Abstract
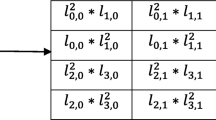
With the rapid development of technology, one of the most important requirements in today’s systems is the reliable transfer of information and confidentiality. Thus, military, electronics, banking systems and many other places have become the fields of use of cryptography science. Cryptology methods are used to solve these problems and need of secure information transfer resulted in the development of reliable encryption techniques. In this study, a new poly-alphabetic substitution cipher is designed using the coordinate axes. The proposed method of a hybrid encryption method is a mix of the Polybius square cipher and the Vigenère cipher, reinforced with the RSA cryptography algorithm. For each letter in the alphabet, there is more than one point on Cartesian coordinate system and in the calculation of these points random chosen values are used. Values used to calculate alphabet and start index of alphabet are send to receiver using RSA algorithm with cipher text. So, with multiple security stages the proposed method is a strong encryption method that is difficult to decode.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Katz, J., Lindell, Y.: Introduction to Modern Cryptography: Principles and Protocols. Chapman & Hall, London (2008)
Koç, Ç.: Cryptographic Engineering. Springer, Heidelberg (2009)
Paar, C., Pelzl, J.: Understanding Cryptography: A Textbook for Student and Practitioners. Springer, Heidelberg (2010). https://doi.org/10.1007/978-3-642-04101-3
Kumar, Y., Munjal, R., Sharma, H.: Comparison of symmetric and asymmetric cryptography with existing vulnerabilities and countermeasures. IJCSMS Int. J. Comput. Sci. Manag. Stud. 11(03), 60–63 (2011)
FIPS 46–3, Data Encryption Standard. National Institute of Standarts and Technology (NIST) (1999)
FIPS 197, Announcing the ADVANCED ENCRYPTION STANDARD (AES). National Institute of Standarts and Technology (NIST) (2001)
Rivest, R.L., Shamir, A., Adleman, L.M.: A method for obtaining digital signatures and public-key cryptosystems. CACM 21(2), 120–126 (1978)
Chaudhury, P., et al.: ACAFP: asymmetric key based cryptographic algorithm using four prime numbers to secure message communication. A review on RSA algorithm. In: 8th Annual Industrial Automation and Electromechanical Engineering Conference (IEMECON), Bangkok, pp. 332–337(2017)
Miller, V.S.: Use of elliptic curves in cryptography. In: Williams, Hugh C. (ed.) CRYPTO 1985. LNCS, vol. 218, pp. 417–426. Springer, Heidelberg (1986). https://doi.org/10.1007/3-540-39799-X_31
Ratna, A. A. P., Purnamasari, P. D., Shaugi, A., Salman, M.: Analysis and comparison of MD5 and SHA-1 algorithm implementation in simple-O authentication based security system. In: 2013 International Conference on QiR, pp. 99–104 (2013)
Rivest, R.: The MD5 Message-Digest Algorithm. Network Working Group, MIT Laboratory for Computer Science and RSA Data Security, Inc., April 1992
Chaves, R., Sousa, L., Sklavos, N., Fournaris, A.P., Kalogeridou, G., Kitsos, P., Sheikh, F.: Secure Hashing: SHA-1, SHA-2, and SHA-3. Taylor & Francis Group, LLC, Milton Park (2016)
Selcuk, B, Tankul, A.N.A., Dundar, A., Akkus, Z., Arslan, M.: Designing a new hybrid cryptographic model using coordinate axes. Anatolian J. Comput. Sci. (accepted)
Highland, H.J.: Data encryption: a non-mathematical approach. Comput. Sec. 16(5), 369–386 (1997)
Paul, A.J., Mythili, P.: Poly-alphabetic substitution mapping for cryptographic transformations. In: Conference: National Conference on Recent Innovations in Technology, March 2009
Kartha, R.S., Paul, V.: An efficient algorithm for polyalphabetic substitution using infinite number of alphabetical tables. Int. J. Appl. Eng. Res. 13(4), 14–20 (2018)
Aung, T.M., Naing, H.H., Hla, N.N.: A complex transformation of monoalphabetic cipher to polyalphabetic cipher: (Vigenère-Affine cipher). Int. J. Mach. Learn. Comput. 9(3), 296–303 (2019)
Saraswat, A., Khatri, C., Thakral, P., Biswas, P.: An extended hybridization of vigenère and caesar cipher techniques for secure communication. Proc. Comput. Sci. 92, 355–360 (2016)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2020 ICST Institute for Computer Sciences, Social Informatics and Telecommunications Engineering
About this paper
Cite this paper
Selçuk, B., Tankül, A.N.A. (2020). Designing a New Hybrid Cryptographic Model. In: Bhuiyan, T., Rahman, M.M., Ali, M.A. (eds) Cyber Security and Computer Science. ICONCS 2020. Lecture Notes of the Institute for Computer Sciences, Social Informatics and Telecommunications Engineering, vol 325. Springer, Cham. https://doi.org/10.1007/978-3-030-52856-0_3
Download citation
DOI: https://doi.org/10.1007/978-3-030-52856-0_3
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-52855-3
Online ISBN: 978-3-030-52856-0
eBook Packages: Computer ScienceComputer Science (R0)