Abstract
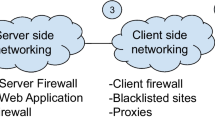
Cross-site scripting attacks represent one of the major security threats in today’s Web applications. Current approaches to mitigate cross-site scripting vulnerabilities rely on either server-based or client-based defense mechanisms. Although effective for many attacks, server-side protection mechanisms may leave the client vulnerable if the server is not well patched. On the other hand, client-based mechanisms may incur a significant overhead on the client system. In this work, we present a hybrid client-server solution that combines the benefits of both architectures. Our Proxy-based solution leverages the strengths of both anomaly detection and control flow analysis to provide accurate detection. We demonstrate the feasibility and accuracy of our approach through extended testing using real-world cross-site scripting exploits.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Appshield, Sanctum Inc. (2004)
Security focus-bugtraq (2010), http://www.securityfocus.com/archive/1
Bates, D., Barth, A., Jackson, C.: Regular expressions considered harmful in client-side XSS filters. In: 19th International Conference on World Wide Web, WWW 2010, pp. 91–100. ACM (2010)
Bisht, P., Venkatakrishnan, V.N.: XSS-GUARD: Precise Dynamic Prevention of Cross-Site Scripting Attacks. In: Zamboni, D. (ed.) DIMVA 2008. LNCS, vol. 5137, pp. 23–43. Springer, Heidelberg (2008)
Bonfante, G., Kaczmarek, M., Marion, J.-Y.: Control Flow Graphs as Malware Signatures. In: International Workshop on the Theory of Computer Viruses, TCV 2007, Nancy, France (2007)
Chen, S., Meseguer, J., Sasse, R., Wang, H.J., Wang, Y.-M.: A systematic approach to uncover security flaws in gui logic. In: IEEE Symposium on Security and Privacy, pp. 71–85. IEEE Computer Society (2007)
ComputerWeekly.com. Hackers broaden reach of cross-site scripting attacks (2007)
Cook, S.: A Web developer’s guide to cross-site scripting. t. r, SANS institute (2003)
Cova, M., Balzarotti, D., Felmetsger, V., Vigna, G.: Swaddler: An Approach for the Anomaly-Based Detection of State Violations in Web Applications. In: Kruegel, C., Lippmann, R., Clark, A. (eds.) RAID 2007. LNCS, vol. 4637, pp. 63–86. Springer, Heidelberg (2007)
Earl, C., Might, M., Horn, D.V.: Pushdown control-flow analysis of higher-order programs. In: The 2010 Workshop on Scheme and Functional Programming (2010)
Gundy, M.V., Chen, H.: Noncespaces: Using randomization to enforce information flow tracking and thwart cross-site scripting attacks. In: Annual Network & Distributed System Security Symposium (2009)
Jovanovic, N., Kruegel, C., Kirda, E.: Pixy: A static analysis tool for detecting web application vulnerabilities. In: IEEE Symposium on Security and Privacy, pp. 258–263. IEEE Computer Society (2006)
Kirda, E., Kruegel, C., Vigna, G., Jovanovic, N.: Noxes: a client-side solution for mitigating cross-site scripting attacks. In: 2006 ACM Symposium on Applied Computing, SAC 2006, pp. 330–337. ACM (2006)
Munoz, J.L., Forne, J., Esparza, O., Soriano, M.: Certificate revocation system implementation based on the merkle hash tree. International Journal of Information Security 2, 110–124 (2004), 10.1007/s10207-003-0026-4
OWASP. Top 10 2010 - the open web application security project (2007), http://www.owasp.org
OWASP. DOM based XSS (2011), https://www.owasp.org/index.php/DOM_Based_XSS
Raman, P.: JaSpin: JavaScript Based Anomaly Detection of Cross-Site Scripting Attacks. Master’s thesis, Carleton University, Ottawa, Ontario (2008)
Schwartz, N.: Steering clear of triples: Deriving the control flow graph directly from the Abstract Syntax Tree in C programs. Technical report, New York, NY, USA (1998)
Scott, D., Sharp, R.: Abstracting application-level web security. In: Proceedings of the 11th International Conference on World Wide Web, pp. 396–407. ACM (2002)
SpiderLabs. Analysis of lizamoon: Stored XSS via SQL injection (2011), http://blog.spiderlabs.com/2011/04/analysis-of-lizamoon-stored-xss-via-sql-injection.html
Sundareswaran, S., Squicciarini, A.C.: DeCore: Detecting Content Repurposing Attacks on Clients’ Systems. In: Jajodia, S., Zhou, J. (eds.) SecureComm 2010. LNICST, vol. 50, pp. 199–216. Springer, Heidelberg (2010)
Wassermann, G., Su, Z.: Static detection of cross-site scripting vulnerabilities. In: 30th International Conference on Software Engineering, pp. 171–180. ACM (2008)
Wurzinger, P., Platzer, C., Ludl, C., Kirda, E., Kruegel, C.: Swap: Mitigating XSS attacks using a reverse proxy. In: Proceedings of the 2009 ICSE Workshop on Software Engineering for Secure Systems, IWSESS 2009, pp. 33–39. IEEE Computer Society, Washington, DC (2009)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2012 IFIP International Federation for Information Processing
About this paper
Cite this paper
Sundareswaran, S., Squicciarini, A.C. (2012). XSS-Dec: A Hybrid Solution to Mitigate Cross-Site Scripting Attacks. In: Cuppens-Boulahia, N., Cuppens, F., Garcia-Alfaro, J. (eds) Data and Applications Security and Privacy XXVI. DBSec 2012. Lecture Notes in Computer Science, vol 7371. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-31540-4_17
Download citation
DOI: https://doi.org/10.1007/978-3-642-31540-4_17
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-31539-8
Online ISBN: 978-3-642-31540-4
eBook Packages: Computer ScienceComputer Science (R0)