Abstract
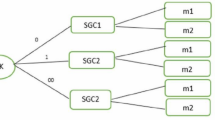
In order to protect communication security among sensor nodes, a cryptographic method are needed by ad hoc sensor networks. According to that most ad hoc sensor networks are deployed in groups, a group-based multicast key management scheme is proposed to extend RPS scheme in this paper. Compared with RPS, our scheme improves the probability that a shared key exists between two sensor nodes, and reduce the probability that the shared key is decrypted.
This paper is supported by the following foundation: National Science foundation of China “60603059” “60403026” “60503055”; Postdoctoral science foundation of china “2005038193”; Postdoctoral foundation of Heilongjiang province, china; Tackling key technical problem of Heilongjiang province “GC06C106” Science Foundation of Harbin Engineering University “HEUFFT05010”; Young backbone teacher project of Harbin Engineering University.
Chapter PDF
Similar content being viewed by others
References
Blundo, C., De Santis, A., Herzberg, A., Kutten, S., Vaccaro, U., Yung, M.: Perfectly-Secure Key Distribution for Dynamic Conferences. In: Brickell, E.F. (ed.) CRYPTO 1992. LNCS, vol. 740, pp. 471–486. Springer, Heidelberg (1993)
Fiat, A., Naor, M.: Broadcast encryption. In: Stinson, D.R. (ed.) CRYPTO 1993. LNCS, vol. 773, pp. 480–491. Springer, Heidelberg (1994)
Halevy, D., Shamir, A.: The LSD Broadcast Encryption Scheme. In: Yung, M. (ed.) CRYPTO 2002. LNCS, vol. 2442, pp. 47–60. Springer, Heidelberg (2002)
Kumar, R., Rajagopalan, S., Sahai, A.: Coding Constructions for Blacklisting Problems without Computational Assumptions. In: Wiener, M.J. (ed.) CRYPTO 1999. LNCS, vol. 1666, pp. 609–623. Springer, Heidelberg (1999)
Naor, D., Naor, M., Lotspiech, J.: Revocation and Tracing Schemes for Stateless Receivers. In: Kilian, J. (ed.) CRYPTO 2001. LNCS, vol. 2139, pp. 41–62. Springer, Heidelberg (2001)
Blom, R.: An Optimal Class of Symmetric Key Generation Systems. In: Beth, T., Cot, N., Ingemarsson, I. (eds.) EUROCRYPT 1984. LNCS, vol. 209, pp. 335–338. Springer, Heidelberg (1985)
Matsumoto, T., Imai, H.: On the Key Predistribution System: A Practical Solution to the Key Distribution Problem. In: Pomerance, C. (ed.) CRYPTO 1987. LNCS, vol. 293, pp. 185–193. Springer, Heidelberg (1988)
Leighton, T., Micali, S.: Secret-Key Agreement without Public-Key Cryptography. In: Stinson, D.R. (ed.) CRYPTO 1993. LNCS, vol. 773, pp. 456–479. Springer, Heidelberg (1994)
Zapata, M.G., Asokan, N.: Securing Ad-Hoc Routing Protocols. In: Proc. of WiSe’02, Singapore, pp. 1–10 (2002)
Chan, H., Perrig, A., Song, D.: Random Key Predistribution Schemes for Sensor Networks. In: Proc. of S&P’03, California, US, pp. 197–215 (2003)
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2007 Springer Berlin Heidelberg
About this paper
Cite this paper
Cai, S., Yao, W., Yao, N., Li, Y., Gu, G. (2007). Group-Based Key Management for Multicast of Ad Hoc Sensor Network. In: Shi, Y., van Albada, G.D., Dongarra, J., Sloot, P.M.A. (eds) Computational Science – ICCS 2007. ICCS 2007. Lecture Notes in Computer Science, vol 4489. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-72588-6_7
Download citation
DOI: https://doi.org/10.1007/978-3-540-72588-6_7
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-72587-9
Online ISBN: 978-3-540-72588-6
eBook Packages: Computer ScienceComputer Science (R0)