Abstract
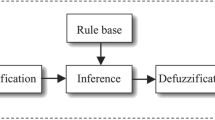
Sensor networks are often deployed in unattended environments, thus leaving these networks vulnerable to false data injection attacks. False data injection attacks will not only cause false alarms that waste real world response efforts, but also drain the finite amount of energy in a battery powered network. The key inheritance based filtering scheme can detect a false report at the very next node of the compromised node that injected the false report before it consumes a significant amount of energy. The choice of a security threshold value in this scheme represents a trade off between security and overhead. In this paper, we propose a fuzzy adaptive threshold determining method for the key inheritance based filtering scheme. The fuzzy rule based system is exploited to determine the security threshold value by considering the average energy level of all the nodes along the path from the base station to a cluster, the number of nodes in that cluster, and the number of compromised nodes. We also introduce a modified version of this scheme to reduce the overhead for changing the threshold value. The proposed method can conserve energy, while it provides sufficient resilience.
This research was supported by the MIC (Ministry of Information and Communication), Korea, under the ITRC (Information Technology Research Center) support program supervised by the IITA (Institute of Information Technology Advancement). (IITA-2006-C1090-0603-0028).
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Zhang, Y., Liu, W., Lou, W., Fang, Y.: Location-Based Compromise-Tolerant Security Mechanisms for Wireless Sensor Networks. IEEE J. Sel. Area Comm. 24(2), 247–260 (2006)
Przydatek, B., Song, D., Perrig, A.: SIA: Secure Information Aggregation in Sensor Networks. In: Proc. of SenSys, pp. 255–265 (2003)
Zhu, S., Setia, S., Jajodia, S., Ning, P.: An Interleaved Hop-by-Hop Authentication Scheme for Filtering of Injected False Data in Sensor Networks. In: Proc. of S&P, pp. 259–271 (2004)
Li, F., Wu, J.: A Probabilistic Voting-based Filtering Scheme in Wireless Sensor Networks. In: Proc. of IWCMC, pp. 27–32 (2006)
Yang, H., Lu, S.: Commutative Cipher Based En-Route Filtering in Wireless Sensor Networks. In: Proc. of VTC 2003, pp. 1223–1227 (2003)
Ye, F., Luo, H., Lu, S.: Statistical En-Route Filtering of Injected False Data in Sensor Networks. IEEE J. Sel. Area Comm 23(4), 839–850 (2005)
Zhang, W., Cao, G.: Group Rekeying for Filtering False Data in Sensor Networks: A Predistribution and Local Collaboration-based Approach. In: Proc. of INFOCOM 2005, pp. 503–514 (2005)
Zhang, Y., Yang, J., Vu, H.T.: The Interleaved Authentication for Filtering False Reports in Multipath Routing based Sensor Networks. In: Proc. of IPDPS (2006)
Lee, H., Cho, T.: Key Inheritance-Based False Data Filtering Scheme in Wireless Sensor Networks. In: Inoue, K., Satoh, K., Toni, F. (eds.) Computational Logic in Multi-Agent Systems. LNCS (LNAI), vol. 4371, pp. 116–127. Springer, Heidelberg (2007)
Perrig, A., Szewczyk, R., Tygar, J.D., Wen, V., Culler, D.E.: SPINS: Security Protocols for Sensor Networks. Wirel. Netw. 8(5), 521–534 (2002)
Chi, S., Cho, T.: Fuzzy Logic based Propagation Limiting Method for Message Routing in Wireless Sensor Networks. In: Gavrilova, M., Gervasi, O., Kumar, V., Tan, C.J.K., Taniar, D., Laganà, A., Mun, Y., Choo, H. (eds.) ICCSA 2006. LNCS, vol. 3983, pp. 58–67. Springer, Heidelberg (2006)
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2007 Springer Berlin Heidelberg
About this paper
Cite this paper
Lee, H.Y., Cho, T.H. (2007). Fuzzy Adaptive Threshold Determining in the Key Inheritance Based Sensor Networks. In: Okuno, H.G., Ali, M. (eds) New Trends in Applied Artificial Intelligence. IEA/AIE 2007. Lecture Notes in Computer Science(), vol 4570. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-73325-6_7
Download citation
DOI: https://doi.org/10.1007/978-3-540-73325-6_7
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-73322-5
Online ISBN: 978-3-540-73325-6
eBook Packages: Computer ScienceComputer Science (R0)