Abstract
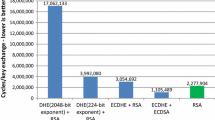
Recently Castryck, Lange, Martindale, Panny, and Renes published CSIDH, a new key exchange scheme using supersingular elliptic curve isogenies. Due to its small key sizes and the possibility of a non-interactive and a static-static key exchange, CSIDH seems very interesting for practical applications. However, the performance is rather slow. Therefore, we employ some techniques to speed up the algorithms, mainly by restructuring the elliptic curve point multiplications and by using twisted Edwards curves in the isogeny image curve computations, yielding a speed-up factor of 1.33 in comparison to the implementation of Castryck et al. Furthermore, we suggest techniques for constant-time implementations.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
Notes
- 1.
In [1] it is stated that the best performance for SIKEp503 and SIKEp751 on a 3.4 GHz processor is 10.1 ms and 30.5 ms, respectively.
- 2.
The implementation results in [8] suggest that SIKE is about 10x faster than CSIDH at NIST security level 1. Note that SIKE uses a protected constant-time implementation, while the numbers for CSIDH are obtained from an unprotected non-constant-time implementation.
- 3.
We refer to the version from 27.04.2018 throughout this work.
- 4.
Instead of using the values from [8], we measured their implementation in our setting in order to give a fair comparison.
- 5.
We measured 318.9 \(\times \,10^6\) clock cycles for the running time for the key \(e'\) in the setting from Table 1, using the optimized implementation.
References
Azarderakhsh, R., et al.: Supersingular isogeny key encapsulation, Round 1 submission, NIST Post-Quantum Cryptography Standardization (2017). https://sike.org/files/SIDH-spec.pdf
Bernstein, D.J., Birkner, P., Joye, M., Lange, T., Peters, C.: Twisted Edwards curves. In: Vaudenay, S. (ed.) AFRICACRYPT 2008. LNCS, vol. 5023, pp. 389–405. Springer, Heidelberg (2008). https://doi.org/10.1007/978-3-540-68164-9_26
Bernstein, D.J., Birkner, P., Lange, T., Peters, C.: ECM using Edwards curves. Math. Comput. 82(282), 1139–1179 (2013)
Biasse, J.F., Jacobson Jr., M.J., Iezzi, A.: A note on the security of CSIDH. arXiv preprint arXiv:1806.03656 (2018)
Bonnetain, X., Schrottenloher, A.: Quantum security analysis of CSIDH and ordinary isogeny-based schemes. Cryptology ePrint Archive, Report 2018/537 (2018). https://eprint.iacr.org/2018/537
Bos, J.W., Friedberger, S.: Arithmetic considerations for isogeny based cryptography. Cryptology ePrint Archive, Report 2018/376 (2018). https://eprint.iacr.org/2018/376
Castryck, W., Galbraith, S., Farashahi, R.R.: Efficient arithmetic on elliptic curves using a mixed Edwards-Montgomery representation. Cryptology ePrint Archive, Report 2008/218 (2008), http://eprint.iacr.org/2008/218
Castryck, W., Lange, T., Martindale, C., Panny, L., Renes, J.: CSIDH: an efficient post-quantum commutative group action (2018). https://eprint.iacr.org/2018/383.pdf
Childs, A., Jao, D., Soukharev, V.: Constructing elliptic curve isogenies in quantum subexponential time. J. Math. Cryptology 8(1), 1–29 (2014)
Costello, C., Hisil, H.: A simple and compact algorithm for SIDH with arbitrary degree isogenies. In: Takagi, T., Peyrin, T. (eds.) ASIACRYPT 2017. LNCS, vol. 10625, pp. 303–329. Springer, Cham (2017). https://doi.org/10.1007/978-3-319-70697-9_11
Costello, C., Longa, P., Naehrig, M.: Efficient algorithms for supersingular isogeny Diffie-Hellman. In: Robshaw, M., Katz, J. (eds.) CRYPTO 2016. LNCS, vol. 9814, pp. 572–601. Springer, Heidelberg (2016). https://doi.org/10.1007/978-3-662-53018-4_21
Couveignes, J.M.: Hard homogeneous spaces. Cryptology ePrint Archive, Report 2006/291 (2006). https://eprint.iacr.org/2006/291
De Feo, L.: Mathematics of isogeny based cryptography. Notes from a summer school on Mathematics for Post-quantum cryptography (2017). http://defeo.lu/ema2017/poly.pdf
Edwards, H.M.: A normal form for elliptic curves. Bull. Am. Math. Soc. 44, 393–422 (2007)
Feo, L.D., Kieffer, J., Smith, B.: Towards practical key exchange from ordinary isogeny graphs. Cryptology ePrint Archive, Report 2018/485 (2018). https://eprint.iacr.org/2018/485
Jao, D., De Feo, L., Plût, J.: Towards quantum-resistant cryptosystems from supersingular elliptic curve isogenies. J. Math. Cryptology 8(3), 209–247 (2014)
Marin, L.: Differential elliptic point addition in Twisted Edwards curves. In: 2013 27th International Conference on Advanced Information Networking and Applications Workshops, pp. 1337–1342 (2013)
Meyer, M., Reith, S., Campos, F.: On hybrid SIDH schemes using Edwards and Montgomery curve arithmetic. Cryptology ePrint Archive, Report 2017/1213 (2017). https://eprint.iacr.org/2017/1213
Montgomery, P.L.: Speeding the Pollard and Elliptic Curve methods of factorization. Math. Comput. 48(177), 243–264 (1987)
Moody, D., Shumow, D.: Analogues of Vélu’s formulas for isogenies on alternate models of elliptic curves. Math. Comput. 85(300), 1929–1951 (2016)
Renes, J.: Computing Isogenies between montgomery curves using the action of (0, 0). In: Lange, T., Steinwandt, R. (eds.) PQCrypto 2018. LNCS, vol. 10786, pp. 229–247. Springer, Cham (2018). https://doi.org/10.1007/978-3-319-79063-3_11
Rostovtsev, A., Stolbunov, A.: Public-key cryptosystem based on isogenies. Cryptology ePrint Archive, Report 2006/145 (2006). http://eprint.iacr.org/2006/145
The National Institute of Standards and Technology (NIST): Submission requirements and evaluation criteria for the post-quantum cryptography standardization process (2016)
Vélu, J.: Isogénies entre courbes elliptiques. C.R. Acad. Sci. Paris, Série A 271, 238–241 (1971)
Acknowledgements
This work was partially supported by Elektrobit Automotive, Erlangen, Germany. We thank Fabio Campos, Marc Stöttinger, and the anonymous reviewers for their helpful and valuable comments.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2018 Springer Nature Switzerland AG
About this paper
Cite this paper
Meyer, M., Reith, S. (2018). A Faster Way to the CSIDH. In: Chakraborty, D., Iwata, T. (eds) Progress in Cryptology – INDOCRYPT 2018. INDOCRYPT 2018. Lecture Notes in Computer Science(), vol 11356. Springer, Cham. https://doi.org/10.1007/978-3-030-05378-9_8
Download citation
DOI: https://doi.org/10.1007/978-3-030-05378-9_8
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-05377-2
Online ISBN: 978-3-030-05378-9
eBook Packages: Computer ScienceComputer Science (R0)