Abstract
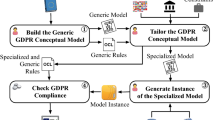
The European General Data Protection Regulation (GDPR, EU 2016/679), adopted by the European Parliament has profoundly changed the legislative approach to the protection of personal data by the European Union. The GDPR provisions require organizations to make deep changes. Organizations have to shift from an approach based on the adoption of minimum-security measures, provided by the EU Directive of 1994, to a proactive approach based on accountability. Organizations that manage personal data of EU citizens have to adopt systems of verification and continuous improvement and adopt principles such as privacy by design and privacy by default. The rule of “privacy by design” calls for privacy to be taken into account throughout the whole engineering process. A key point is the methods for checking compliance with GDPR. This paper proposes a structured approach based on business process modelling, to support compliance with the GDPR. We have identified an approach that has to identify the most important key points for GDPR compliance.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
E.-O. Wilhelm, A brief history of the General Data Protection Regulation
M. Pesic, H. Schonenberg, W.M.P. Van Der Aalst, DECLARE: full support for loosely-structured processes, in Proceedings—IEEE International Enterprise Distributed Object Computing Workshop, EDOC (2007)
T.T. Hildebrandt, R.R. Mukkamala, Declarative event-based workflow as distributed dynamic condition response graphs (2011). arXiv:1110.4161
D. Harel, M. Politi, I. Books24x7, Modeling Reactive Systems with Statecharts (1998)
A.M. Fernandez-Saez, D. Caivano, M. Genero, M.R.V. Chaudron, On the use of UML documentation in software maintenance: results from a survey in industry, in 2015 ACM/IEEE 18th International Conference on Model Driven Engineering Languages and Systems, MODELS 2015—Proceedings (2015), pp. 292–301
O.M. Group, OMG unified modeling language TM (OMG UML), Superstructure v.2.5. InformatikSpektrum (2015)
P. Ardimento, D. Caivano, M. Cimitile, G. Visaggio, Empirical investigation of the efficacy and efficiency of tools for transferring software engineering knowledge. J. Inf. Knowl. Manag. 7(3), 197–207 (2008)
S. España, N. Condori-Fernandez, A. González, O. Pastor, An empirical comparative evaluation of requirements engineering methods. J. Braz. Comput. Soc. 16(1), 3–19 (2010)
R. Hull et al., Introducing the guard-stage-milestone approach for specifying business entity lifecycles, in Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) (2011)
Object Management Group, Case Management Model and Notation (CMMN) (2013)
Object Management Group, Business Process Model and Notation (BPMN) Version 2.0 (2011)
M. Cremonini, E. Damiani, S.C. di Vimercati, P. Samarati, A. Corallo, G. Elia, Security, Privacy, and Trust in Mobile Systems and Applications (IGI Global, 2005)
M. Enamul Kabir, H. Wang, E. Bertino, A conditional purpose-based access control model with dynamic roles. Expert Syst. Appl. (2011)
C. Ardito, U. Barchetti, A. Capodieci, A. Guido, L. Mainetti, Business process design meets business practices through enterprise patterns. Int. J. e-Collab. 10(1), 57–73 (2014)
U. Barchetti, A. Capodieci, A.L. Guido, L. Mainetti, Modelling collaboration processes through design patterns. Comput. Inf. 30(1), 113–135 (2011)
A. Capodieci, L. Mainetti, L. Alem, An innovative approach to digital engineering services delivery: an application in maintenance, in 2015 11th International Conference on Innovations in Information Technology (IIT) (IIT’15), Dubai, UAE (2015), pp. 336–343
W. Labda, N. Mehandjiev, P. Sampaio, Modeling of privacy-aware business processes in BPMN to protect personal data, in Proceedings of the 29th Annual ACM Symposium on Applied Computing, New York, NY, USA (2014), pp. 1399–1405
A.D. Brucker, Integrating security aspects into business process models. Inf. Technol. 55(6), 239–246 (2013)
Y. Cherdantseva, J. Hilton, O. Rana, Towards SecureBPMN—aligning BPMN with the information assurance and security domain, in Business Process Model and Notation (2012), pp. 107–115
O. Altuhhov, R. Matulevičius, N. Ahmed, An extension of business process model and notation for security risk management. Int. J. Inf. Syst. Model. Des. (IJISMD) 4(4), 93–113 (2013)
P. Pullonen, R. Matulevičius, D. Bogdanov, PE-BPMN: privacy-enhanced business process model and notation, in Business Process Management (2017), pp. 40–56
M. Salnitri, F. Dalpiaz, P. Giorgini, Designing secure business processes with SecBPMN. Softw. Syst. Model. 16(3), 737–757 (2017)
M.E.A. Chergui, S.M. Benslimane, A valid BPMN extension for supporting security requirements based on cyber security ontology, in Model and Data Engineering (2018), pp. 219–232
C.L. Maines, D. Llewellyn-Jones, S. Tang, B. Zhou, A cyber security ontology for BPMN-security extensions, in 2015 IEEE International Conference on Computer and Information Technology; Ubiquitous Computing and Communications; Dependable, Autonomic and Secure Computing; Pervasive Intelligence and Computing (2015), pp. 1756–1763
C.L. Maines, B. Zhou, S. Tang, Q. Shi, Adding a third dimension to BPMN as a means of representing cyber security requirements, in 2016 9th International Conference on Developments in eSystems Engineering (DeSE) (2016), pp. 105–110
K.S. Sang, B. Zhou, BPMN security extensions for healthcare process, in 2015 IEEE International Conference on Computer and Information Technology; Ubiquitous Computing and Communications; Dependable, Autonomic and Secure Computing; Pervasive Intelligence and Computing (2015), pp. 2340–2345
A. Rodríguez, E. Fernández-Medina, M. Piattini, A BPMN extension for the modeling of security requirements in business processes. IEICE Trans. Inf. Syst. (2007)
M. Menzel, I. Thomas, C. Meinel, Security requirements specification in service-oriented business process management, in 2009 International Conference on Availability, Reliability and Security (2009), pp. 41–48
M. Palmirani, M. Martoni, A. Rossi, C. Bartolini, L. Robaldo, PrOnto: privacy ontology for legal reasoning, in Electronic Government and the Information Systems Perspective (2018), pp. 139–152
D. Basin, S. Debois, T. Hildebrandt, On purpose and by necessity: compliance under the GDPR, in Financial Cryptography and Data Security (FC) (2018)
A. Capodieci, L. Mainetti, Business process awareness to support GDPR compliance, in In Proceedings of the 9th International Conference on Information Systems and Technologies (ICIST 2019). ACM, New York, NY, USA, Article 2 (2019), 6 pages. https://doi.org/10.1145/3361570.3361573
Acknowledgements
This work was partially supported by the “EASYPAL” project no. Y95B457, funded by Innolabs Apulia Region (Italy), entitled “Sostegno alla creazione di soluzioni innovative finalizzate a specifici problemi di rilevanza sociale” under the POR Puglia FESR 2014-2020 research program sub-azione 1.4.B.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2020 Springer Nature Switzerland AG
About this paper
Cite this paper
Capodieci, A., Mainetti, L. (2020). A Structured Approach to GDPR Compliance. In: Przegalinska, A., Grippa, F., Gloor, P. (eds) Digital Transformation of Collaboration. COINs 2019. Springer Proceedings in Complexity. Springer, Cham. https://doi.org/10.1007/978-3-030-48993-9_16
Download citation
DOI: https://doi.org/10.1007/978-3-030-48993-9_16
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-48992-2
Online ISBN: 978-3-030-48993-9
eBook Packages: Mathematics and StatisticsMathematics and Statistics (R0)