investigation on the effects of privacy policies on perceived fairness of online vendors. J. Internet Commer. 8(1–2), 88–112 (2009). https://doi.org/10.1080/15332860903341356
Schwaig, K.S., Kane, G.C., Storey, V.C.: Compliance to the fair information practices: how are the Fortune 500 handling online privacy disclosures? Inf. Manag. 43(7), 805–820 (2006). https://doi.org/10.1016/j.im.2006.07.003
Bansal, G., Zahedi, F.M., Gefen, D.: Do context and personality matter? Trust and privacy concerns in disclosing private information online. Inf. Manag. 53(1), 1–21 (2016). https://doi.org/10.1016/j.im.2015.08.001
Joinson, A.N., Reips, U.D., Buchanan, T., Schofield, C.B.P.: Privacy, trust, and self-disclosure online. Hum. Comput. Interact. 25(1), 1–24 (2010). https://doi.org/10.1080/07370020903586662
Taddei, S., Contena, B.: Privacy, trust and control: which relationships with online self-disclosure? Comput. Hum. Behav. 29(3), 821–826 (2013). https://doi.org/10.1016/j.chb.2012.11.022
Dehdarirad, T., Villarroya, A., Barrios, M.: Research on women in science and higher education: a bibliometric analysis. Scientometrics 103(3), 795–812 (2015). https://doi.org/10.1007/s11192-015-1574-x
Wu, X., Chen, X., Zhan, F.B., Hong, S.: Global research trends in landslides during 1991–2014: a bibliometric analysis. Landslides 12(6), 1215–1226 (2015). https://doi.org/10.1007/s10346-015-0624-z
Olijnyk, N.V.: A quantitative examination of the intellectual profile and evolution of information security from 1965 to 2015. Scientometrics 105(2), 883–904 (2015). https://doi.org/10.1007/s11192-015-1708-1
Anyi, K.W.U., Zainab, A.N., Anuar, N.B.: Bibliometric studies on single journals: a review. Malaysian Journal of Library and Information Science, vol. 14, no. 1. pp. 17–55, (2009). Accessed from 21 Oct 2021. [Online]. Available: http://ijie.um.edu.my/index.php/MJLIS/article/view/6951
José de Oliveira, O., Francisco da Silva, F., Juliani, F., César Ferreira Motta Barbosa, L., Vieira Nunhes, T.: Bibliometric method for mapping the state-of-the-art and identifying research gaps and trends in literature: an essential instrument to support the development of scientific Projects. In: Scientometrics Recent Advances (2019)
Barev, T.J., Janson, A.: Towards an integrative understanding of privacy nudging – systematic review and research Agenda. In: 18th Annu. Pre-ICIS Work. HCI Res. MIS, (2019). Accessed from 21 Oct 2021. [Online]. Available: https://www.alexandria.unisg.ch/258828/
Ngoc, B.T., Van, B.D., The, Q.P.: Privacy, security, and policies: a review of problems and solutions with semantic web technologies. Adv. Intell. Syst. Comput. 1013, 1–10 (2020). https://doi.org/10.1007/978-981-32-9186-7_1
Kokolakis, S.: Privacy attitudes and privacy behaviour: a review of current research on the privacy paradox phenomenon. Comput. Secur. 64, 122–134 (2017). https://doi.org/10.1016/j.cose.2015.07.002
O’Loughlin, K., Neary, M., Adkins, E.C., Schueller, S.M.: Reviewing the data security and privacy policies of mobile apps for depression. Internet Interv. 15, 110–115 (2019). https://doi.org/10.1016/j.invent.2018.12.001
Sambada, J., Bhayani, S.: A review of literature on consumer privacy concerns and behaviour. Int. J. Manag. Stud. V(3(9)), 23 (2018). https://doi.org/10.18843/ijms/v5i3(9)/04
Shen, N., et al.: Understanding the patient privacy perspective on health information exchange: a systematic review. Int. J. Med. Inform. 125, 1–12 (2019). https://doi.org/10.1016/j.ijmedinf.2019.01.014
Pattakou, A., Kalloniatis, C.: Security and privacy under a unified framework: a review. personales.upv.es, (2018). Accessed from 27 Feb 2023. [Online]. Available: http://personales.upv.es/thinkmind/dl/journals/sec/sec_v11_n12_2018/sec_v11_n12_2018_3.pdf
Mellado, D., Blanco, C., Sánchez, L.E., Fernández-Medina, E.: A systematic review of security requirements engineering. Comput. Stand. Interfaces 32(4), 153–165 (2010). https://doi.org/10.1016/j.csi.2010.01.006
Pattakou, A., Kalloniatis, C.: Security and privacy requirements engineering methods for traditional and cloud-based systems: a review. Cloud Computing, no. c, p. 7, (2017). Accessed from 27 Feb 2023. [Online]. Available: https://www.academia.edu/download/51928079/cloud_computing_2017_full.pdf#page=156
Wang, Y., et al.: A survey on Metaverse: fundamentals, security, and privacy. IEEE Commun. Surv. Tutor. (2022). https://doi.org/10.1109/COMST.2022.3202047
Juels, A.: RFID security and privacy: a research survey. IEEE J. Sel. Areas Commun. 24(2), 381–394 (2006). https://doi.org/10.1109/JSAC.2005.861395
Tahsien, S.M., Karimipour, H., Spachos, P.: Machine learning based solutions for security of Internet of Things (IoT): a survey. J. Netw. Comput. Appl. (2020). https://doi.org/10.1016/j.jnca.2020.102630
Santos, R., Costa, A.A., Grilo, A.: Bibliometric analysis and review of building information modelling literature published between 2005 and 2015. Autom. Constr. 80, 118–136 (2017). https://doi.org/10.1016/j.autcon.2017.03.005
Zhao, X., Zuo, J., Wu, G., Huang, C.: A bibliometric review of green building research 2000–2016. Archit. Sci. Rev. 62(1), 74–88 (2019). https://doi.org/10.1080/00038628.2018.1485548
Koskinen, J., et al.: How to use bibliometric methods in evaluation of scientific research? An example from Finnish schizophrenia research. Nord. J. Psychiatry 62(2), 136–143 (2008). https://doi.org/10.1080/08039480801961667
Archambault, É., Campbell, D., Gingras, Y., Larivière, V.: Comparing bibliometric statistics obtained from the web of science and Scopus. J. Am. Soc. Inf. Sci. Technol. 60(7), 1320–1326 (2009). https://doi.org/10.1002/asi.21062
Wilson, V., Grant, M.J.: Evidence based library and information practice: what’s in it for you? Health Inf. Libr. J. 30(2), 89–91 (2013). https://doi.org/10.1111/hir.12031
Loomes, D.E., Van Zanten, S.V.: Bibliometrics of the top 100 clinical articles in digestive disease. Gastroenterology (2013). https://doi.org/10.1053/j.gastro.2013.02.013
Mao, G., Zou, H., Chen, G., Du, H., Zuo, J.: Past, current and future of biomass energy research: a bibliometric analysis. Renew. Sustain. Energy Rev. 52, 1823–1833 (2015). https://doi.org/10.1016/j.rser.2015.07.141
Fahimnia, B., Sarkis, J., Davarzani, H.: Green supply chain management: a review and bibliometric analysis. Int. J. Prod. Econ. 162, 101–114 (2015). https://doi.org/10.1016/j.ijpe.2015.01.003
Falagas, M.E., Pitsouni, E.I., Malietzis, G.A., Pappas, G.: Comparison of PubMed, scopus, web of science, and Google scholar: strengths and weaknesses. Wiley Online Libr. 22(2), 338–342 (2008). https://doi.org/10.1096/fj.07-9492LSF
Kulkarni, A.V., Aziz, B., Shams, I., Busse, J.W.: Comparisons of citations in web of science, Scopus, and Google Scholar for articles published in general medical journals. JAMA 302(10), 1092–1096 (2009). https://doi.org/10.1001/jama.2009.1307
Baas, J., Schotten, M., Plume, A., Cote, G., Karimi, R.: Scopus as a curated, high-quality bibliometric data source for academic research in quantitative science studies. Quant. Sci. Stud. 1(1), 377–386 (2020). https://doi.org/10.1162/qss_a_00019
Singh, V.K., Singh, P., Karmakar, M., Leta, J., Mayr, P.: The journal coverage of web of science, scopus and dimensions: a comparative analysis. Scientometrics 126(6), 5113–5142 (2021). https://doi.org/10.1007/s11192-021-03948-5
Wang, H., Liu, M., Hong, S., Zhuang, Y.: A historical review and bibliometric analysis of GPS research from 1991–2010. Scientometrics 95(1), 35–44 (2013). https://doi.org/10.1007/s11192-012-0853-z
van Eck, N.J., Waltman, L.: Visualizing bibliometric networks. In: Measuring scholarly impact, pp. 285–320. Springer International Publishing, Cham (2014)
White, H.D., McCain, K.W.: Visualizing a discipline: an author co-citation analysis of information science, 1972–1995. J. Am. Soc. Inf. Sci. 49(4), 327–355 (1998)
Zupic, I., Čater, T.: Bibliometric methods in management and organization. Organ. Res. Methods 18(3), 429–472 (2015). https://doi.org/10.1177/1094428114562629
Wang, N., Liang, H., Jia, Y., Ge, S., Xue, Y., Wang, Z.: Cloud computing research in the IS discipline: a citation/co-citation analysis. Decis. Support. Syst. 86, 35–47 (2016). https://doi.org/10.1016/j.dss.2016.03.006
Verma, S.: Mapping the intellectual structure of the big data research in the IS discipline: a citation/co-citation analysis. Inf. Resour. Manag. J. 31(1), 21–52 (2018). https://doi.org/10.4018/IRMJ.2018010102
Hallinger, P., Kovačević, J.: A bibliometric review of research on educational administration: science mapping the literature, 1960 to 2018. Rev. Educ. Res. 89(3), 335–369 (2019). https://doi.org/10.3102/0034654319830380
F. O. R. H. A. Century.: Who picks up the tab for science?. BU Today, pp. 1–13, (2016). Accessed from 21 Oct 2021. [Online]. Available: https://scholar.google.com/scholar?hl=en&as_sdt=0%2C5&q=Who+picks+up+the+tab+for+science%3F+For+half+a+century%2C+the+government+funded+research.+Times+are+changing&btnG
Schiermeier, Q.: How Europe’s €100-billion science fund will shape 7 years of research. Nature 591(7848), 20–21 (2021). https://doi.org/10.1038/d41586-021-00496-z
Qiu, J.: China goes back to basics on research funding. Nature 507(7491), 148–149 (2014). https://doi.org/10.1038/507148a
UNESCO Institute for Statistics.: Global Investments in R&D A snapshot of R&D expenditure Figure 1. Regional R&D investments Shares of world R&D expenditure (GERD) by region, (2020). Accessed from 07 Mar 2023. [Online]. Available: https://uis.unesco.org/sites/default/files/documents/fs59-global-investments-rd-2020-en.pdf
Björk, B.C.: Acceptance rates of scholarly peer-reviewed journals: a literature survey. El Prof. Inf. (2019). https://doi.org/10.3145/epi.2019.jul.07
Buela-Casal, G., Gutiérrez-Martínez, O., Bermúdez-Sánchez, M.P., Vadillo-Muñoz, O.: Comparative study of international academic rankings of universities. Scientometrics 71(3), 349–365 (2007). https://doi.org/10.1007/s11192-007-1653-8
Harzing, A.W.: The publish or perish book, (2010). Accessed from 28 Feb 2023. [Online]. Available: http://www.harzing.info/download/popbook12.pdf
Sadeh, N.: Bibliography, (2021). https://normsadeh.org
Flavián, C., Guinalíu, M.: Consumer trust, perceived security and computer privacy: three basic elements of loyalty to a web site. Ind. Manag. Data Syst. 106(5), 601–620 (2006). https://doi.org/10.1108/02635570610666403
Audich, D.: Enhancing readability of privacy policies through ontologies, (2018). Accessed from 21 Oct 2021. [Online]. Available: http://atrium.lib.uoguelph.ca/xmlui/handle/10214/12550
Clark, T.C., Westin, A.F.: Privacy and freedom. Calif. Law Rev. 56(3), 911 (1968). https://doi.org/10.2307/3479272
McDonald, A., Cranor, L.F.: The cost of reading privacy policies. I/S A J. Law Policy Inf. Soc., vol. 4, no. 543, p. 183, (2001). Accessed from 21 Sep 2021. [Online]. Available: https://heinonline.org/hol-cgi-bin/get_pdf.cgi?handle=hein.journals/isjlpsoc4§ion=27
McDonald, A.M., Reeder, R.W., Kelley, P.G., Cranor, L.F.: A comparative study of online privacy policies and formats. In: Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics), pp. 37–55. LNCS, Heidelberg (2009)
Milne, G.R., Culnan, M.J.: Strategies for reducing online privacy risks: why consumers read (or don’t read) online privacy notices. J. Interact. Mark. 18(3), 15–29 (2004). https://doi.org/10.1002/dir.20009
Termsfeed.: Generic computer privacy template, (2017). https://www.termsfeed.com/pdf.assets/pdf/privacy-policy-template
Docracy.: An open source computer privacy for mobile apps, (2011)
3DCart.: Create an online store with 3dcart store builder, (2018)
Kolter, J., Pernul, G.: Generating user-understandable privacy preferences. In: Proceedings - International Conference on Availability, Reliability and Security, pp. 299–306. ARES, (2009). https://doi.org/10.1109/ARES.2009.89
Lucas, M., Franco, M., Patricio, M.: Computer privacy generator, (2017). https://privacypolicygenerator.info/
Miao, D.: PrivacyInformer: an automated privacy description generator for the MIT app inventor, (2014). Accessed from 23 Oct 2021. [Online]. Available: https://dspace.mit.edu/handle/1721.1/95523
Apolinarski, W., Handte, M., Marron, P.J.: Automating the generation of privacy policies for context-sharing applications. In: Proceedings - 2015 International Conference on Intelligent Environments, pp. 73–80. IE, (2015). https://doi.org/10.1109/IE.2015.18
Anderson, A. et al.: extensible access control markup language (xacml) version 1.0,” OASIS, 2003. Accessed from 23 Oct 2021. [Online]. Available: http://xml.coverpages.org/XACMLv20CD-CoreSpec.pdf
Sandhu, R., Samarati, P.: Authentication, access control, and audit. ACM Comput. Surv. 28(1), 241–243 (1996). https://doi.org/10.1145/234313.234412
Open Geospatial Consortium.: Geospatial eXtensible access control markup language (GeoXACML), (2011)
Park, J., Sandhu, R.: The UCON ABC usage control model. ACM Trans. Inf. Syst. Secur. 7(1), 128–174 (2004). https://doi.org/10.1145/984334.984339
Pretschner, A., Hilty, M., Basin, D.: Distributed usage control. Commun. ACM 49(9), 39–44 (2006). https://doi.org/10.1145/1151030.1151053
Lämmel, R., Pek, E.: Understanding privacy policies. Empir. Softw. Eng. 18(2), 310–374 (2013). https://doi.org/10.1007/s10664-012-9204-1
Harkous, H., Fawaz, K., Lebret, R., Schaub, F., Shin, K.G., Aberer, K.: Polisis: automated analysis and presentation of privacy policies using deep learning. In: Proceedings of the 27th USENIX Security Symposium, pp. 531–548, (2018)
Evans, N.J., Phua, J., Lim, J., Jun, H.: Disclosing instagram influencer advertising: the effects of disclosure language on advertising recognition, attitudes, and behavioral intent. J. Interact. Advert. 17(2), 138–149 (2017). https://doi.org/10.1080/15252019.2017.1366885
Bokaei Hosseini, M., Breaux, T.D., Niu, J.: Inferring ontology fragments from semantic role typing of lexical variants. In: Lecture Notes in Computer Science (Including Subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics), vol. 10753, pp. 39–56. LNCS, (2018). https://doi.org/10.1007/978-3-319-77243-1_3.
Cranor, L.F., Arjula, M., Guduru, P.: Use of a P3P user agent by early adopters. In: Proceedings of the ACM conference on computer and communications security, no. WORKSHOP, pp. 1–10, (2002). https://doi.org/10.1145/644527.644528
Marella, A., Pan, C., Hu, Z., Schuab, F., Ur, B., Cranor, L.F.: Assessing privacy awareness from browser Plugins, cups.cs.cmu.edu, no. July, pp. 1–2, (2014). Accessed from 21 Oct 2021. [Online]. Available: http://cups.cs.cmu.edu/soups/2014/posters/soups2014_posters-paper29.pdf
Morel, V., Pardo, R.: SoK: three facets of privacy policies. In: WPES 2020 - Proceedings of the 19th Workshop on Privacy in the Electronic Society, pp. 41–56, (2020). https://doi.org/10.1145/3411497.3420216
Yu, L., Zhang, T., Luo, X., Xue, L., Chang, H.: Toward automatically generating computer privacy for android apps. IEEE Trans. Inf. Forensics Secur. 12(4), 865–880 (2017). https://doi.org/10.1109/TIFS.2016.2639339
Zimmeck, S., et al.: MAPS: scaling privacy compliance analysis to a million apps. Proc. Priv. Enhanc. Technol. 2019(3), 66–86 (2019). https://doi.org/10.2478/popets-2019-0037
Slavin, R. et al.: Toward a framework for detecting computer privacy violations in android application code. In: Proceedings - International Conference on Software Engineering, vol. 14–22, pp. 25–36, (2016). https://doi.org/10.1145/2884781.2884855
Wang, X., Qin, X., Hosseini, M.B., Slavin, R., Breaux, T.D., Niu, J.: GUILeak, in dl.acm.org, pp. 37–47, (2018). https://doi.org/10.1145/3180155.3180196
Reyes, I., et al.: ‘Won’t somebody think of the children? Examining COPPA compliance at scale. Proc. Priv. Enhanc. Technol. 2018(3), 63–83 (2018). https://doi.org/10.1515/popets-2018-0021
Okoyomon, E. et al.: On the ridiculousness of notice and consent: contradictions in app privacy policies. In: Work. Technol. Consum. Prot. (ConPro 2019), conjunction with 39th IEEE Symp. Secur. Privacy, pp. 1–7, (2019). Accessed from 23 Oct 2021. [Online]. Available: https://dspace.networks.imdea.org/handle/20.500.12761/690
Andow, B. et al.: Policylint: investigating internal computer privacy contradictions on google play. In: Proceedings of the 28th USENIX Security Symposium, pp. 585–602, (2019). Accessed from 23 Oct 2021. [Online]. Available: https://www.usenix.org/conference/usenixsecurity19/presentation/andow
Chen, S. et al.: An empirical assessment of security risks of global android banking apps. In: Proceedings - International Conference on Software Engineering, pp. 1310–1322, (2020). https://doi.org/10.1145/3377811.3380417
Enck, W., et al.: TaintDroid: an information-flow tracking system for realtime privacy monitoring on smartphones. ACM Trans. Comput. Syst. (2014). https://doi.org/10.1145/2619091
Reinhardt, D., Borchard, J., Hurtienne, J.: Visual interactive computer privacy: the beter choice?, (2021). https://doi.org/10.1145/3411764.3445465
de Jong, S., Spagnuelo, D.: Iconified representations of privacy policies: a GDPR perspective. In: Advances in Intelligent Systems and Computing, vol. 1160, pp. 796–806. AISC, (2020). https://doi.org/10.1007/978-3-030-45691-7_75
Schwartz, P., Solove, D.: “Notice & Choice,” digitalads.org, (2009). Accessed from 23 Oct 2021. [Online]. Available: http://www.digitalads.org/sites/default/files/publications/digitalads_schwartz_solove_notice_choice_nplan_bmsg_memo.pdf
Oltramari, A., et al.: PrivOnto: a semantic framework for the analysis of privacy policies. Semant. Web 9(2), 185–203 (2018). https://doi.org/10.3233/SW-170283
Shayegh, P., Jain, V., Rabinia, A., Ghanavati, S.: Automated approach to improve IoT privacy policies. arxiv.org, (2019). Accessed from 23 Oct 2021. [Online]. Available: https://arxiv.org/abs/1910.04133
Zimmeck, S., Bellovin, S.M.: Privee: an architecture for automatically analyzing web privacy policies. In: Proceedings of the 23rd USENIX Security Symposium, pp. 1–16, (2014). Accessed from 23 Oct 2021. [Online]. Available: https://www.usenix.org/conference/usenixsecurity14/technical-sessions/presentation/zimmeck
Reagle, J., Cranor, L.F.: The platform for privacy preferences. Commun. ACM 42(2), 48–55 (1999). https://doi.org/10.1145/293411.293455
Kelley, P.G., Bresee, J., Cranor, L.F., Reeder, R.W.: A ‘nutrition label’ for privacy, (2009). https://doi.org/10.1145/1572532.1572538
König, U., Schallaböck, J.: Privacy preferences for E-Mail messages, (2011). Accessed from 23 Oct 2021. [Online]. Available: https://www.ietf.org/proceedings/78/slides/apparea-0.pdf
Rundle, M.C.: International personal data protection and digital identity management tools. SSRN Electron. J. (2011). https://doi.org/10.2139/ssrn.911607
Holtz, L.E., Zwingelberg, H., Hansen, M.: Computer privacy icons. In: Privacy and Identity Management for Life, pp. 279–285 (2011)
van den Berg, B., van der Hof, S.: What happens to my data? A novel approach to informing users of data processing practices. First Monday (2012). https://doi.org/10.5210/fm.v17i7.4010
Li, S., Da Xu, L., Zhao, S.: The internet of things: a survey. Inf. Syst. Front. 17(2), 243–259 (2015). https://doi.org/10.1007/s10796-014-9492-7
Das, A., Degeling, M., Smullen, D., Sadeh, N.: Personalized privacy assistants for the internet of things: providing users with notice and choice. IEEE Pervasive Comput. 17(3), 35–46 (2018). https://doi.org/10.1109/MPRV.2018.03367733
Langheinrich, M.: A privacy awareness system for ubiquitous computing environments. Lect. Notes Comput. Sci. (Incl. Subser. Lect. Notes Artif. Intell. Lect. Notes Bioinform.) 2498, 237–245 (2002). https://doi.org/10.1007/3-540-45809-3_19
Lee, H., Kobsa, A.: Privacy preference modeling and prediction in a simulated campuswide IoT environment. In: 2017 IEEE International Conference on Pervasive Computing and Communications, pp. 276–285. PerCom, (2017). https://doi.org/10.1109/PERCOM.2017.7917874
Emami-Naeini, P. et al.: Privacy expectations and preferences in an IoT world. In: Proceedings of the 13th Symposium on Usable Privacy and Security, SOUPS 2017. pp. 399–412, (2019). Accessed from 22 Feb 2019. [Online]. Available: https://www.usenix.org/conference/soups2017/technical-sessions/presentation/naeini
Mikusz, M., Houben, S., Davies, N., Moessner, K., Langheinrich, M.: Raising awareness of IoT sensor deployments. In: IET Conference Publications, vol. 2018, no. CP740, (2018). https://doi.org/10.1049/cp.2018.0009
Sweeney, L.: k-anonymity: a model for protecting privacy. Int. J. Uncertain. Fuzziness Knowl. Based Syst. 10(5), 557–570 (2002). https://doi.org/10.1142/S0218488502001648
Sklavos, N., Zaharakis, I.D.: Cryptography and security in internet of things (IoTs): models, schemes, and implementations, (2016). https://doi.org/10.1109/NTMS.2016.7792443
Hu, V., Kuhn, D., Ferraiolo, D.: J. V.- Computer, and U. 2015, “Attribute-based access control. ieeexplore.ieee.org, (2015). Accessed from 23 Oct 2021. [Online]. Available: https://ieeexplore.ieee.org/abstract/document/7042715/
Boldt, M., Rekanar, K.: Analysis and text classification of privacy policies from rogue and top-100 fortune global companies. Int. J. Inf. Secur. Priv. 13(2), 47–66 (2019). https://doi.org/10.4018/IJISP.2019040104
Amos, R., Acar, G., Lucherini, E., Kshirsagar, M., Narayanan, A., Mayer, J.: Privacy policies over time: curation and analysis of a million-document dataset. In: The Web Conference 2021 - Proceedings of the World Wide Web Conference, pp. 2165–2176. WWW, (2021). https://doi.org/10.1145/3442381.3450048
Flach, P.: Machine learning: the art and science of algorithms that make sense of data, (2012).
Fawcett, T.: “ROC graphs: Notes and practical considerations for researchers. Mach. Learn., vol. 31, no. 1, pp. 1–38, (2004). Accessed from 23 Oct 2021. [Online]. Available: https://citeseerx.ist.psu.edu/viewdoc/download?doi=10.1.1.123.4749&rep=rep1&type=pdf
Zhu, X., Davidson, I.: Knowledge discovery and data mining: challenges and realities, (2007)
Urban, T., Degeling, M., Holz, T., Pohlmann, N.: Your hashed IP address: Ubuntu. Perspectives on transparency tools for online advertising. In: ACM International Conference Proceeding Series, pp. 702–717, (2019). https://doi.org/10.1145/3359789.3359798
Bufalieri, L., La Morgia, M., Mei, A., Stefa, J.: GDPR: when the right to access personal data becomes a threat. In: Proceedings - 2020 IEEE 13th International Conference on Web Services, pp. 75–83. ICWS, (2020). https://doi.org/10.1109/ICWS49710.2020.00017
Hosseini, M.B., Breaux, T.D., Slavin, R., Niu, J., Wang, X.: Analyzing privacy policies through syntax-driven semantic analysis of information types. Inf. Softw. Technol. (2021). https://doi.org/10.1016/j.infsof.2021.106608
Fan, Y., et al.: Privacy preserving based logistic regression on big data. J. Netw. Comput. Appl. (2020). https://doi.org/10.1016/j.jnca.2020.102769
Mustapha, M., Krasnashchok, K., Al Bassit, A., Skhiri, S.: Computer privacy classification with XLNet (Short Paper). In: Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics), vol. 12484, pp. 250–257. LNCS, (2020). https://doi.org/10.1007/978-3-030-66172-4_16
Labani, S., Wadhwa, K., Asthana, S.: Basic approach to data analysis and writing of results and discussion sections. MAMC J. Med. Sci. 3(1), 6 (2017). https://doi.org/10.4103/mamcjms.mamcjms_50_16
Su, M.Y.: Using clustering to improve the KNN-based classifiers for online anomaly network traffic identification. J. Netw. Comput. Appl. 34(2), 722–730 (2011). https://doi.org/10.1016/j.jnca.2010.10.009
Kim, D.W., Yan, P., Zhang, J.: Detecting fake anti-virus software distribution webpages. Comput. Secur. 49, 95–106 (2015). https://doi.org/10.1016/j.cose.2014.11.008
Sarne, D., Schler, J., Singer, A., Sela, A., Tov, I.B.S.: Unsupervised topic extraction from privacy policies. In; The Web Conference 2019 - Companion of the World Wide Web Conference, pp. 563–568. WWW, (2019). https://doi.org/10.1145/3308560.3317585
Jardine, E.: Privacy, censorship, data breaches and Internet freedom: the drivers of support and opposition to Dark Web technologies. New Media Soc. 20(8), 2824–2843 (2018). https://doi.org/10.1177/1461444817733134
Robillard, J.M., et al.: Availability, readability, and content of privacy policies and terms of agreements of mental health apps. Internet Interv. (2019). https://doi.org/10.1016/j.invent.2019.100243
Tomuro, N., Lytinen, S., Hornsburg, K.: Automatic summarization of privacy policies using ensemble learning. In: CODASPY 2016 - Proceedings of the 6th ACM Conference on Data and Application Security and Privacy, pp. 133–135, (2016). https://doi.org/10.1145/2857705.2857741
Audich, D.A., Dara, R., Nonnecke, B.: Extracting keyword and keyphrase from online privacy policies. In: 2016 11th International Conference on Digital Information Management, pp. 127–132. ICDIM, (2016). https://doi.org/10.1109/ICDIM.2016.7829792
Fabian, B., Ermakova, T., Lentz, T.: Large-scale readability analysis of privacy policies. In: Proceedings - 2017 IEEE/WIC/ACM International Conference on Web Intelligence, pp. 18–25. WI, (2017). https://doi.org/10.1145/3106426.3106427
Audich, D.A., Dara, R., Nonnecke, B.: Computer privacy annotation for semi-automated analysis: a cost-effective approach. IFIP Adv. Inf. Commun. Technol. 528, 29–44 (2018). https://doi.org/10.1007/978-3-319-95276-5_3
Fan, W., He, J., Guo, M., Li, P., Han, Z., Wang, R.: Privacy preserving classification on local differential privacy in data centers. J. Parallel Distrib. Comput. 135, 70–82 (2020). https://doi.org/10.1016/j.jpdc.2019.09.009
Acknowledgements
The Ministry of Higher Education Malaysia supported this research for the Fundamental Research Grant Scheme with Project Code: FRGS/1/2023/ICT07/USM/02/1.
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest
All authors declare that they have no conflict of interest.
Ethical approval
This article does not contain any studies with human participants or animals performed by any of the authors.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Ali, A.S., Zaaba, Z.F. & Singh, M.M. The rise of “security and privacy”: bibliometric analysis of computer privacy research. Int. J. Inf. Secur. 23, 863–885 (2024). https://doi.org/10.1007/s10207-023-00761-4
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10207-023-00761-4