Abstract
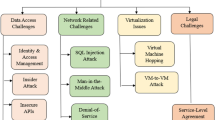
In today’s world, almost everything has been digitised and hence the cloud computing is emerging as a boom in its field. But the most disturbing fact is that the cloud computing also appears as a vulnerable platform and therefore the security becomes the most important aspect in the cloud computing applications. Security issues are mainly dealt with known and unknown threats, malware and network access by unknown or unauthorised users. Hence, it has become a fundamental feature to create a secure platform for the cloud computing technologies. In this scenario, we proposed a RTMDC (Reputation based Trust Management system with Data Colouring) systems, which builds and tests a secure platform using Reputation Based Trust Management technique. Reputation based trust factor is then calculated using the collective reviews given by the users. This research work focuses on the images that has been related to the cloud users.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Shaik Hussain, S.I., Yuvaraj, V.: A secure data access control method using AES for P2P storage cloud. IEEE (2015)
He, H., Li, R., Dong, X., Zhang, Z.: Secure, efficient and fine-grained data access control mechanism for P2P storage cloud. IEEE (2014)
Manjusha, R., Ramachandran, R.: Sharing data in cloud based on Trust Attribute Based Encryption (TABE). ARPN J. Eng. Appl. Sci. 10(9), 3 (2015)
Bonatti, P., Duma, C., Olmedilla, D., Shahmehri, N.: An integration of reputation-based and policy based trust management
Liu, Y.-C., Ma, Y.-T., Zhang, H.-S., Li, D.-Y., Chen, G.-S.: A method for trust management in cloud computing: data coloring by cloud watermarking. Int. J. Autom. Comput. 8(3), 280 (2011)
Banerjee, A., Neogy, S., Chowdhury, C.: Reputation based trust management system for MANET. In: Third International Conference on Emerging Applications of Information Technology (EAIT) (2012)
Selcuk, A.A., Uzun, E., Pariente, M.R.: A reputation-based trust management system for P2P networks. Int. J. Netw. Secur. 6(3), 235–245 (2008)
Noor, T.H., Sheng, Q.Z., Yao, L., Dustdar, S., Ngu, A.H.H.: CloudArmor: supporting reputation-based trust management for cloud services. IEEE Trans. Parallel Distrib. Syst. 27(2), 367–380 (2015)
Nitya Lakshmi, R., Laavanya, R., Meenakshi, M., Suresh Gana Dhas, C.: Analysis of attribute based encryption schemes. Int. J. Comput. Sci. Eng. Commun. 3(3), 1076–1081 (2015)
Saravana Kumar, N., Rajya Lakshmi, G.V., Balamurugan, B.: Enhanced attribute based encryption for cloud computing. In: International Conference on Information and Communication Technologies (ICICT 2014) (2014)
Hwang, K., Li, D.: Trusted cloud computing with secure resources and data coloring. IEEE (2010)
Chadha, K., Bajpai, A.: Security aspects of cloud computing. Int. J. Comput. Appl. 40(8), 43–47 (2012)
Security for Cloud Computing Ten Steps to Ensure Success: Cloud Standards Customer Council (2017)
Author information
Authors and Affiliations
Corresponding authors
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2020 Springer Nature Switzerland AG
About this paper
Cite this paper
Verma, P., Dongre, N., Bittal, V. (2020). RTMDC for Effective Cloud Data Security. In: Balaji, S., Rocha, Á., Chung, YN. (eds) Intelligent Communication Technologies and Virtual Mobile Networks. ICICV 2019. Lecture Notes on Data Engineering and Communications Technologies, vol 33. Springer, Cham. https://doi.org/10.1007/978-3-030-28364-3_6
Download citation
DOI: https://doi.org/10.1007/978-3-030-28364-3_6
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-28363-6
Online ISBN: 978-3-030-28364-3
eBook Packages: EngineeringEngineering (R0)