Abstract
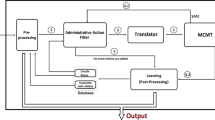
We present a new approach for automated knowledge-based verification of access control policies. The verification method not only discovers if a vulnerability exists, but also produces the strategies that can be used by the attacker to exploit the vulnerability. It investigates the information needed by the attacker to achieve the goal and whether he acquires that information when he proceeds through the strategy or not. We provide a policy language for specifying access control rules and the corresponding query language that is suited for expressing the properties we aim to verify. The policy language is expressive enough to handle integrity constraints and policy invariants. Finally, we compare the results and enhancements of the current method - implemented as a policy verification tool called PoliVer - over similar works in the context of dynamic access control policy verification.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Zhang, N., Ryan, M., Guelev, D.P.: Synthesising verified access control systems through model checking. J. Comput. Secur. 16(1), 1–61 (2008)
Becker, M.Y.: Specification and analysis of dynamic authorisation policies. In: CSF 2009: Proceedings of the 2009 22nd IEEE Computer Security Foundations Symposium, pp. 203–217. IEEE Computer Society, Washington, DC, USA (2009)
Dougherty, D.J., Fisler, K., Krishnamurthi, S.: Specifying and reasoning about dynamic access-control policies. In: Furbach, U., Shankar, N. (eds.) IJCAR 2006. LNCS (LNAI), vol. 4130, pp. 632–646. Springer, Heidelberg (2006)
Naldurg, P., Campbell, R.H.: Dynamic access control: preserving safety and trust for network defense operations. In: SACMAT 2003: Proceedings of the Eighth ACM Symposium on Access Control Models and Technologies, pp. 231–237. ACM, New York (2003)
Fisler, K., Krishnamurthi, S., Meyerovich, L.A., Tschantz, M.C.: Verification and change-impact analysis of access-control policies. In: ICSE 2005: Proceedings of the 27th International Conference on Software Engineering, pp. 196–205. ACM, New York (2005)
Becker, M.Y., Gordon, A.D., Fournet, C.: SecPAL: Design and semantics of a decentralised authorisation language. Technical report, Microsoft Research, Cambridge (September 2006)
Li, N., Mitchell, J.C., Winsborough, W.H.: Design of a role-based trust management framework. In: Proceedings of the 2002 IEEE Symposium on Security and Privacy, pp. 114–130. IEEE Computer Society Press, Los Alamitos (2002)
Bell, D., LaPadula., L.J.: Secure computer systems: Mathematical foundations and model. Technical report, The Mitre Corporation (1976)
Bell, D.E.: Looking back at the bell-la padula model. In: ACSAC 2005: Proceedings of the 21st Annual Computer Security Applications Conference, pp. 337–351. IEEE Computer Society, Washington, DC, USA (2005)
Becker, M.Y., Nanz, S.: A logic for state-modifying authorization policies. ACM Trans. Inf. Syst. Secur. 13(3), 1–28 (2010)
Fox, M., Long, D.: Pddl2.1: An extension to pddl for expressing temporal planning domains. Journal of Artificial Intelligence Research 20, 61–124 (2003)
Koleini, M., Ryan, M.: A knowledge-based verification method for dynamic access control policies. Technical report, University of Birmingham, School of Computer Science (2010), http://www.cs.bham.ac.uk/~mdr/research/projects/11-AccessControl/poliver/
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2011 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Koleini, M., Ryan, M. (2011). A Knowledge-Based Verification Method for Dynamic Access Control Policies. In: Qin, S., Qiu, Z. (eds) Formal Methods and Software Engineering. ICFEM 2011. Lecture Notes in Computer Science, vol 6991. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-24559-6_18
Download citation
DOI: https://doi.org/10.1007/978-3-642-24559-6_18
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-24558-9
Online ISBN: 978-3-642-24559-6
eBook Packages: Computer ScienceComputer Science (R0)