Abstract
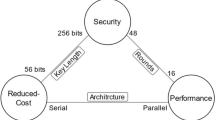
We motivate the notion of green cryptographic engineering, wherein we discuss several approaches to energy minimization or energy efficient cryptographic processes. We propose the amortization of computations paradigm in the design of cryptographic schemes; this paradigm can be used in line with existing approaches. We describe an example structure that exemplifies this paradigm and at the end of the paper we ask further research questions for this direction.
Chapter PDF
Similar content being viewed by others
References
3rd Generation Partnership Project, “Specification of the MILENAGE Algorithm Set: An Example Algorithm Set for the 3GPP Authentication and Key Generation Functions f1, f1*, f2, f3, f4, f5 and f5* - Document 2 (TS 35.206): Algorithm Specification; Document 5 (TR 35.909): Summary and Results of Design and Evaluation”, http://www.3gpp.org
Badel, S., Dağtekin, N., Nakahara, J., Ouafi, K., Reffé, N., Sepehrdad, P., Sušil, P., Vaudenay, S.: ARMADILLO: A Multi-purpose Cryptographic Primitive Dedicated to Hardware. In: Mangard, S., Standaert, F.-X. (eds.) CHES 2010. LNCS, vol. 6225, pp. 398–412. Springer, Heidelberg (2010)
Berger, T.P., Minier, M., Pousse, B.: Software Oriented Stream Ciphers Based upon FCSRs in Diversified Mode. In: Roy, B., Sendrier, N. (eds.) INDOCRYPT 2009. LNCS, vol. 5922, pp. 119–135. Springer, Heidelberg (2009)
Bicakci, K., Gultekin, H., Tavli, B.: The Impact of One-Time Energy Costs on Network Lifetime in Wireless Sensor Networks. IEEE Communications Letters 13(12), 905–907 (2009)
The Climate Group, “SMART 2020: Enabling the Low Carbon Economy in the Information Age” Global e-Sustainability Initiative, GeSI (2008)
de Meulenaer, G., Gosset, F., Standaert, F.-X., Pereira, O.: On the Energy Cost of Communication and Cryptography in Wireless Sensor Networks. In: Proc. WiMob 2008, pp. 580–585. IEEE (2008)
Delgado-Mohatar, O., Sierra, J.M., Brankovic, L., Fúster-Sabater, A.: An Energy-Efficient Symmetric Cryptography Based Authentication Scheme for Wireless Sensor Networks. In: Samarati, P., Tunstall, M., Posegga, J., Markantonakis, K., Sauveron, D. (eds.) WISTP 2010. LNCS, vol. 6033, pp. 332–339. Springer, Heidelberg (2010)
Dodis, Y., Steinberger, J.: Message Authentication Codes from Unpredictable Block Ciphers. In: Halevi, S. (ed.) CRYPTO 2009. LNCS, vol. 5677, pp. 267–285. Springer, Heidelberg (2009)
Gauravaram, P., Millan, W.L., Dawson, E., Viswanathan, K.: Constructing Secure Hash Functions by Enhancing Merkle-Damgård Construction. In: Batten, L.M., Safavi-Naini, R. (eds.) ACISP 2006. LNCS, vol. 4058, pp. 407–420. Springer, Heidelberg (2006)
Gilbert, H.: The Security of ”One-Block-to-Many” Modes of Operation. In: Johansson, T. (ed.) FSE 2003. LNCS, vol. 2887, pp. 376–395. Springer, Heidelberg (2003)
Greenemeier, L.: Can the World’s Telecoms Slash their Energy Consumption 1000-Fold? Scientific American (January 11, 2010)
Halevi, S., Hall, W.E., Jutla, C.S.: The Hash Function “Fugue”. SHA-3 Candidate Submission (September 15, 2009)
Kaps, J.-P., Gaubatz, G., Sunar, B.: Cryptography on a Speck of Dust. IEEE Computers 40(2), 38–44 (2007)
Kayalvizhi, R., Vijayalakshmi, M., Vaidehi, V.: Energy Analysis of RSA and ELGAMAL Algorithms for Wireless Sensor Networks. In: Meghanathan, N., Boumerdassi, S., Chaki, N., Nagamalai, D. (eds.) CNSA 2010. CCIS, vol. 89, pp. 172–180. Springer, Heidelberg (2010)
Lehmann, A., Tessaro, S.: A Modular Design for Hash Functions: Towards Making the Mix-Compress-Mix Approach Practical. In: Matsui, M. (ed.) ASIACRYPT 2009. LNCS, vol. 5912, pp. 364–381. Springer, Heidelberg (2009)
Pike Research, “’Green’ Telecom Equipment will Represent 46% of Network Capital Expenditures by 2013” Pike Research (June 9, 2009)
Preneel, B., Govaerts, R., Vandewalle, J.: Hash Functions Based on Block Ciphers: A Synthetic Approach. In: Stinson, D.R. (ed.) CRYPTO 1993. LNCS, vol. 773, pp. 368–378. Springer, Heidelberg (1994)
Rogaway, P., Steinberger, J.: Security/Efficiency Tradeoffs for Permutation-Based Hashing. In: Smart, N.P. (ed.) EUROCRYPT 2008. LNCS, vol. 4965, pp. 220–236. Springer, Heidelberg (2008)
Rogaway, P., Steinberger, J.: Constructing Cryptographic Hash Functions from Fixed-Key Blockciphers. In: Wagner, D. (ed.) CRYPTO 2008. LNCS, vol. 5157, pp. 433–450. Springer, Heidelberg (2008)
Shamir, A., Tauman, Y.: Improved Online/Offline Signature Schemes. In: Kilian, J. (ed.) CRYPTO 2001. LNCS, vol. 2139, pp. 355–367. Springer, Heidelberg (2001)
Shrimpton, T., Stam, M.: Building a Collision-Resistant Compression Function from Non-Compressing Primitives. In: Aceto, L., Damgård, I., Goldberg, L.A., Halldórsson, M.M., Ingólfsdóttir, A., Walukiewicz, I. (eds.) ICALP 2008, Part II. LNCS, vol. 5126, pp. 643–654. Springer, Heidelberg (2008)
Szczechowiak, P., Kargi, A., Scott, M., Collier, M.: On the Application of Pairing based Cryptography to Wireless Sensor Networks. In: Proc. WiSec 2009, pp. 1–12. ACM (2009)
Troutman, J., Rijmen, V.: Green Cryptography: Cleaner Engineering through Recycling. IEEE Security and Privacy 7(4), 71–73 (2009)
Weis, R., Effelsberg, W., Lucks, S.: Remotely Keyed Encryption with Java Cards: a Secure and Efficient Method to Encrypt Multimedia Streams. In: Proc. ICME 2000, pp. 537–540. IEEE (2000)
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2012 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Minier, M., Phan, R.C.W. (2012). Energy-Efficient Cryptographic Engineering Paradigm. In: Camenisch, J., Kesdogan, D. (eds) Open Problems in Network Security. iNetSec 2011. Lecture Notes in Computer Science, vol 7039. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-27585-2_7
Download citation
DOI: https://doi.org/10.1007/978-3-642-27585-2_7
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-27584-5
Online ISBN: 978-3-642-27585-2
eBook Packages: Computer ScienceComputer Science (R0)