Abstract
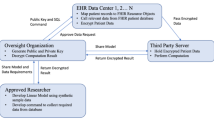
Large databases are increasingly used to manage sensitive data; however, they are vulnerable to abuse by insiders and intruders. We describe a novel method that protects electronic records from intruders and even the most powerful of insiders, the system administrators. Confidential data are partitioned and distributed after asymmetric encryption for management over multiple databases. Data splitting and distributed management prevent unauthorized and covert access by any single party. Confidential systems using this design can work synergistically with existing security measures and are suitable for health, genomic, and financial records.
The original version of this chapter was revised: The copyright line was incorrect. This has been corrected. The Erratum to this chapter is available at DOI: 10.1007/978-0-387-35508-5_22
Chapter PDF
Similar content being viewed by others
References
Anderson, R. (1998). The Decode proposal for an Icelandic health database. http://www.cl.cam.ac.uk/users/rja14/iceland/iceland.html.
Bouzelat, M., Quantin, C. and Dusserre, L. (1996). Extraction and anonymity protocol of medical file. Proceedings of the AMIA Annual Fall Symposium, pp. 323 - 327.
Dusserre, L. Quantin, C. and Bouzelat, M. (1995). A one way public key cryptosystem for the linkage of nominal files in epidemiological studies. Medinfo, 8(1), pp. 611 647.
Enserink, M. (1998). Opponents criticize Iceland’s database [news]. Science, 282 (5390), p. 859.
Ex-employee videotapes Stanford medical data security breach. Inside Healthcare Computing,May 27, 1996.
How a 13-year-old breached HIS security, made phony AIDS calls. inside Healthcare Computing,March 4, 1996.
Michaelis, J., Miller, M., Pommerening, K. and Schmidtmann, I. (1995). A new concept to ensure data privacy and data security in cancer registries. Medinfo, 8 (pt 1), pp. 661 - 665.
O’Connor, J., Gray, J., McCollum, C. and Notargiacomo, L. (1992). Research Directions in Database Security (ed. T. Lunt ), Springer-Verlag, pp. 41 - 62.
Pangalos, G. (1996). Security of medical database systems for health care IT and security personnel. Data Security for Health Care, Volume II: Technical Guidelines (eds. The SEISMED Consortium), IOS Press, pp. 235 - 342.
Pommerening, K., Miller, M., Schmidtmann, I. and Michaelis, J. (1996). Pseudonyms for cancer registries. Methods Inf Med, 35, pp. 112 - 121.
Rabin, M. (1989). Efficient dispersal of information for security, load balancing, and fault tolerance. Journal of the ACM, 36 (2), pp. 335 - 348.
Schneier, B. (1996). Applied Cryptography, Second Edition, John Wiley and Sons, pp. 461-482, pp. 561 - 596.
Sweeney, L. (1996). Replacing personally-identifying information in medical records, the Scrub system. Proceedings of the AMIA Annual Fall Symposium, pp. 333 - 337.
Sweeney, L. (1997). Guaranteeing anonymity when sharing medical data, the Datafly System. Proceedings of the AMIA Annual Fall Symposium, pp. 51 - 55.
U.S. Congress, Office of Technology Assessment (1993). Protecting Privacy in Computerized Medical Information. Washington, DC: U.S. Government Printing Office.
Zitner, A. (1997). Protecting the privacy of medical records. The Boston Globe.
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2000 IFIP International Federation for Information Processing
About this chapter
Cite this chapter
Ho, A.PJ. (2000). A Secret Splitting Method for Assuring the Confidentiality of Electronic Records. In: Atluri, V., Hale, J. (eds) Research Advances in Database and Information Systems Security. IFIP — The International Federation for Information Processing, vol 43. Springer, Boston, MA. https://doi.org/10.1007/978-0-387-35508-5_8
Download citation
DOI: https://doi.org/10.1007/978-0-387-35508-5_8
Publisher Name: Springer, Boston, MA
Print ISBN: 978-1-4757-6411-6
Online ISBN: 978-0-387-35508-5
eBook Packages: Springer Book Archive