Abstract
Designing security-critical systems correctly is very difflcult. We present work on software engineering of security critical systems, supported by the CASE tool AUTOFOCUS.
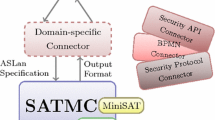
Security critical systems are specified with extended structure diagrams, message sequence charts for the protocols and statecharts for the attacker, translated into an AUTOFOCUS system model and examined for security weaknesses using model checking. Additionally, the specifications could be simulated or tested - which is a first step towards integration of cryptographic primitives, intuitive graphical modelling, simulation and model checking.
We explain our method at the example of a part of the Common Electronic Purse Specifications (CEPS), and comment on potential of vulnerability and consequences for the design.
This work was partially supported by the Studienstiftung des deutschen Volkes, and by the German Ministry of Economics within the FairPay project
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
M. Abadi, M. Burrows, C. Kaufman, and B. Lampson. Authentication and delegation with smart-cards. Science of Computer Programming, 21(2):93–113, 1993.
R. Anderson. Why cryptosystems fail. Communications of the ACM, 37(11):32–40, November 1994.
R. Anderson. The formal verification of a payment system. In Mike Hinchey and Jonathan Bowen, editors, Industrial-Strength Formal Methods in Practice. Springer, 1999.
R. Anderson. Security Engineering: A Guide to Building Dependable Distributed Systems. Wiley, 2001.
N. Asokan, P. Janson, M. Steiner, and M. Waidner. The state of the art in electronic payment systems. Advances in Computers, 53, 2000.
M. Burrows, M. Abadi, and R. Needham. A logic of authentication. Proceedings of the Royal Society of London A, 426:233–271, 1989.
M. Broy, F. Dederich, C. Dendorfer, M. Fuchs, T. Gritzner, and R. Weber. The design of distributed systems — an introduction to FOCUS. Technical Report TUM-I9202, Technische Universität München, 1992.
D. Dolev and A. Yao. On the security of public key protocols. IEEE Transactions on Information Theory, 29(2):198–208, 1983.
D. Gollmann. What do we mean by entity authentication ? In IEEE Symposium on Security and Privacy, 1996.
D. Gollmann. Computer Security. J. Wiley, 1999.
D. Gollmann. On the verification of cryptographic protocols — a tale of two committees. In Workshop on Security Architectures and Information Flow, volume 32 of Electronical Notes in Theoretical Computer Science, 2000.
Stefanos Gritzalis, Diomidis Spinellis, and Panagiotis Georgiadis. Security protocols over open networks and distributed systems: Formal methods for their analysis, design, and verification. Computer Communications, 22(8):695–707, 1999.
F. Huber, S. Molterer, A. Rausch, B. Schätz, M. Sihling, and O. Slotosch. Tool supported Specification and Simulation of Distributed Systems. In International Symposium on Software Engineering for Parallel and Distributed Systems, pages 155–164, 1998.
F. Huber, S. Molterer, B. Schätz, O. Slotosch, and A. Vilbig. Traffic Lights-An AUTOFOCUS Case Study. In 1998 International Conference on Application of Concurrency to System Design, pages 282–294. IEEE Computer Society, 1998.
ITU. ITU-TS Recommendation Z. 120: Message Sequence Chart (MSC). ITU-TS, Geneva, 1996.
Jan Jürjens. Object-oriented modelling of audit security for smart-card payment schemes. In P. Paradinas, editor, IFIP/SEC 2001-16th International Conference on Information Security. Kluwer, 2001a.
Jan Jürjens. Secrecy-preserving refinement. In Formal Methods Europe, LNCS. Springer, 2001b.
Jan Jürjens. Towards development of secure systems using UML. In H. Hußmann, editor, Fundamental Approaches to Software Engineering (FASE/ETAPS, International Conference), LNCS. Springer, 2001c.
J. Jürjens and G. Wimmel. Specification-based Testing of Firewalls. In Andrei Ershov 4th International Conference “Perspectives of System Informatics ” (PSI’01). Springer, 2001. To appear.
I. Krüger. Distributed System Design with Message Sequence Charts. PhD thesis, Technische Universität München, 2000.
V. Lotz. Threat scenarios as a means to formally develop secure systems. Journal of Computer Security 5, pages 31–67, 1997.
G. Lowe. Breaking and fixing the Needham-Schroeder Public-Key Protocol using FDR. In Margaria and Steffen, editors, TACAS, volume 1055 of LNCS. Springer, 1996.
Lawrence C. Paulson. The inductive approach to verifying cryptographic protocols. Journal of Computer Security, 6(1–2):85–128, 1998.
J. Philipps and O. Slotosch. The Quest for Correct Systems: Model Checking of Diagramms and Datatypes. In Asia Pacific Software Engineering Conference 1999, 1999.
Birgit Pfitzmann and Michael Waidner. A model for asynchronous reactive systems and its applications to secure message transmissions. In IEEE Symposium on Security and Privacy, 2001.
P. Ryan, S. Schneider, M. Goldsmith, G. Lowe, and B. Roscoe. Analysis and Design of Security Protocols. Addison Wesley, 2001.
S. Stepney, D. Cooper, and J. Woodcock. An Electronic Purse: Specification, Refinement, and Proof. Oxford University Computing Laboratory, 2000. Technical Monograph PRG-126.
O. Slotosch. Quest: Overview over the Project. In D. Hutter, W. Stephan, P Traverso, and M. Ullmann, editors, Applied Formal Methods — FM-Trends 98, pages 346–350. Springer LNCS 1641, 1998.
G. Wimmel, H. Lötzbeyer, A. Pretschner, and O. Slotosch. Specification Based Test Sequence Generation with Propositional Logic. Journal on Software Testing Verfication and Reliability, 10, 2000.
G. Wimmel and A. Wißpeitner. Extended description techniques for security engineering. In P. Paradinas, editor, IFIP/SEC 2001 — 16th International Conference on Information Security. Kluwer, 2001.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2001 IFIP International Federation for Information Processing
About this chapter
Cite this chapter
Jürjens, J., Wimmel, G. (2001). Security Modelling for Electronic Commerce: The Common Electronic Purse Specifications. In: Schmid, B., Stanoevska-Slabeva, K., Tschammer, V. (eds) Towards the E-Society. IFIP International Federation for Information Processing, vol 74. Springer, Boston, MA. https://doi.org/10.1007/0-306-47009-8_36
Download citation
DOI: https://doi.org/10.1007/0-306-47009-8_36
Publisher Name: Springer, Boston, MA
Print ISBN: 978-0-7923-7529-6
Online ISBN: 978-0-306-47009-7
eBook Packages: Springer Book Archive