Abstract
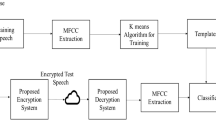
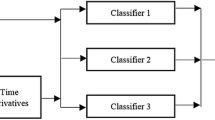
In this research we propose to use phoneme spotting to improve the results in the generation of a cryptographic key. Phoneme spotting selects the phonemes with highest accuracy in the user classification task. The key bits are constructed by using the Automatic Speech Recognition and Support Vector Machines. Firstly, a speech recogniser detects the phoneme limits in each speech utterance. Afterwards, the support vector machine performs a user classification and generates a key. By selecting the highest accuracy phonemes for a a set of 10, 20, 30 and 50 speakers randomly chosen from the YOHO database, it is possible to generate reliable cryptographic keys.
Chapter PDF
Similar content being viewed by others
Keywords
- Support Vector Machine
- Hide Markov Model
- Support Vector Machine Model
- Automatic Speech Recognition
- Speech Recogniser
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Boser, B., Guyon, I., Vapnik, V.: A training algorithm for optimal margin classifiers. In: Proceedings of the Fifth Annual Workshop on Computational Learning Theory (1992)
Campbell, J.P.: Jr.: Features and Measures for Speaker Recognition. Ph.D. Dissertation, Oklahoma State University (1992)
Cortes, C., Vapnik, V.: Support-vector network. Machine Learning 20, 273–297 (1995)
Higgins, A., Porter, J.,, J.: Bahler L.: YOHO Speaker Authentication Final Report. ITT Defense Communications Division (1989)
Young, S., Woodland, P.: HTK Hidden Markov Model Toolkit home page, http://htk.eng.cam.ac.uk/
Monrose, F., Reiter, M.K., Li, Q., Wetzel, S.: Cryptographic Key Generation From Voice. In: Proceedings of the IEEE Conference on Security and Privacy, Oakland, CA (2001)
Osuna, E.: Freund R., and Girosi F.: Support vector machines: Training and applications. Technical Report AIM-1602, MIT A.I. Lab (1996)
Osuna, E.: Training Support Vector Machines: An Application to Face Recognition. In: IEEE Conference on Computer Vision and Pattern Recognition, pp. 130–136 (1997)
Furui, S.: Digital Speech Processing, Synthesis, and Recognition. Mercel Dekker, Inc., New York (2001)
Rabiner, L.R.: A tutorial on hidden Markov models and selected applications in speech recognition. Proceedings of the IEEE 77(2), 257–286 (1989)
Rabiner, L.R., Juang, B.-H.: Fundamentals of speech recognition. Prentice-Hall, New-Jersey (1993)
Uludag, U., Pankanti, S., Prabhakar, S., Jain, A.K.: Biometric cryptosystems: issues and challenges. Proceedings of the IEEE 92(6) (2004)
Lee, K., Hon, H., Reddy, R.: An overview of the SPHINX speech recognition system. IEEE Transactions on Acoustics, Speech and Signal Processing 38(1), 35–45 (1990)
Joachims, T.: SVMLight: Support Vector Machine, SVM-Light Support Vector Machine University of Dortmund (1999), http://svmlight.joachims.org/
Wilcox, L., Smith, I., Bush, M.: Wordspotting for voice editing and audio indexing, CHI 1992. In: Proceedings of the SIGCHI conference on Human factors in computing systems, pp. 655–656. ACM Press, New York (1992)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2005 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
García-Perera, L.P., Nolazco-Flores, J.A., Mex-Perera, C. (2005). Phoneme Spotting for Speech-Based Crypto-key Generation. In: Sanfeliu, A., Cortés, M.L. (eds) Progress in Pattern Recognition, Image Analysis and Applications. CIARP 2005. Lecture Notes in Computer Science, vol 3773. Springer, Berlin, Heidelberg. https://doi.org/10.1007/11578079_80
Download citation
DOI: https://doi.org/10.1007/11578079_80
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-29850-2
Online ISBN: 978-3-540-32242-9
eBook Packages: Computer ScienceComputer Science (R0)