Abstract
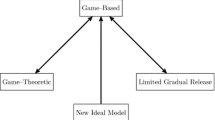
We put forward the notion of a verifiably secure device, in essence a stronger notion of secure computation, and achieve it in the ballot-box model. Verifiably secure devices
-
1
Provide a perfect solution to the problem of achieving correlated equilibrium, an important and extensively investigated problem at the intersection of game theory, cryptography and efficient algorithms; and
-
1
Enable the secure evaluation of multiple interdependent functions.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Aumann, R.: Subjectivity and correlation in randomized strategies. J. Math. Econ. 1, 67–96 (1974)
Bárány, I.: Fair distribution protocols or how the players replace fortune. Mathematics of Operation Research 17, 327–341 (1992)
Barrington, D.: Bounded-width polynomial-size branching programs recognize exactly those languages in NC1. In: Proceedings of STOC (1986)
Ben-Or, M., Goldwasser, S., Wigderson, A.: Completeness Theorems for Non-Cryptographic Fault-Tolerant Distributed Computation. In: Proceedings of STOC (1988)
Ben-Porath, E.: Correlation without mediation: Expanding the set of equilibria outcomes by “cheap” pre-play procedures. Journal of Economic Theory 80, 108–122 (1998)
Canetti, R.: Universally composable security. A new paradaigm for cryptographic protocols. In: Proceedings of FOCS (2001)
Cleve, R.: Limits on the Security of Coin Flips When Half the Processors are Faulty. In: Proceedings of STOC (1986)
Dodis, Y., Halevi, S., Rabin, T.: A Cryptographic Solution to a Game Theoretic Problem. In: Bellare, M. (ed.) CRYPTO 2000. LNCS, vol. 1880, Springer, Heidelberg (2000)
Dodis, Y., Micali, S.: Parallel Reducibility for Information-Theoretically Secure Computation. In: Bellare, M. (ed.) CRYPTO 2000. LNCS, vol. 1880, Springer, Heidelberg (2000)
Gerardi, D.: Unmediated communication in games with complete and incomplete information. Journal of Economic Theory 114, 104–131 (2004)
Goldreich, O., Micali, S., Wigderson, A.: How to play any mental game. In: Proceedings of STOC (1987)
Halpern, J., Teague, V.: Rational secret sharing and multiparty computation. In: Proceedings of STOC (2004)
Izmalkov, S., Lepinski, M., Micali, S.: Rational secure function evaluation and ideal mechanism design. In: Proceedings of FOCS (2005)
Kushilevitz, E., Lindell, Y., Rabin, T.: Information-Theoretically Secure Protocols and Security under Composition. In: Proceedings of STOC (2006)
Lepinksi, M., Micali, S., Peikert, C., Shelat, A.: Completely fair SFE and coalition-safe cheap talk. In: Proceedings of PODC (2004)
Urbano, A., Vila, J.E.: Computational complexity and communication: Coordination in two-player games. Econometrica 70(5), 1893–1927 (2002)
Yao, A.: A proof of Yao’s protocol for secure two-party computation (2004) (Never published. The result is presented in Lindell and Pinkas), http://www.cs.biu.ac.il/~lindell/abstracts/yao_abs.html
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2008 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Izmalkov, S., Lepinski, M., Micali, S. (2008). Verifiably Secure Devices. In: Canetti, R. (eds) Theory of Cryptography. TCC 2008. Lecture Notes in Computer Science, vol 4948. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-78524-8_16
Download citation
DOI: https://doi.org/10.1007/978-3-540-78524-8_16
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-78523-1
Online ISBN: 978-3-540-78524-8
eBook Packages: Computer ScienceComputer Science (R0)